信息网络安全 ›› 2026, Vol. 26 ›› Issue (2): 291-303.doi: 10.3969/j.issn.1671-1122.2026.02.009
基于Moran过程和随机演化博弈模型的网络防御决策方法
网络空间部队信息工程大学密码工程学院 郑州 450001
-
收稿日期:2025-05-24出版日期:2026-02-10发布日期:2026-02-23 -
通讯作者:胡航 huhang_hh@163.com -
作者简介:胡航(1994—),男,河南,硕士研究生,主要研究方向为网络安全博弈|冯凯(1995—),男,陕西,硕士研究生,主要研究方向为防御建模和安全评估|谭晶磊(1994—),男,山东,讲师,博士,主要研究方向为网络安全博弈与智能决策|张玉臣(1977—),男,河南,教授,博士,主要研究方向为网络空间安全 -
基金资助:国家自然科学基金(62502103);中国博士后科学基金(2025M771548)
Network Defense Decision-Making Method Based on Moran Process and Stochastic Evolutionary Game Model
HU Hang( ), FENG Kai, TAN Jinglei, ZHANG Yuchen
), FENG Kai, TAN Jinglei, ZHANG Yuchen
School of Cryptographic Engineering ,Cyberspace Force Information Engineering University Zhengzhou 450001, China
-
Received:2025-05-24Online:2026-02-10Published:2026-02-23
