信息网络安全 ›› 2026, Vol. 26 ›› Issue (2): 325-337.doi: 10.3969/j.issn.1671-1122.2026.02.012
基于污点流分析的物联网固件高可信度漏洞检测
1.河北科技大学信息科学与工程学院 石家庄 050018 2.西安电子科技大学网络与信息安全学院 西安 710071 3.河北省网络安全感知与防御技术创新中心 石家庄 052161
-
收稿日期:2025-06-20出版日期:2026-02-10发布日期:2026-02-23 -
通讯作者:武少广 wushaoguang@hebust.edu.cn -
作者简介:张光华(1979—),男,河北,教授,博士,CCF高级会员,主要研究方向为网络与信息安全|李国瑜(2002—),男,山东,硕士研究生,主要研究方向为固件安全|王鹤(1987—),女,河南,讲师,博士,主要研究方向为应用密码和量子密码协议|李珩(1978—),男,河北,副教授,硕士,主要研究方向为软件工程|武少广(1987—),男,河北,讲师,硕士,CCF会员,主要研究方向为人工智能安全 -
基金资助:国家自然科学基金(62072239);国家自然科学基金(62372236);河北省硕士在读研究生创新能力培养资助项目(CXZZSS2025076)
High-Confidence Vulnerability Detection in IoT Firmware Based on Taint Flow Analysis
ZHANG Guanghua1, LI Guoyu1, WANG He2, LI Heng3, WU Shaoguang1( )
)
1. School of Information Science and Engineering ,Hebei University of Science and Technology Shijiazhuang 050018, China 2. School of Cyber Engineering ,Xidian University Xi’an 710071, China 3. Hebei Cybersecurity Perception and Defense Technology Innovation Center Shijiazhuang 052161, China
-
Received:2025-06-20Online:2026-02-10Published:2026-02-23
摘要:
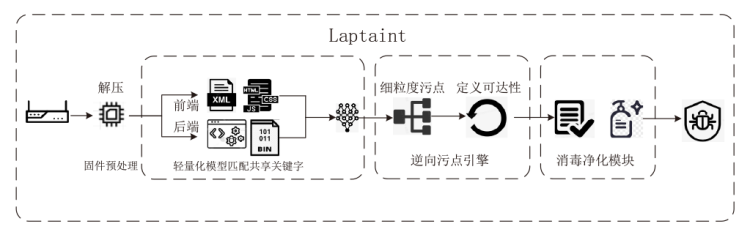
随着物联网设备的普及,其内嵌固件的安全漏洞面临的挑战日益严峻。当前,主流的污点分析方案存在路径爆炸和误报率高的问题。为了克服现有方案的不足,文章提出基于污点流分析的物联网固件高可信度漏洞检测方案Laptaint。首先,融合了轻量化模型和模糊匹配进行相应的关键字匹配,通过精确识别输入源来减少因源点丢失而造成的假阴性问题;然后,构建了细粒度污点语义模型,利用定义可达性分析从危险函数调用点开始,迭代地向后追踪,到达污点源;最后,集成的消毒验证模块通过4种检查逻辑,对污点输入进行有效性验证。对30个真实设备固件进行测试,实验结果表明,Laptaint方案以82.02%的准确率来挖掘漏洞,性能优于同类方案。
中图分类号:
引用本文
张光华, 李国瑜, 王鹤, 李珩, 武少广. 基于污点流分析的物联网固件高可信度漏洞检测[J]. 信息网络安全, 2026, 26(2): 325-337.
ZHANG Guanghua, LI Guoyu, WANG He, LI Heng, WU Shaoguang. High-Confidence Vulnerability Detection in IoT Firmware Based on Taint Flow Analysis[J]. Netinfo Security, 2026, 26(2): 325-337.
