信息网络安全 ›› 2025, Vol. 25 ›› Issue (2): 228-239.doi: 10.3969/j.issn.1671-1122.2025.02.004
基于FFT-iTransformer的网络安全态势特征插补与预测
- 1.西南交通大学计算机与人工智能学院,成都 611756
2.西南交通大学唐山研究院,唐山 063000
-
收稿日期:2024-12-02出版日期:2025-02-10发布日期:2025-03-07 -
通讯作者:高志超 E-mail:gzc@my.swjtu.edu.cn -
作者简介:张新有(1971—),男,河南,副教授,博士,主要研究方向为分布式计算与应用、网络安全|高志超(2001—),男,四川,硕士研究生,主要研究方向为人工智能和网络安全|冯力(1974—),男,四川,教授,博士,主要研究方向为人工智能和网络安全|邢焕来(1984—),男,河北,副教授,博士,CCF会员,主要研究方向为人工智能和网络安全 -
基金资助:国家自然科学基金(62172342)
FFT-iTransformer-Based Cybersecurity Situation Awareness Feature Imputation and Prediction
ZHANG Xinyou1, GAO Zhichao2( ), FENG Li1, XING Huanlai1
), FENG Li1, XING Huanlai1
- 1. School of Computing and Artificial Intelligence, Southwest Jiaotong University, Chengdu 611756, China
2. Tangshan Institute, Southwest Jiaotong University, Tangshan 063000, China
-
