信息网络安全 ›› 2026, Vol. 26 ›› Issue (2): 315-324.doi: 10.3969/j.issn.1671-1122.2026.02.011
基于可信执行环境的层次角色基分级加密方案
1.北京交通大学智能交通数据安全与隐私保护技术实验室 北京 100044 2.计算智能与网络信息安全兵团重点实验室 石河子 832003 3.中国铁道科学研究院集团有限公司电子计算技术研究所 北京 100081
-
收稿日期:2025-04-23出版日期:2026-02-10发布日期:2026-02-23 -
通讯作者:赵佳 zhaojia@bjtu.edu.cn -
作者简介:赵佳(1980—),女,内蒙古,副教授,博士,CCF会员,主要研究方向为隐私保护、密码学|王妍淳(2001—),女,河北,硕士研究生,主要研究方向为隐私保护|马洪亮(1977—),男,新疆,副教授,博士,主要研究方向为网络安全、大数据安全、异常检测|李琪(1987—),女,北京,高级工程师,硕士,主要研究方向为网络安全测评、数据安全管理 -
基金资助:国家重点研发计划(2023YFB2703702);国铁集团科技研究开发计划(P2023W001);计算智能与网络信息安全兵团重点实验室开放课题(CS24GY00010)
Hierarchical Role-Based Encryption Scheme Based on Trusted Execution Environment
ZHAO Jia1( ), WANG Yanchun1, MA Hongliang2, LI Qi3
), WANG Yanchun1, MA Hongliang2, LI Qi3
1. Intelligent Trafic Data Security and Privacy Protection Technology Laboratory ,Beijing Jiaotong University Beijing 100044, China 2. Xinjiang Production and Construction Corps Key Laboratory of Computing Intelligence and Network