| [1] |
BRIDGES L.The Changing Face of Malware[J]. Network Security, 2008, 2008(1): 17-20.
|
| [2] |
PATHAK P B, NANDED Y M.A Dangerous Trend of Cybercrime: Ransomware Growing Challenge[J]. International Journal of Advanced Research in Computer Engineering & Technology(IJARCET), 2016, 5(2): 371-373.
|
| [3] |
BHARDWAJ A, AVASTHI V, SASTRY H, et al.Ransomware Digital Extortion: A Rising New Age Threat[J]. Indian Journal of Science and Technology, 2016, 9(14): 1-5.
|
| [4] |
AL-RIMY B A S, MAAROF M A, SHAID S Z M. Ransomware Threat Success Factors, Taxonomy, and Countermeasures: A Survey and Research Directions[J]. Computers & Security, 2018, 74(5): 144-166.
|
| [5] |
SYMANTEC. 2017 Internet Security Threat Report[EB/OL]. , 2019-10-15.
|
| [6] |
SYMANTEC.2019 Internet Security Threat Report[EB/OL]. , 2019-10-15.
|
| [7] |
ZHANG Hanqi, XI Xiao, FRANCESCO M, et al.Classification of Ransomware Families with Machine Learning Based on N-gram of Opcodes[J]. Future Generation Computer Systems, 2019, 90(1): 211-221.
|
| [8] |
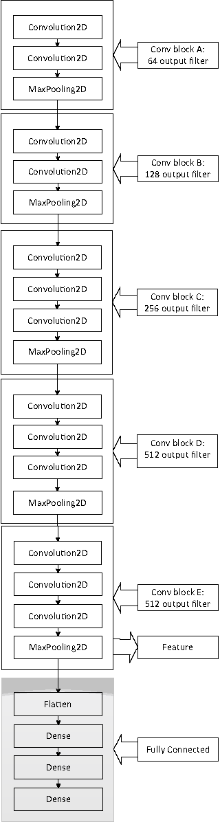
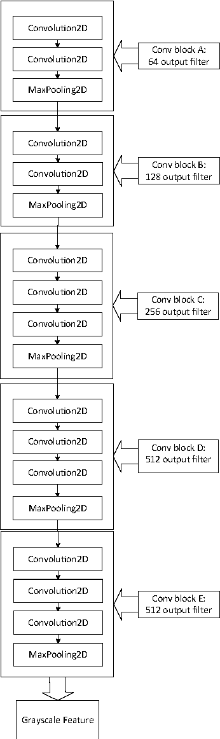
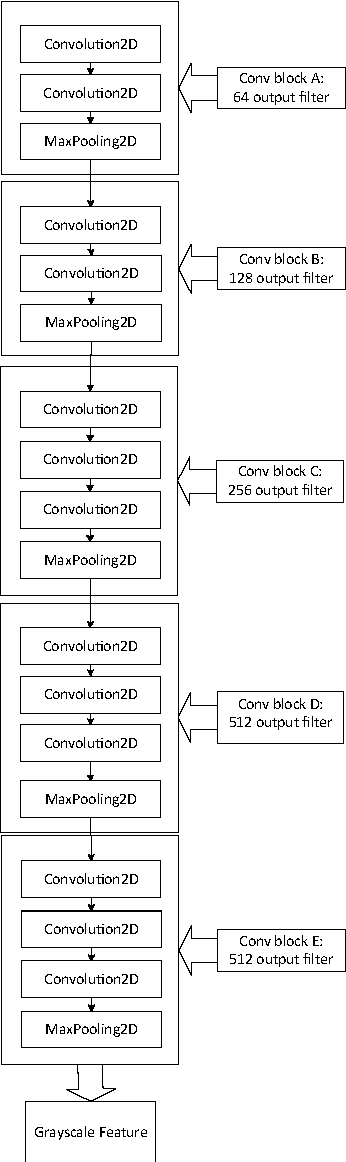
SIMONYAN K, ZISSERMAN A. Very Deep Convolutional Networks for Large-Scale Image Recognition[EB/OL]. , 2019-10-15.
