Netinfo Security ›› 2026, Vol. 26 ›› Issue (3): 442-451.doi: 10.3969/j.issn.1671-1122.2026.03.010
Previous Articles Next Articles
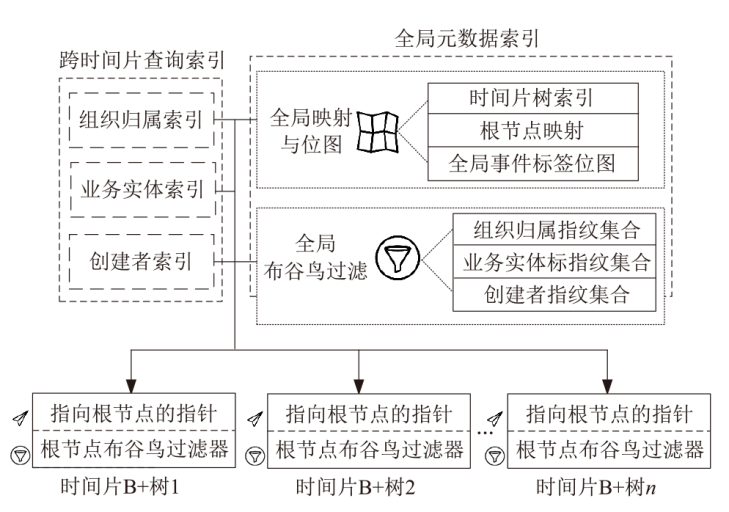
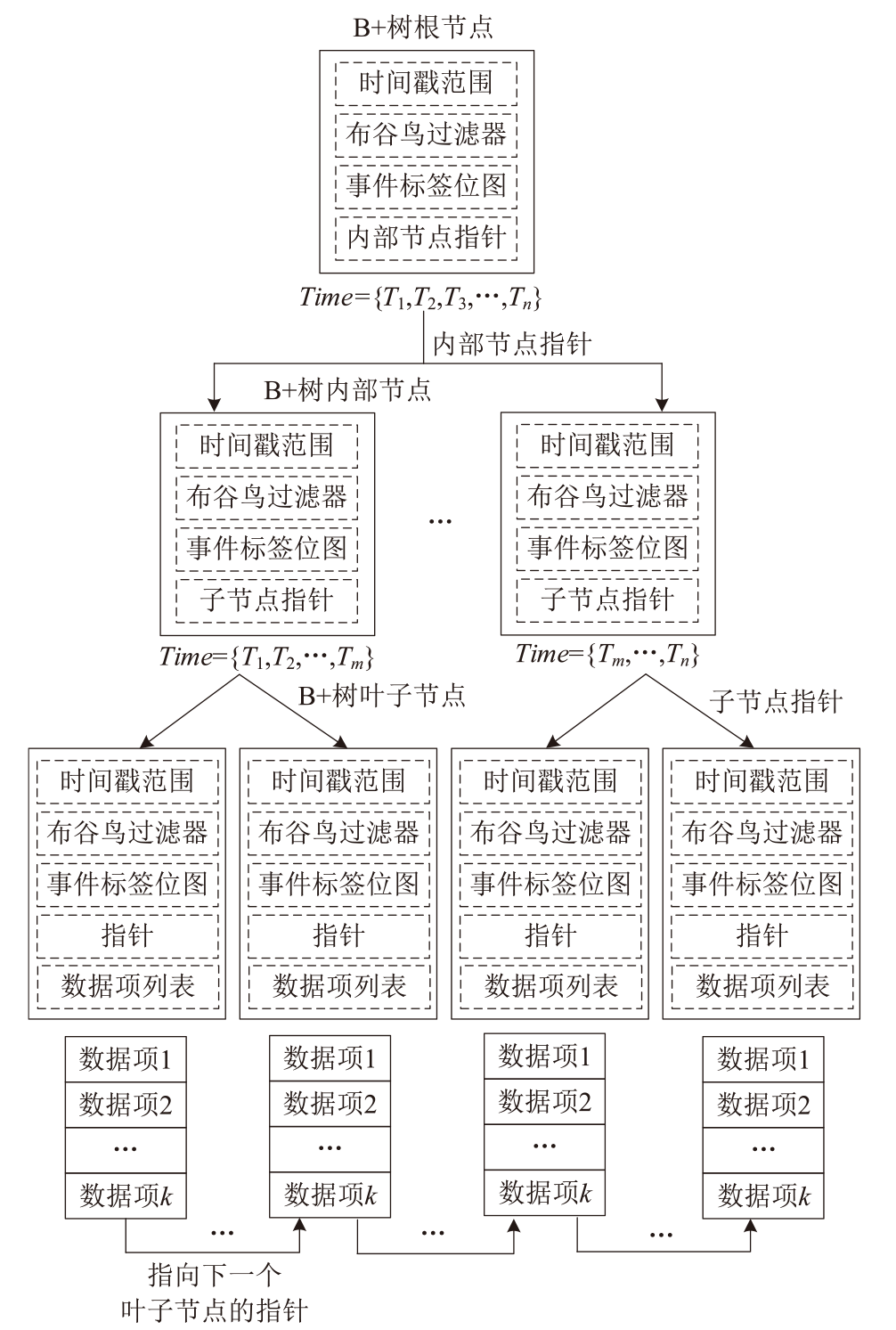
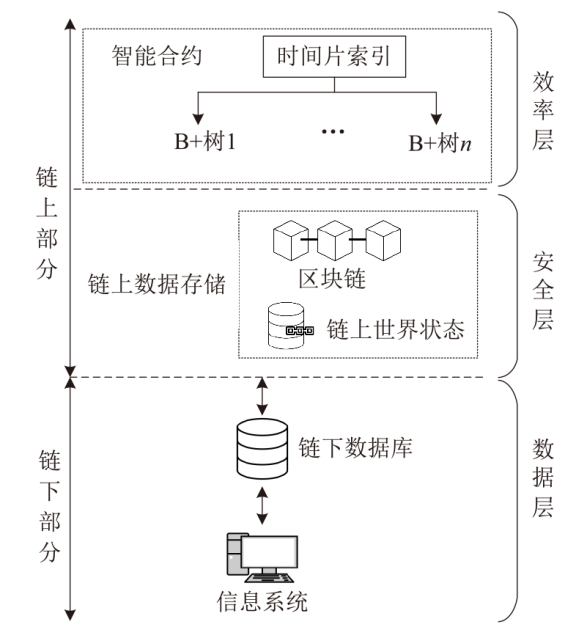
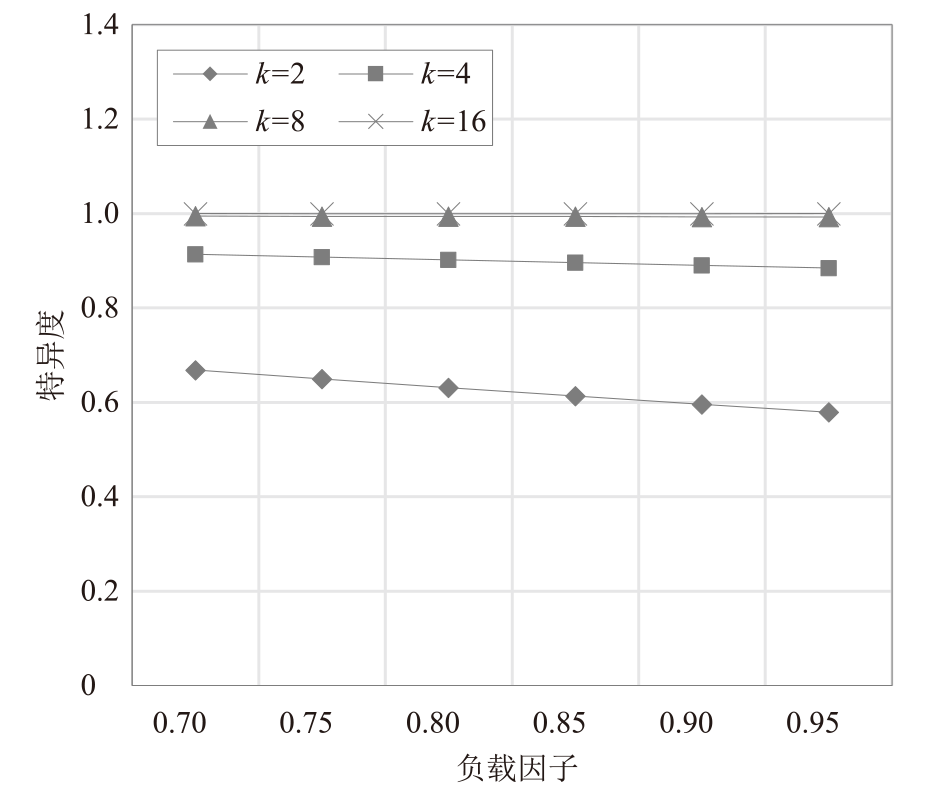
Blockchain Data Provenance Mechanism Integrating Cuckoo Filters and Temporal B+ Tree
LUO Wenhua1( ), XU Shilong1, LYU Tao1, ZHANG Ning2
), XU Shilong1, LYU Tao1, ZHANG Ning2
- 1. School of Public Security Information Technology and Intelligence, Criminal Investigation Police University of China, Shenyang 110035, China
2. Commission for Discipline Inspection of the Communist Party of China of Jiaxing Nanhu District, Jiaxing 314051, China
-
