信息网络安全 ›› 2026, Vol. 26 ›› Issue (3): 378-388.doi: 10.3969/j.issn.1671-1122.2026.03.004
DiffGuard:基于扩散模型与自适应序列学习的网络流量异常检测框架
- 浙江警察学院信息网络安全学院,杭州 310053
-
收稿日期:2025-07-07出版日期:2026-03-10发布日期:2026-03-30 -
通讯作者:丁伟杰 E-mail:dingweijie@zjjcxy.cn -
作者简介:胡文涛(1995—),男,浙江,讲师,博士,主要研究方向为人工智能、数据治理|丁伟杰(1980—),男,河南,教授,博士,主要研究方向为人工智能 -
基金资助:国家重点研发计划(2024YFF0618800);“十四五”第二批本科省级教学改革重点项目(ZGZD2024080)
DiffGuard: Network Traffic Anomaly Detection Based on Diffusion Models and Adaptive Sequence Learning
- College of Information and Cyber Security, Zhejiang Police College, Hangzhou 310053, China
-
Received:2025-07-07Online:2026-03-10Published:2026-03-30
摘要:
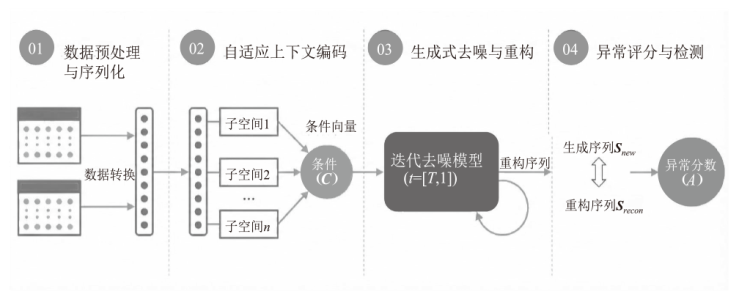
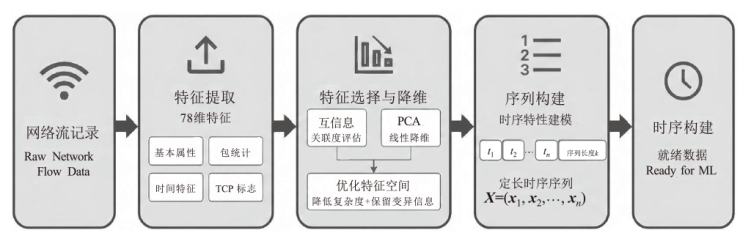
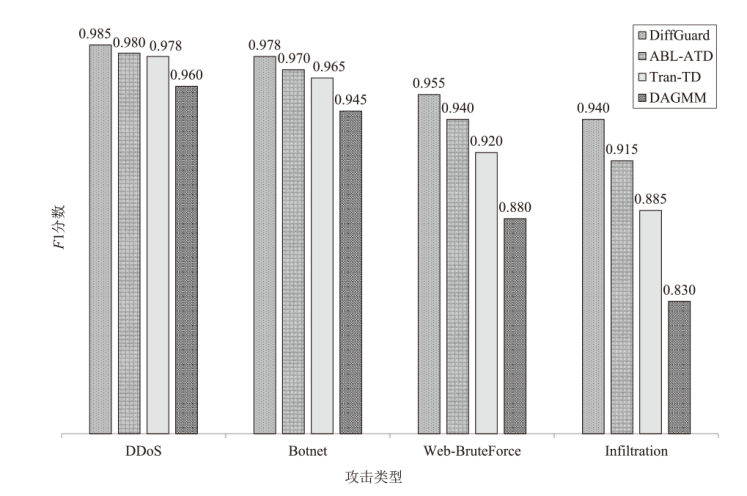
