信息网络安全 ›› 2026, Vol. 26 ›› Issue (2): 304-314.doi: 10.3969/j.issn.1671-1122.2026.02.010
基于过程间字符串常量分析的Java注入漏洞检测方法
1.先进计算与智能工程(国家级)实验室 无锡 214100 2.江南大学信息化建设管理处 无锡 214122 3.江南计算技术研究所 无锡 214083
-
收稿日期:2025-01-04出版日期:2026-02-10发布日期:2026-02-23 -
通讯作者:许朴 cuanduo@126.com -
作者简介:许朴(1991—),男,江苏,工程师,硕士,主要研究方向为网络安全|孙心怡(1991—),女,江苏,工程师,硕士,主要研究方向为教育信息化|朱永根(1989—),男,江苏,工程师,本科,主要研究方向为网络安全
A Method for Detecting Java Injection Vulnerabilities Based on Interprocedure Constant String Analysis
XU Pu1( ), SUN Xinyi2, ZHU Yonggen3
), SUN Xinyi2, ZHU Yonggen3
1. Laboratory for Advanced Computing and Intelligence Engineering Wuxi 214100, China 2. Information Construction Management Division of Jiangnan University Wuxi 214122, China 3. Jiangnan Institute of Computing Technology Wuxi 214083, China
-
Received:2025-01-04Online:2026-02-10Published:2026-02-23
摘要:
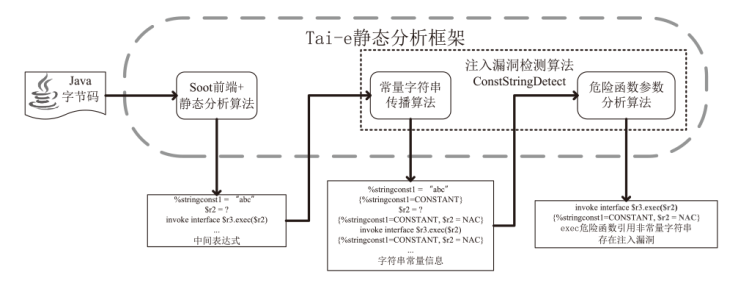
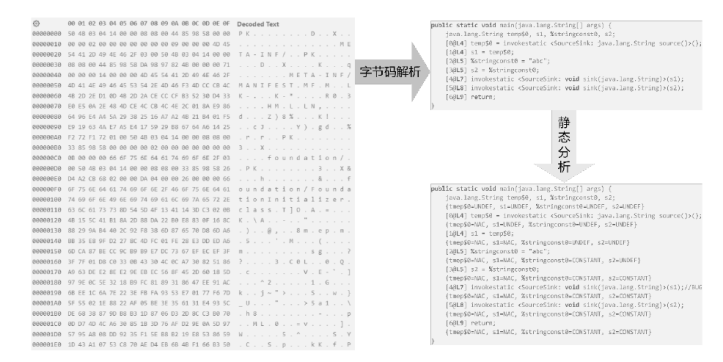
静态分析包含控制流分析、数据流分析、指针分析、污点分析等方法。这些方法能够基于抽象解释理论在不同抽象域上对程序进行分析,从而获取程序信息。这些信息可以用来辅助编译优化、程序理解、漏洞检测等。注入漏洞是由外部输入危险函数而产生的。针对注入漏洞,静态分析主要采用规则匹配和污点分析两种方案进行检测。规则匹配方案是基于语法规则模版进行漏洞匹配,其误报率较高;污点分析方案利用污点源到目标位置的可达性进行漏洞检测,其依赖污点源及传播规则的完备性。文章利用字符串常量传播算法实现程序中变量引用字符串信息分析,然后,通过字符串信息的危险函数参数分析算法实现对注入漏洞的检测。文章在开源Java静态分析框架Tai-e上实现,该方法命名为ConstStringDetect。在Juliet java v1.3和OWASP v1.2测试集上进行实验,测试CWE-078(命令注入漏洞)、CWE-089(SQL注入漏洞)和CWE-090(LDAP注入漏洞)3种注入漏洞。实验结果表明,文章方法相较于先进静态漏洞检测工具SpotBugs和CodeQL,在没有针对特定函数规则的情况下,召回率高于CodeQL,误报率远低于SpotBugs。
中图分类号:
引用本文
许朴, 孙心怡, 朱永根. 基于过程间字符串常量分析的Java注入漏洞检测方法[J]. 信息网络安全, 2026, 26(2): 304-314.
XU Pu, SUN Xinyi, ZHU Yonggen. A Method for Detecting Java Injection Vulnerabilities Based on Interprocedure Constant String Analysis[J]. Netinfo Security, 2026, 26(2): 304-314.