摘要:
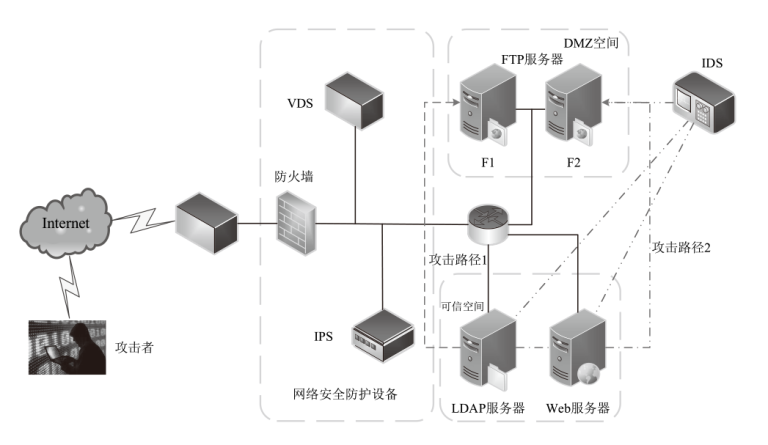
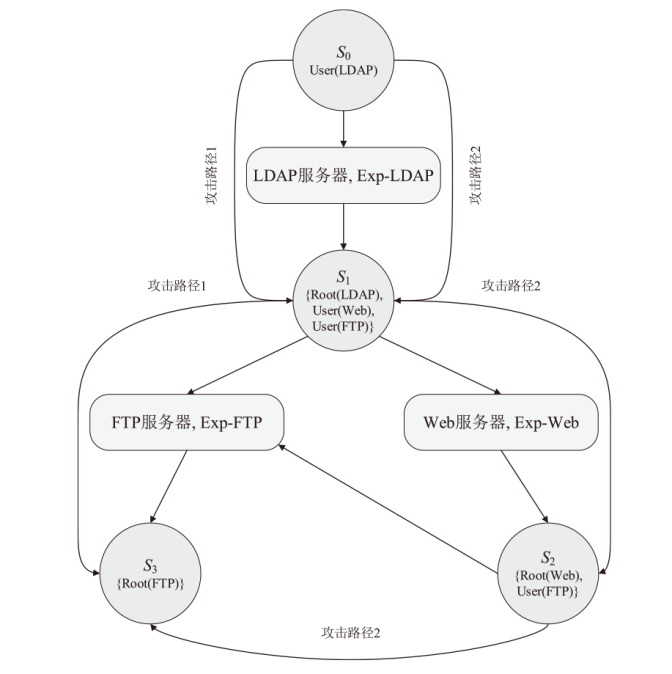
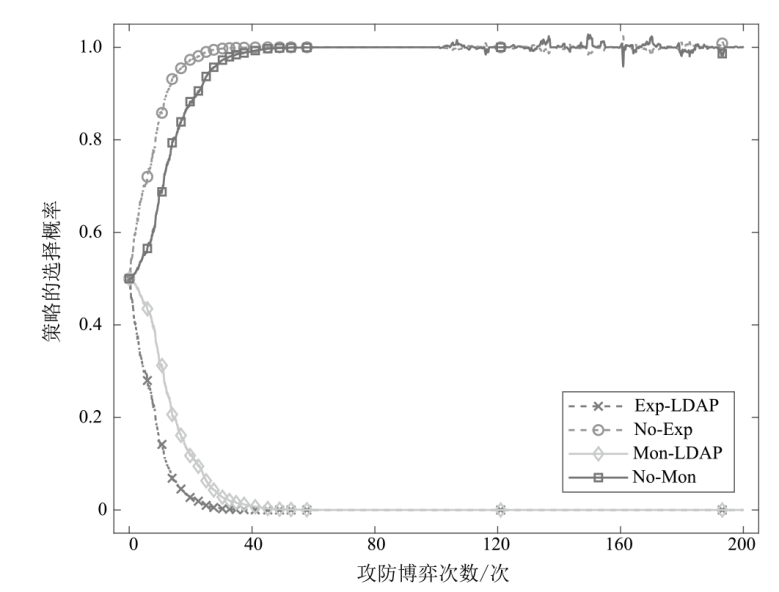
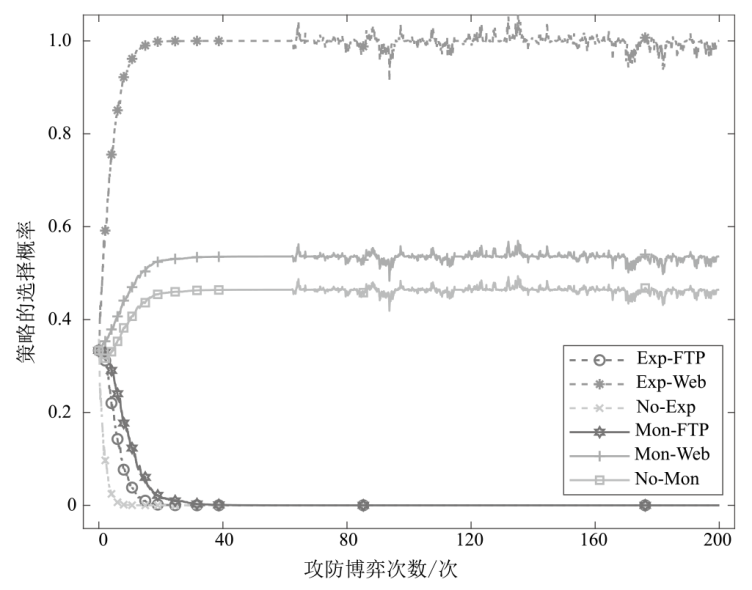
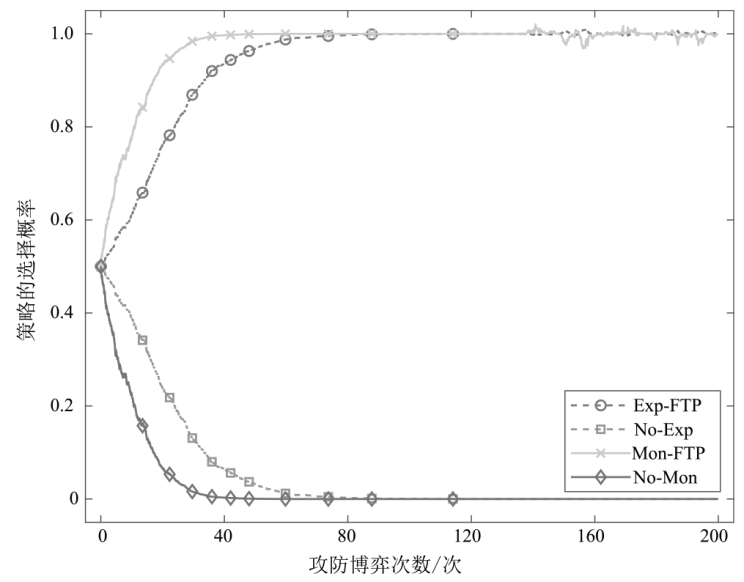
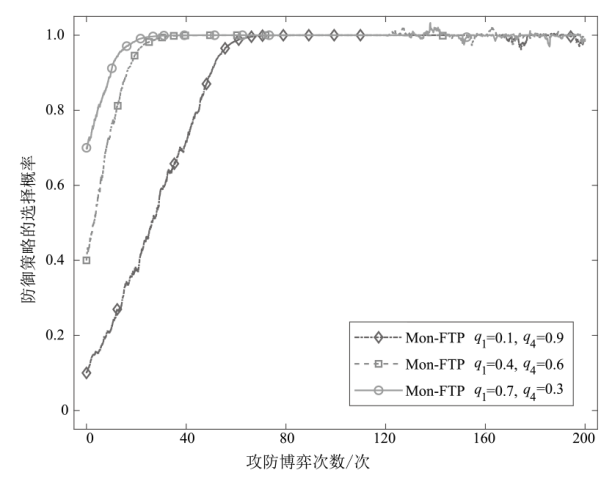
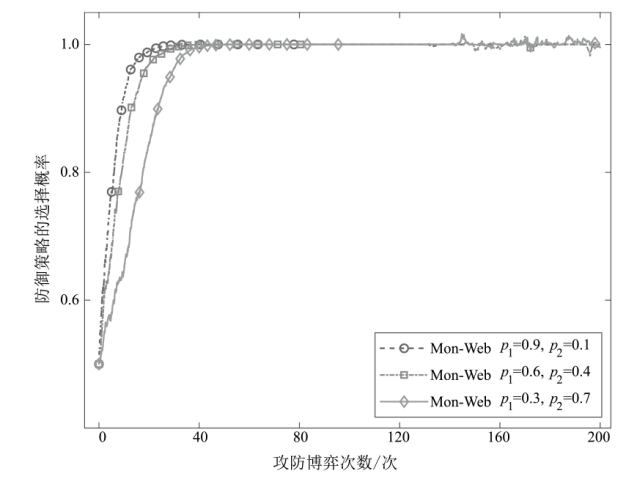
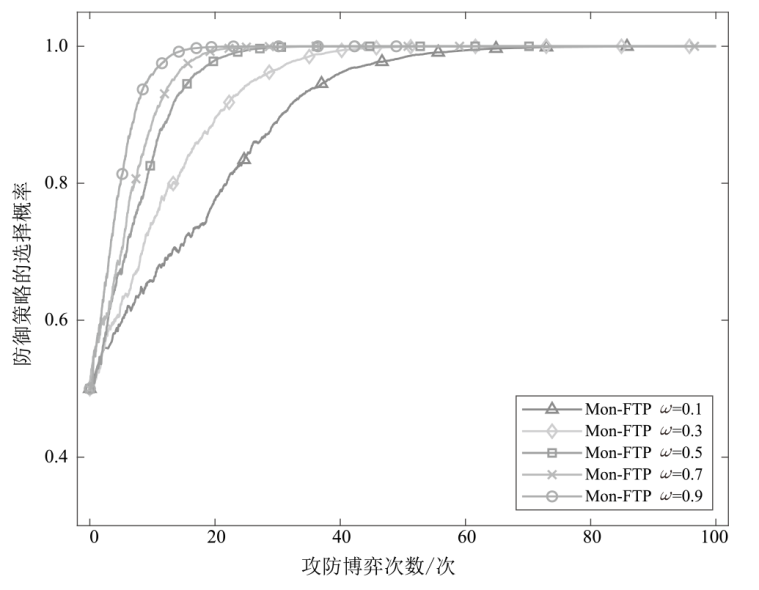
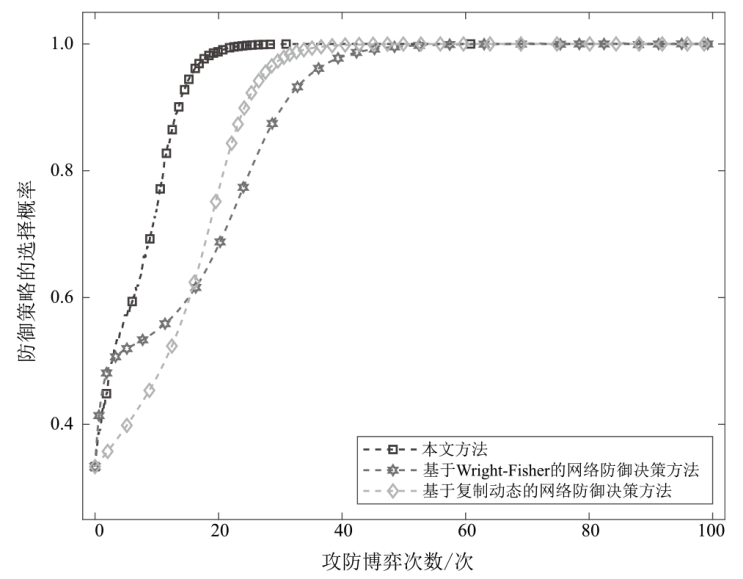
现有的网络防御决策方法大多基于攻防双方完全理性的假设以及确定性博弈模型,难以模拟实际网络攻防场景,导致实用性较差。为更好地适应有限理性条件下的网络攻防博弈场景,文章提出了基于Moran过程和随机演化博弈模型的网络防御决策方法,引入选择强度系数描述攻防双方对优势策略的偏好程度,通过求解攻防策略动态演化方程设计最优防御策略决策算法,并刻画策略选择的演化轨迹。数值仿真实验结果验证了文章所提方法的科学性和有效性,分析探讨了不同网络状态下攻防策略的演变规律。同时,与基于Wright-Fisher和基于复制动态的网络防御决策方法相比,文章所提最优防御策略的收敛速度分别提高了23.1%和17.4%,表明该方法在学习效率和收敛速度方面具有优势。
中图分类号:
引用本文
