Netinfo Security ›› 2026, Vol. 26 ›› Issue (4): 579-590.doi: 10.3969/j.issn.1671-1122.2026.04.006
Previous Articles Next Articles
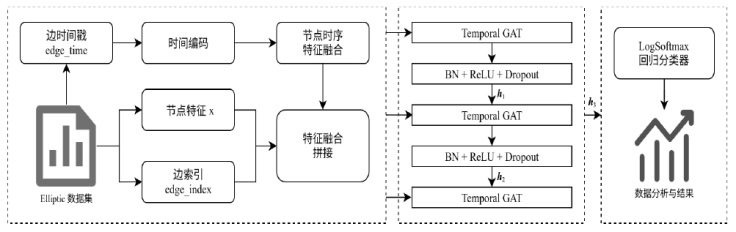
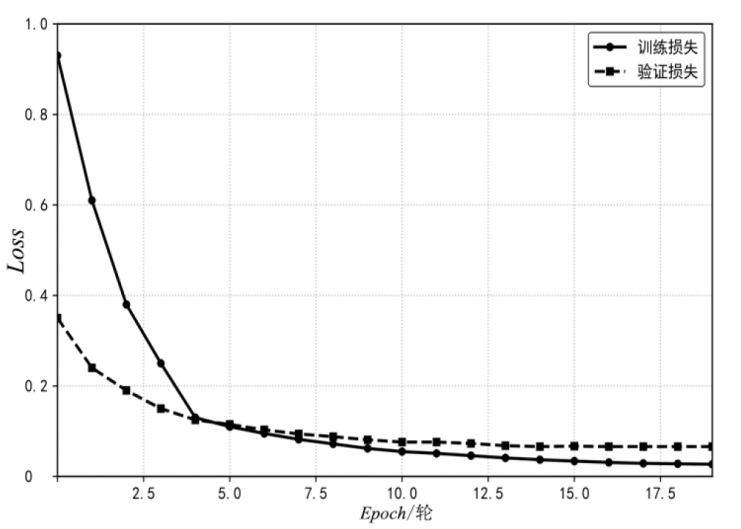
A Blockchain Anomaly Transaction Detection Method Based on Temporal Graph Attention Network
LI Jinkai1, WANG Jingwen1, DONG Libo2, YAO Wenhan3, LIU Chengjie1, WEN Weiping1( )
)
- 1
School of Software & Microelectronics ,Peking University Beijing 100871, China
2Haidian Branch of the Beijing Municipal Public Security Bureau Beijing 100089, China
3School of Computer Science ,Xiangtan University Xiangtan 411100, China
-
Received:2025-12-28Online:2026-04-10Published:2026-04-29
CLC Number:
Cite this article
LI Jinkai, WANG Jingwen, DONG Libo, YAO Wenhan, LIU Chengjie, WEN Weiping. A Blockchain Anomaly Transaction Detection Method Based on Temporal Graph Attention Network[J]. Netinfo Security, 2026, 26(4): 579-590.
share this article
Add to citation manager EndNote|Ris|BibTeX
URL: http://netinfo-security.org/EN/10.3969/j.issn.1671-1122.2026.04.006
| [1] | HOU Jian, LU Hui, LIU Fangai, et al. A Survey on Encrypted Malicious Traffic Detection and Adversarial Attacks[J]. Journal of Software, 2024, 35(1): 333-355. |
| 侯剑, 鲁辉, 刘方爱, 等. 加密恶意流量检测及对抗综述[J]. 软件学报, 2024, 35(1): 333-355. | |
| [2] | HASSAN M U, REHMANI M H, CHEN Jinjun. Anomaly Detection in Blockchain Networks: A Comprehensive Survey[J]. IEEE Communications Surveys & Tutorials, 2023, 25(1): 289-318. |
| [3] | WANG Lipeng, GUAN Zhi, LI Qingshan, et al. Survey on Blockchain Data Security Services[J]. Journal of Software, 2023, 34(1): 1-32. |
| 王利朋, 关志, 李青山, 等. 区块链数据安全服务综述[J]. 软件学报. 2023, 34(1): 1-32. | |
| [4] | Chainalysis. 2025 Crypto Crime Trends: Illicit Volumes Portend Record Year as On-Chain Crime Becomes Increasingly Diverse and Professionalized[EB/OL].(2025-01-15)[2025-12-20]. https://www.chainalysis.com/blog/2025-crypto-crime-report-introduction/. |
| [5] | FATF. Money Laundering and Terrorist Financing Red Flag Indicators Associated with Virtual Assets[EB/OL].(2020-09-14)[2025-12-20]. https://www.fatf-gafi.org/content/dam/fatf-gafi/reports/Virtual-Assets-Red-Flag-Indicators.pdf. |
| [6] | HUANG Shiyong, HAO Xiaohan, SUN Yani, et al. TMAS: A Transaction Misbehavior Analysis Scheme for Blockchain[EB/OL]. [2025-12-20]. https://doi.org/10.1016/j.bcra.2024.100197. |
| [7] | ZHANG Xiaoqi, BAI Xue, LI Guangsong, et al. Blockchain Abnormal Transaction Detection Based on Network Representation Learning[J]. Network Security and Data Governance, 2022, 41(10): 11-20. |
| 张晓琦, 白雪, 李光松, 等. 基于网络表示学习的区块链异常交易检测[J]. 网络安全与数据治理, 2022, 41(10): 11-20. | |
| [8] | ZHAO Peng, WANG Wenjian, GUO Husheng, et al. Blockchain Abnormal Transaction Detection Based on XGBoost and Random Forest[J]. Journal of Nanjing University of Posts and Telecommunications (Natural Science Edition), 2025, 45(1): 115-122. |
| 赵鹏, 王文剑, 郭虎升, 等. 基于XGBoost和随机森林的区块链异常交易检测[J]. 南京邮电大学学报(自然科学版), 2025, 45(1): 115-122. | |
