Netinfo Security ›› 2025, Vol. 25 ›› Issue (3): 478-493.doi: 10.3969/j.issn.1671-1122.2025.03.010
Previous Articles Next Articles
CAN Bus Intrusion Detection Method Based on Spatio-Temporal Graph Neural Networks
LIU Chenfei1,2, WAN Liang1,2( )
)
- 1. State Key Laboratory of Public Big Data, Guiyang 550025, China
2. College of Computer Science and Technology, Guizhou University, Guiyang 550025, China
-
Received:2025-01-14Online:2025-03-10Published:2025-03-26 -
Contact:WAN Liang E-mail:lwan@gzu.edu.cn
CLC Number:
Cite this article
LIU Chenfei, WAN Liang. CAN Bus Intrusion Detection Method Based on Spatio-Temporal Graph Neural Networks[J]. Netinfo Security, 2025, 25(3): 478-493.
share this article
| 类别 | 模型 | 准确率 | 精确率 | 召回率 | F1分数 |
|---|---|---|---|---|---|
| 正常 | AHDNN[ | 98.20% | 96.94% | 97.57% | 96.94% |
| DCNN[ | 98.30% | 98.82% | 98.55% | 99.39% | |
| VGG-16[ | 97.17% | 97.66% | 97.42% | 97.66% | |
| HyDL[ | 98.90% | 99.28% | 98.90% | 99.53% | |
| CANnolo[ | 97.93% | 96.37% | 97.14% | 96.37% | |
| NovelADS[ | 99.34% | 99.19% | 99.26% | 99.19% | |
| GNLNet | 99.99% | 100% | 99.99% | 99.99% | |
| DoS攻击 | AHDNN[ | 94.16% | 97.02% | 94.16% | 95.57% |
| DCNN[ | 95.98% | 90.80% | 95.98% | 93.32% | |
| VGG-16[ | 95.58% | 95.54% | 94.12% | 95.81% | |
| HyDL[ | 97.96% | 98.30% | 96.34% | 97.32% | |
| CANnolo[ | 97.47% | 96.66% | 95.82% | 96.24% | |
| NovelADS[ | 98.01% | 97.34% | 97.31% | 97.19% | |
| GNLNet | 99.65% | 98.24% | 99.65% | 98.94% | |
| Fuzzy攻击 | AHDNN[ | 95.12% | 96.52% | 93.16% | 94.79% |
| DCNN[ | 94.13% | 95.51% | 92.14% | 93.78% | |
| VGG-16[ | 92.13% | 93.61% | 91.12% | 92.35% | |
| HyDL[ | 97.11% | 97.64% | 96.68% | 97.11% | |
| CANnolo[ | 96.17% | 97.14% | 95.16% | 96.17% | |
| NovelADS[ | 98.09% | 98.31% | 98.12% | 96.16% | |
| GNLNet | 99.87% | 99.89% | 99.87% | 99.88% | |
| Gear欺骗攻击 | AHDNN[ | 98.35% | 98.42% | 99.04% | 98.35% |
| DCNN[ | 98.14% | 98.41% | 98.01% | 98.22% | |
| VGG-16[ | 98.93% | 99.05% | 98.65% | 98.96% | |
| HyDL[ | 99.31% | 99.27% | 99.03% | 99.35% | |
| CANnolo[ | 98.46% | 98.65% | 98.32% | 98.72% | |
| NovelADS[ | 99.85% | 99.89% | 99.80% | 99.84% | |
| GNLNet | 99.99% | 100% | 99.99% | 100% | |
| RPM欺骗攻击 | AHDNN[ | 98.85% | 98.26% | 99.05% | 98.93% |
| DCNN[ | 98.13% | 98.59% | 98.02% | 98.30% | |
| VGG-16[ | 98.26% | 99.02% | 98.78% | 98.64% | |
| HyDL[ | 99.06% | 99.15% | 99.25% | 99.06% | |
| CANnolo[ | 98.94% | 99.05% | 98.96% | 99.14% | |