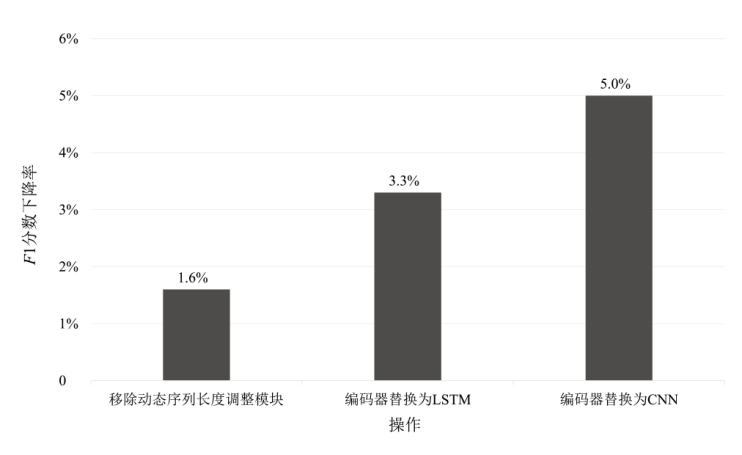
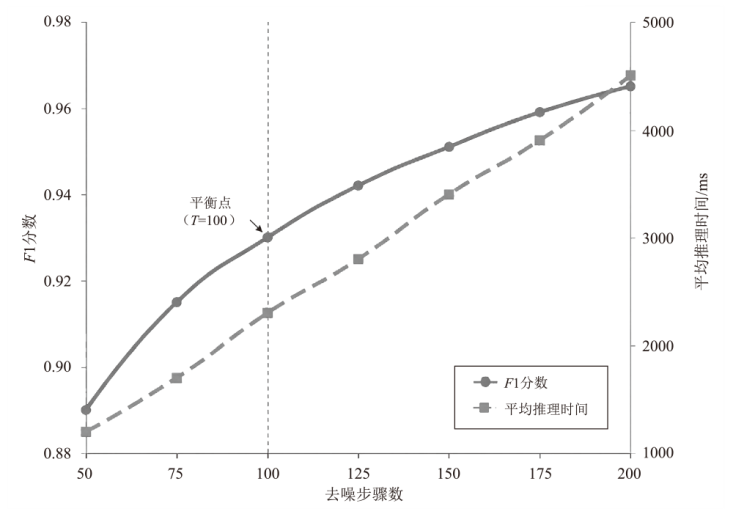
针对传统深度学习方法在处理高维、动态网络流量时的检测瓶颈,文章提出一种无监督网络流量异常检测框架DiffGuard。该框架将异常检测重构为生成式修复任务,区别于基于重构的方法,其核心在于融合扩散模型的生成式去噪能力与自适应序列建模技术。DiffGuard通过以输入序列上下文为条件的反向去噪过程,从潜在异常序列中恢复其正常形态,并以修复前后的重构误差量化异常程度。为增强时序建模,DiffGuard引入基于Transformer的条件编码器捕捉长期依赖,同时,设计基于流量熵的自适应序列长度机制,动态调整分析窗口以适应流量变化。实验结果表明,DiffGuard在CIC-IDS-2018数据集上的F1分数达到0.965,优于其他主流方法,且在Web渗透等隐蔽攻击检测上的F1分数达到0.955。实验结果验证了DiffGuard在复杂网络安全场景中的有效性与应用潜力。
中图分类号:
引用本文
胡文涛, 丁伟杰. DiffGuard:基于扩散模型与自适应序列学习的网络流量异常检测框架[J]. 信息网络安全, 2026, 26(3): 378-388.
HU Wentao, DING Weijie. DiffGuard: Network Traffic Anomaly Detection Based on Diffusion Models and Adaptive Sequence Learning[J]. Netinfo Security, 2026, 26(3): 378-388.