Received:2024-12-02Online:2025-02-10Published:2025-03-07
摘要:
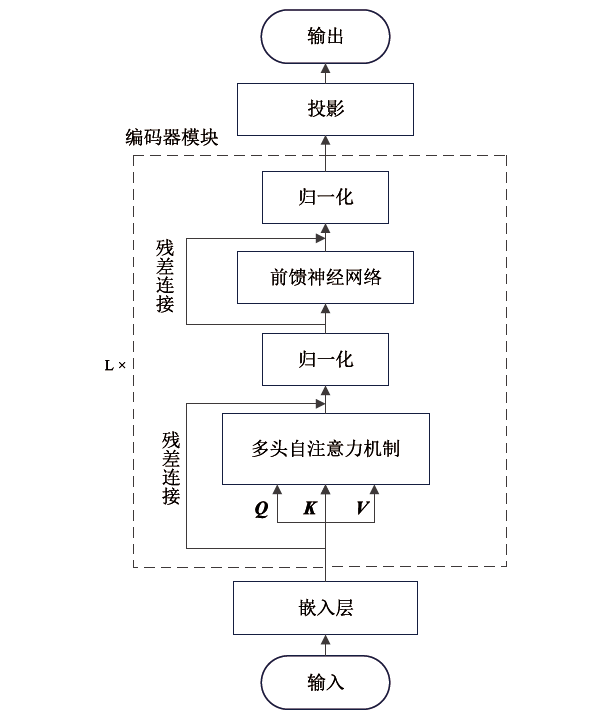
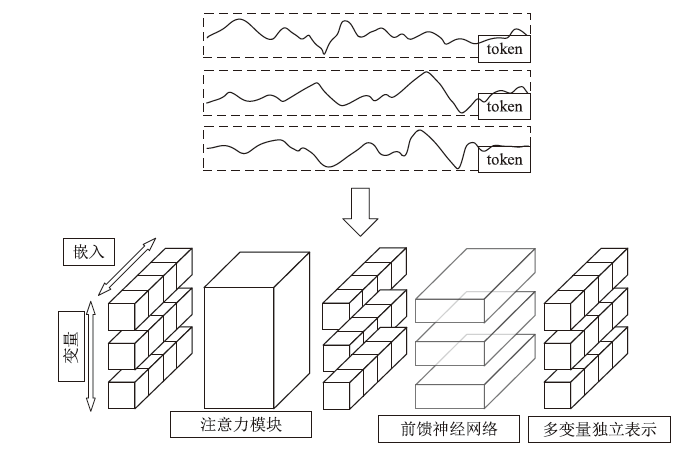
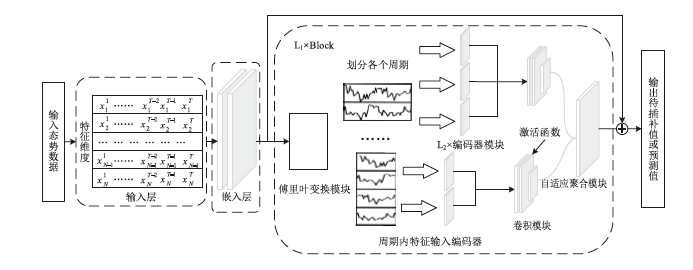
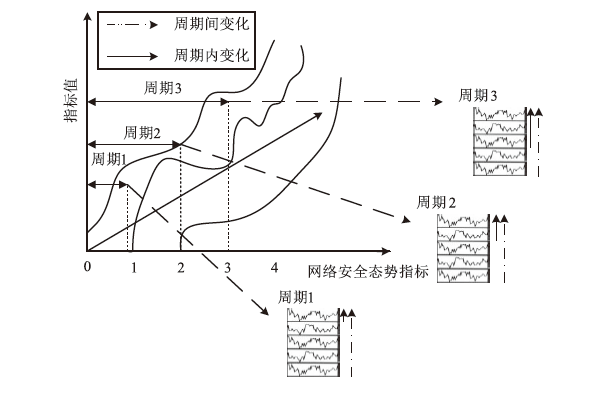
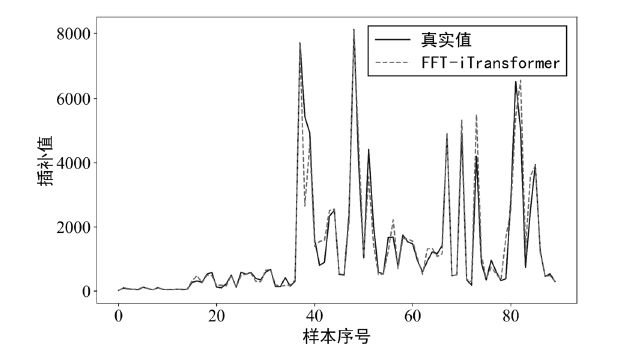
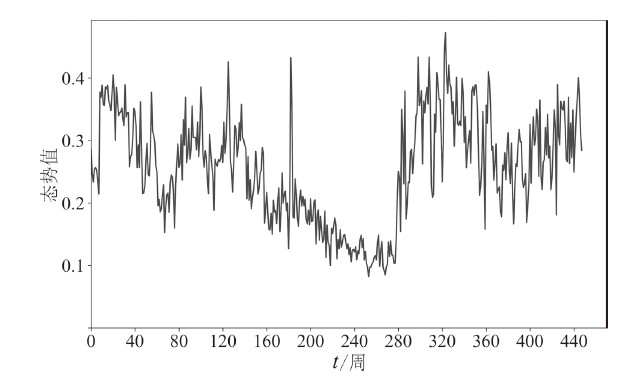
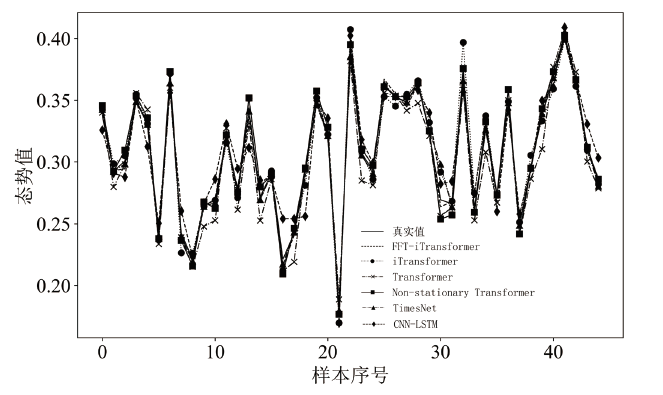
为解决当前网络安全态势预测精度低、指标采集缺失等问题,文章提出一种基于快速傅里叶变换改进的iTransformer模型(FFT-iTransformer)。该模型利用iTransformer架构对时间序列数据进行维度反转嵌入。通过快速傅里叶变换将一维时间序列扩展为二维空间,将周期内的近邻特征和周期间的远邻特征分别映射到二维张量的行与列。首先,模型将周期内特征输入编码器,通过注意力机制学习周期内的局部特征,从而有效捕捉网络安全指标间的动态关联性(如信息安全漏洞数量与感染主机数量间的关联)。然后,将编码器输出的周期内张量融合为二维,传入卷积模块进一步提取二维特征,以捕捉周期间的全局特征。最后,根据振幅所反映的周期相对重要性进行自适应聚合。实验结果表明,该模型预测拟合度可达0.995378,在10%的缺失率下,插补拟合度可达0.879,优于大多数现有模型,可准确插补网络安全态势指标的缺失值,并预测态势值。
中图分类号:
引用本文
张新有, 高志超, 冯力, 邢焕来. 基于FFT-iTransformer的网络安全态势特征插补与预测[J]. 信息网络安全, 2025, 25(2): 228-239.
