信息网络安全 ›› 2026, Vol. 26 ›› Issue (4): 521-541.doi: 10.3969/j.issn.1671-1122.2026.04.002
基于机器学习的恶意软件检测方法综述
火箭军工程大学 西安 710025
-
收稿日期:2025-09-12出版日期:2026-04-10发布日期:2026-04-29 -
通讯作者:张运豪 E-mail:2350525702@qq.com -
作者简介:李海龙(1978—),男,甘肃,副教授,博士,主要研究方向为复杂网络和网络安全|张运豪(1999—),男,重庆,硕士研究生,主要研究方向为网络安全|沈燮阳(1989—),男,河南,讲师,博士,主要研究方向为数据安全和访问控制|邢宇航(1979—),男,河南,副教授,博士,主要研究方向为网络与信息安全|崔治安(2000—),男,山东,硕士研究生,主要研究方向为网络安全 -
基金资助:国家自然科学基金(62176263)
A Survey of Machine Learning-Based Malware Detection Methods
LI Hailong, ZHANG Yunhao( ), SHEN Xieyang, XING Yuhang, CUI Zhian
), SHEN Xieyang, XING Yuhang, CUI Zhian
Rocket Force University of Engineering Xi’an 710025, China
-
Received:2025-09-12Online:2026-04-10Published:2026-04-29
摘要:
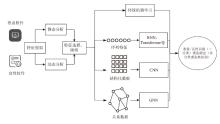
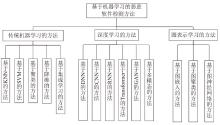
随着网络空间威胁的不断升级,恶意软件在数量与复杂性方面呈爆炸式增长。机器学习凭借其强大的特征提取能力,被广泛应用于恶意软件检测任务中。本文综述了近年来基于机器学习的恶意软件检测技术。首先,介绍了恶意软件的定义与检测体系;其次,详细综述了传统机器学习、深度学习和图表示学习在恶意软件检测中的应用;再次,对这3类机器学习方法进行比较和分析;最后,总结了当前面临的技术瓶颈,并提出未来展望。
中图分类号:
引用本文
李海龙, 张运豪, 沈燮阳, 邢宇航, 崔治安. 基于机器学习的恶意软件检测方法综述[J]. 信息网络安全, 2026, 26(4): 521-541.
LI Hailong, ZHANG Yunhao, SHEN Xieyang, XING Yuhang, CUI Zhian. A Survey of Machine Learning-Based Malware Detection Methods[J]. Netinfo Security, 2026, 26(4): 521-541.
表1
传统机器学习的检测方法对比
| 方法 | 典型方案 | 优点 | 缺点 |
|---|---|---|---|
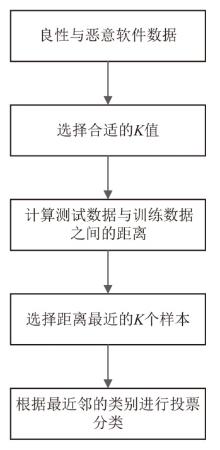
| KNN | 文献[ | 原理简单且容易实现、对特征向量的适配性好 | 依赖样本分布均匀性、易受特征维度影响、样本量过大时距离计算耗时 |
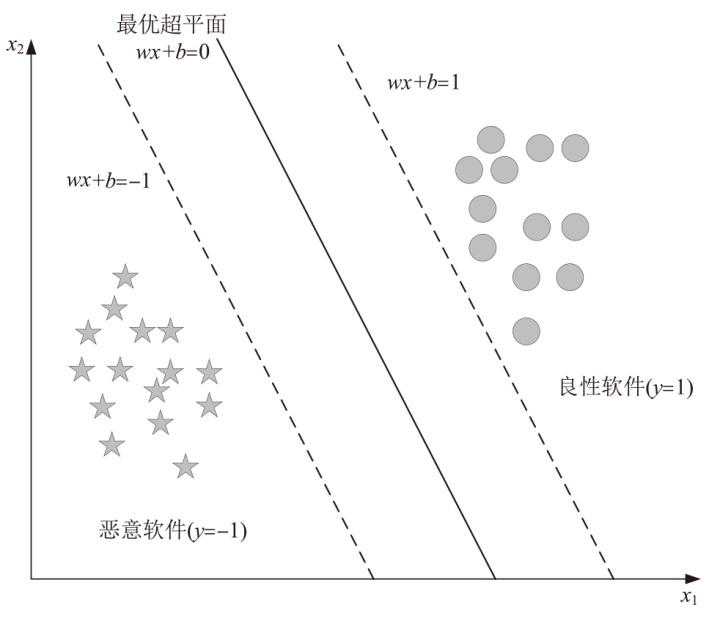
| SVM | 文献[ | 在少样本场景鲁棒性高、处理非线性特征能力强 | 参数调优复杂、依赖数据的高质量标签、易受对抗攻击影响 |
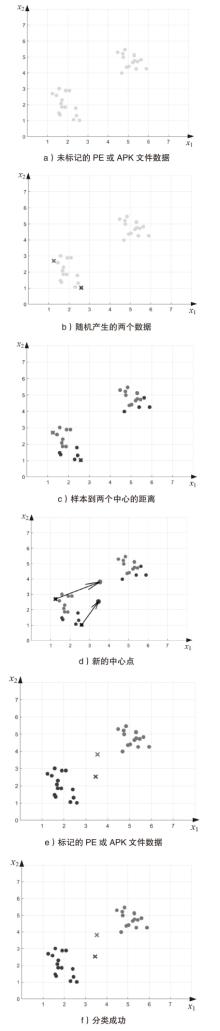
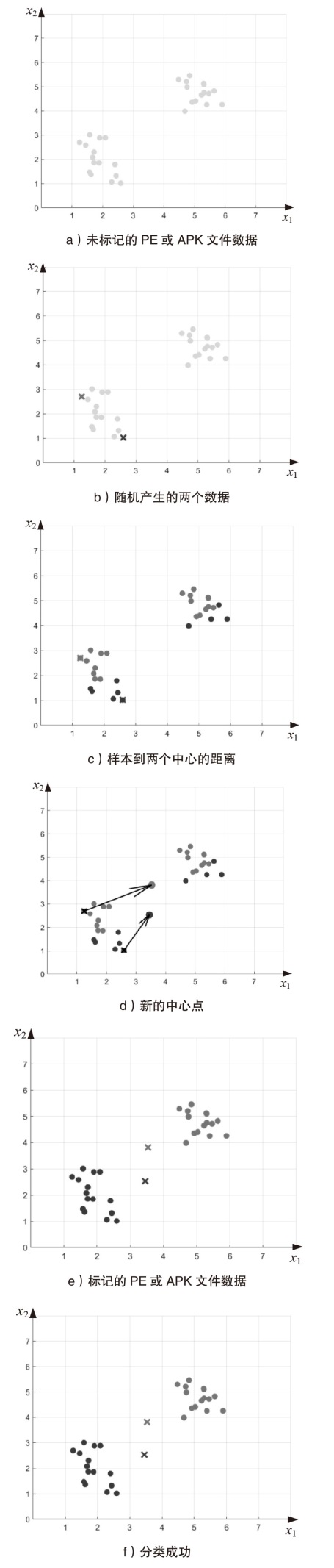
| 聚类方法 | 文献[ | 无需标注数据、减少人工分析工作量、适合 新型变种恶意检测 | 可解释性低、稳定性差、易出现簇边界模糊 |
| 降维方法 | 文献[ | 缓解“维度灾难”、 减少计算与存储负担 | 合适的方法与有效的降维匹配困难、对特征的分布敏感 |
| 集成方法 | 文献[ | 对抗鲁棒性高、过拟合风险低、泛化能力强 | 方法复杂度高、依赖基学习器的质量、可解释性弱 |
表2
基于深度学习的检测方法对比
| 方法 | 典型方案 | 优点 | 缺点 |
|---|---|---|---|
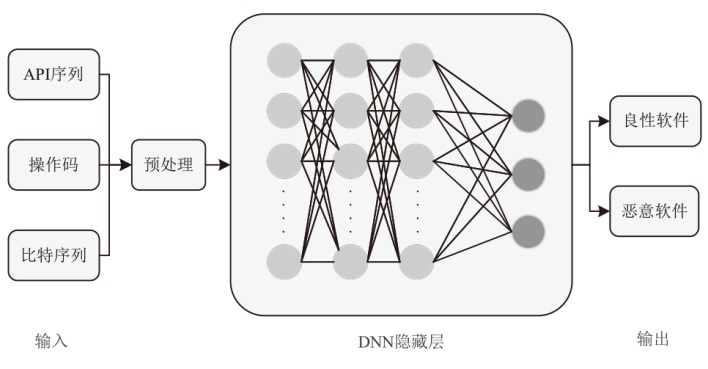
| DNN | 文献[ | 结构自适应、语义建模能力强 | 大规模标注数据与算力的依赖较强、 可解释性差 |
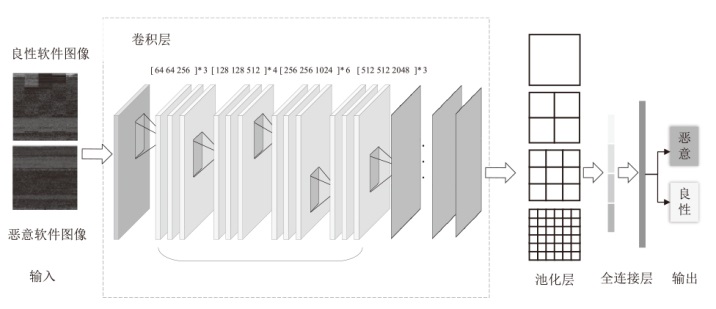
| CNN | 文献[ | 特征学习自动化、对图像结构高敏感、泛化能力强 | 全局捕捉能力差、 模型易过拟合、抗对抗样本弱 |
| RNN | 文献[ | 序列短程建模能力强、局部依赖捕捉能力强 | 对抗性弱、对长序列处理能力差 |
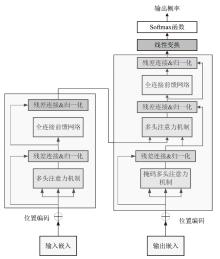
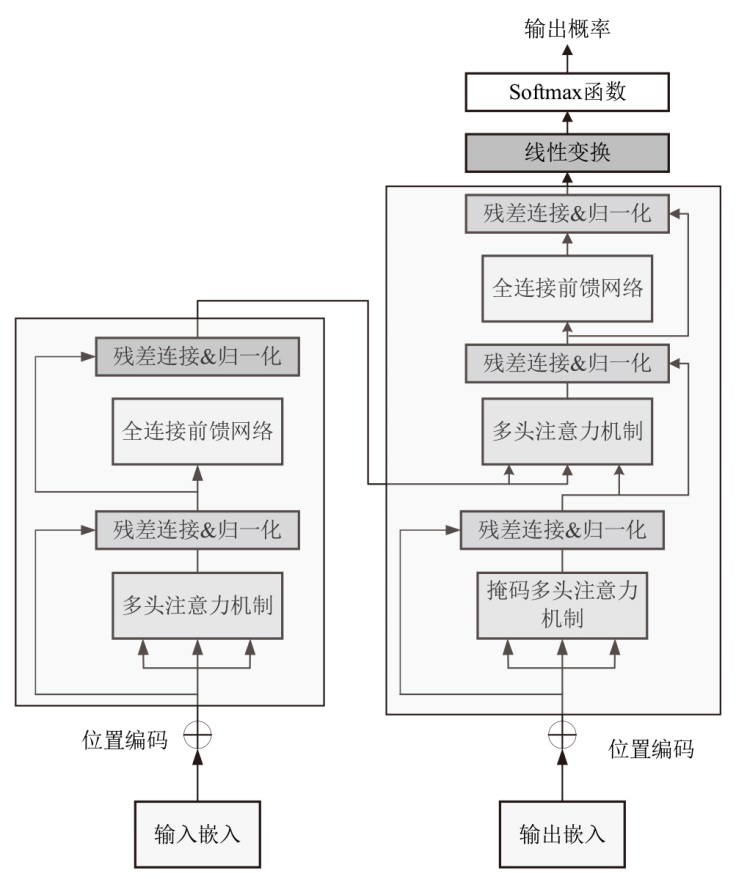
| Transformer | 文献[ | 全局依赖捕捉能力强、上下文理解能力好 | 对长序列敏感、模型训练量大 |
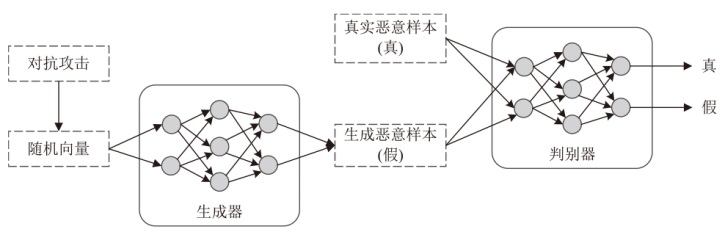
| GAN | 文献[ | 增强样本多样性、提升鲁棒性、辅助零日检测 | 训练不稳定、伪样本风险高、计算开销大 |
| 多模态 | 文献[ | 特征互补性强、鲁棒性高、检测性能好 | 模型结构复杂、模态对齐难度大 |
表4
3种检测分类方法的比较
| 方法 | 优点 | 缺点 | 改进方向 | 应用场景 |
|---|---|---|---|---|
| 基于传统机器学习的方法 | 处理非线性关系能力强,能适应 新型变种恶意行为,还能处理高维特征以及大规模数据,在保持精度的同时降低模型的训练量 | 高度依赖手工特征质量,泛化能力差,易受对抗样本影响,产生误报和漏报,且模型易老化,难以应对概念漂移 | 通过主动学习、数据增强等方式缓解高质量标注数据获取困难的问题,并持续优化特征提取流程以应对对抗性攻击和数据漂移问题 | 移动端、PC端的 恶意软件 识别 |
| 基于深度学习的方法 | 深度学习架构能自动提取高维、 复杂特征,支持API序列、图像等多个模态输入,在大规模云环境下可高效处理海量样本,准确率高 | 训练需大量样本及高性能硬件支持,模型调参过程复杂,可解释性差,还存在 过拟合风险 | 进行模型压缩及轻量化模型构建,引入可解释技术(如XAI、SHAP等)提升模型的可解释性 | 大规模 样本检测、多模态 分析等 |