表2
Laptiant与SaTc、Mango警报数量对比
| 固件品牌及数量 | SaTc | Mango | Laptaint | |||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 警告 | 漏洞 | 警告 | 漏洞 | 警告 | 漏洞 | |||||||
| cmdi | bof | cmdi | bof | cmdi | bof | cmdi | bof | cmdi | bof | cmdi | bof | |
| TP-Link(8) | 0 | 2 | 0 | 1 | 11 | 55 | 5 | 35 | 7 | 40 | 5 | 32 |
| D-Link(8) | 0 | 27 | 0 | 11 | 7 | 32 | 3 | 19 | 5 | 24 | 3 | 18 |
| NetGear(7) | 12 | 144 | 8 | 45 | 73 | 694 | 36 | 348 | 47 | 394 | 35 | 327 |
| Tenda(7) | 6 | 117 | 5 | 71 | 78 | 56 | 50 | 25 | 52 | 32 | 48 | 25 |
| 总计 | 18 | 290 | 13 | 128 | 169 | 837 | 94 | 427 | 111 | 490 | 91 | 402 |
表3
Laptiant与SaTc、Mango准确率对比
| 固件品牌及数量 | SaTc | Mango | Laptaint | |||
|---|---|---|---|---|---|---|
| FP | TP | FP | TP | FP | TP | |
| TP-Link(8) | 50% | 50% | 39.40% | 60.60% | 21.28% | 78.72% |
| D-Link(8) | 59.26% | 40.74% | 43.59% | 56.41% | 27.59% | 72.41% |
| NetGear(7) | 66.03% | 33.97% | 59.46% | 50.06% | 17.47% | 82.53% |
| Tenda(7) | 38.22% | 61.78% | 44.03% | 55.97% | 13.10% | 86.90% |
| 平均 | 54.23% | 45.77% | 48.22% | 51.78% | 17.98% | 82.02% |
表4
Laptaint与SaTc、Mango分析速率对比
| 固件品牌及数量 | SaTc | Mango | Laptaint | |||
|---|---|---|---|---|---|---|
| 时间 | 时间 | 时间 | ||||
| cmdi | bof | cmdi | bof | cmdi | bof | |
| TP-Link(8) | 12h28min | 16h49min | 19h40min | 21h12min | 24h10min | 22h31min |
| D-Link(8) | 67h14min | 71h32min | 12h7min | 29h40min | 11h57min | 31h49min |
| NetGear(7) | 58h28min | 84h9min | 27h19min | 35h6min | 27h49min | 32h22min |
| Tenda(7) | 37h30min | 61h38min | 18h12min | 24h23min | 15h30min | 25h22min |
| 总计 | 175h40min | 234h8min | 77h18min | 110h21min | 79h26min | 112h4min |
表6
SaTc、Mango、Laptaint在路由器中的共享关键字提高比例
| 固件 | |||||
|---|---|---|---|---|---|
| DIR-842.fw.revA.1-02.eu.multi.0151008 | 231 | 342 | 423 | 83.12% | 23.68% |
| DIR-868L.w.evA.1-12.eu.multi.20170316 | 254 | 412 | 464 | 82.68% | 12.62% |
| DIR-880L.A1.FW107WWb08 | 179 | 263 | 321 | 79.33% | 22.05% |
| XR500-V2.1.0.4 | 456 | 542 | 545 | 19.52% | 0.55% |
| R6400v2-V1.0.4.84.10.0.58 | 573 | 453 | 625 | 9.08% | 37.97% |
| R7000-V1.0.11.100.10.2.100 | 542 | 582 | 591 | 9.04% | 1.55% |
| US.AC6V1.0BR.V15.03.05.16.multi.TD01 | 274 | 321 | 519 | 89.42% | 61.68% |
| US.AC9V1.0B.V15.03.05.14.multi.TD01 | 312 | 521 | 642 | 105.77% | 23.22% |
| US.AC15V1.0BR.V15.03.05.19.multi.TD01 | 317 | 475 | 719 | 126.81% | 51.37% |
| wa830nv2.en.3.14.8.up.boot | 211 | 264 | 428 | 102.84% | 62.12% |
| wr1043ndv3.en.3.16.9.up.boot | 97 | 153 | 188 | 93.81% | 22.88% |
| TD-W9970v1.0.9.1.2.5.up.boot.2015-08-31.17.13.22 | 102 | 243 | 256 | 150.98% | 5.34% |
| 平均 | 296 | 381 | 477 | 61.25% | 25.16% |
表7
Laptaint消融实验二
| 路由器品牌及数量 | 正向分析 | 逆向分析 | 提升效率 | ||