ZHANG Xinyou, GAO Zhichao, FENG Li, XING Huanlai. FFT-iTransformer-Based Cybersecurity Situation Awareness Feature Imputation and Prediction[J]. Netinfo Security, 2025, 25(2): 228-239.
使用本文
| [1] |
HE Chunrong, ZHU Jiang. Security Situation Prediction Method of GRU Neural Network Based on Attention Mechanism[J]. Systems Engineering and Electronics, 2021, 43(1): 258-266.
doi: 10.3969/j.issn.1001-506X.2021.01.32 |
|
何春蓉, 朱江. 基于注意力机制的GRU神经网络安全态势预测方法[J]. 系统工程与电子技术, 2021, 43(1): 258-266.
doi: 10.3969/j.issn.1001-506X.2021.01.32 |
|
| [2] | AMIRI M, JENSEN R. Missing Data Imputation Using Fuzzy-Rough Methods[J]. Neurocomputing, 2016, 205: 152-164. |
| [3] | BARTHOLOMEW D J. Time Series Analysis Forecasting and Control[J]. Journal of the Operational Research Society, 1971, 22(2): 199-201. |
| [4] | HAMZAÇEBI C. Improving Artificial Neural Networks’ Performance in Seasonal Time Series Forecasting[J]. Information Sciences, 2008, 178(23): 4550-4559. |
| [5] | WANG Jun, DU Wenjie, CAO Wei, et al. Deep Learning for Multivariate Time Series Imputation: A Survey[EB/OL]. (2024-02-06)[2024-11-11]. https://doi.org/10.48550/arXiv.240.04059. |
| [6] | CHE Zhengping, PURUSHOTHAM S, CHO K, et al. Recurrent Neural Networks for Multivariate Time Series with Missing Values[EB/OL]. (2018-04-17)[2024-11-11]. https://pubmed.ncbi.nlm.nih.gov/29666385/. |
| [7] | WU Haixu, HU Tengge, LIU Yong, et al. TimesNet: Temporal 2D-Variation Modeling for General Time Series Analysis[EB/OL]. (2023-04-12)[2024-11-11]. https://doi.org/10.48550/arXiv.2210.02186. |
| [8] | CINI A, MARISCA I, ALIPPI C. Filling the G_ap_s: Multivariate Time Series Imputation by Graph Neural Networks[EB/OL]. (2022-02-10)[2024-11-11]. https://doi.org/10.48550/arXiv.2108.00298. |
| [9] | LIU Yong, WU Haixu, WANG Jianmin, et al. Non-Stationary Transformers[C]// ACM. Proceedings of the 36th International Conference on Neural Information Processing Systems. New York: ACM, 2022: 9881-9889. |
| [10] |
HU Jingjing, MA Dongyan, LIU Chen, et al. Network Security Situation Prediction Based on MR-SVM[J]. IEEE Access, 2019, 7: 130937-130945.
doi: 10.1109/ACCESS.2019.2939490 |
| [11] |
ZHAO Dongmei, WU Yaxing, ZHANG Hongbin. Network Security Situation Prediction Based on IPSO-BiLSTM[J]. Computer Science, 2022, 49(7): 357-362.