表2
过程内字符串传播规则
| 语句种类 | 语句示例 | 字符串传播规则 |
|---|---|---|
| 对象创建 | l : lvar = new T() | |
| 字符串创建 | l : lvar = “abc” | |
| 变量复制 | l : lvar = rvar | |
| 方法调用 | l : lvar = rvar.k(a1,…, an) |
表3
存在注入可能的危险函数及相应参数
| 漏洞类型 | 类 | 危险函数 | 参数位置 |
|---|---|---|---|
| CWE-078 命令注入 | java.lang.Runtime | exec | all |
| java.lang.ProcessBuilder | command | 0 | |
| <init> | 0 | ||
| CWE-089 SQL注入 | java.sql.Statement | execute | 0 |
| addBatch | 0 | ||
| executeQuery | 0 | ||
| executeUpdate | 0 | ||
| java.sql.Connection | prepareCall | 0 | |
| prepareStatement | 0 | ||
| org.springframework.jdbc.core.JdbcTemplate | queryForObject | 0 | |
| queryForRowSet | 0 | ||
| queryForMap | 0 | ||
| queryForList | 0 | ||
| query | 0 | ||
| execute | 0 | ||
| batchUpdate | 0 | ||
| CWE-090 LDAP 注入 | javax.naming.directory.DirContext | search | 1 |
| javax.naming.directory.InitialDirContext | search | 1 |
表5
注入漏洞测试结果
| 测试工具 | 测试对象 | TP | FN | TN | FP | Total | TPR | FPR | Score |
|---|---|---|---|---|---|---|---|---|---|
| ConstStringDetect | Juliet Java CWE-078 | 444 | 0 | 600 | 24 | 1068 | 100% | 3.85% | 96.15% |
| SpotBugs+FindSecBugs | Juliet Java CWE-078 | 444 | 0 | 0 | 624 | 1068 | 100% | 100.00% | 0 |
| CodeQL(ExecTainted.ql+ ExecTaintedLocal.ql) | Juliet Java CWE-078 | 444 | 0 | 612 | 12 | 1068 | 100% | 1.92% | 98.08% |
| CodeQL(ExecUnescaped.ql) | Juliet Java CWE-078 | 222 | 222 | 390 | 234 | 1068 | 50% | 37.50% | 12.50% |
| ConstStringDetect | OWASP CWE-078 | 126 | 0 | 57 | 68 | 251 | 100% | 54.40% | 45.60% |
| SpotBugs+FindSecBugs | OWASP CWE-078 | 126 | 0 | 14 | 111 | 251 | 100% | 88.80% | 11.20% |
| CodeQL(ExecTainted.ql+ ExecTaintedLocal.ql) | OWASP CWE-078 | 98 | 28 | 64 | 61 | 251 | 77.78% | 48.80% | 28.98% |
| CodeQL(ExecUnescaped.ql) | OWASP CWE-078 | 0 | 126 | 106 | 19 | 251 | 0 | 15.20% | -15.20% |
| ConstStringDetect | Juliet Java CWE-089 | 592 | 0 | 784 | 32 | 1408 | 100% | 3.92% | 96.08% |
| SpotBugs+FindSecBugs | Juliet Java CWE-089 | 592 | 0 | 0 | 816 | 1408 | 100% | 100% | 0 |
| CodeQL(SqlTainted.ql+ SqlTaintedLocal.ql) | Juliet Java CWE-089 | 592 | 0 | 800 | 16 | 1408 | 100% | 1.96% | 98.04% |
| CodeQL(SqlConcatenated.ql) | Juliet Java CWE-089 | 407 | 185 | 485 | 331 | 1408 | 68.75% | 40.56% | 28.19% |
| ConstStringDetect | OWASP CWE-089 | 272 | 0 | 127 | 105 | 504 | 100% | 45.26% | 54.74% |
| SpotBugs+FindSecBugs | OWASP CWE-089 | 272 | 0 | 43 | 189 | 504 | 100% | 81.47% | 18.53% |
| CodeQL(SqlTainted.ql+ SqlTaintedLocal.ql) | OWASP CWE-089 | 272 | 0 | 145 | 87 | 504 | 100% | 37.50% | 62.50% |
| CodeQL(SqlConcatenated.ql) | OWASP CWE-089 | 0 | 272 | 112 | 120 | 504 | 0 | 51.72% | -51.72% |
| ConstStringDetect | Juliet Java CWE-090 | 444 | 0 | 600 | 24 | 1068 | 100% | 3.85% | 96.15% |
| SpotBugs+FindSecBugs | Juliet Java CWE-090 | 444 | 0 | 0 | 624 | 1068 | 100% | 100% | 0 |
| CodeQL(Ldapinjection.ql) | Juliet Java CWE-090 | 222 | 222 | 618 | 6 | 1068 | 50% | 0.96% | 49.04% |
| ConstStringDetect | OWASP CWE-090 | 27 | 0 | 18 | 14 | 59 | 100% | 43.75% | 56.25% |
| SpotBugs+FindSecBugs | OWASP CWE-090 | 27 | 0 | 5 | 27 | 59 | 100% | 100% | 0 |
| CodeQL(Ldapinjection.ql) | OWASP CWE-090 | 27 | 0 | 19 | 13 | 59 | 100% | 40.63% | 59.37% |
| [1] |
QU Zhenqing, LING Xiang, WANG Ting, et al. AdvSQLi: Generating Adversarial SQL Injections against Real-World WAF-as-a-Service[J]. IEEE Transactions on Information Forensics and Security, 2024, 19: 2623-2638.