|---|---|---|---|---|---|
| 时间 | 时间 | ||||
| cmdi | bof | cmdi | bof | ||
| TP-Link(8) | 31h26min | 30h42min | 24h10min | 22h31min | 33.15% |
| D-Link(8) | 12h53min | 32h34min | 11h57min | 31h49min | 3.65% |
| NetGear(7) | 42h19min | 53h21min | 27h49min | 32h22min | 58.95% |
| Tenda(7) | 19h49min | 34h14min | 15h30min | 25h22min | 32.25% |
| 总计 | 106h27min | 150h51min | 79h26min | 112h4min | 34.36% |
| [1] | LIU Lingxiang, PAN Zulie, LI Yang, et al. A Static Localization Method for Firmware Vulnerabilities Based on Front-End and Back-End Correlation Analysis[J]. Netinfo Security, 2022, 22(8): 44-54. |
| 刘翎翔, 潘祖烈, 李阳, 等. 基于前后端关联性分析的固件漏洞静态定位方法[J]. 信息网络安全, 2022, 22(8):44-54. | |
| [2] | VAILSHERY L S. Topic: Internet of Things (IoT)[EB/OL]. (2024-06-11)[2025-05-13]. https://www.statista.com/topics/2637/internet-of-things/. |
| [3] |
ZHANG Guanghua, CHEN Fang, CHANG Jiyou, et al. Accelerating Firmware Vulnerability Discovery via Precise Intermediate Taint Source and Dangerous Function Localization[J]. Computer Science, 2025, 52(7): 1-12.
doi: 10.1063/1.31803 URL |
| 张光华, 陈放, 常继友, 等. 利用精确中间污点源和危险函数定位加速固件漏洞挖掘[J]. 计算机科学, 2025, 52(7):1-12. | |
| [4] | THREAT I T. 150000 Verkada Security Cameras Hacked—to Make a Point[EB/OL]. (2021-03-12)[2025-05-14]. https://www.threatdown.com/blog/150000-verkada-security-cameras-hacked-to-make-a-point/. |
| [5] | ANTONAKAKIS M, APRIL T, BAILEY M, et al. Understanding the Mirai Botnet[C]// USENIX. The 26th USENIX Conference on Security Symposium. Berkeley: USENIX, 2017: 1093-1110. |
| [6] | LANGNER R. Stuxnet: Dissecting a Cyberwarfare Weapon[J]. IEEE Security & Privacy, 2011, 9(3): 49-51. |
| [7] | WANG Ningchao, CHEN Zuoning, GAN Shuitao, et al. Research on the Technologies of Security Analysis Technologies on the Embedded Device Firmware[EB/OL]. (2023-02-22)[2025-05-14]. https://jglobal.jst.go.jp/en/detail?JGLOBAL_ID=202102221104018110. |
| [8] | CHEN Libo, WANG Yanhao, CAI Quanpu, et al. Sharing More and Checking Less: Leveraging Common Input Keywords to Detect Bugs in Embedded Systems[C]// USENIX. The 30th USENIX Security Symposium. Berkeley: USENIX, 2021: 303-319. |
| [9] | SRIVASTAVA P, PENG Hui, LI Jiahao, et al. FirmFuzz: Automated IoT Firmware Introspection and Analysis[C]// ACM. The 2nd International ACM Workshop on Security and Privacy for the Internet-of-Things. New York: ACM, 2019: 15-21. |
| [10] | GUO Jundong. Research on Automated Vulnerability Discovery Technology for Routers Based on Static Analysis[D]. Beijing: Beijing Jiaotong University, 2024. |
| 郭俊东. 基于静态分析的路由器自动化漏洞挖掘技术研究[D]. 北京: 北京交通大学, 2024. | |