Received:2025-08-18Online:2026-03-10Published:2026-03-30
CLC Number:
Cite this article
LUO Wenhua, XU Shilong, LYU Tao, ZHANG Ning. Blockchain Data Provenance Mechanism Integrating Cuckoo Filters and Temporal B+ Tree[J]. Netinfo Security, 2026, 26(3): 442-451.
share this article
Add to citation manager EndNote|Ris|BibTeX
URL: http://netinfo-security.org/EN/10.3969/j.issn.1671-1122.2026.03.010
| [1] | CHEN Mo, GAO Gugang, JIANG Yifan, et al. Blockchain-Based Evidence Storage System for Police Body-Worn Cameras[J]. Internet of Things Technology, 2025, 15(5): 96-99. |
| 陈默, 高谷刚, 蒋逸凡, 等. 执法记录仪区块链存证系统[J]. 物联网技术, 2025, 15(5): 96-99. | |
| [2] | FAN Wei, LI Haibo, ZHANG Zhujun. Blockchain Digital Forensics: Technology and Architecture[J]. Journal of Communications, 2024, 45(12): 124-141. |
|
范伟, 李海波, 张珠君. 区块链数字取证:技术及架构研究[J]. 通信学报, 2024, 45(12): 124-141.
doi: 10.11959/j.issn.1000-436x.2024204 |
|
| [3] | ZHANG Peng, LUO Wenhua. Blockchain-Based Log Data Provenance Mechanism Using Bloom Filter Search Tree[J]. Netinfo Security, 2024, 24(11): 1739-1748. |
| 张鹏, 罗文华. 基于布隆过滤器查找树的日志数据区块链溯源机制[J]. 信息网络安全, 2024, 24(11): 1739-1748. | |
| [4] | WOOD G. A Secure Decentralised Generalised Transaction Ledger[J]. Ethereum Project Yellow Paper, 2014(151): 1-32. |
| [5] |
WANG Hancheng, DAI Haipeng, CHEN Shusen, et al. Filter Data Structures: A Survey[J]. Computer Science, 2024, 51(1): 35-40.
doi: 10.11896/jsjkx.231000193 |
|
王瀚橙, 戴海鹏, 陈树森, 等. 过滤器数据结构研究综述[J]. 计算机科学, 2024, 51(1): 35-40.