doi: 10.11896/jsjkx.210900103 |
|
赵冬梅, 吴亚星, 张红斌. 基于IPSO-BiLSTM的网络安全态势预测[J]. 计算机科学, 2022, 49(7): 357-362.
doi: 10.11896/jsjkx.210900103 |
|
| [12] |
SUN Junfeng, LI Chenghai, CAO Bo. Network Security Situation Prediction Based on TCN-BiLSTM[J]. Systems Engineering and Electronics, 2023, 45(11): 3671-3679.
doi: 10.12305/j.issn.1001-506X.2023.11.36 |
|
孙隽丰, 李成海, 曹波. 基于TCN-BiLSTM的网络安全态势预测[J]. 系统工程与电子技术, 2023, 45(11): 3671-3679.
doi: 10.12305/j.issn.1001-506X.2023.11.36 |
|
| [13] | ZHAO Dongmei, LI Zhijian. Network Security Situation Prediction Based on Transformer[J]. Journal of Huazhong University of Science and Technology (Natural Science Edition), 2022, 50(5): 46-52. |
| 赵冬梅, 李志坚. 基于Transformer的网络安全态势预测[J]. 华中科技大学学报(自然科学版), 2022, 50(5): 46-52. | |
| [14] | LIU Yong, HU Tengge, ZHANG Haoran, et al. iTransformer: Inverted Transformers are Effective for Time Series Forecasting[EB/OL]. (2024-03-14)[2024-11-11]. https://doi.org/10.48550/arXiv.2310.06625. |
| [15] | ZHANG Jianhui, TENG Jie, LI Xiuhui, et al. Short-Term Prediction of Photovoltaic Power Based on Meteorological Features and Improved Transformer[J]. Journal of Engineering for Thermal Energy and Power, 2024, 39(8): 146-154. |
| 张建辉, 滕婕, 李秀慧, 等. 基于气象特征和改进Transformer的光伏功率短期预测[J]. 热能动力工程, 2024, 39(8): 146-154. | |
| [16] | ZHOU Tian, MA Ziqing, WEN Qingsong, et al. FEDformer: Frequency Enhanced Decomposed Transformer for Long-Term Series Forecasting[EB/OL]. (2022-06-16)[2024-11-11]. https://doi.org/10.48550/arXiv.2201.12740. |
| [17] | LIU Shizhan, YU Hang, LIAO Cong, et al. Pyraformer: Low-Complexity Pyramidal Attention for Long-Range Time Series Modeling and Forecasting[EB/OL]. (2023-02-14)[2024-11-11]. https://openreview.net/forum?id=0EXmFzUn5I. |
| [18] | DAS A, KONG Weihao, LEACH A, et al. Long-Term Forecasting with TIDE: Time-Series Dense Encoder[EB/OL]. (2024-04-04)[2024-11-11]. https://doi.org/10.48550/arXiv.2304.08424. |
| [19] | SZEGEDY C, LIU Wei, JIA Yangqing, et al. Going Deeper with Convolutions[C]// IEEE. 2015 IEEE Conference on Computer Vision and Pattern Recognition (CVPR). New York: IEEE, 2015: 1-9. |
| [20] | WU Haixu, XU Jiehui, WANG Jianmin, et al. Autoformer: Decomposition Transformers with Auto-Correlation for Long-Term Series Forecasting[EB/OL]. (2022-01-07)[2024-11-11]. https://doi.org/10.48550/arXiv.2106.13008. |
| [21] | LI Peng, GE Ruzhe, DONG Cun, et al. Adaptive SOH Estimation Method Based on the Transpose Transformer Model for Electrochemical Energy Storage[EB/OL]. (2024-08-12)[2024-11-11]. https://doi.org/10.13336/j.1003-6520.hve.20240555. |