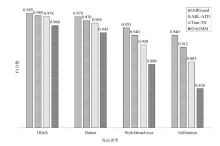
表2
不同算法实验结果
| 算法 | CIC-IDS-2018数据集 | CIC-DDoS2019数据集 | ||||
|---|---|---|---|---|---|---|
| F1分数 | 精确率 | 召回率 | F1分数 | 精确率 | 召回率 | |
| 隔离森林 | 0.812 | 0.835 | 0.791 | 0.856 | 0.871 | 0.842 |
| DAGMM | 0.901 | 0.910 | 0.892 | 0.925 | 0.931 | 0.919 |
| AnoGAN | 0.919 | 0.908 | 0.931 | 0.933 | 0.931 | 0.937 |
| Tran-AD | 0.936 | 0.941 | 0.931 | 0.945 | 0.953 | 0.937 |
| ABL-ATD | 0.952 | 0.958 | 0.946 | 0.961 | 0.969 | 0.953 |
| DiffGuard | 0.965 | 0.961 | 0.969 | 0.972 | 0.967 | 0.977 |
| [1] | JIANG Jiansen, SHAO An. “Fengqiao Experience” in the New Era: From the Governance Programme to Governance Paradigm[J]. Journal of Zhejiang Police College, 2023(5): 3-19. |
| 蒋建森, 邵安. 新时代“枫桥经验”:从治理方案走向治理范式[J]. 浙江警察学院学报, 2023(5):3-19. | |
| [2] | HU Wentao, XU Jingkai, DING Weijie. Unsupervised Network Traffic Anomaly Detection Based on Abductive Learning[J]. Netinfo Security, 2024, 24(11): 1675-1684. |
| 胡文涛, 徐靖凯, 丁伟杰. 基于溯因学习的无监督网络流量异常检测[J]. 信息网络安全, 2024, 24(11):1675-1684. | |
| [3] | WALLING S, LODH S. Network Intrusion Detection System for IoT Security Using Machine Learning and Statistical Based Hybrid Feature Selection[EB/OL]. (2024-06-05)[2025-06-10]. https://onlinelibrary.wiley.com/doi/abs/10.1002/spy2.429. |
| [4] |
TORABI H, MIRTAHERI S L, GRECO S. Practical Autoencoder Based Anomaly Detection by Using Vector Reconstruction Error[J]. Cybersecurity, 2023, 6: 1-13.
doi: 10.1186/s42400-022-00134-9 |
| [5] | SAXENA D, CAO Jiannong. Generative Adversarial Networks (GANs): Challenges, Solutions, and Future Directions[J]. ACM Computing Surveys, 2022, 54(3): 1-42. |
| [6] | GU Wei, XING Hongyan, HOU Tianhao. Abnormal Traffic Detection Method Based on Traffic Spatial-Temporal Features and Adaptive Weighting Coefficients[J]. Journal of Electronics & Information Technology, 2024, 46(6): 2647-2654. |
| 顾伟, 行鸿彦, 侯天浩. 基于网络流量时空特征和自适应加权系数的异常流量检测方法[J]. 电子与信息学报, 2024, 46(6):2647-2654. | |
| [7] | SUN Xiuxuan, CHEN Jianhua. Graph Wavenet+TimeGrad Probabilistic Model for High-Dimensional Time Series Prediction[C]// IEEE. 2023 International Conference on Machine Learning and Applications (ICMLA). New York: IEEE, 2023: 1833-1838. |
| [8] | TASHIRO Y, SONG Jiaming, SONG Yang, et al. CSDI: Conditional Score-Based Diffusion Models for Probabilistic Time Series Imputation[C]// NeurIPS. Advances in Neural Information Processing Systems. Cambridge: MIT Press, 2021: 24804-24816. |
| [9] | YANG Xue, LI Guojun, XU Bo. Self-Adaption User Behaviour Identification Technology Based on the Analysis of Network Flow[J]. Journal of Zhejiang Police College, 2023(6): 97-114. |
| 杨雪, 李国军, 徐博. 基于网络流量分析的自适应用户行为识别技术[J]. 浙江警察学院学报, 2023(6):97-114. | |
| [10] | JIANG Xi, LIU Shinan, GEMBER-JACOBSON A, et al. NetDiffusion: Network Data Augmentation through Protocol-Constrained Traffic Generation[J]. The ACM on Measurement and Analysis of Computing Systems, 2024, 8(1): 1-32. |