doi: 10.11896/jsjkx.231000193 |
|
| [6] | NAKAZONO S, BESSHO Y, KAWASHIMA H, et al. Griffin: Fast Transactional Database Index with Hash and B+-Tree[C]// IEEE. 2024 IEEE 20th International Conference on E-Science. New York: IEEE, 2024: 1-10. |
| [7] | SUN Jin, SONG Nana, WANG Lu, et al. A Blockchain-Based Multi-Keyword Rank Search Scheme for B+ Tree Inverted Index[EB/OL]. (2025-04-01)[2025-07-30]. https://dl.acm.org/doi/abs/10.1016/j.csi.2024.103968. |
| [8] | XU Songsong, GUO Xiaobing, XU Ke. Vifiable Bloom Filter (VBF): Accelerate the Query and Proof of Nonexistent Data in Ablockchain[J]. Sci Sin Inform, 2023, 53: 2386-2405. |
| 徐松松, 过晓冰, 徐恪. 可验证布隆过滤器:加速区块链中的不存在查询与证明[J]. 中国科学:信息科学, 2023, 53: 2386-2405. | |
| [9] | SUN Wenpeng, WANG Shuo, LI Jing. Lightweight and Efficient Verifiable Query Scheme for Blockchain[J]. Journal of Chinese Computer Systems, 2024, 45(8): 1944-1952. |
| 孙文鹏, 王硕, 李京. 一种面向区块链系统的轻量级高效可验证查询方法[J]. 小型微型计算机系统, 2024, 45(8): 1944-1952. | |
| [10] | SUN Li, DAI Huan, LIU Wenhao, et al. An Efficient Query Method for Blockchain Transaction Retrieval[J]. Computer Simulation, 2024, 41(11): 408-415. |
| 孙立, 戴欢, 刘文豪, 等. 一种面向区块链交易检索的高效查询方法[J]. 计算机仿真, 2024, 41(11): 408-415. | |
| [11] | HUANG Sui, LI Jian, FAN Bingbing. IABC: A Cross-Domain Authentication Method Based on Blockchain and Cuckoo Filter[J]. Journal of Chinese Computer Systems, 2020, 41(12): 2620-2625. |
| 黄穗, 李健, 范冰冰. IABC: 一种基于区块链和布谷鸟过滤器的跨域认证方法[J]. 小型微型计算机系统, 2020, 41(12): 2620-2625. | |
| [12] | WANG Hancheng, CHEN Zhipeng, DAI Haipeng, et al. Lock-Free Concurrent Cuckoo Filter[J]. Journal of Software, 2024, 36(7): 3339-3357. |
| 王瀚橙, 陈志鹏, 戴海鹏, 等. 无锁并发布谷鸟过滤器[J]. 软件学报, 2024, 36(7): 3339-3357. | |
| [13] | NIU Shufen, WANG Jinfeng, WANG Bobin, et al. Ciphertext Sorting Search Scheme Based on B+ Tree Index Structure on Blockchain[J]. Journal of Electronics & Information Technology, 2019, 41(10): 2409-2415. |
| 牛淑芬, 王金风, 王伯彬, 等. 区块链上基于B+树索引结构的密文排序搜索方案[J]. 电子与信息学报, 2019, 41(10): 2409-2415. | |
| [14] | CHEN Yuan, LI Ao, LI Wenhai, et al. FB+-Tree: A Memory-Optimized B+-Tree with Latch-Free Update[EB/OL]. (2025-03-30)[2025-07-30]. https://arxiv.org/abs/2503.23397. |
| [15] | ZHANG Min, LI Wei, FAN Qing. Hybrid Inverted Index Construction Method for Multidimensional Semantic Organization of Scientific and Technical Literature[J]. Journal of Modern Information, 2024, 44(2): 107-114, 129. |
|
张敏, 李唯, 范青. 面向科技文献多维语义组织的混合倒排索引构建方法[J]. 现代情报, 2024, 44(2): 107-114, 129.
doi: 10.3969/j.issn.1008-0821.2024.02.009 |
|
| [16] | ZHAI Peng, HE Jingsha, ZHANG Yu. An Identity Authentication Method Based on SM9 and Blockchain in the IoT Environment[J]. Netinfo Security, 2024, 24(2): 179-187. |
| 翟鹏, 何泾沙, 张昱. 物联网环境下基于SM9算法和区块链技术的身份认证方法[J]. 信息网络安全, 2024, 24(2): 179-187. | |
| [17] | NEWELL J, UR-REHMAN S, MAMUN Q, et al. EASL: Enhanced Append-Only Skip List Index for Agile Block Data Retrieval on Blockchain[EB/OL]. (2025-03-01)[2025-07-30]. https://www.sciencedirect.com/science/article/pii/S0167739X24005181. |
| [18] | FAN Bin, ANDERSEN D G, KAMINSKY M, et al. Cuckoo Filter: Practically Better than Bloom[C]// ACM. The 10th ACM International on Conference on Emerging Networking Experiments and Technologies. New York: ACM, 2014: 75-88. |