| [11] | ZHANG Guanghua, CHANG Jiyou, CHEN Fang, et al. Firmware Simulation Scheme of IoT Devices Based on Dynamic Substitution of Library Functions[J]. Netinfo Security, 2025, 25(7): 1053-1062. |
| 张光华, 常继友, 陈放, 等. 基于库函数动态替换的物联网设备固件仿真方案[J]. 信息网络安全, 2025, 25(7):1053-1062. | |
| [12] | SHOSHITAISHVILI Y, WANG Ruoyu, SALLS C, et al. (State of ) The Art of War: Offensive Techniques in Binary Analysis[C]// IEEE. 2016 IEEE Symposium on Security and Privacy. New York: IEEE, 2016: 138-157. |
| [13] | ZADDACH J, BRUNO L, BALZAROTTI D, et al. Avatar: A Framework to Support Dynamic Security Analysis of Embedded Systems’ Firmwares[C]// NDSS. Network and Distributed System Security (NDSS) Symposium. San Diego: NDSS, 2014: 157-173. |
| [14] | CHEN Jiongyi, DIAO Wenrui, ZHAO Qingchuan, et al. IoTFuzzer: Discovering Memory Corruptions in IoT Through App-Based Fuzzing[C]// NDSS. Network and Distributed System Security Symposium 2018. San Diego: NDSS, 2018: 187-202. |
| [15] | WEI Zhou, ZHANG Lan, LE Guan, et al. What Your Firmware Tells You is not How You Should Emulate It: A Specification-Guided Approach for Firmware Emulation[C]// ACM. The 2022 ACM SIGSAC Conference on Computer and Communications Security. New York: ACM, 2022: 3269-3283. |
| [16] | ZHENG Yaowen, DAVANIAN A, ZHU Hongsong, et al. FIRM-AFL: High-Throughput Greybox Fuzzing of IoT Firmware via Augmented Process Emulation[C]// USENIX. The 28th USENIX Conference on Security Symposium (SEC’19). Berkeley: USENIX, 2019: 1099-1114. |
| [17] | SHE Dongdong, CHEN Yizheng, ABHISHEK S, et al. Neutaint: Efficient Dynamic Taint Analysis with Neural Networks[C]// IEEE. The 41th IEEE Symposium on Security and Privacy. New York: IEEE, 2020: 1527-1543. |
| [18] | QIAN Sang, WANG Yanhao, LIU Yuwei, et al. AirTaint: Making Dynamic Taint Analysis Faster and Easier[C]// IEEE. 2024 IEEE Symposium on Security and Privacy (SP). New York: IEEE, 2024: 3998-4014. |
| [19] | ZHU Yuming, DONG Weiyu. nnTaint: An Optimized Dynamic Taint Analysis Method Based on Neural Network[C]// IEEE. 2022 IEEE 10th International Conference on Information, Communication and Networks (ICICN). New York: IEEE, 2022: 63-70. |
| [20] | KIM M, KIM D, KIM E, et al. FirmAE: Towards Large-Scale Emulation of IoT Firmware for Dynamic Analysis[C]// ACM. The 36th Annual Computer Security Applications Conference. New York: ACM, 2020: 733-745. |
| [21] | GAO Zicong, ZHANG Chao, LIU Hangtian, et al. Faster and Better: Detecting Vulnerabilities in Linux-Based IoT Firmware with Optimized Reaching Definition Analysis[C]// NDSS. Network and Distributed System Security Symposium 2024. San Diego: NDSS, 2024: 564-571. |