| NovelADS[ | 99.35% | 99.36% | 99.16% | 99.26% | |
| GNLNet | 100% | 100% | 100% | 100% |
| 类别 | 模型 | 准确率 | 精确率 | 召回率 | F1分数 |
|---|---|---|---|---|---|
| 正常 | GNAT[ | 99.76% | 99.86% | 99.76% | 99.81% |
| CAN-GAT-2[ | 99.81% | 99.92% | 99.81% | 99.86% | |
| EIW-AGT[ | 98.92% | 98.74% | 99.91% | 97.83% | |
| E-GRACL[ | 97.84% | 96.47% | 97.82% | 96.64% | |
| GNLNet | 99.99% | 100% | 99.99% | 99.99% | |
| DoS攻击 | GNAT[ | 99.05% | 96.51% | 99.05% | 97.76% |
| CAN-GAT-2[ | 99.13% | 97.09% | 99.13% | 98.10% | |
| EIW-AGT[ | 97.36% | 98.23% | 98.12% | 97.24% | |
| E-GRACL[ | 96.56% | 96.84% | 96.18% | 95.84% | |
| GNLNet | 99.65% | 98.24% | 99.65% | 98.94% | |
| Fuzzy攻击 | GNAT[ | 98.47% | 99.46% | 98.47% | 98.96% |
| CAN-GAT-2[ | 99.36% | 99.68% | 99.36% | 99.52% | |
| EIW-AGT[ | 96.45% | 95.74% | 96.53% | 95.68% | |
| E-GRACL[ | 97.03% | 97.64% | 96.89% | 96.96% | |
| GNLNet | 99.87% | 99.89% | 99.87% | 99.88% | |
| Gear欺骗攻击 | GNAT[ | 99.94% | 99.95% | 99.94% | 99.94% |
| CAN-GAT-2[ | 99.98% | 99.98% | 99.98% | 99.98% | |
| EIW-AGT[ | 98.69% | 96.90% | 96.68% | 96.77% | |
| E-GRACL[ | 98.04% | 95.02% | 95.39% | 95.18% | |
| GNLNet | 99.99% | 100% | 99.99% | 100% | |
| RPM欺骗攻击 | GNAT[ | 99.95% | 99.96% | 99.95% | 99.96% |
| CAN-GAT-2[ | 99.99% | 99.99% | 99.99% | 99.99% | |
| EIW-AGT[ | 97.82% | 98.17% | 98.27% | 97.57% | |
| E-GRACL[ | 96.38% | 97.63% | 97.51% | 96.22% | |
| GNLNet | 100% | 100% | 100% | 100% |
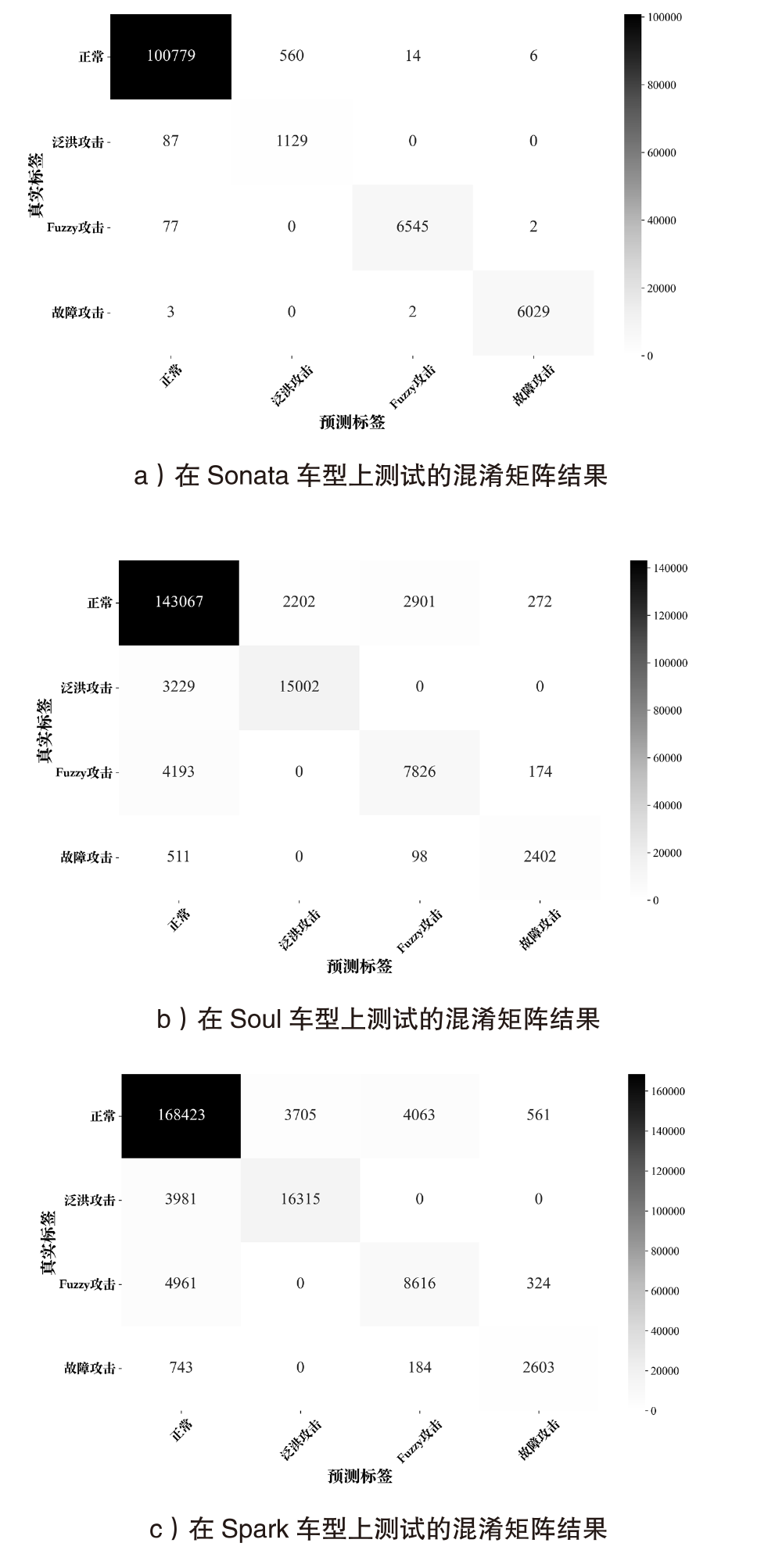
| 测试车型 | 类别 | 准确率 | 精确率 | 召回率 | F1分数 |
|---|---|---|---|---|---|
| 起亚Soul | 正常 | 92.68% | 94.75% | 96.38% | 95.96% |
| 泛洪攻击 | 97.01% | 87.20% | 82.29% | 84.67% | |
| Fuzzy攻击 | 95.95% | 72.30% | 64.18% | 68.00% | |
| 故障攻击 | 99.42% | 84.34% | 79.77% | 81.99% | |
| 雪佛兰Spark | 正常 | 91.60% | 94.56% | 95.29% | 94.92% |
| 泛洪攻击 | 96.42% | 81.49% | 80.39% | 80.94% | |
| Fuzzy攻击 | 95.56% | 66.98% | 61.98% | 64.38% | |
| 故障攻击 | 99.16% | 74.63% | 73.74% | 74.18% |
| 类别 | 图构建方法 | 准确率 | 精确率 | 召回率 | F1分数 |
|---|---|---|---|---|---|
| 正常 | 文献[ | 78.28% | 72.54% | 73.46% | 70.31% |
| 加入回溯链接机制 | 88.26% | 82.93% | 84.39% | 82.74% | |
| DoS攻击 | 文献[ | 72.32% | 68.02% | 69.54% | 68.75% |
| 加入回溯链接机制 | 85.01% | 79.71% | 81.23% | 80.46% | |
| Fuzzy攻击 | 文献[ | 71.03% | 66.81% | 68.32% | 67.56% |
| 加入回溯链接机制 | 82.94% | 78.92% | 81.31% | 79.11% | |
| Gear欺骗攻击 | 文献[ | 74.12% | 69.25% | 70.41% | 69.33% |
| 加入回溯链接机制 | 87.67% | 87.53% | 87.75% | 87.64% | |
