信息网络安全 ›› 2026, Vol. 26 ›› Issue (2): 211-223.doi: 10.3969/j.issn.1671-1122.2026.02.003
面向工控系统的C语言异常处理路径定向模糊测试方法
1.复旦大学大数据研究院 上海 200433 2.复旦大学软件学院 上海 200433
-
收稿日期:2025-06-27出版日期:2026-02-10发布日期:2026-02-23 -
通讯作者:陈平 pchen@fudan.edu.cn -
作者简介:陶慈(2003—),女,安徽,博士研究生,主要研究方向为系统安全|陈昊然(1997—),男,黑龙江,硕士,主要研究方向为网络安全、区块链|陈平(1985—),男,江苏,研究员,博士,主要研究方向为软件和系统安全 -
基金资助:国家重点研发计划(2022YFB3104300)
A Directed Fuzz Testing Method for C Language Exception Handling Paths in Industrial Control Systems
TAO Ci1, CHEN Haoran2, CHEN Ping1( )
)
1. Institute of Big Data ,Fudan University Shanghai 200433, China 2. School of Software ,Fudan University Shanghai 200433, China
-
Received:2025-06-27Online:2026-02-10Published:2026-02-23
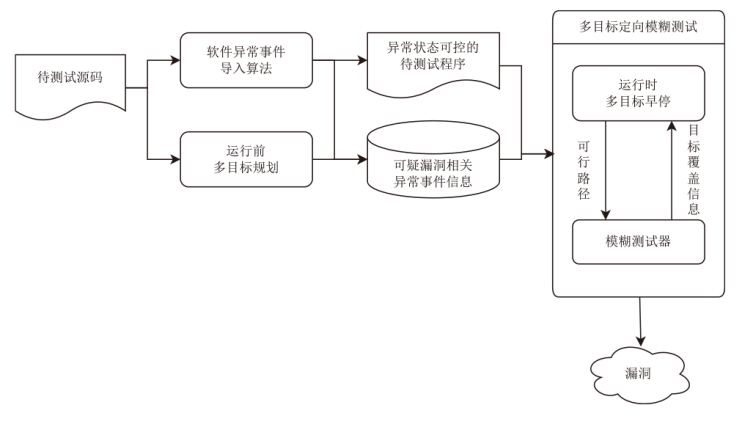
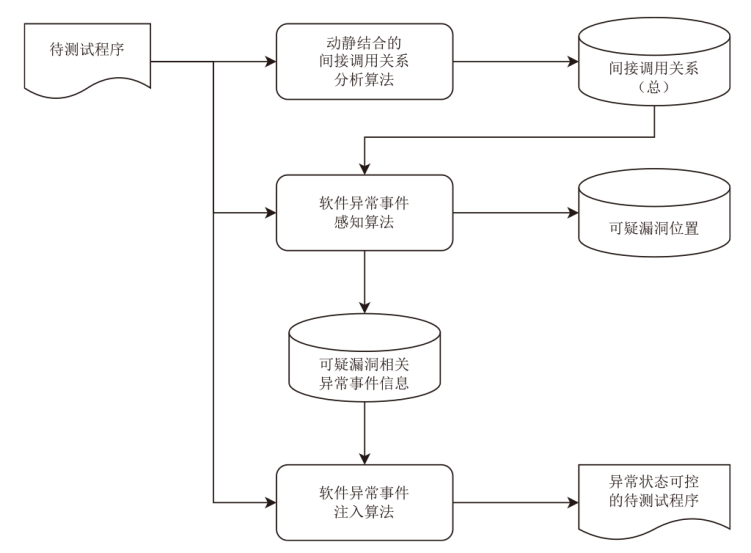
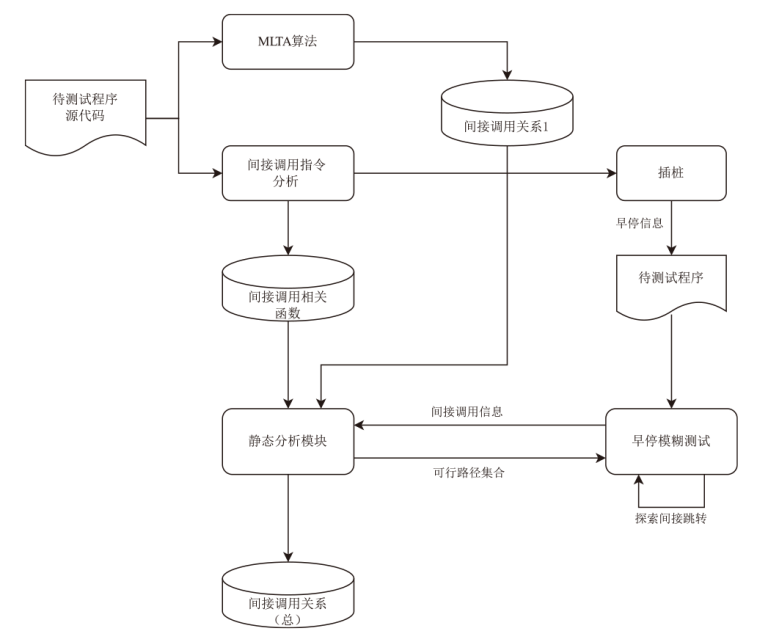
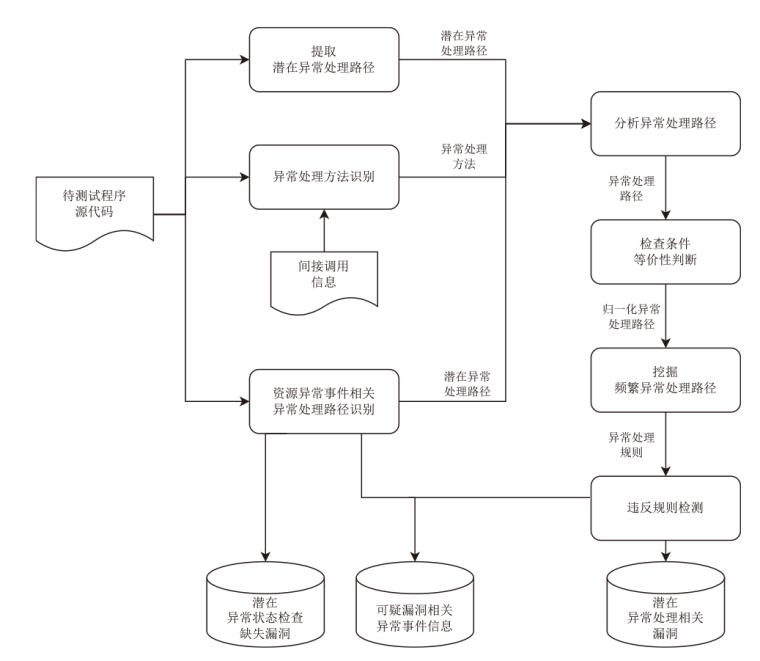
摘要:
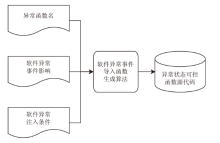
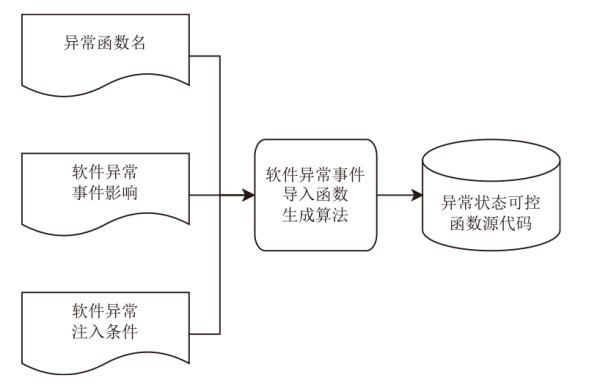
针对工控系统中C语言程序因缺乏统一异常处理机制导致的异常处理漏洞检测难题,文章提出一种面向工控系统的C语言异常处理路径定向模糊测试方法。该方法通过异常测试条件建模与异常处理漏洞检测两个阶段协同工作,提升异常处理相关漏洞的检测能力。在异常测试条件建模阶段,设计软件异常事件导入算法,采用动静结合的间接调用关系分析与异常注入技术,生成异常状态可控的待测试程序;在异常处理漏洞检测阶段,构建多目标定向模糊测试框架 MEFuzz,通过运行前多目标规划与运行时多目标早停算法,动态调节测试资源分配,提高多上下文异常处理路径的探索效率。基于UniBench数据集的实验结果表明,该方法在静态检测准确率(22.22%)与模糊测试漏洞触发总数(294个)上均优于现有工具,改善因子达1.26,能有效提升工控系统C语言程序异常处理路径相关漏洞的检测效果。
中图分类号:
引用本文
陶慈, 陈昊然, 陈平. 面向工控系统的C语言异常处理路径定向模糊测试方法[J]. 信息网络安全, 2026, 26(2): 211-223.