| [11] | XIAO Chunjing, GOU Zehua, TAI Wenxin, et al. Imputation-Based Time-Series Anomaly Detection with Conditional Weight-Incremental Diffusion Models[C]// ACM. The 29th ACM SIGKDD Conference on Knowledge Discovery and Data Mining. New York: ACM, 2023: 2742-2751. |
| [12] | HU Wentao, JIANG Dawei, WU Sai, et al. IceBerg: Deep Generative Modeling for Constraint Discovery and Anomaly Detection[C]// IEEE. 2022 IEEE Intl Conf on Parallel & Distributed Processing with Applications, Big Data & Cloud Computing, Sustainable Computing & Communications, Social Computing & Networking (ISPA/BDCloud/SocialCom/SustainCom). New York: IEEE, 2022: 74-81. |
| [13] | LIU Yuxiao, CHEN Wei, ZHANG Tianyue, et al. Explainable Anomaly Traffic Detection Based on Sparse Autoencoders[J]. Netinfo Security, 2023, 23(7): 74-85. |
| 刘宇啸, 陈伟, 张天月, 等. 基于稀疏自动编码器的可解释性异常流量检测[J]. 信息网络安全, 2023, 23(7):74-85. | |
| [14] | CHEN Furong, XIONG Chen, LI Ting, et al. A Survey on Time Series Anomaly Detection[J]. Journal of Beijing Jiaotong University, 2025, 49(3): 1-13. |
| 陈福荣, 熊琛, 李婷, 等. 时间序列异常检测综述[J]. 北京交通大学学报, 2025, 49(3):1-13. | |
| [15] |
LI Haitao, WANG Ruimin, DONG Weiyu, et al. Semi-Supervised Network Traffic Anomaly Detection Method Based on GRU[J]. Computer Science, 2023, 50(3): 380-390.
doi: 10.11896/jsjkx.220100032 |
|
李海涛, 王瑞敏, 董卫宇, 等. 一种基于GRU的半监督网络流量异常检测方法[J]. 计算机科学, 2023, 50(3):380-390.
doi: 10.11896/jsjkx.220100032 |
|
| [16] | PANDE S D, LANKE G R, SONI M, et al. Deep Learning-Based Intrusion Detection Model for Network Security[C]// Springer. Intelligent Computing and Networking. Heidelberg: Springer, 2023: 377-386. |
| [17] | LI Shuifang, HONG Fanghua, ZHU Jianyu, et al. Clustering Analysis of Network Anomalous Traffic Based on Spark Platform[C]// CCF. The 33rd National Conference on Computer Security. Beijing: CCF, 2018: 175-179. |
| 李水芳, 洪芳华, 朱剑宇, 等. 基于Spark平台的网络异常流量聚类分析[C]// 中国计算机学会.第33次全国计算机安全学术交流会. 北京: 中国计算机学会,2018:175-179. | |
| [18] | MA Min, FU Yu, HUANG Kai. A Principal Component Analysis Scheme for Security Outsourcing in Cloud Environment Based on Secret Sharing[J]. Netinfo Security, 2023, 23(4): 61-71. |
| 马敏, 付钰, 黄凯. 云环境下基于秘密共享的安全外包主成分分析方案[J]. 信息网络安全, 2023, 23(4):61-71. | |
| [19] | SHARAFALDIN I, LASHKARI A H, GHORBANI A. Toward Generating a New Intrusion Detection Dataset and Intrusion Traffic Characterization[C]// INSTICC. The 4th International Conference on Information Systems Security and Privacy (ICISSP 2018). Setúbal: INSTICC, 2018: 108-116. |
| [20] | CHEN Yang, ZHANG Junzhe, YEO C K. Network Anomaly Detection Using Federated Deep Autoencoding Gaussian Mixture Model[C]// Springer. Machine Learning for Networking. Heidelberg: Springer, 2020: 1-14. |
| [21] |
TULI S, CASALE G, JENNINGS N R. TranAD: Deep Transformer Networks for Anomaly Detection in Multivariate Time Series Data[J]. Proceedings of the VLDB Endowment, 2022, 15(6): 1201-1214.