胡航, 冯凯, 谭晶磊, 张玉臣. 基于Moran过程和随机演化博弈模型的网络防御决策方法[J]. 信息网络安全, 2026, 26(2): 291-303.
HU Hang, FENG Kai, TAN Jinglei, ZHANG Yuchen. Network Defense Decision-Making Method Based on Moran Process and Stochastic Evolutionary Game Model[J]. Netinfo Security, 2026, 26(2): 291-303.
| [1] | MATHEU S N, HERNANDEZ-RAMOS J L, SKARMETA A F, et al. A Survey of Cybersecurity Certification for the Internet of Things[J]. ACM Computing Surveys, 2021, 53(6): 1-36. |
| [2] | OSBORNE M J. Introduction to GAME THEory[M]. Oxford: Oxford University Press, 2003. |
| [3] |
KAKKAD V, SHAH H, PATEL R, et al. A Comparative Study of Applications of Game Theory in Cyber Security and Cloud Computing[J]. Procedia Computer Science, 2019, 155: 680-685.
doi: 10.1016/j.procs.2019.08.097 URL |
| [4] | SHARMA D P, ENOCH S Y, CHO J H, et al. Dynamic Security Metrics for Software-Defined Network-Based Moving Target Defense[EB/OL]. (2020-11-15)[2025-02-17]. https://www.sciencedirect.com/science/article/abs/pii/S1084804520302770. |
| [5] | HO E, RAJAGOPALAN A, SKVORTSOV A, et al. Game Theory in Defence Applications: A Review[EB/OL]. (2021-11-02)[2025-02-17]. https://arxiv.org/abs/2111.01876. |
| [6] | HU Hao, LIU Yuling, ZHANG Hongqi, et al. Optimal Network Defense Strategy Selection Based on Incomplete Information Evolutionary Game[J]. IEEE Access, 2018(6): 29806-29821. |
| [7] |
SHAO Chengwu, LI Yanfu. Optimal Defense Resources Allocation for Power System Based on Bounded Rationality Game Theory Analysis[J]. IEEE Transactions on Power Systems, 2021, 36(5): 4223-4234.