| 基于图表示学习的方法 | 利用调用图、控制流图等结构捕捉程序之间的复杂依赖关系,擅长 识别家族变种和行为异常,且具备一定可解释性,图结构便于追踪恶意逻辑路径 | 特征提取和图构建代价高,资源消耗大,且易受图结构对抗攻击影响,泛化能力有限 | 引入深度学习融合图结构,提升结构学习,同时利用剪枝、规约来优化图结构,还可进行对抗性训练增强鲁棒性 | 恶意家族溯源及变种恶意软件的识别 |
| [1] | YE Yanfang, LI Tao, ADJEROH D, et al. A Survey on Malware Detection Using Data Mining Techniques[J]. ACM Computing Surveys (CSUR), 2017, 50(3): 1-40. |
| [2] | ANTON K. Mobile Malware Evolution in 2024[EB/OL].(2025-03-03)[2025-08-18]. https://securelist.com/mobile-threat-report-2024/115494. |
| [3] | SHIJO P V, SALIM A. Integrated Static and Dynamic Analysis for Malware Detection[J]. Procedia Computer Science, 2015, 46: 804-811. |
| [4] | KINABLE J, KOSTAKIS O. Malware Classification Based on Call Graph Clustering[J]. Journal in Computer Virology, 2011, 7(4): 233-245. |
| [5] | OR-MEIR O, NISSIM N, ELOVICI Y, et al. Dynamic Malware Analysis in the Modern Era—A State of the Art Survey[J]. ACM Computing Surveys (CSUR), 2019, 52(5): 1-48. |
| [6] | SAEED I A, SELAMAT A, ABUAGOUB A M A. A Survey on Malware and Malware Detection Systems[EB/OL].(2013-04-23)[2025-08-18]. https://www.researchgate.net/profile/Imtithal-Saeed/publication/272238656_A_Survey_on_Malwares_and_Malware_Detection_Systems/links/566284c608ae192bbf8cf1a5/A-Survey-on-Malwares-and-Malware-Detection-Systems.pdf. |
| [7] | KRAMER S, BRADFIELD J C. A General Definition of Malware[J]. Journal in Computer Virology, 2010, 6(2): 105-114. |
| [8] | MARION J Y. Ransomware: Extortion is My Business[J]. Communications of the ACM, 2025, 68(5): 36-47. |
| [9] | WANG Siyu, WU Haiyong, LU Ning, et al. Atsdetector: An Android Trojan Spyware Detection Approach with Multi-Features[EB/OL].(2025-03)[2025-08-18]. https://www.sciencedirect.com/science/article/pii/S016740482400525X. |
| [10] | SERAJ S, PAVLIDIS M, TROVATI M, et al. Maddroid: Malicious Adware Detection in Android Using Deep Learning[J]. Journal of Cyber Security Technology, 2024, 8(3): 163-190. |
| [11] | YANG Wei, KONG Deguang, XIE Tao, et al. Malware Detection in Adversarial Settings: Exploiting Feature Evolutions and Confusions in Android Apps[C]// Springer.The 33rd Annual Computer Security Applications Conference. Heidelberg: Springer, 2017: 288-302. |
| [12] | LI Xun, LIU Lei, LIU Yuzhou, et al. Multimodal Fusion for Android Malware Detection Based on Large Pre-Trained Models[EB/OL].(2025-04-03)[2025-08-18]. https://ieeexplore.ieee.org/abstract/document/10948385/. |
| [13] | ANAND A, SINGH J P, SINGH A K. Smali Code-Based Deep Learning Model for Android Malware Detection[J]. The Journal of Supercomputing, 2025, 81(4): 1-31. |
| [14] | OU Fan, XU Jian. S3Feature:A Static Sensitive Subgraph-Based Feature for Android Malware Detection[EB/OL].(2022-02-16)[2025-08-18]. https://www.sciencedirect.com/science/article/pii/S0167404821003370. |
| [15] | HUANG Hong, HUANG Weitao, ZHOU Yinghang, et al. Fedroid: A Lightweight and Interpretable Machine Learning-Based Android Malware Detection System[EB/OL].(2025-02-25)[2025-08-18]. https://link.springer.com/article/10.1007/s10586-024-04865-x. |