| 李鹏, 葛儒哲, 董存, 等. 基于转置Transformer模型的电化学储能自适应SOH估计方法[EB/OL]. (2024-08-12)[2024-11-11]. https://doi.org/10.13336/j.1003-6520.hve.20240555. | |
| [22] | DONG Shi, SHU Longhui, XIA Qinyu, et al. Device Identification Method for Internet of Things Based on Spatial-Temporal Feature Residuals[J]. IEEE Transactions on Services Computing, 2024, 17(6): 3400-3416. |
| [23] | National Internet Emergency Center. The Cybersecurity Information and Dynamics Weekly Report from 2013 to 2022[EB/OL]. (2022-04-20)[2024-11-11]. https://www.cert.org.cn/publish/main/44/index_20.html. |
| 国家互联网应急中心. 2013年至2022年网络安全信息与动态周报[EB/OL]. (2022-04-20)[2024-11-11]. https://www.cert.org.cn/publish/main/44/index_20.html. | |
| [24] | MUNKHDALAI L, MUNKHDALAI T, PARK K H, et al. An End-to-End Adaptive Input Selection with Dynamic Weights for Forecasting Multivariate Time Series[J]. IEEE Access, 2019, 7: 99099-99114. |
| [25] | XIA Qinyu, DONG Shi, PENG Tao. An Abnormal Traffic Detection Method for IoT Devices Based on Federated Learning and Depthwise Separable Convolutional Neural Networks[C]// IEEE. 2022 IEEE International Performance, Computing, and Communications Conference (IPCCC). New York: IEEE, 2022: 352-359. |
| [1] | 李海龙, 崔治安, 沈燮阳. 网络流量特征的异常分析与检测方法综述[J]. 信息网络安全, 2025, 25(2): 194-214. |
| [2] | 高汉成, 黄海平. 对抗DDoS攻击的新型分布式大规模流量清洗方案[J]. 信息网络安全, 2025, 25(1): 78-87. |
| [3] | 问闻, 刘钦菊, 邝琳, 任雪静. 隐私保护体系下网络威胁情报共享的研究现状和方案设计[J]. 信息网络安全, 2024, 24(7): 1129-1137. |
| [4] | 张长琳, 仝鑫, 佟晖, 杨莹. 面向网络安全领域的大语言模型技术综述[J]. 信息网络安全, 2024, 24(5): 778-793. |
| [5] | 杨志鹏, 刘代东, 袁军翼, 魏松杰. 基于自注意力机制的网络局域安全态势融合方法研究[J]. 信息网络安全, 2024, 24(3): 398-410. |
| [6] | 金志刚, 陈旭阳, 武晓栋, 刘凯. 增量式入侵检测研究综述[J]. 信息网络安全, 2024, 24(12): 1819-1830. |
| [7] | 李娇, 张玉清, 吴亚飚. 面向网络安全关系抽取的大语言模型数据增强方法[J]. 信息网络安全, 2024, 24(10): 1477-1483. |
| [8] | 何开宇, 王彬, 于哲, 陈方. ARP欺骗攻击与硬件防御研究[J]. 信息网络安全, 2024, 24(10): 1604-1610. |
| [9] | 付静. 水利关键信息基础设施安全保护探索与实践[J]. 信息网络安全, 2023, 23(8): 121-127. |
| [10] | 孙珵珵. 网络安全治理对策研究[J]. 信息网络安全, 2023, 23(6): 104-110. |
| [11] | 王晓狄, 黄诚, 刘嘉勇. 面向网络安全开源情报的知识图谱研究综述[J]. 信息网络安全, 2023, 23(6): 11-21. |
| [12] | 李冬, 于俊清, 文瑞彬, 谢一丁. 基于IPv6的容器云内生安全机制[J]. 信息网络安全, 2023, 23(12): 21-28. |
| [13] | 金志刚, 刘凯, 武晓栋. 智能电网AMI领域IDS研究综述[J]. 信息网络安全, 2023, 23(1): 1-8. |
| [14] | 孙鹏宇, 谭晶磊, 李晨蔚, 张恒巍. 基于时间微分博弈的网络安全防御决策方法[J]. 信息网络安全, 2022, 22(5): 64-74. |
| [15] | 金波, 唐前进, 唐前临. CCF计算机安全专业委员会2022年网络安全十大发展趋势解读[J]. 信息网络安全, 2022, 22(4): 1-6. |
| 阅读次数 | ||||||||||||||||||||||||||||||||||||||||||||||||||
|
全文 26
|
|
|||||||||||||||||||||||||||||||||||||||||||||||||
|
摘要 77
|
|
|||||||||||||||||||||||||||||||||||||||||||||||||