doi: 10.1109/TPWRS.2021.3060009 |
| [8] | ZHANG Hengwei, TAN Jinglei, LIU Xiaohu, et al. Moving Target Defense Decision-Making Method: A Dynamic Markov Differential Game Model[C]// ACM. The 7th ACM Workshop on Moving Target Defense. New York: ACM, 2020: 21-29. |
| [9] |
HUANG Jianming, ZHANG Hengwei, WANG Jindong, et al. Defense Strategies Selection Based on Attack-Defense Evolutionary Game Model[J]. Journal on Communications, 2017, 38(1): 168-176.
doi: 10.11959/j.issn.1000-436x.2017019 |
|
黄健明, 张恒巍, 王晋东, 等. 基于攻防演化博弈模型的防御策略选取方法[J]. 通信学报, 2017, 38(1): 168-176.
doi: 10.11959/j.issn.1000-436x.2017019 |
|
| [10] | HUANG Jianming, ZHANG Hengwei. Selection of Optimal Defense Strategies Based on an Improved Replicator Dynamics Evolutionary Game Model[J]. Journal of Communications, 2018, 39(1): 170-182. |
|
黄健明, 张恒巍. 基于改进复制动态演化博弈模型的最优防御策略选取[J]. 通信学报, 2018, 39(1): 170-182.
doi: 10.11959/j.issn.1000-436x.2018010 |
|
| [11] | LIU Yanhua, CHEN Hui, ZHANG Hao, et al. Defense Strategy Selection Model Based on Multistage Evolutionary Game Theory[EB/OL]. (2021-12-11)[2025-02-17]. https://onlinelibrary.wiley.com/doi/10.1155/2021/4773894. |
| [12] | WU Zenan, TIAN Liqin, ZHANG Yi, et al. Network Attack and Defense Modeling and System Security Analysis: A Novel Approach Using Stochastic Evolutionary Game Petri Net[EB/OL]. (2021-11-13)[2025-02-17]. https://onlinelibrary.wiley.com/doi/10.1155/2021/4005877. |
| [13] |
ZHANG Hengwei, TAN Jinglei, LIU Xiaohu, et al. Cybersecurity Threat Assessment Integrating Qualitative Differential and Evolutionary Games[J]. IEEE Transactions on Network and Service Management, 2022, 19(3): 3425-3437.
doi: 10.1109/TNSM.2022.3166348 URL |
| [14] |
TAN Jinglei, JIN Hui, HU Hao, et al. WF-MTD: Evolutionary Decision Method for Moving Target Defense Based on Wright-Fisher Process[J]. IEEE Transactions on Dependable and Secure Computing, 2023, 20(6): 4719-4732.
doi: 10.1109/TDSC.2022.3232537 URL |
| [15] | MA Runnian, ZHANG Enning, WANG Gang, et al. A Network Defense Decision-Making Method Based on an Improved Evolutionary Game Model[J]. Journal of Electronics & Information Technology, 2023, 45(6): 1970-1980. |
| [16] |
JIN Hui, ZHANG Senlei, ZHANG Bin, et al. Evolutionary Game Decision-Making Method for Network Attack and Defense Based on Regret Minimization Algorithm[J]. Journal of King Saud University-Computer and Information Sciences, 2023, 35(3): 292-302.