| [16] | JEON J, JEONG B, BAEK S, et al. Static Multi Feature-Based Malware Detection Using Multi SPP-Net in Smart Iot Environments[J]. IEEE Transactions on Information Forensics and Security, 2024, 19: 2487-2500. |
| [17] | KIRAZ O, DOGRU I A. Visualising Static Features and Classifying Android Malware Using a Convolutional Neural Network Approach[EB/OL].(2024-04-24)[2025-08-18]. https://www.mdpi.com/2076-3417/14/11/4772. |
| [18] | CUI Yuning, SUN Yi, LIN Zhaowen. Droidhook: A Novel API-Hook Based Android Malware Dynamic Analysis Sandbox[EB/OL].(2023-02-24)[2025-08-18]. https://link.springer.com/article/10.1007/s10515-023-00378-w. |
| [19] | AGGARWAL S, TROIA F D. Malware Classification Using Dynamically Extracted API Call Embeddings[EB/OL].(2024-05-20)[2025-08-18]. https://www.mdpi.com/2076-3417/14/13/5731. |
| [20] | YAN Pei, TAN Shunquan, WANG Miaohui, et al. Enhanced Dynamic Analysis for Malware Detection with Gradient Attack[EB/OL].(2024-10-07)[2025-08-18]. https://ieeexplore.ieee.org/abstract/document/10706706/. |
| [21] | THAKUR P, KANSAL V, RISHIWAL V. Hybrid Deep Learning Approach Based on LSTM and CNN for Malware Detection[J]. Wireless Personal Communications, 2024, 136(3): 1879-1901. |
| [22] | TRIZNA D, DEMETRIO L, BIGGIO B, et al. Nebula: Self-Attention for Dynamic Malware Analysis[J]. IEEE Transactions on Information Forensics and Security, 2024, 19: 6155-6167. |
| [23] | ZHANG Sanfeng, SU Heng, LIU Hongxian, et al. MPDroid: A Multimodal Pre-Training Android Malware Detection Method with Static and Dynamic Features[EB/OL].(2025-03)[2025-08-18]. https://www.sciencedirect.com/science/article/pii/S0167404824005686. |
| [24] | SONG Yafei, ZHANG Dandan, WANG Jian, et al. Application of Deep Learning in Malware Detection: A Review[EB/OL].(2025-04-22)[2025-08-18]. https://link.springer.com/article/10.1186/s40537-025-01157-y. |
| [25] | SENANAYAKE J, KALUTARAGE H, AL-KADRI M O. Android Mobile Malware Detection Using Machine Learning: A Systematic Review[EB/OL].(2021-05-29)[2025-08-18]. https://www.mdpi.com/2079-9292/10/13/1606. |
| [26] | BILOT T, MADHOUN N E, AGHA K A, et al. A Survey on Malware Detection with Graph Representation Learning[J]. ACM Computing Surveys, 2024, 56(11): 1-36. |
| [27] | BABBAR H, RANI S, SAH D K, et al. Detection of Android Malware in the Internet of Things through the K-Nearest Neighbor Algorithm[EB/OL].(2023-07-20)[2025-08-18]. https://www.mdpi.com/1424-8220/23/16/7256. |
| [28] | DOLESI K, STEINBACH E, VELASQUEZ A, et al. A Machine Learning Approach to Ransomware Detection Using Opcode Features and K-Nearest Neighbors on Windows[EB/OL].(2024-10-11)[2025-08-18]. https://www.techrxiv.org/doi/full/10.36227/techrxiv.172926410.04244699. |
| [29] | GU Xiaoyao, YAN Jichang. Hierarchical K-Nearest Neighbors for Ransomware Detection Using Opcode Sequences[EB/OL].(2024-06-11)[2025-08-18]. https://www.techrxiv.org/doi/full/10.36227/techrxiv.171838524.46252988. |