TAO Ci, CHEN Haoran, CHEN Ping. A Directed Fuzz Testing Method for C Language Exception Handling Paths in Industrial Control Systems[J]. Netinfo Security, 2026, 26(2): 211-223.
表2
异常处理路径静态检测效果
| 被测软件 | 漏洞数量与准确率 | 本文方法 | EH-Miner | Crix |
|---|---|---|---|---|
| flvmeta | 可疑漏洞数/个 | 6 | 4 | 5 |
| 实际可疑漏洞数/个 | 2 | 1 | 1 | |
| 准确率 | 33.33% | 25.00% | 20.00% | |
| imginfo | 可疑漏洞数/个 | 2 | 1 | 0 |
| 实际可疑漏洞数/个 | 1 | 0 | 无 | |
| 准确率 | 50.00% | 0 | 无 | |
| tiffsplit | 可疑漏洞数/个 | 25 | 11 | 18 |
| 实际可疑漏洞数/个 | 3 | 1 | 2 | |
| 准确率 | 12.00% | 9.09% | 11.11% | |
| tcpdump | 可疑漏洞数/个 | 5 | 2 | 3 |
| 实际可疑漏洞数/个 | 2 | 1 | 2 | |
| 准确率 | 40.00% | 50.00% | 66.67% | |
| sqlite3 | 可疑漏洞数/个 | 7 | 3 | 5 |
| 实际可疑漏洞数/个 | 2 | 0 | 1 | |
| 准确率 | 28.57% | 0 | 20.00% | |
| 总计 | 可疑漏洞数/个 | 45 | 21 | 31 |
| 实际可疑漏洞数/个 | 10 | 3 | 6 | |
| 准确率 | 22.22% | 14.29% | 19.35% |
表3
模糊测试方法漏洞检测数量
| 被测软件 | 模糊测试方法 | 触发漏洞总数/个 | F |
|---|---|---|---|
| flvmeta | AFL | 22 | — |
| AFL++ | 23 | 1.05 | |
| Windranger | 25 | 1.14 | |
| MEFuzz | 27 | 1.23 | |
| imginfo | AFL | 0 | — |
| AFL++ | 0 | — | |
| Windranger | 0 | — | |
| MEFuzz | 0 | — | |
| tiffsplit | AFL | 28 | — |
| AFL++ | 33 | 1.18 | |
| Windranger | 34 | 1.21 | |
| MEFuzz | 37 | 1.32 | |
| tcpdump | AFL | 162 | — |
| AFL++ | 195 | 1.20 | |
| Windranger | 174 | 1.07 | |
| MEFuzz | 207 | 1.28 | |
| sqlite3 | AFL | 21 | — |
| AFL++ | 25 | 1.19 | |
| Windranger | 24 | 1.14 | |
| MEFuzz | 23 | 1.10 | |
| 总计 | AFL | 233 | — |
| AFL++ | 276 | 1.18 | |
| Windranger | 257 | 1.10 | |
| MEFuzz | 294 | 1.26 |
| [1] | PAKKI A, LU Kangjie. Exaggerated Error Handling Hurts! An In-Depth Study and Contextaware Detection[C]// ACM. The 2020 ACM SIGSAC Conference on Computer and Communications Security. New York: ACM, 2020: 1203-1218. |
| [2] | LU Kangjie, PAKKI A, WU Qiushi. Automatically Identifying Security Checks for Detecting Kernel Semantic Bugs[C]// Springer. The 24th European Symposium on Research in Computer Security, Luxembourg (Computer Security-ESORICS 2019). Heidelberg: Springer, 2019: 3-25. |
| [3] | LU Kangjie, PAKKI A, WU Qiushi. Detecting Missing-Check Bugs via Semantic-and Context-Aware Criticalness and Constraints Inferences[C]// USENIX. The 28th USENIX Security Symposium (USENIX Security 19). Berkely: USENIX, 2019: 1769-1786. |
| [4] | MITRE. CWE-754:Improper Check for Unusual or Exceptional Conditions[EB/OL]. [2025-06-10]. https://cwe.mitre.org/data/definitions/754.html. |
| [5] |
ZHAN Dongyang, YU Xiangzhan, ZHANG Hongli, et al. ErrHunter: Detecting Error-Handling Bugs in the Linux Kernel through Systematic Static Analysis[J]. IEEE Transactions on Software Engineering, 2023, 49(2): 684-698.