| [9] | SHAYEGAN M J, SABOR H R, UDDIN M, et al. A Collective Anomaly Detection Technique to Detect Crypto Wallet Frauds on Bitcoin Network[EB/OL].(2022-02-05)[2025-12-20]. https://www.semanticscholar.org/reader/b5999b5f76d8999c2316c0fec40bcec9d11e8e54. |
| [10] | SONG Yuhan, ZHU Yuefei, WEI Fushan. A Blockchain Abnormal Transaction Detection Scheme Based on AdaBoost Model[J]. Netinfo Security, 2024, 24(1): 24-35. |
| 宋玉涵, 祝跃飞, 魏福山. 一种基于AdaBoost模型的区块链异常交易检测方案[J]. 信息网络安全, 2024, 24(1): 24-35. | |
| [11] | WEBER M, DOMENICONI G, CHEN Jie, et al. Anti-Money Laundering in Bitcoin: Experimenting with Graph Convolutional Networks for Financial Forensics[EB/OL].(2019-07-31)[2025-12-20]. https://doi.org/10.48550/arXiv.1908.02591. |
| [12] | SHEN Meng, SANG Anqi, ZHU Liehuang, et al. Identification Method of Abnormal Blockchain Digital Currency Transaction Behavior Based on Motivation Analysis[J]. Chinese Journal of Computers, 2021, 44(1): 193-208. |
| 沈蒙, 桑安琪, 祝烈煌, 等. 基于动机分析的区块链数字货币异常交易行为识别方法[J]. 计算机学报. 2021, 44(1): 193-208. | |
| [13] | YU Jiahao, WU Xian, LIU Hao, et al. BlockFound: Customized Blockchain Foundation Model for Anomaly Detection[EB/OL].(2024-09-27)[2025-12-10]. https://openreview.net/forum?id=LPXfOxe0zF. |
| [14] | LIN Wei. Blockchain Abnormal Transaction Detection Based on Multi-Feature Fusion[J]. Netinfo Security, 2022, 22(10): 24-30. |
| 林伟. 基于多特征融合的区块链异常交易检测[J]. 信息网络安全, 2022, 22(10): 24-30. | |
| [15] | WANG Yulong, ZHENG Qingxiao, LI Xuedong, et al. CoSemiGNN: Blockchain Fraud Detection with Dynamic Graph Neural Networks Based on Co-Association of Semi-Supervised[EB/OL]. [2025-12-20]. https://doi.org/10.1016/j.eswa.2025.129853. |
| [16] | LIU Jie, LI Qilin, AN Senjian, et al. EdgeConvFormer: Dynamic Graph CNN and Transformer Based Anomaly Detection in Multivariate Time Series[EB/OL].(2023-12-04)[2025-12-20]. https://arxiv.org/abs/2312.01729. |
| [17] | WANG Zhiqiang, NI Anfa, TIAN Ziqing, et al. Research on Blockchain Abnormal Transaction Detection Technology Combining CNN and Transformer Structure[EB/OL]. [2025-12-20]. https://doi.org/10.1016/j.compeleceng.2024.109194. |
| [18] | ZHU Huijuan, CHEN Jinfu, LI Zhiyuan, et al. Blockchain Abnormal Transaction Detection Method Based on Multi-Feature Adaptive Fusion[J]. Journal on Communications, 2021, 42(5): 41-50. |
| 朱会娟, 陈锦富, 李致远, 等. 基于多特征自适应融合的区块链异常交易检测方法[J]. 通信学报, 2021, 42(5): 41-50. | |
| [19] | GAO Haoyu, CAO Chunjie, BAI Yirui, et al. A Survey on Blockchain Security Supervision[J]. Journal on Communications, 2025, 46(4): 49-70. |
| 高昊昱, 曹春杰, 白伊瑞, 等. 区块链安全监管研究综述[J]. 通信学报. 2025, 46(4): 49-70. | |
| [20] | XU Da, RUAN Chuanwei, KORPEOGLU E, et al. Inductive Representation Learning on Temporal Graphs[EB/OL].(2019-12-20)[2025-12-10]. https://openreview.net/forum?id=rJeW1yHYwH. |
| [21] | SONG K, DHRAIEF M A, XU Muhua, et al. Identifying Money Laundering Subgraphs on the Blockchain[C]// ACM. The 5th ACM International Conference on AI in Finance (ICAIF 24). New York: ACM, 2024: 195-203. |
| [22] | TAN Pengliu, ZHOU Ye. Blockchain Abnormal Transaction Detection Based on GAT and SVM[J]. Application Research of Computers, 2024, 41(1): 21-25. |