| [30] | AL S A, ABUALHAJ M M, SHAMBOUR Q Y, et al. Enhancing Malware Detection Performance: Leveraging K-Nearest Neighbors with Firefly Optimization Algorithm[J]. Multimedia Tools and Applications, 2025, 84(12): 10071-10094. |
| [31] | ZHOU Shuncheng, LI Honghui, FU Xueliang, et al. A Novel Malware Detection Model in the Software Supply Chain Based on LSTM and SVMS[EB/OL].(2024-07-13)[2025-08-18]. https://www.mdpi.com/2076-3417/14/15/6678. |
| [32] | FARFOURA M E, MASHAL I, ALKHATIB A, et al. A Lightweight Machine Learning Methods for Malware Classification[EB/OL].(2024-10-10)[2025-08-18]. https://link.springer.com/article/10.1007/s10586-024-04755-2. |
| [33] | LI Junhao, HE Junjiang, LI Wenshan, et al. Syndroid: An Adaptive Enhanced Android Malware Classification Method Based on CTGAN-SVM[EB/OL].(2023-07-26)[2025-08-18]. https://www.sciencedirect.com/science/article/pii/S016740482300514X. |
| [34] | RIZVI S K J, ASLAM W, SHAHZAD M, et al. PROUD-MAL: Static Analysis-Based Progressive Framework for Deep Unsupervised Malware Classification of Windows Portable Executable[J]. Complex & Intelligent Systems, 2022, 8(1): 673-685. |
| [35] | CHAKRABORTY T, PIERAZZI F, SUBRAHMANIAN V S. EC2: Ensemble Clustering and Classification for Predicting Android Malware Families[J]. IEEE Transactions on Dependable and Secure Computing, 2017, 17(2): 262-277. |
| [36] | HAN Y S, SEO H B, YOON M K. Detecting Internet-of-Things Malware on Evidence Generation[EB/OL].(2024-08-06)[2025-08-18]. https://ieeexplore.ieee.org/abstract/document/10623818/. |
| [37] | LIU Zhen, WANG Ruoyu, JAPKOWICZ N, et al. Research on Unsupervised Feature Learning for Android Malware Detection Based on Restricted Boltzmann Machines[J]. Future Generation Computer Systems, 2021, 120: 91-108. |
| [38] | GUNDUZ H. Malware Detection Framework Based on Graph Variational Autoencoder Extracted Embeddings from API-Call Graphs[EB/OL].(2022-05-18)[2025-08-18]. https://peerj.com/articles/cs-988/. |
| [39] | DONG Shi, SHU Longhui, NIE Shan. Android Malware Detection Method Based on CNN and DNN Bybrid Mechanism[J]. IEEE Transactions on Industrial Informatics, 2024, 20(5): 7744-7753. |
| [40] | LIU Guiyun, ZHANG Jiezhao, ZHONG Xiaojing, et al. Hybrid Optimal Control for Malware Propagation in UAV-WSN System: A Stacking Ensemble Learning Control Algorithm[J]. IEEE Internet of Things Journal, 2024, 11(11): 36549-36568. |
| [41] | CHEN Jiaqi, YUAN Chong, LI Jiashuo, et al. ELAMD: An Ensemble Learning Framework for Adversarial Malware Defense[EB/OL].(2023-05-17)[2025-08-18]. https://www.sciencedirect.com/science/article/pii/S2214212623000923. |
| [42] | ZHU Huijuan, LI Yang, WANG Liangmin, et al. A Multi-Model Ensemble Learning Framework for Imbalanced Android Malware Detection[EB/OL].(2023-07-05)[2025-08-18]. https://www.sciencedirect.com/science/article/pii/S0957417423014549. |