| RPM欺骗攻击 | 文献[ | 75.24% | 70.46% | 71.47% | 70.73% |
| 加入回溯链接机制 | 88.34% | 89.65% | 89.78% | 89.71% |
| [1] | LUO Qian, LIU Jiajia. Wireless Telematics Systems in Emerging Intelligent and Connected Vehicles: Threats and Solutions[J]. IEEE Wireless Communications, 2018, 25(6): 113-119. |
| [2] | ZHOU Haibo, LIU Bo, LUAN T H, et al. ChainCluster: Engineering a Cooperative Content Distribution Framework for Highway Vehicular Communications[J]. IEEE Transactions on Intelligent Transportation Systems, 2014, 15(6): 2644-2657. |
| [3] | SHARMA K, BUTLER B, JENNINGS B. Graph-Based Heuristic Solution for Placing Distributed Video Processing Applications on Moving Vehicle Clusters[J]. IEEE Transactions on Network and Service Management, 2022, 19(3): 3076-3089. |
| [4] | MARTINELLI F, MERCALDO F, NARDONE V, et al. Who’s Driving My Car?A Machine Learning Based Approach to Driver Identification[C]// IEEE. Proceedings of the 4th International Conference on Information Systems Security and Privacy. New York: IEEE, 2018: 367-372. |
| [5] | CAO Yue, LI Sifan, LYU Chenchen, et al. Towards Cyber Security for Low-Carbon Transportation: Overview, Challenges and Future Directions[EB/OL]. (2023-06-19)[2024-12-30]. https://doi.org/10.1016/j.rser.2023.113401. |
| [6] | WARD D, IBARRA I, RUDDLE A. Threat Analysis and Risk Assessment in Automotive Cyber Security[J]. SAE International Journal of Passenger Cars-Electronic and Electrical Systems, 2013, 6(2): 507-513. |
| [7] | MILLER C. Remote Exploitation of an Unaltered Passenger Vehicle[EB/OL]. (2015-08-10)[2024-12-30]. https://cis.temple.edu/-qzeng/cis4360-spring17/papers/Remote-Car-Hacking.pdf. |
| [8] | WANG Kai, ZHANG Aiheng, SUN Haoran, et al. Analysis of Recent Deep-Learning-Based Intrusion Detection Methods for in-Vehicle Network[J]. IEEE Transactions on Intelligent Transportation Systems, 2023, 24(2): 1843-1854. |
| [9] | CORRIGAN S. Introduction to the Controller Area Network (CAN)[EB/OL]. (2016-05-10)[2024-12-30]. https://www.ti.com/cn/lit/an/sloa101b/sloa101b.pdf?ts=1740374594584. |
| [10] | DAI Yinfei, ZHOU Xiuzhen, LIU Yubao, et al. In-Vehicle Network Intrusion Detection System Based on Can Bus Data[EB/OL]. (2024-04-09)[2024-12-30]. https://doi.org/10.13229/j.cnki.jdxbgxb.20240044. |
| 戴银飞, 周秀贞, 刘玉宝, 等. 基于CAN总线数据的车载网络入侵检测系统[EB/OL]. (2024-04-09)[2024-12-30]. https://doi.org/10.13229/j.cnki.jdxbgxb.20240044. | |