doi: 10.1109/TIFS.2024.3350911 URL |
| [2] | ERIK, FABIO, ZHU Chang, et al. Toss a Fault to Your Witcher: Applying Grey-box Coverage-Guided Mutational Fuzzing to Detect SQL and Command Injection Vulnerabilities[C]// IEEE. 2023 IEEE Symposium on Security and Privacy (SP). New York: IEEE, 2023: 2658-2675. |
| [3] | YIN Xiaokang, CAI Ruijie, ZHANG Yizheng, et al. Accelerating Command Injection Vulnerability Discovery in Embedded Firmware with Static Backtracking Analysis[C]// ACM. The 12th International Conference on the Internet of Things (IoT ’22). New York: ACM, 2023: 65-72. |
| [4] | CHEN Libo, WANG Yanhao, CAI Quanpu, et al. Sharing More and Checking Less: Leveraging Common Input Keywords to Detect Bugs in Embedded Systems[C]// USENIX. The 30th USENIX Security Symposium. Berkeley: USENIX, 2021: 303-319. |
| [5] | BENJAMIN, EUGENE, QIN Zhiguang. SQL Injection Attack Detection Using Fingerprints and Pattern Matching Technique[C]// IEEE. 2017 8th IEEE International Conference on Software Engineering and Service Science (ICSESS). New York: IEEE, 2017: 583-587. |
| [6] | CHENG Kai, LI Qiang, WANG Lei, et al. DTaint: Detecting the Taint-Style Vulnerability in Embedded Device Firmware[C]// IEEE. The 48th Annual IEEE/IFIP International Conference on Dependable Systems and Networks (DSN). New York: IEEE, 2018: 430-441. |
| [7] | TAN Tian, LI Yue. Tai-E: A Developer-Friendly Static Analysis Framework for Java by Harnessing the Good Designs of Classics[C]// ACM. The 32nd ACM SIGSOFT International Symposium on Software Testing and Analysis (ISSTA 2023). New York: ACM, 2023: 1093-1105. |
| [8] | BODDEN E. Soot: A Framework for Analyzing and Transforming Java and Android Applications[EB/OL]. [2024-4-15]. http://soot-oss.github.io/soot/. |
| [9] |
SMARAGDAKIS Y, BALATSOURAS G. Pointer Analysis[J]. Foundations and Trends in Programming Languages, 2015, 2(1): 1-69.
doi: 10.1561/PGL URL |
| [10] | ANDERSEN L O. Program Analysis and Specialization for the C Programming Language[D]. Copenhagen: University of Copenhagen, DIKU, 1994. |
| [11] | BEN, CALVIN. Flow-Sensitive Pointer Analysis for Millions of Lines of Code[C]// IEEE. International Symposium on Code Generation and Optimization (CGO 2011). New York: IEEE, 2011: 289-298. |
| [12] | TAN Tian, MA Xiaoxing, XU Chang, et al. Survey on Java Pointer Analysis[J]. Journal of Computer Research and Development, 2023, 60(2): 274-293. |
| 谭添, 马晓星, 许畅, 等. Java指针分析综述[J]. 计算机研究与发展, 2023, 60(2): 274-293. | |
| [13] | LIU Jie, LI Yue, TAN Tian, et al. Reflection Analysis for Java: Uncovering More Reflective Targets Precisely[C]// IEEE. 2017 IEEE 28th International Symposium on Software Reliability Engineering (ISSRE). New York: IEEE, 2017: 12-23. |
| [14] | The University of Maryland. SpotBugs[EB/OL]. [2024-04-15]. https://spotbugs.github.io/. |