| [22] | REDINI N, MACHIRY A, WANG Ruoyu, et al. Karonte: Detecting Insecure Multi-Binary Interactions in Embedded Firmware[C]// IEEE. 2020 IEEE Symposium on Security and Privacy (SP). New York: IEEE, 2020: 1544-1561. |
| [23] | GIBBS W, RAJ A S, VADAYATH J M, et al. Operation Mango: Scalable Discovery of Taint-Style Vulnerabilities in Binary Firmware Services[C]// USENIX. The 33rd USENIX Conference on Security Symposium. Berkeley: USENIX, 2024: 7123-7139. |
| [24] | CHENG Kai, ZHENG Yangwen, LIU Tao, et al. Detecting Vulnerabilities in Linux-Based Embedded Firmware with SSE-Based on-Demand Alias Analysis[C]// ACM. The 32nd ACM SIGSOFT International Symposium on Software Testing and Analysis. New York: ACM, 2023: 360-372. |
| [25] | LIU Puzhuo, ZHENG Yaowen, SUN Chengnian, et al. FITS: Inferring Intermediate Taint Sources for Effective Vulnerability Analysis of IoT Device Firmware[C]// ACM. The 28th ACM International Conference on Architectural Support for Programming Languages and Operating Systems. New York: ACM, 2024: 138-152. |
| [26] | CHENG Kai, LI Qiang, WANG Lei, et al. DTaint: Detecting the Taint-Style Vulnerability in Embedded Device Firmware[C]// IEEE. 2018 48th Annual IEEE/IFIP International Conference on Dependable Systems and Networks (DSN). New York: IEEE, 2018: 430-441. |
| [27] | EACMEN P. ReFirmLabs/Binwalk: Firmware Analysis Tool[EB/OL]. [2025-05-17]. https://github.com/ReFirmLabs/binwalk. |
| [1] | 陶慈, 陈昊然, 陈平. 面向工控系统的C语言异常处理路径定向模糊测试方法[J]. 信息网络安全, 2026, 26(2): 211-223. |
| [2] | 许朴, 孙心怡, 朱永根. 基于过程间字符串常量分析的Java注入漏洞检测方法[J]. 信息网络安全, 2026, 26(2): 304-314. |
| [3] | 王磊, 陈炯峄, 王剑, 冯袁. 基于污点分析与文本语义的固件程序交互关系智能逆向分析方法[J]. 信息网络安全, 2025, 25(9): 1385-1396. |
| [4] | 张学旺, 卢荟, 谢昊飞. 基于节点中心性和大模型的漏洞检测数据增强方法[J]. 信息网络安全, 2025, 25(4): 550-563. |
| [5] | 常振轩, 郑之涵, 梅傲寒, 谭毓安. 一种面向固件网络应用的高效灰盒模糊测试方法[J]. 信息网络安全, 2025, 25(4): 654-663. |
| [6] | 张雨轩, 黄诚, 柳蓉, 冷涛. 结合提示词微调的智能合约漏洞检测方法[J]. 信息网络安全, 2025, 25(4): 664-673. |
| [7] | 孟辉, 毛琳琳, 彭聚智. 大语言模型驱动的无害化处理识别方法[J]. 信息网络安全, 2025, 25(12): 1990-1998. |
| [8] | 王鹃, 张勃显, 张志杰, 谢海宁, 付金涛, 王洋. 基于模糊测试的Java反序列化漏洞挖掘[J]. 信息网络安全, 2025, 25(1): 1-12. |
| [9] | 李鹏超, 张全涛, 胡源. 基于双注意力机制图神经网络的智能合约漏洞检测方法[J]. 信息网络安全, 2024, 24(11): 1624-1631. |
| [10] | 张光华, 刘永升, 王鹤, 于乃文. 基于BiLSTM和注意力机制的智能合约漏洞检测方案[J]. 信息网络安全, 2022, 22(9): 46-54. |
| [11] | 文伟平, 李经纬, 焦英楠, 李海林. 一种基于随机探测算法和信息聚合的漏洞检测方法[J]. 信息网络安全, 2019, 19(1): 1-7. |
| [12] | 赵健, 王瑞, 李思其. 基于污点分析的智能家居漏洞挖掘技术研究[J]. 信息网络安全, 2018, 18(6): 36-44. |
| [13] | 达小文, 毛俐旻, 吴明杰, 郭敏. 一种基于补丁比对和静态污点分析的漏洞定位技术研究[J]. 信息网络安全, 2017, 17(9): 5-5. |
| [14] | 王夏菁, 胡昌振, 马锐, 高欣竺. 二进制程序漏洞挖掘关键技术研究综述[J]. 信息网络安全, 2017, 17(8): 1-13. |
| [15] | 彭建山, 奚琪, 王清贤. 二进制程序整型溢出漏洞的自动验证方法[J]. 信息网络安全, 2017, 17(5): 14-21. |
| 阅读次数 | ||||||
|
全文 |
|
|||||
|
摘要 |
|
|||||