| [11] | LIU Jiajia, ZHANG Shubin, SUN Wen, et al. In-Vehicle Network Attacks and Countermeasures: Challenges and Future Directions[J]. IEEE Network, 2017, 31(5): 50-58. |
| [12] | DELWAR H M, INOUE H, OCHIAI H, et al. An Effective in-Vehicle CAN Bus Intrusion Detection System Using CNN Deep Learning Approach[C]// IEEE. 2020 IEEE Global Communications Conference. New York: IEEE, 2020: 1-6. |
| [13] | SONG H M, WOO J, KIM H K. In-Vehicle Network Intrusion Detection Using Deep Convolutional Neural Network[EB/OL]. (2019-10-03)[2024-12-30]. https://doi.org/10.1016/j.vehcom.2019.100198. |
| [14] | AHMED I, JEON G, AHMAD A. Deep Learning-Based Intrusion Detection System for Internet of Vehicles[J]. IEEE Consumer Electronics Magazine, 2023, 12(1): 117-123. |
| [15] | HANSELMANN M, STRAUSS T, DORMANN K, et al. CANet: An Unsupervised Intrusion Detection System for High Dimensional CAN Bus Data[J]. IEEE Access, 2020, 8: 58194-58205. |
| [16] | JEDH M, BEN O L, AHMED N, et al. Detection of Message Injection Attacks Onto the CAN Bus Using Similarities of Successive Messages-Sequence Graphs[J]. IEEE Transactions on Information Forensics and Security, 2021, 16: 4133-4146. |
| [17] | LONGARI S, NOVA V D H, ZAGO M, et al. CANnolo: An Anomaly Detection System Based on LSTM Autoencoders for Controller Area Network[J]. IEEE Transactions on Network and Service Management, 2021, 18(2): 1913-1924. |
| [18] | AGRAWAL K, ALLADI T, AGRAWAL A, et al. NovelADS: A Novel Anomaly Detection System for Intra-Vehicular Networks[J]. IEEE Transactions on Intelligent Transportation Systems, 2022, 23(11): 22596-22606. |
| [19] | ZEKRY A, SAYED A, MOUSSA M, et al. Anomaly Detection Using IoT Sensor-Assisted ConvLSTM Models for Connected Vehicles[C]// IEEE. 2021 IEEE 93rd Vehicular Technology Conference (VTC2021-Spring). New York: IEEE, 2021: 1-6. |
| [20] | ZHANG Hengrun, ZENG Kai, LIN Shuai. Federated Graph Neural Network for Fast Anomaly Detection in Controller Area Networks[J]. IEEE Transactions on Information Forensics and Security, 2023, 18: 1566-1579. |
| [21] | XIAO Junchao, YANG Lin, ZHONG Fuli, et al. Robust Anomaly-Based Intrusion Detection System for in-Vehicle Network by Graph Neural Network Framework[J]. Applied Intelligence, 2023, 53(3): 3183-3206. |
| [22] | XIAO Junchao, CHEN Hongbo, ZHONG Fuli. A Novel Feature Extraction Framework Using Graph Node Attention Network for in-Vehicle Networks Intrusion Detection[J]. IEEE Systems Journal, 2024, 18(1): 150-161. |