Information Security Shihezi 832003, China 3. Institute of Computing Technologies ,China Academy of Railway Sciences Group Co., Ltd. Beijing 100081, China
-
Received:2025-04-23Online:2026-02-10Published:2026-02-23
摘要:
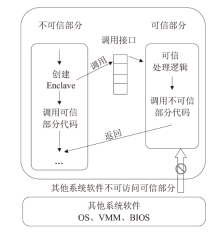
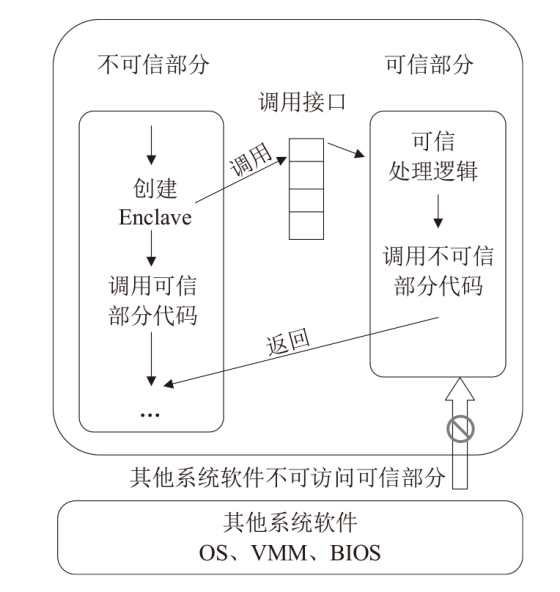
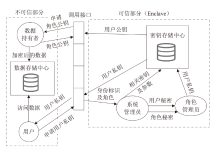
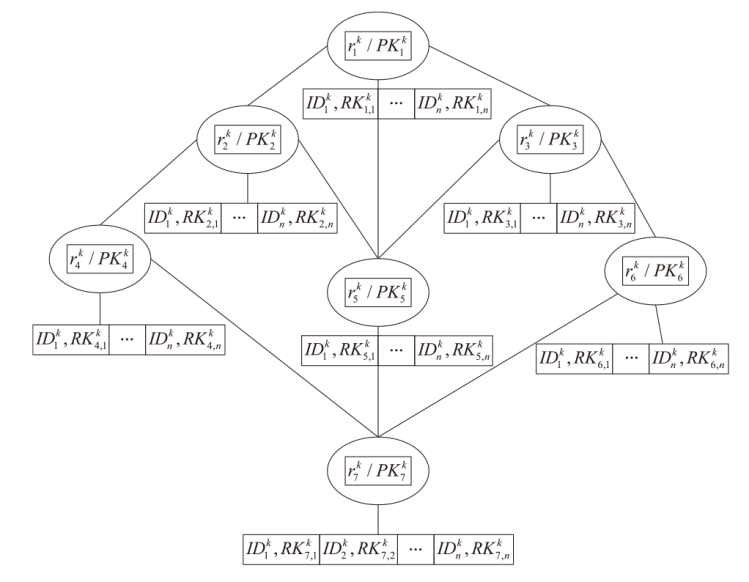
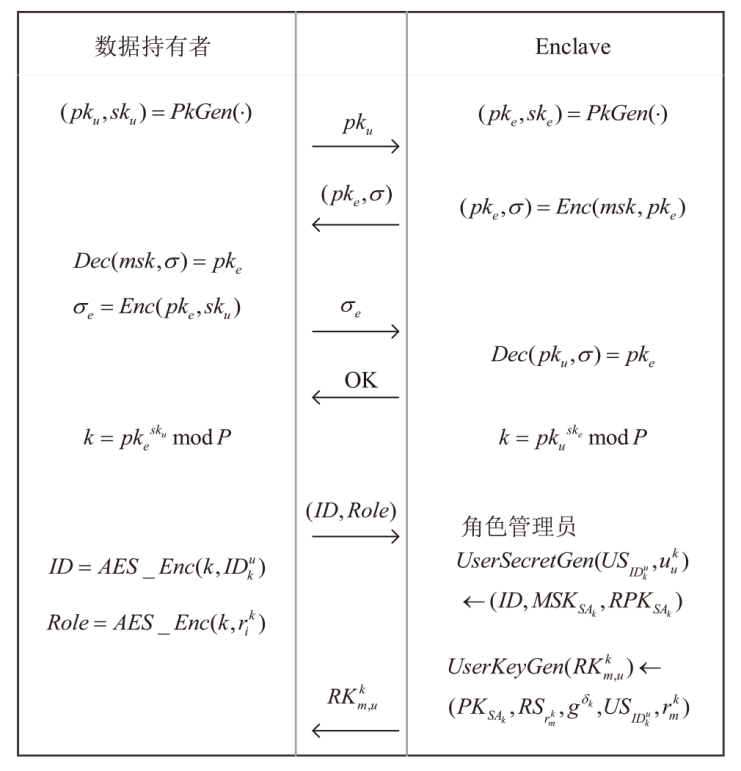
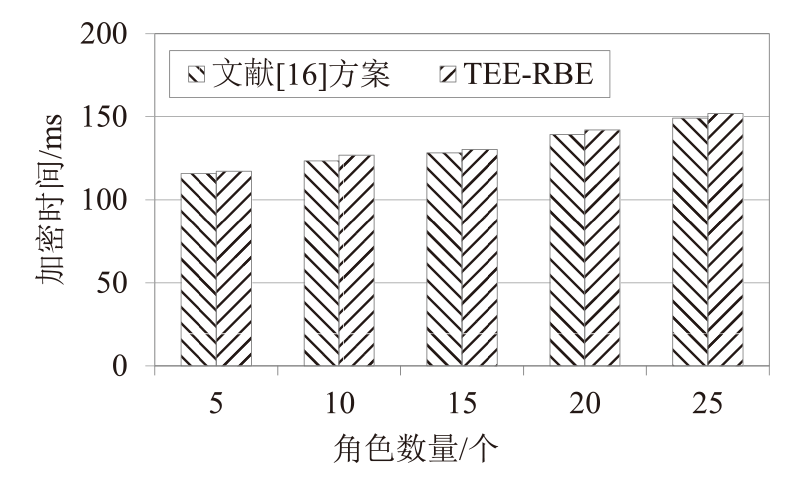
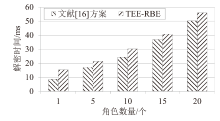
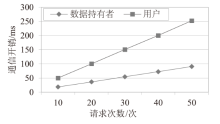
文章提出一种基于可信执行环境的层次角色基分级加密方案,以解决现有加密技术在数据敏感性保护和运行时的安全问题。该方案结合了层次角色基加密技术和可信计算,根据数据敏感性选择不同层次的角色公钥进行加密,实现对数据访问权限和敏感性要求的动态匹配。对于一般性数据,采用深层节点的角色密钥进行加密;对于高度敏感数据,使用靠近根节点的浅层节点的角色密钥进行加密。此外,该方案将加密操作和密钥管理操作置于可信执行环境中,可有效防止加密密钥和敏感数据被窃取或篡改,弥补了传统加密方案在系统运行时防护能力差的不足。同时,该方案结合可信执行环境的硬件隔离特性和层次角色基加密技术,不仅提升了系统的抗攻击能力,还实现了更精细的权限管理。实验结果表明,该方案在保证数据安全的同时具有较高的计算效率。
中图分类号:
引用本文
赵佳, 王妍淳, 马洪亮, 李琪. 基于可信执行环境的层次角色基分级加密方案[J]. 信息网络安全, 2026, 26(2): 315-324.