| [43] | VASHISHTHA L K, CHATTERJEE K, ROUT S S. An Ensemble Approach for Advance Malware Memory Analysis Using Image Classification Techniques[EB/OL].(2023-09-18)[2025-08-18]. https://www.sciencedirect.com/science/article/pii/S221421262300145X. |
| [44] | SINGH S, KRISHNAN D, VAZIRANI V, et al. Deep Hybrid Approach with Sequential Feature Extraction and Classification for Robust Malware Detection[EB/OL].(2024-09-26)[2025-08-18]. https://www.sciencedirect.com/science/article/pii/S1110866524001026. |
| [45] | THAKUR P, KANSAL V, RISHIWAL V. Hybrid Deep Learning Approach Based on LSTM and CNN for Malware Detection[J]. Wireless Personal Communications, 2024, 136(3): 1879-1901. |
| [46] | MORENO-TORRES J G, RAEDER T, ALAIZ-RODRIGUEZ R, et al. A Unifying View on Dataset Shift in Classification[J]. Pattern Recognition, 2012, 45(1): 521-530. |
| [47] | SHAHIDI S M, SHAKERI H, JALALI M. A Semantic Malware Detection Model Based on the GMDH Neural Networks[EB/OL].(2021-05-08)[2025-08-18]. https://www.sciencedirect.com/science/article/pii/S0045790621001075. |
| [48] | ZHAO Wenxiang, WU Juntao, MENG Zhaoyi. Apppoet: Large Language Model Based Android Malware Detection via Multi-View Prompt Engineering[EB/OL].(2025-03-16)[2025-08-18]. https://www.sciencedirect.com/science/article/pii/S0957417424024138. |
| [49] | OpenAI. Product and Research Updates of OpenAI[EB/OL].(2025-10-29)[2025-08-18]. Https://Openai.Com/. |
| [50] | ZHANG Yunchun, LI Haorui, ZHENG Yang, et al. Enhanced DNNs for Malware Classification with GAN-Based Adversarial Training[J]. Journal of Computer Virology and Hacking Techniques, 2021, 17(2): 153-163. |
| [51] | LI Qi, MI Jiaxin, LI Weishi, et al. CNN-Based Malware Variants Detection Method for Internet of Things[J]. IEEE Internet of Things Journal, 2021, 8(12): 16946-16962. |
| [52] | BENSAOUD A, KALITA J. CNN-LSTM and Transfer Learning Models for Malware Classification Based on Opcodes and API Calls[EB/OL].(2024-04-26)[2025-08-18]. https://www.sciencedirect.com/science/article/pii/S0950705124001783. |
| [53] | KHAN S H, ALAHMADI T J, ULLAH W, et al. A New Deep Boosted CNN and Ensemble Learning Based Iot Malware Detection[EB/OL].(2023-10-08)[2025-08-18]. https://www.sciencedirect.com/science/article/pii/S016740482300295X. |
| [54] | HABIBI O, CHEMMAKHA M, LAZAAR M. Performance Evaluation of CNN and Pre-Trained Models for Malware Classification[J]. Arabian Journal for Science and Engineering, 2023, 48(8): 10355-10369. |
| [55] | JHA S, PRASHAR D, LONG H V, et al. Recurrent Neural Network for Detecting Malware[EB/OL].(2020-12-18)[2025-08-18]. https://www.sciencedirect.com/science/article/pii/S0167404820303102. |
| [56] | CEN Mingcan, JIANG F, DOSS R. Ransoguard: A RNN-Based Framework Leveraging Pre-Attack Sensitive APIs for Early Ransomware Detection[EB/OL].(2025-03-16)[2025-08-18]. https://www.sciencedirect.com/science/article/pii/S0167404824005996. |