| 谭朋柳, 周叶. 基于GAT与SVM的区块链异常交易检测[J]. 计算机应用研究, 2024, 41(1): 21-25. | |
| [23] | ASIRI A, SOMASUNDARAM K. Graph Convolution Network for Fraud Detection in Bitcoin Transactions[EB/OL].(2025-04-01)[2025-12-20]. https://doi.org/10.1038/s41598-025-95672-w. |
| [1] | HU Wentao, DING Weijie. DiffGuard: Network Traffic Anomaly Detection Based on Diffusion Models and Adaptive Sequence Learning [J]. Netinfo Security, 2026, 26(3): 378-388. |
| [2] | LUO Wenhua, XU Shilong, LYU Tao, ZHANG Ning. Blockchain Data Provenance Mechanism Integrating Cuckoo Filters and Temporal B+ Tree [J]. Netinfo Security, 2026, 26(3): 442-451. |
| [3] | LIANG Guangjun, QIU Yuchen, SI Hongtao, WANG Qun, MA Zhuo, CHEN Yuqi. Blockchain Virtual Currency Traceability and Analysis [J]. Netinfo Security, 2026, 26(3): 482-490. |
| [4] | GUO Yi, LI Xuqing, ZHANG Zijiao, ZHANG Hongtao, ZHANG Liancheng, ZHANG Xiangli. A Review of Data Security Sharing Based on Blockchain [J]. Netinfo Security, 2026, 26(1): 1-23. |
| [5] | LI Dong, GAO Yuan, YU Junqing, ZENG Muhong, CHEN Junxin. Polymorphic Network Control and Security Monitor Based on P4 [J]. Netinfo Security, 2026, 26(1): 115-124. |
| [6] | DONG Jiayu, GAO Hongmin, MA Zhaofeng, LAI Guanhui. Research and Implementation of Multi-Signature Mechanism in Blockchain [J]. Netinfo Security, 2026, 26(1): 125-138. |
| [7] | YANG Jianxin, WANG Xiaoding, LIN Hui. Improved Consensus Algorithm Based on HotStuff and Multi-Ary Trees [J]. Netinfo Security, 2025, 25(9): 1447-1455. |
| [8] | SHE Wei, MA Tianxiang, FENG Haige, LIU Wei. Tracing-Free Blockchain Covert Communication Method Based on RBF Mechanism [J]. Netinfo Security, 2025, 25(8): 1302-1312. |
| [9] | LIU Feng, HUANG Hao. A Decentralized Regulatory Architecture Based on Smart Contracts and Prophecy Machines with Active Sensor Networks [J]. Netinfo Security, 2025, 25(6): 898-909. |
| [10] | YE Jiajun, GAO Cuifeng, XUE Yinxing. Research on Price Oracle Manipulation Source Code Detection Method Based on Static Analysis [J]. Netinfo Security, 2025, 25(5): 732-746. |
| [11] | QIN Jinlei, KANG Yimin, LI Zheng. Lightweight Fine-Grained Multi-Dimensional Multi-Subset Privacy-Preserving Data Aggregation for Smart Grid [J]. Netinfo Security, 2025, 25(5): 747-757. |
| [12] | ZHU Xiaoqiang, ZHANG Haowen, LIN Yanzi, LIU Jiqiang. Lightweight Distributed Authentication Scheme Based on Trusted Digital Identity [J]. Netinfo Security, 2025, 25(5): 817-827. |
| [13] | YANG Yatao, DING Yucheng, LIU Peihe, SANG Peng. Research on Blockchain-Based Privacy Preservation and Digital Authentication [J]. Netinfo Security, 2025, 25(4): 640-653. |
| [14] | ZHANG Yuxuan, HUANG Cheng, LIU Rong, LENG Tao. Smart Contract Vulnerability Detection Method Combining Prompt Tuning [J]. Netinfo Security, 2025, 25(4): 664-673. |
| [15] | CHEN Hongsong, LIU Xinrui, TAO Zimei, WANG Zhiheng. A Survey of Anomaly Detection Model for Time Series Data Based on Deep Learning [J]. Netinfo Security, 2025, 25(3): 364-391. |
| Viewed | ||||||
|
Full text |
|
|||||
|
Abstract |
|
|||||