doi: 10.14778/3514061.3514067 URL |
| [22] |
LÜER F, BOHM C. Anomaly Detection Using Generative Adversarial Networks Reviewing Methodological Progress and Challenges[J]. ACM SIGKDD Explorations Newsletter, 2024, 25(2): 29-41.
doi: 10.1145/3655103.3655109 URL |
| [23] | ELMRABIT N, ZHOU Feixiang, LI Fengyin, et al. Evaluation of Machine Learning Algorithms for Anomaly Detection[C]// IEEE. 2020 International Conference on Cyber Security and Protection of Digital Services (Cyber Security). New York: IEEE, 2020: 1-8. |
| [1] | 康文杰, 刘怡果, 刘绪崇, 赵薇, 欧阳天健, 李嘉欣. 基于多源检测与AI行为分析的挖矿木马协同防御研究[J]. 信息网络安全, 2026, 26(3): 389-398. |
| [2] | 梁广俊, 裘宇辰, 司宏韬, 王群, 马卓, 陈宇琪. 区块链虚拟货币溯源与分析[J]. 信息网络安全, 2026, 26(3): 482-490. |
| [3] | 黄冬, 陈智军. 网络安全教育领域热点及趋势分析—基于CiteSpace的图谱量化分析[J]. 信息网络安全, 2026, 26(3): 491-499. |
| [4] | 李冬, 高源, 于俊清, 曾木虹, 陈俊鑫. 一种基于P4的多模态网络控制与安全检测方案[J]. 信息网络安全, 2026, 26(1): 115-124. |
| [5] | 熊翱, 刘雨潇, 钱旭盛, 张楠. 基于扩散模型和生成对抗网络的生成式隐写方法[J]. 信息网络安全, 2025, 25(8): 1223-1230. |
| [6] | 施开波, 丁甲, 王俊, 蔡肖. 基于监督重启的电力系统网络安全防御策略[J]. 信息网络安全, 2025, 25(6): 910-919. |
| [7] | 魏松杰, 吴琴琴, 袁军翼. 基于运行参数增强API序列的勒索软件动态检测方法研究[J]. 信息网络安全, 2025, 25(5): 713-721. |
| [8] | 李元诚, 孙鹤洋, 张桐, 张贺方, 杨立群. 基于DACDiff的分布式电源调度控制系统FDIAs防御方法[J]. 信息网络安全, 2025, 25(4): 578-586. |
| [9] | 王舜, 邱菡, 何英. 基于本体与攻击—故障树的智能网联汽车功能安全和网络安全联合分析评估方法[J]. 信息网络安全, 2025, 25(4): 598-609. |
| [10] | 陈红松, 刘新蕊, 陶子美, 王志恒. 基于深度学习的时序数据异常检测研究综述[J]. 信息网络安全, 2025, 25(3): 364-391. |
| [11] | 许智双, 张昆, 范俊超, 常晓林. 基于本体的网络安全知识图谱构建方法[J]. 信息网络安全, 2025, 25(3): 451-466. |
| [12] | 李海龙, 崔治安, 沈燮阳. 网络流量特征的异常分析与检测方法综述[J]. 信息网络安全, 2025, 25(2): 194-214. |
| [13] | 张新有, 高志超, 冯力, 邢焕来. 基于FFT-iTransformer的网络安全态势特征插补与预测[J]. 信息网络安全, 2025, 25(2): 228-239. |
| [14] | 高汉成, 黄海平. 对抗DDoS攻击的新型分布式大规模流量清洗方案[J]. 信息网络安全, 2025, 25(1): 78-87. |
| [15] | 周书丞, 李杨, 李传荣, 郭璐璐, 贾辛洪, 杨兴华. 基于上下文的异常根因算法[J]. 信息网络安全, 2024, 24(7): 1062-1075. |
| 阅读次数 | ||||||
|
全文 |
|
|||||
|
摘要 |
|
|||||