|
| [9] |
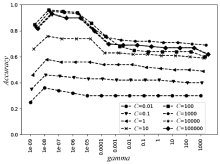
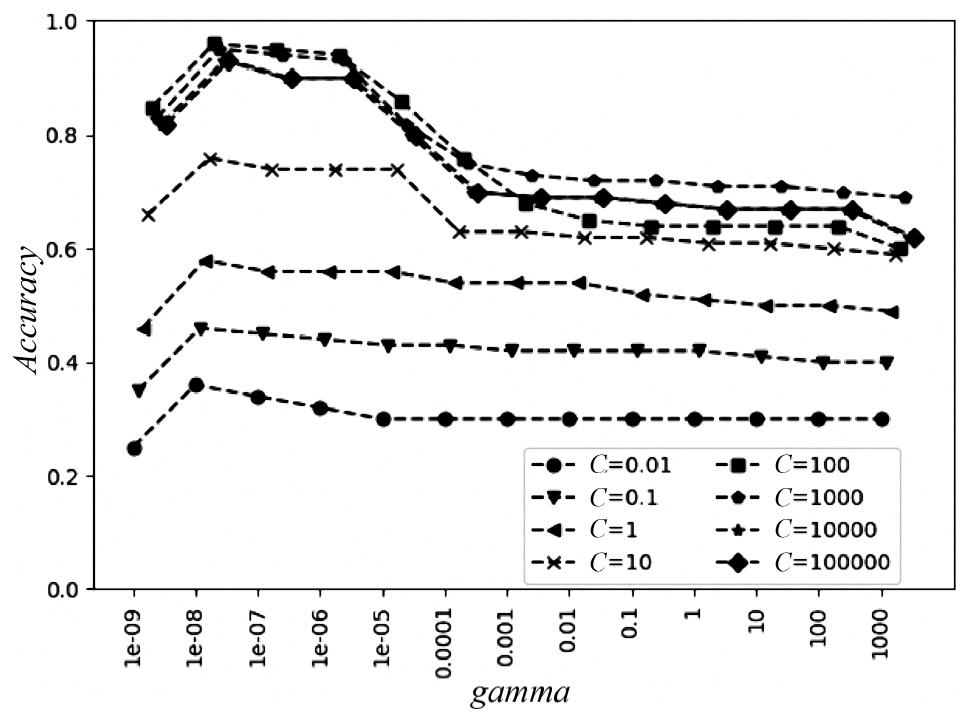
HSU C W, LIN C. J . A Comparison of Methods for Multiclass Support Vector Machines[J]. IEEE Transactions on Neural Networks, 2002, 13(2): 415-425.
|
| [10] |
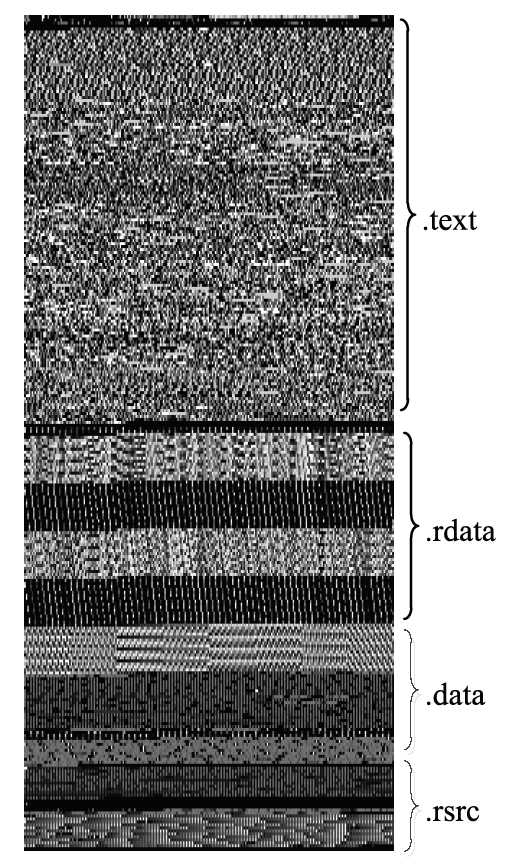
CONTI G, DEAN E, SINDA M, et al.Visual Reverse Engineering of Binary and Data Files[C]//DBLP.International Workshop on Visualization for Computer Security, September 15, 2008, Cambridge, MA, USA. Heidelberg: Springer, 2008: 1-17.
|
| [11] |
NATARAJ L, KARTHIKEYAN S, JACOB G, et al. Malware Images: Visualization and Automatic Classification[EB/OL]. , 2019-10-15.
|
| [12] |
KANCHERLA K, MUKKAMALA S. Image Visualization Based Malware Detection[EB/OL]. , 2019-10-15.
|
| [13] |
CHEN Zheng, FANG Yong, LIU Liang, et al.Detection Method of Ransomware Based on Dynamic Symbol Execution[J]. Computer Engineering, 2018, 44(6): 104-110.
|
|
陈政,方勇,刘亮,等.基于动态符号执行的勒索软件检测方法[J].计算机工程,2018,44(6):104-110.
|
| [14] |
ADE K.Detection and Analysis Cerber Ransomware Based on Network Forensics Behavior[J]. International Journal of Network Security, 2018, 20(5): 836-843.
|
| [15] |
KHARRAZ A, KIRDA E. Redemption: Real-Time Protection Against Ransomware at End-Hosts[EB/OL]. , 2019-10-15.
|
| [16] |
MORATO D.Ransomware Early Detection by the Analysis of File Sharing Traffic[J]. Journal of Network and Computer Applications, 2018, 124(15): 14-32.
|
| [17] |
KOLODENKER E, KOCH W, STRINGHINI G, et al. PayBreak: Defense Against Cryptographic Ransomware[EB/OL]. , 2019-10-15.
|
| [18] |
CONTINELLA A, GUAGNELLI A, ZINGARO G, et al.ShieldFS: A Self-Healing Ransomware-Aware Filesystem[C]//ICPS.Proceedings of the 32nd Annual Conference on Computer Security Applications, December 5, 2016, Los Angeles, California, USA. New York: ACM Press, 2016: 336-347.
|
| [19] |
DATA W P. Cryptostopper[EB/OL]. , 2019-10-15.
|
| [20] |
VINAYAKUMAR R, SOMAN K. P, VELAN K. Evaluating Shallow and Deep Networks for Ransomware Detection and Classification[EB/OL]. , 2019-10-15.
|
 ), SHEN Guowei1,2, JIANG Chaohui1,2
), SHEN Guowei1,2, JIANG Chaohui1,2