ZHAO Jia, WANG Yanchun, MA Hongliang, LI Qi. Hierarchical Role-Based Encryption Scheme Based on Trusted Execution Environment[J]. Netinfo Security, 2026, 26(2): 315-324.
| [1] |
ASOKAN N, EKBERG J E, KOSTIAINEN K, et al. Mobile Trusted Computing[J]. Proceedings of the IEEE, 2014, 102(8): 1189-1206.
doi: 10.1109/JPROC.2014.2332007 URL |
| [2] | CHANG C C, LIN I C, TSAI H M, et al. A Key Assignment Scheme for Controlling Access in Partially Ordered User Hierarchies[C]// IEEE. The 18th International Conference on Advanced Information Networking and Applications. New York: IEEE, 2004: 376-379. |
| [3] |
AKL S G, TAYLOR P D. Cryptographic Solution to a Problem of Access Control in a Hierarchy[J]. ACM Transactions on Computer Systems, 1983, 1(3): 239-248.
doi: 10.1145/357369.357372 URL |
| [4] | ATALLAH M J, BLANTON M, FAZIO N, et al. Dynamic and Efficient Key Management for Access Hierarchies[J]. ACM Transactions on Information and System Security, 2009, 12(3): 1-43. |
| [5] |
LIN Yuli, HSU C L. Secure Key Management Scheme for Dynamic Hierarchical Access Control Based on ECC[J]. Journal of Systems and Software, 2011, 84(4): 679-685.
doi: 10.1016/j.jss.2010.11.926 URL |
| [6] |
TANG Shaohua, LI Xiaoyu, HUANG Xinyi, et al. Achieving Simple, Secure and Efficient Hierarchical Access Control in Cloud Computing[J]. IEEE Transactions on Computers, 2016, 65(7): 2325-2331.
doi: 10.1109/TC.2015.2479609 URL |
| [7] | CHEN Y R, TZENG W G. Hierarchical Key Assignment with Dynamic Read-Write Privilege Enforcement and Extended KI-Security[C]// Springer. International Conference on Applied Cryptography and Network Security. Heidelberg: Springer, 2017: 165-183. |
| [8] | PAREEK G, PURUSHOTHAMA B R. Efficient Strong Key Indistinguishable Access Control in Dynamic Hierarchies with Constant Decryption Cost[C]// ACM. The 11th International Conference on Security of Information and Networks. New York: ACM, 2018: 1-7. |
| [9] |
ZHOU Lan, VARADHARAJAN V, HITCHENS M. Enforcing Role-Based Access Control for Secure Data Storage in the Cloud[J]. The Computer Journal, 2011, 54(10): 1675-1687.
doi: 10.1093/comjnl/bxr080 URL |
| [10] |
ZHU Yan, AHN G J, HU Hongxin, et al. Role-Based Cryptosystem: A New Cryptographic RBAC System Based on Role-Key Hierarchy[J]. IEEE Transactions on Information Forensics and Security, 2013, 8(12): 2138-2153.
doi: 10.1109/TIFS.2013.2287858 URL |
| [11] |
MARIN-PERE J M, PEREZ G M, SKARMETA-GOMEZ A F. SecRBAC: Secure Data in the Clouds[J]. IEEE Transactions on Services Computing, 2017, 10(5): 726-740.