doi: 10.1109/TSE.2022.3160155 URL |
| [6] | QASEM A, SHIRANI P, DEBBABI M, et al. Automatic Vulnerability Detection in Embedded Devices and Firmware: Survey and Layered Taxonomies[J]. ACM Computing Surveys, 2021, 54(2): 1-42. |
| [7] | LU Shenming, ZUO Zhiqiang, WANG Linzhang. Progress in Parallelization of Static Program Analysis[J]. Journal of Software, 2020, 31(5): 1243-1254. |
| 陆申明, 左志强, 王林章. 静态程序分析并行化研究进展[J]. 软件学报, 2020, 31(5):1243-1254. | |
| [8] | SONNEKALB T, HEINZE T S, MÄDER P. Deep Security Analysis of Program Code: A Systematic Literature Review[EB/OL]. (2022-01-01)[2025-06-10]. https://doi.org/10.1007/s10664-021-1002. |
| [9] |
LIN Guanjun, WEN Sheng, HAN Qinglong, et al. Software Vulnerability Detection Using Deep Neural Networks: A Survey[J]. Proceedings of the IEEE, 2020, 108(10): 1825-1848.
doi: 10.1109/PROC.5 URL |
| [10] | BODDEN E. Inter-Procedural Data-Flow Analysis with IFDS/IDE and Soot[C]// ACM. The ACM SIGPLAN International Workshop on State of the Art in Java Program Analysis. New York: ACM, 2012: 3-8. |
| [11] | MARJAMÄKI D. Cppcheck: A Tool for Static C/C++ Code Analysis[EB/OL]. [2025-06-10]. https://cppcheck.sourceforge.io. |
| [12] | Checkmarx. Checkmarx[EB/OL]. [2025-06-10]. https://checkmarx.com/. |
| [13] | LI Zhen, ZOU Deqing, XU Shouhuai, et al. VulDeePecker: A Deep Learning-Based System for Vulnerability Detection[EB/OL]. (2018-01-05)[2025-06-10]. https://arxiv.org/abs/1801.01681. |
| [14] | VENKATESH G A. The Semantic Approach to Program Slicing[C]// ACM. The ACM SIGPLAN 1991 Conference on Programming Language Design and Implementation. New York: ACM, 1991: 107-119. |
| [15] |
LI Zhen, ZOU Deqing, XU Shouhuai, et al. SySeVR: A Framework for Using Deep Learning to Detect Software Vulnerabilities[J]. IEEE Transactions on Dependable and Secure Computing, 2022, 19(4): 2244-2258.