| [57] | LUO Xi, FAN Honghui, YIN Lihua, et al. CAG-Malconv: A Byte-Level Malware Detection Method with CBAM and Attention-GRU[EB/OL].(2024-07-08)[2025-08-18]. https://ieeexplore.ieee.org/abstract/document/10589435/. |
| [58] | ABDULLAH M A, YU Y, ADU K, et al. HCL-Classifier: CNN and LSTM Based Hybrid Malware Classifier for Internet of Things (Iot)[J]. Future Generation Computer Systems, 2023, 142: 41-58. |
| [59] | OWOH N, ADEJOH J, HOSSEINZADEH S, et al. Malware Detection Based on API Call Sequence Analysis: A Gated Recurrent Unit-Generative Adversarial Network Model Approach[EB/OL].(2024-09-02)[2025-08-18]. https://www.mdpi.com/1999-5903/16/10/369. |
| [60] | WU Yinwei, LI Meijin, ZENG Qi, et al. Droidrl: Feature Selection for Android Malware Detection with Reinforcement Learning[EB/OL].(2023-05-16)[2025-08-18]. https://www.sciencedirect.com/science/article/pii/S0167404823000366. |
| [61] | QIAN Liping, LIN Cong. Channel Features and API Frequency-Based Transformer Model for Malware Identification[EB/OL].(2023-12-07)[2025-08-18]. https://www.mdpi.com/1424-8220/24/2/580. |
| [62] | WANG Peng, LIN Tongcan, WU Di, et al. TTDAT: Two-Step Training Dual Attention Transformer for Malware Classification Based on API Call Sequences[EB/OL].(2023-11-11)[2025-08-18]. https://www.mdpi.com/2076-3417/14/1/92. |
| [63] | DEMIRKIRAN F, ÇAYIR A, UNAL U, et al. An Ensemble of Pre-Trained Transformer Models for Imbalanced Multiclass Malware Classification[EB/OL].(2022-10-16)[2025-08-18]. https://www.sciencedirect.com/science/article/pii/S0167404822002401. |
| [64] | FENG Pengbin, GAI Le, YANG Li, et al. DawnGNN: Documentation Augmented Windows Malware Detection Using Graph Neural Network[EB/OL].(2024-05-13)[2025-08-18]. https://www.sciencedirect.com/science/article/pii/S0167404824000890. |
| [65] | DENG Xiaoheng, WANG Zhe, PEI Xinjun, et al. Transmalde: An Effective Transformer Based Hierarchical Framework for Iot Malware Detection[J]. IEEE Transactions on Network Science and Engineering, 2023, 11(1): 140-151. |
| [66] | SHARMA O, SHARMA A, KALIA A. MIGAN: GAN for Facilitating Malware Image Synthesis with Improved Malware Classification on Novel Dataset[EB/OL].(2024-05-18)[2025-08-18]. https://www.sciencedirect.com/science/article/pii/S0957417423031809. |
| [67] | KIM J Y, BU S J, CHO S B. Malware Detection Using Deep Transferred Generative Adversarial Networks[C]// Springer. International Conference on Neural Information Processing. Heidelberg: Springer, 2017: 556-564. |
| [68] | GAO Xiaowei, HU Changzhen, SHAN Chu, et al. Malicage: A Packed Malware Family Classification Framework Based on DNN and GAN[EB/OL].(2022-08-12)[2025-08-18]. https://www.sciencedirect.com/science/article/pii/S2214212622001296. |
| [69] | ZHANG Yunchun, LI Haorui, ZHENG Yang, et al. Enhanced DNNs for Malware Classification with GAN-Based Adversarial Training[J]. Journal of Computer Virology and Hacking Techniques, 2021, 17(2): 153-163. |