doi: 10.1109/TSC.2016.2553668 URL |
| [12] | SCHWARZ M, WEISER S, GRUSS D. Practical Enclave Malware with Intel SGX[C]// Springer. International Conference on Detection of Intrusions and Malware, and Vulnerability Assessment. Heidelberg: Springer, 2019: 177-196. |
| [13] | RAN Jinhao, CAI Dongliang. Attribute Signature Identity Authentication Scheme Based on Blockchain and Trusted Execution Environment[J]. Journal of Computer Research and Development, 2023, 60(11): 2555-2566. |
| 冉津豪, 蔡栋梁. 基于区块链和可信执行环境的属性签名身份认证方案[J]. 计算机研究与发展, 2023, 60(11):2555-2566. | |
| [14] | YE Jiajun. Research on Federated Learning Algorithms Based on Trusted Execution Environment[D]. Hangzhou: Zhejiang University, 2024. |
| 叶家俊. 基于可信执行环境的联邦学习算法研究[D]. 杭州: 浙江大学, 2024. | |
| [15] | HE Jiahao. Research and Implementation of Data Privacy Protection Method for Fabric Consortium Chain Based on Trusted Execution Environment[D]. Nanjing: Southeast University, 2023. |
| 何嘉昊. 基于可信执行环境的Fabric联盟链数据隐私保护方法研究与实现[D]. 南京: 东南大学, 2023. | |
| [16] |
SULTAN N H, VARADHARAJAN V, ZHOU Lan, et al. A Role-Based Encryption(RBE) Scheme for Securing Outsourced Cloud Data in a Multi-Organization Context[J]. IEEE Transactions on Services Computing, 2022, 16(3): 1647-1661.
doi: 10.1109/TSC.2022.3194252 URL |
| [1] | 林甜甜, 王奕天, 王小航, 竺婷, 任奎. CCASim:Arm机密计算架构性能仿真器研究[J]. 信息网络安全, 2026, 26(2): 189-210. |
| [2] | 拾以娟, 周丹平, 范磊, 刘茵. 基于可信执行环境的安全多方计算协议[J]. 信息网络安全, 2025, 25(9): 1439-1446. |
| [3] | 胡文澳, 严飞, 张立强. 一种面向NPU内存侧信道攻击的安全防护方案[J]. 信息网络安全, 2025, 25(6): 977-987. |
| [4] | 郝萌, 李佳勇, 杨洪伟, 张伟哲. 异构CPU-GPU系统机密计算综述[J]. 信息网络安全, 2025, 25(11): 1658-1672. |
| [5] | 关志, 胡建斌, 李悦, 陈钟. 基于可信执行环境的区块链技术与应用综述[J]. 信息网络安全, 2025, 25(11): 1673-1690. |
| [6] | 薛开平, 张淳一, 柳枫, 王峰. 基于可信执行环境的加密数据库索引安全增强方案[J]. 信息网络安全, 2025, 25(11): 1718-1731. |
| [7] | 赵波, 吕佳敏, 王一琁. 一种面向容器生命周期的多维安全度量架构[J]. 信息网络安全, 2025, 25(11): 1745-1761. |
| [8] | 王亚杰, 陆锦标, 李宇航, 范青, 张子剑, 祝烈煌. 基于可信执行环境的联邦学习分层动态防护算法[J]. 信息网络安全, 2025, 25(11): 1762-1773. |
| [9] | 卢笛, 刘玉佳, 吕超越, 孙梦娜, 张清文, 杨力. 一种云原生TEE服务共享机制[J]. 信息网络安全, 2025, 25(11): 1774-1791. |
| [10] | 金娃, 秦宇, 刘菁润, 尚科彤, 贾梦涵, 林江南. 基于机密计算平台的TEE和TPM硬件可信信道构建方案[J]. 信息网络安全, 2025, 25(11): 1792-1810. |
| [11] | 胡宇义, 蔡炜, 陈竞凡, 刘莫寒, 王鹃, 何运. 面向机密容器的统一远程证明机制研究[J]. 信息网络安全, 2025, 25(11): 1811-1823. |
| [12] | 余发江, 王朝州. TrustZone半虚拟化与容器化实现机制[J]. 信息网络安全, 2025, 25(10): 1523-1536. |
| [13] | 孙钰, 熊高剑, 刘潇, 李燕. 基于可信执行环境的安全推理研究进展[J]. 信息网络安全, 2024, 24(12): 1799-1818. |
| [14] | 唐雨, 张驰. 一种基于Intel SGX的信息中心网络隐私保护方案[J]. 信息网络安全, 2023, 23(6): 55-65. |
| [15] | KELEKET GOMA Christy Junior Yannick, 易文哲, 王鹃. 一种基于SGX的轻量Fabric链码可信执行环境构建方法[J]. 信息网络安全, 2022, 22(7): 73-83. |
| 阅读次数 | ||||||
|
全文 |
|
|||||
|
摘要 |
|
|||||