doi: 10.1109/TDSC.2021.3051525 URL |
| [16] | CAO Sicong, SUN Xiaobing, BO Lili, et al. MVD: Memory-Related Vulnerability Detection Based on Flow-Sensitive Graph Neural Networks[C]// IEEE. 2022 IEEE/ACM 44th International Conference on Software Engineering(ICSE). New York: IEEE, 2022: 1456-1468. |
| [17] | AHMADI M, FARKHANI R M, WILLIAMS R, et al. Finding Bugs Using Your Own Code: Detecting Functionally-Similar Yet Inconsistent Code[C]// USENIX. The 30th USENIX Security Symposium (USENIX Security 21). Berkely: USENIX, 2021: 2025-2040. |
| [18] | ZHU Xiaogang, WEN Sheng, CAMTEPE S, et al. Fuzzing: A Survey for Roadmap[J]. ACM Computing Surveys, 2022, 54: 1-36. |
| [19] | LIU Peiyu, JI Shouling, ZHANG Xuhong, et al. IFIZZ: Deep-State and Efficient Fault-Scenario Generation to Test Iot Firmware[C]// IEEE. 2021 36th IEEE/ACM International Conference on Automated Software Engineering (ASE). New York: IEEE, 2021: 805-816. |
| [20] | LU Kang jie, HU Hong. Where Does It Go? Refining Indirect-Call Targets with Multi-Layer Type Analysis[C]// ACM. The 2019 ACM SIGSAC Conference on Computer and Communications Security. New York: ACM, 2019: 1867-1881. |
| [21] | SRIVASTAVA P, NAGY S, HICKS M, et al. One Fuzz Doesn’t Fit All: Optimizing Directed Fuzzing via Target-Tailored Program State Restriction[C]// ACM. The 38th Annual Computer Security Applications Conference. New York: ACM, 2022: 388-399. |
| [22] | JIA Zhouyang, LI Shanshan, YU Tingting, et al. Detecting Error-Handling Bugs without Error Specification Input[C]// IEEE. 2019 34th IEEE/ACM International Conference on Automated Software Engineering (ASE). New York: IEEE, 2019: 213-225. |
| [23] | LI Yuwei, JI Shouling, CHEN Yuan, et al. UNIFUZZ: A Holistic and Pragmatic Metrics-Driven Platform for Evaluating Fuzzers[C]// USENIX. The 30th USENIX Security Symposium (USENIX Security 21). Berkely: USENIX, 2021: 2777-2794. |
| [1] | 许朴, 孙心怡, 朱永根. 基于过程间字符串常量分析的Java注入漏洞检测方法[J]. 信息网络安全, 2026, 26(2): 304-314. |
| [2] | 张光华, 李国瑜, 王鹤, 李珩, 武少广. 基于污点流分析的物联网固件高可信度漏洞检测[J]. 信息网络安全, 2026, 26(2): 325-337. |
| [3] | 张学旺, 卢荟, 谢昊飞. 基于节点中心性和大模型的漏洞检测数据增强方法[J]. 信息网络安全, 2025, 25(4): 550-563. |
| [4] | 张雨轩, 黄诚, 柳蓉, 冷涛. 结合提示词微调的智能合约漏洞检测方法[J]. 信息网络安全, 2025, 25(4): 664-673. |
| [5] | 李鹏超, 张全涛, 胡源. 基于双注意力机制图神经网络的智能合约漏洞检测方法[J]. 信息网络安全, 2024, 24(11): 1624-1631. |
| [6] | 浦珺妍, 李亚辉, 周纯杰. 基于概率攻击图的工控系统跨域动态安全风险分析方法[J]. 信息网络安全, 2023, 23(9): 85-94. |
| [7] | 钟远鑫, 刘嘉勇, 贾鹏. 基于动态时间切片和高效变异的定向模糊测试[J]. 信息网络安全, 2023, 23(8): 99-108. |
| [8] | 王华忠, 田子蕾. 基于改进CGAN算法的工控系统入侵检测方法[J]. 信息网络安全, 2023, 23(1): 36-43. |
| [9] | 张光华, 刘永升, 王鹤, 于乃文. 基于BiLSTM和注意力机制的智能合约漏洞检测方案[J]. 信息网络安全, 2022, 22(9): 46-54. |
| [10] | 李佳玮, 吴克河, 张波. 基于高斯混合聚类的电力工控系统异常检测研究[J]. 信息网络安全, 2021, 21(3): 53-63. |
| [11] | 王华忠, 程奇. 基于改进鲸鱼算法的工控系统入侵检测研究[J]. 信息网络安全, 2021, 21(2): 53-60. |
| [12] | 文伟平, 李经纬, 焦英楠, 李海林. 一种基于随机探测算法和信息聚合的漏洞检测方法[J]. 信息网络安全, 2019, 19(1): 1-7. |
| [13] | 赵健, 王瑞, 李思其. 基于污点分析的智能家居漏洞挖掘技术研究[J]. 信息网络安全, 2018, 18(6): 36-44. |
| [14] | 文伟平, 郭荣华, 孟正, 柏皛. 信息安全风险评估关键技术研究与实现[J]. 信息网络安全, 2015, 15(2): 7-8. |
| [15] | . 典型文档类CVE漏洞检测工具的研究与实现[J]. , 2014, 14(6): 18-. |
| 阅读次数 | ||||||
|
全文 |
|
|||||
|
摘要 |
|
|||||