| [15] | FABIAN, NICO, DANIEL, et al. Modeling and Discovering Vulnerabilities with Code Property Graphs[C]// IEEE. 2014 IEEE Symposium on Security and Privacy. New York: IEEE, 2014: 590-604. |
| [16] | OEGE, MATHIEU, ELNAR, et al. Keynote Address:.QL for Source Code Analysis[C]// IEEE. Seventh IEEE International Working Conference on Source Code Analysis and Manipulation (SCAM 2007). New York: IEEE, 2007: 3-16. |
| [17] | Gary A. Kildall. A Unified Approach To Global Program Optimization[C]// IEEE. The 1st annual ACM SIGACT-SIGPLAN symposium on Principles of programming languages (POPL ’73). New York: ACM, 1973: 194-206. |
| [18] | Kam, John B. and Jeffrey D. Ullman. Monotone Data Flow Analysis Frameworks[J]. Acta Informatica, 1977, 7: 305-317. |
| [19] | CHEN Liqian, FAN Guangsheng, YIN Banghu, et al. Research Progress on Abstract Interpretation and Its Application[J]. Journal of Computer Research and Development, 2023, 60(2): 227-247. |
| 陈立前, 范广生, 尹帮虎, 等. 抽象解释及其应用研究进展[J]. 计算机研究与发展, 2023, 60(2): 227-247. | |
| [20] | COUSOT P, COUSOT R. Abstract Interpretation: A Unified Lattice Model for Static Analysis of Programs By Construction Or Approximation of Fixpoints[C]// ACM. The 4th ACM SIGACT-SIGPLAN Symposium on Principles of Programming Languages. New York: ACM, 1977: 238-252. |
| [21] | NIST. Juliet Java[EB/OL]. [2024-04-15]. https://samate.nist.gov/SARD/test-suites/111. |
| [22] | OWASP Foundation. OWASP Benchmark[EB/OL]. [2024-04-15]. https://owasp.org/www-project-benchmark/. |
| [1] | 陶慈, 陈昊然, 陈平. 面向工控系统的C语言异常处理路径定向模糊测试方法[J]. 信息网络安全, 2026, 26(2): 211-223. |
| [2] | 张光华, 李国瑜, 王鹤, 李珩, 武少广. 基于污点流分析的物联网固件高可信度漏洞检测[J]. 信息网络安全, 2026, 26(2): 325-337. |
| [3] | 詹东阳, 黄子龙, 谭凯, 俞兆丰, 贺铮, 张宏莉. 面向Serverless应用的跨函数行为分析与约束技术[J]. 信息网络安全, 2025, 25(9): 1329-1337. |
| [4] | 叶佳骏, 高翠凤, 薛吟兴. 基于静态分析的价格预言机操纵源代码检测方法研究[J]. 信息网络安全, 2025, 25(5): 732-746. |
| [5] | 张学旺, 卢荟, 谢昊飞. 基于节点中心性和大模型的漏洞检测数据增强方法[J]. 信息网络安全, 2025, 25(4): 550-563. |
| [6] | 张雨轩, 黄诚, 柳蓉, 冷涛. 结合提示词微调的智能合约漏洞检测方法[J]. 信息网络安全, 2025, 25(4): 664-673. |
| [7] | 许良晨, 孟昭逸, 黄文超, 熊焰. 面向程序可达性验证的数组处理循环压缩方法[J]. 信息网络安全, 2024, 24(3): 374-384. |
| [8] | 李鹏超, 张全涛, 胡源. 基于双注意力机制图神经网络的智能合约漏洞检测方法[J]. 信息网络安全, 2024, 24(11): 1624-1631. |
| [9] | 陈星任, 熊焰, 黄文超, 付贵禄. 一种基于静态分析的多视图硬件木马检测方法[J]. 信息网络安全, 2023, 23(10): 48-57. |
| [10] | 张光华, 刘永升, 王鹤, 于乃文. 基于BiLSTM和注意力机制的智能合约漏洞检测方案[J]. 信息网络安全, 2022, 22(9): 46-54. |
| [11] | 杨铭, 张健. 基于图像识别的恶意软件静态检测模型[J]. 信息网络安全, 2021, 21(10): 25-32. |
| [12] | 李明磊, 黄晖, 陆余良. 面向漏洞挖掘的基于符号分治区的测试用例生成技术[J]. 信息网络安全, 2020, 20(5): 39-46. |
| [13] | 胡建伟, 赵伟, 闫峥, 章芮. 基于机器学习的SQL注入漏洞挖掘技术的分析与实现[J]. 信息网络安全, 2019, 19(11): 36-42. |
| [14] | 文伟平, 李经纬, 焦英楠, 李海林. 一种基于随机探测算法和信息聚合的漏洞检测方法[J]. 信息网络安全, 2019, 19(1): 1-7. |
| [15] | 陈虎, 周瑶, 赵军锁. 针对特定文件结构和关键指令的符号执行优化方法[J]. 信息网络安全, 2018, 18(9): 86-94. |
| 阅读次数 | ||||||
|
全文 |
|
|||||
|
摘要 |
|
|||||