| [70] | KIM T G, KANG B J, RHO M, et al. A Multimodal Deep Learning Method for Android Malware Detection Using Various Features[J]. IEEE Transactions on Information Forensics and Security, 2018, 14(3): 773-788. |
| [71] | MENG Yi, LUKTARHAN N, YANG Xiaotong, et al. Gbadroid: An Android Malware Detection Method Based on Multi-View Feature Fusion[EB/OL].(2025-02-14)[2025-08-18]. https://link.springer.com/article/10.1007/s11227-025-06977-6. |
| [72] | CHEN Shaojie, LANG Bo, LIU Hongyu, et al. Android Malware Detection Method Based on Graph Attention Networks and Deep Fusion of Multimodal Features[EB/OL].(2024-05-06)[2025-08-18]. https://www.sciencedirect.com/science/article/pii/S095741742302119X. |
| [73] | SONG Yucai, CHEN Yang, LANG Bo, et al. Topic Model Based Android Malware Detection[C]// Springer. International Conference on Security, Privacy and Anonymity in Computation, Communication and Storage. Heidelberg: Springer, 2019: 384-396. |
| [74] | PENG Hao, YANG Jieshuai, ZHAO Dandan, et al. Malgne: Enhancing the Performance and Efficiency of Cfg-Based Malware Detector by Graph Node Embedding in Low Dimension Space[J]. IEEE Transactions on Information Forensics and Security, 2024, 19: 4881-4896. |
| [75] | WU Xiaowang, WANG Yan, FANG Yong, et al. Embedding Vector Generation Based on Function Call Graph for Effective Malware Detection and Classification[J]. Neural Computing and Applications, 2022, 34(11): 8643-8656. |
| [76] | PEKTAŞ A, ACARMAN T. Deep Learning for Effective Android Malware Detection Using API Call Graph Embeddings[J]. Soft Computing, 2020, 24(2): 1027-1043. |
| [77] | TANG Lihong, CHEN Xiao, WEN Sheng, et al. Demystifying the Evolution of Android Malware Variants[J]. IEEE Transactions on Dependable and Secure Computing, 2023, 21(4): 3324-3341. |
| [78] | AMER E, ZELINKA I. A Dynamic Windows Malware Detection and Prediction Method Based on Contextual Understanding of API Call Sequence[EB/OL].(2020-05-16)[2025-08-18]. https://www.sciencedirect.com/science/article/pii/S0167404820300444. |
| [79] | GAO Han, CHENG Shaoyin, ZHANG Weiming. Gdroid: Android Malware Detection and Classification with Graph Convolutional Network[EB/OL].(2021-07-18)[2025-08-18]. https://www.sciencedirect.com/science/article/pii/S0167404821000882. |
| [80] | YANG Jin, LIANG Huijia, REN Hang, et al. SAC: Collaborative Learning of Structure and Content Features for Android Malware Detection Framework[EB/OL].(2025-07-06)[2025-08-18]. https://www.sciencedirect.com/science/article/pii/S0925231225007258. |
| [81] | GUO Wenjie, DU Wenbiao, YANG Xiuqi, et al. Malhapgnn: An Enhanced Call Graph-Based Malware Detection Framework Using Hierarchical Attention Pooling Graph Neural Network[EB/OL].(2025-01-10)[2025-08-18]. https://www.mdpi.com/1424-8220/25/2/374. |
| [82] | MENG Yi, LUKTARHAN N, YANG Xiaotong, et al. GBAdroid: An Android Malware Detection Method Based on Multi-View Feature Fusion[EB/OL].(2025-02-14)[2025-08-18]. https://link.springer.com/article/10.1007/s11227-025-06977-6. |