doi: 10.1016/j.jksuci.2023.01.018 URL |
| [17] | HAN Tiaojuan, LU Jianfeng, ZHANG Hao, et al. Evolution Analysis of Low-Carbon Cooperation of Service Providers Based on Moran Process in Cloud Manufacturing[EB/OL]. (2024-03-21)[2025-02-17]. https://doi.org/10.1371/journal.pone.0299952. |
| [18] | WANG Xianjia, GU Cuiling, ZHAO Jinhua, et al. Stochastic Evolution Dynamic Model of Moran Process with Selection Difference and Its Application[J]. Systems Engineering-Theory & Practice, 2020, 40(5): 1193-1209. |
|
王先甲, 顾翠伶, 赵金华, 等. 选择差异下Moran过程的随机博弈模型及其应用[J]. 系统工程理论与实践, 2020, 40(5): 1193-1209.
doi: 10.12011/1000-6788-2019-1494-17 |
|
| [19] | XU Yanping, ZHU Lilong. Pharmaceutical Enterprises’ R&D Innovation Cooperation Moran Strategy When Considering Tax Incentives[EB/OL]. (2022-11-17)[2025-02-17]. https://www.mdpi.com/1660-4601/19/22/15197. |
| [20] | ZHU Lilong, XU Yanping. Pharmaceutical Enterprises’ Quality Management Decision Moran Analysis under Blockchain Technology-Based on the Perspective of Prospect Theory[EB/OL]. (2024-08-19)[2025-02-17]. https://www.cnki.com.cn/Article/CJFDTotal-ZGGK20240312002.htm. |
| 朱立龙, 徐艳萍. 区块链技术下医药企业质量管理决策Moran分析—基于前景理论的视角[EB/OL]. (2024-08-19)[2025-02-17]. https://www.cnki.com.cn/Article/CJFDTotal-ZGGK20240312002.htm. | |
| [21] | HE Shuhong, HUANG Zhenxiong. The Random Evolutionary Game Model of Disaster Reduction Cooperation Development in the Lancang-Mekong Sub-Region[J]. Journal of Catastrophology, 2024, 39(4): 76-80. |
| 何树红, 黄振雄. 澜湄次区域减灾合作发展的随机演化博弈模型[J]. 灾害学, 2024, 39(4): 76-80. | |
| [22] |
WHIGHAM P A, DICK G. Evolutionary Dynamics for the Spatial Moran Process[J]. Genetic Programming and Evolvable Machines, 2008, 9(2): 157-170.
doi: 10.1007/s10710-007-9046-6 URL |
| [23] |
NOWAK M A, SASAKI A, TAYLOR C, et al. Emergence of Cooperation and Evolutionary Stability in Finite Populations[J]. Nature, 2004, 428(6983): 646-650.
doi: 10.1038/nature02414 |
| [24] | TRAULSEN A, CLAUSSEN J C, HAUERT C. Coevolutionary Dynamics: From Finite to Infinite Populations[EB/OL]. (2005-12-02)[2025-02-17]. https://journals.aps.org/prl/abstract/10.1103/PhysRevLett.95.238701. |
| [25] | LEI Cheng, MA Duohe, ZHANG Hongqi. Optimal Strategy Selection for Moving Target Defense Based on Markov Game[J]. IEEE Access, 2017(5): 156-169. |
| [1] | 王焕臻, 徐洪平, 李旷代, 刘洋, 姚琳元. 一种基于分层强化学习的网络防御自主决策研究[J]. 信息网络安全, 2026, 26(1): 91-101. |
| [2] | 金志刚, 王新建, 李根, 岳顺民. 融合攻击图和博弈模型的网络防御策略生成方法[J]. 信息网络安全, 2021, 21(1): 1-9. |
| [3] | 金辉, 张红旗, 张传富, 胡浩. 复杂网络中基于QRD的主动防御决策方法研究[J]. 信息网络安全, 2020, 20(5): 72-82. |
| [4] | 池水明;周苏杭. DDoS攻击防御技术研究[J]. , 2012, 12(5): 0-0. |
| [5] | 吴晓明;李莉. 构建可信可控的内网防御体系[J]. , 2010, (5): 0-0. |
| [6] | 隋京;黄晓峰. 蜜罐技术及其在网络安全中的应用分析[J]. , 2010, (12): 0-0. |
| 阅读次数 | ||||||
|
全文 |
|
|||||
|
摘要 |
|
|||||