| [23] | HAMILTON W L, YING R, LESKOVEC J, et al. Inductive Representation Learning on Large Graphs[C]// ACM. Proceedings of the 31st International Conference on Neural Information Processing Systems. New York: ACM, 2017: 1025-1035. |
| [24] | VELICKOVIC P, CUCURULL G, CASANOVA A, et al. Graph Attention Networks[EB/OL]. (2018-02-04)[2024-12-30]. https://arxiv.org/abs/1710.10903. |
| [25] | YIN Ying, ZHOU Zhihong, YAO Lihong. Research on LSTM-Based CAN Intrusion Detection Model[J]. Netinfo Security, 2022, 22(12): 57-66. |
| 银鹰, 周志洪, 姚立红. 基于LSTM的CAN入侵检测模型研究[J]. 信息网络安全, 2022, 22(12): 57-66. | |
| [26] | HAN M L, KWAK B I, KIM H K. Anomaly Intrusion Detection Method for Vehicular Networks Based on Survival Analysis[J]. Vehicular Communications, 2018, 14: 52-63. |
| [27] | GUPTA K D, SHARMA D K, DWIVEDI R, et al. AHDNN: Attention-Enabled Hierarchical Deep Neural Network Framework for Enhancing Security of Connected and Autonomous Vehicles[EB/OL]. [2024-12-30]. https://doi.org/10.1142/S0218126623500585. |
| [28] | LO W, ALQAHTANI H, THAKUR K, et al. A Hybrid Deep Learning Based Intrusion Detection System Using Spatial-Temporal Representation of in-Vehicle Network Traffic[EB/OL]. (2022-03-30)[2024-12-30]. https://doi.org/10.1016/j.vehcom.2022.100471. |
| [29] | KARPAGAVALLI C, KALIAPPAN M. Edge Implicit Weighting with Graph Transformers for Robust Intrusion Detection in Internet of Things Network[EB/OL]. (2024-12-21)[2024-12-30]. https://doi.org/10.1016/j.cose.2024.104299. |
| [30] | LIN Lieqing, ZHONG Qi, QIU Jiasheng, et al. E-GRACL: An IoT Intrusion Detection System Based on Graph Neural Networks[EB/OL]. (2024-10-21)[2024-12-30]. https://doi.org/10.1007/s11227-024-06471-5. |
| [31] | LO W W, LAYEGHY S, SARHAN M, et al. E-GraphSAGE: A Graph Neural Network Based Intrusion Detection System for IoT[C]// IEEE. NOMS 2022 IEEE/IFIP Network Operations and Management Symposium. New York: IEEE, 2022: 1-9. |
| [32] | ABUALHOUL M Y, SHAGDAR O, NASHASHIBI F. Visible Light Inter-Vehicle Communication for Platooning of Autonomous Vehicles[C]// IEEE. 2016 IEEE Intelligent Vehicles Symposium (IV). New York: IEEE, 2016: 508-513. |
| [1] | JIN Zengwang, JIANG Lingyang, DING Junyi, ZHANG Huixiang, ZHAO Bo, FANG Pengfei. A Review of Research on Industrial Control System Security [J]. Netinfo Security, 2025, 25(3): 341-363. |