| [83] | GU Jintao, ZHU Hongliang, HAN Zewei, et al. GSEdroid: GNN-Based Android Malware Detection Framework Using Lightweight Semantic Embedding[EB/OL].(2024-05-16)[2025-08-18]. https://www.sciencedirect.com/science/article/pii/S0167404824001081. |
| [84] | ZHANG Heyu, LI Binglong, YU Shilong, et al. Procgcn: Detecting Malicious Process in Memory Based on DGCNN[EB/OL].(2024-06-21)[2025-08-18]. https://peerj.com/articles/cs-2193/. |
| [85] | PENG Hao, YU Zehao, ZHAO Dandan, et al. Evading Control Flow Graph Based GNN Malware Detectors via Active Opcode Insertion Method with Maliciousness Preserving[EB/OL].(2025-03-17)[2025-08-18]. https://www.nature.com/articles/s41598-025-92023-7. |
| [86] | SUN Tiezhu, DAOUDI N, PIAN Weiguo, et al. Temporal-Incremental Learning for Android Malware Detection[J]. ACM Transactions on Software Engineering and Methodology, 2025, 34(4): 1-30. |
| [87] | RUNZE M, YIN Shangnan, FENG Xia, et al. A Lightweight Deep Learning-Based Android Malware Detection Framework[EB/OL].(2024-12-18)[2025-08-18]. https://www.sciencedirect.com/science/article/pii/S0957417424015008. |
| [88] | FERDOUS J, ISLAM R, MAHBOUBI A, et al. A Survey on ML Techniques for Multi-Platform Malware Detection: Securing PC, Mobile Devices, Iot, and Cloud Environments[EB/OL].(2025-02-13)[2025-08-18]. https://www.mdpi.com/1424-8220/25/4/1153. |
| [89] | GOPINATH M, SETHURAMAN S C. A Comprehensive Survey on Deep Learning Based Malware Detection Techniques[EB/OL].(2022-12-08)[2025-08-18]. https://www.sciencedirect.com/science/article/pii/S1574013722000636. |
| [1] | 徐衍微, 涂敏, 张亮. 深度伪造语音真实性鉴定研究综述[J]. 信息网络安全, 2026, 26(3): 367-377. |
| [2] | 秦振凯, 罗起宁, 农熏衣, 于小川, 操晓春. 融合性别与情绪强度提示特征的多层次语音情感识别模型[J]. 信息网络安全, 2026, 26(3): 420-431. |
| [3] | 王腾, 樊坤渭, 张瑶. 面向分布式学习的多密钥同态加密与差分隐私融合方案[J]. 信息网络安全, 2026, 26(2): 236-250. |
| [4] | 王亚杰, 陆锦标, 谭冬黎, 范青, 祝烈煌. 面向胶囊网络的成员推理风险评估[J]. 信息网络安全, 2026, 26(1): 38-48. |
| [5] | 徐茹枝, 武晓欣, 吕畅冉. 基于Transformer的超分辨率网络对抗样本防御方法研究[J]. 信息网络安全, 2025, 25(9): 1367-1376. |
| [6] | 陈咏豪, 蔡满春, 张溢文, 彭舒凡, 姚利峰, 朱懿. 多尺度多层次特征融合的深度伪造人脸检测方法[J]. 信息网络安全, 2025, 25(9): 1456-1464. |
| [7] | 王新猛, 陈俊雹, 杨一涛, 李文瑾, 顾杜娟. 贝叶斯优化的DAE-MLP恶意流量识别模型[J]. 信息网络安全, 2025, 25(9): 1465-1472. |
| [8] | 金志刚, 李紫梦, 陈旭阳, 刘泽培. 面向数据不平衡的网络入侵检测系统研究综述[J]. 信息网络安全, 2025, 25(8): 1240-1253. |
| [9] | 王钢, 高雲鹏, 杨松儒, 孙立涛, 刘乃维. 基于深度学习的加密恶意流量检测方法研究综述[J]. 信息网络安全, 2025, 25(8): 1276-1301. |
| [10] | 魏松杰, 吴琴琴, 袁军翼. 基于运行参数增强API序列的勒索软件动态检测方法研究[J]. 信息网络安全, 2025, 25(5): 713-721. |
| [11] | 张兴兰, 陶科锦. 基于高阶特征与重要通道的通用性扰动生成方法[J]. 信息网络安全, 2025, 25(5): 767-777. |
| [12] | 金增旺, 江令洋, 丁俊怡, 张慧翔, 赵波, 方鹏飞. 工业控制系统安全研究综述[J]. 信息网络安全, 2025, 25(3): 341-363. |
| [13] | 陈红松, 刘新蕊, 陶子美, 王志恒. 基于深度学习的时序数据异常检测研究综述[J]. 信息网络安全, 2025, 25(3): 364-391. |
| [14] | 李海龙, 崔治安, 沈燮阳. 网络流量特征的异常分析与检测方法综述[J]. 信息网络安全, 2025, 25(2): 194-214. |
| [15] | 武浩莹, 陈杰, 刘君. 改进Simon32/64和Simeck32/64神经网络差分区分器[J]. 信息网络安全, 2025, 25(2): 249-259. |
| 阅读次数 | ||||||
|
全文 |
|
|||||
|
摘要 |
|
|||||