| [19] | GAO Guanyue, SUN Chuanheng, LUO Na, et al. Blockchain-Based Multi-Condition Query Optimization Method for Traceability Data of Agricultural Product Supply Chain[J]. Transactions of the Chinese Society for Agricultural Machinery, 2024, 55(3): 362-374. |
| 高官岳, 孙传恒, 罗娜, 等. 基于区块链的农产品供应链溯源数据多条件查询优化方法研究[J]. 农业机械学报, 2024, 55(3): 362-374. | |
| [20] | WU Haotian, TANG Yuzhe, SHEN Zhaoyan, et al. TELEX: Two-Level Learned Index for Rich Queries on Enclave-Based Blockchain Systems[J]. IEEE Transactions on Knowledge and Data Engineering, 2025, 37(7): 4299-4313. |
| [1] | LIANG Guangjun, QIU Yuchen, SI Hongtao, WANG Qun, MA Zhuo, CHEN Yuqi. Blockchain Virtual Currency Traceability and Analysis [J]. Netinfo Security, 2026, 26(3): 482-490. |
| [2] | GUO Yi, LI Xuqing, ZHANG Zijiao, ZHANG Hongtao, ZHANG Liancheng, ZHANG Xiangli. A Review of Data Security Sharing Based on Blockchain [J]. Netinfo Security, 2026, 26(1): 1-23. |
| [3] | DONG Jiayu, GAO Hongmin, MA Zhaofeng, LAI Guanhui. Research and Implementation of Multi-Signature Mechanism in Blockchain [J]. Netinfo Security, 2026, 26(1): 125-138. |
| [4] | WU Yue, ZHANG Yawen, CHENG Xiangran. Research on Security Defense Strategy of Information System Based on Dynamic Security Management Model [J]. Netinfo Security, 2026, 26(1): 59-68. |
| [5] | YANG Jianxin, WANG Xiaoding, LIN Hui. Improved Consensus Algorithm Based on HotStuff and Multi-Ary Trees [J]. Netinfo Security, 2025, 25(9): 1447-1455. |
| [6] | SHE Wei, MA Tianxiang, FENG Haige, LIU Wei. Tracing-Free Blockchain Covert Communication Method Based on RBF Mechanism [J]. Netinfo Security, 2025, 25(8): 1302-1312. |
| [7] | LIU Feng, HUANG Hao. A Decentralized Regulatory Architecture Based on Smart Contracts and Prophecy Machines with Active Sensor Networks [J]. Netinfo Security, 2025, 25(6): 898-909. |
| [8] | YE Jiajun, GAO Cuifeng, XUE Yinxing. Research on Price Oracle Manipulation Source Code Detection Method Based on Static Analysis [J]. Netinfo Security, 2025, 25(5): 732-746. |
| [9] | QIN Jinlei, KANG Yimin, LI Zheng. Lightweight Fine-Grained Multi-Dimensional Multi-Subset Privacy-Preserving Data Aggregation for Smart Grid [J]. Netinfo Security, 2025, 25(5): 747-757. |
| [10] | ZHU Xiaoqiang, ZHANG Haowen, LIN Yanzi, LIU Jiqiang. Lightweight Distributed Authentication Scheme Based on Trusted Digital Identity [J]. Netinfo Security, 2025, 25(5): 817-827. |
| [11] | YANG Yatao, DING Yucheng, LIU Peihe, SANG Peng. Research on Blockchain-Based Privacy Preservation and Digital Authentication [J]. Netinfo Security, 2025, 25(4): 640-653. |
| [12] | ZHANG Yuxuan, HUANG Cheng, LIU Rong, LENG Tao. Smart Contract Vulnerability Detection Method Combining Prompt Tuning [J]. Netinfo Security, 2025, 25(4): 664-673. |
| [13] | ZHANG Guanping, WEI Fushan, CHEN Xi, GU Chunxiang. Blockchain-Based Privacy-Preserving Cross-Domain Authentication Protocol [J]. Netinfo Security, 2025, 25(12): 1948-1960. |
| [14] | GUAN Zhi, HU Jianbin, LI Yue, CHEN Zhong. A Comprehensive Survey of Blockchain Technologies and Applications Based on Trusted Execution Environments [J]. Netinfo Security, 2025, 25(11): 1673-1690. |
| [15] | SHEN Haoting, PENG Zhigang, LIU Yuxuan, WANG Yafei. Hardware Authentication Mechanism for Consortium Blockchain Based on Differentiated Physical Unclonable Function Models [J]. Netinfo Security, 2025, 25(11): 1732-1744. |
| Viewed | ||||||
|
Full text |
|
|||||
|
Abstract |
|
|||||