| [2] | LIU Lianhai, LI Huiye, MAO Donghui. CBAM-CNN Network-Based Intrusion Detection Method Using Image Convex Hull Features [J]. Netinfo Security, 2024, 24(9): 1422-1431. |
| [3] | ZHANG Hao, XIE Dazhi, HU Yunsheng, YE Junwei. A Review of Network Anomaly Detection Based on Semi-Supervised Learning [J]. Netinfo Security, 2024, 24(4): 491-508. |
| [4] | WANG Jian, CHEN Lin, WANG Kailun, LIU Jiqiang. Application Layer DDoS Detection Method Based on Spatio-Temporal Graph Neural Network [J]. Netinfo Security, 2024, 24(4): 509-519. |
| [5] | JIANG Rong, LIU Haitian, LIU Cong. Unsupervised Network Intrusion Detection Method Based on Ensemble Learning [J]. Netinfo Security, 2024, 24(3): 411-426. |
| [6] | FENG Guangsheng, JIANG Shunpeng, HU Xianlang, MA Mingyu. New Research Progress on Intrusion Detection Techniques for the Internet of Things [J]. Netinfo Security, 2024, 24(2): 167-178. |
| [7] | JIN Zhigang, DING Yu, WU Xiaodong. Federated Intrusion Detection Algorithm with Bilateral Correction Merging Gradient Difference [J]. Netinfo Security, 2024, 24(2): 293-302. |
| [8] | SUN Hongzhe, WANG Jian, WANG Peng, AN Yulong. Network Intrusion Detection Method Based on Attention-BiTCN [J]. Netinfo Security, 2024, 24(2): 309-318. |
| [9] | JIN Zhigang, CHEN Xuyang, WU Xiaodong, LIU Kai. A Review of Incremental Intrusion Detection [J]. Netinfo Security, 2024, 24(12): 1819-1830. |
| [10] | SHEN Hua, TIAN Chen, GUO Sensen, MU Zhiying. Research on Adversarial Machine Learning-Based Network Intrusion Detection Method [J]. Netinfo Security, 2023, 23(8): 66-75. |
| [11] | PENG Hanzhong, ZHANG Zhujun, YAN Liyue, HU Chenglin. Research on Intrusion Detection Mechanism Optimization Based on Federated Learning Aggregation Algorithm under Consortium Chain [J]. Netinfo Security, 2023, 23(8): 76-85. |
| [12] | LIU Changjie, SHI Runhua. A Smart Grid Intrusion Detection Model for Secure and Efficient Federated Learning [J]. Netinfo Security, 2023, 23(4): 90-101. |
| [13] | GAO Qingguan, ZHANG Bo, FU Anmin. An Advanced Persistent Threat Detection Method Based on Attack Graph [J]. Netinfo Security, 2023, 23(12): 59-68. |
| [14] | JIN Zhigang, LIU Kai, WU Xiaodong. A Review of IDS Research in Smart Grid AMI Field [J]. Netinfo Security, 2023, 23(1): 1-8. |
| [15] | WANG Huazhong, TIAN Zilei. Intrusion Detection Method of ICS Based on Improved CGAN Algorithm [J]. Netinfo Security, 2023, 23(1): 36-43. |
| Viewed | ||||||
|
Full text |
|
|||||
|
Abstract |
|
|||||