Netinfo Security ›› 2026, Vol. 26 ›› Issue (3): 452-461.doi: 10.3969/j.issn.1671-1122.2026.03.011
Previous Articles Next Articles
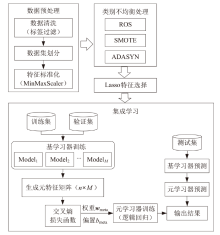
Anomaly Detection Method for Bitcoin Transactions Based on ADASYN, Lasso Regression, and Ensemble Learning
CHEN Chao1,2( ), WANG Nuoxuan1, ZHOU Shengli1
), WANG Nuoxuan1, ZHOU Shengli1
- 1. College of Information and Cyber Security, Zhejiang Police College, Hangzhou 310053, China
2. College of Computer Science and Technology, Zhejiang University, Hangzhou 310058, China
-
Received:2025-07-26Online:2026-03-10Published:2026-03-30
CLC Number:
Cite this article
CHEN Chao, WANG Nuoxuan, ZHOU Shengli. Anomaly Detection Method for Bitcoin Transactions Based on ADASYN, Lasso Regression, and Ensemble Learning[J]. Netinfo Security, 2026, 26(3): 452-461.
share this article
Add to citation manager EndNote|Ris|BibTeX
URL: http://netinfo-security.org/EN/10.3969/j.issn.1671-1122.2026.03.011
| 模型 | 超参数 | 数值 | 搜索范围 |
|---|---|---|---|
| LR | 最大迭代次数 | 1000次 | [500,2000] |
| 正则化参数 | 1.0 | [0.01,10] | |
| 随机种子 | 42 | 固定 | |
| XGB | 最大树深度 | 5 | [3,10] |
| 学习率 | 0.08 | [0.01,0.5] | |
| 树数量 | 400棵 | [50,500] | |
| L2正则化参数 | 0.8 | [0,10] | |
| 最小子节点权重 | 2 | [1,10] | |
| 随机种子 | 42 | 固定 | |
| MLP | 隐藏层结构 | [100,100] | {[50,50],[100,100],[200,200]} |
| 激活函数 | ReLU | 固定 | |
| 学习率η | 0.001 | [0.0001,0.01] | |
| 最大迭代次数 | 1000次 | [500,2000] | |
| 批量大小 | 200 | [100,500] | |
| 随机种子 | 42 | 固定 | |
| RF | 树数量 | 300棵 | [50,500] |
| 最大深度 | 15 | [10,30] | |
| 每次分裂特征数 | 40个 | ||
| 最小分裂样本数 | 3个 | [2,10] | |
| 随机种子 | 42 | 固定 |
| 集成学习模型 | 精确率 | 召回率 | F1值 |
|---|---|---|---|
| LR+XGB | 0.8740 | 0.6851 | 0.7681 |
| LR+MLP | 0.9869 | 0.4857 | 0.6510 |
| LR+RF | 0.7028 | 0.7295 | 0.7159 |
| XGB+MLP | 0.9060 | 0.7027 | 0.7915 |
| XGB+RF | 0.7677 | 0.7202 | 0.7432 |
| MLP+RF | 0.7222 | 0.7322 | 0.7272 |
| LR+XGB+RF | 0.9858 | 0.6408 | 0.7767 |
| XGB+MLP+RF | 0.7490 | 0.7193 | 0.7339 |
| LR+MLP+RF | 0.9903 | 0.6574 | 0.7902 |
| LR+XGB+MLP | 0.9952 | 0.5789 | 0.7320 |
| LR+XGB+MLP+RF | 0.9915 | 0.6482 | 0.7839 |
| [1] |
TRZCIONKA M. The Bitcoin-Democratic Money in a Neoliberal Economy[J]. Ad Americam, 2019, 19: 155-173.
doi: 10.12797/AdAmericam.19.2018.19.11 URL |
| [2] | GAJDEK S. Bitcoin as an Example of Cryptocurrency-Current State and Perspectives[J]. Annals of Marketing Management & Economics, 2018, 4(2): 47-56. |
| [3] |
SABRY F, LABDA W, ERBAD A, et al. Cryptocurrencies and Artificial Intelligence: Challenges and Opportunities[J]. IEEE Access, 2020, 8: 175840-175858.
doi: 10.1109/Access.6287639 URL |
| [4] | PHAM T, LEE S. Anomaly Detection in Bitcoin Network Using Unsupervised Learning Methods[EB/OL]. (2017-02-25)[2025-04-28]. http://arxiv.org/abs/1611.03941. |
| [5] | SONG K, ALI DHRAIEF M, XU Muhua, et al. Identifying Money Laundering Subgraphs on the Blockchain[C]// ACM. The 5th ACM International Conference on AI in Finance. New York: ACM, 2024: 195-203. |
| [6] | ADLOORI H, DASANAPU V, MERGU A C. Graph Network Models to Detect Illicit Transactions in Block Chain[EB/OL]. (2024-09-23)[2025-05-28]. http://arxiv.org/abs/2410.07150. |
| [7] | HUMRANAN P, SUPRATID S. A Study on GCN Using Focal Loss on Class-Imbalanced Bitcoin Transaction for Anti-Money Laundering Detection[C]// IEEE. 2023 International Electrical Engineering Congress(iEECON). New York: IEEE, 2023: 101-104. |
| [8] | OSTERRIEDER J, CHAN S, CHU J, et al. Enhancing Security in Blockchain Networks: Anomalies, Frauds, and Advanced Detection Techniques[EB/OL]. (2024-02-17)[2025-05-10]. http://arxiv.org/abs/2402.11231. |
| [9] |
PETTERSSON R E, ANGELIS J. Combating Money Laundering with Machine Learning-Applicability of Supervised-Learning Algorithms at Cryptocurrency Exchanges[J]. Journal of Money Laundering Control, 2022, 25(4): 766-778.
doi: 10.1108/JMLC-09-2021-0106 URL |
| [10] |
ZHU Huijuan, CHEN Jinfu, LI Zhiyuan, et al. Blockchain Anomaly Transaction Detection Method Based on Adaptive Multi-Feature Fusion[J]. Journal on Communications, 2021, 42(5): 41-50.
doi: 10.11959/j.issn.1000-436x.2021030 |
|
朱会娟, 陈锦富, 李致远, 等. 基于多特征自适应融合的区块链异常交易检测方法[J]. 通信学报, 2021, 42(5):41-50.
doi: 10.11959/j.issn.1000-436x.2021030 |
|
| [11] | MONAMO P, MARIVATE V, TWALA B. Unsupervised Learning for Robust Bitcoin Fraud Detection[C]// IEEE. 2016 Information Security for South Africa(ISSA). New York: IEEE, 2016: 129-134. |
| [12] | SAYADI S, BEN R S, CHOUKAIR Z. Anomaly Detection Model over Blockchain Electronic Transactions[C]// IEEE. 2019 15th International Wireless Communications & Mobile Computing Conference(IWCMC). New York: IEEE, 2019: 895-900. |
| [13] | HASAN M, RAHMAN M S, JANICKE H, et al. Detecting Anomalies in Blockchain Transactions Using Machine Learning Classifiers and Explainability Analysis[EB/OL]. (2024-01-07)[2025-04-28]. https://doi.org/10.1016/j.bcra.2024.100207. |
| [14] | FELDMAN E V, RUCHAY A N, MATVEEVA V K, et al. Bitcoin Abnormal Transaction Detection Based on Machine Learning[C]// Springer. Recent Trends in Analysis of Images, Social Networks and Texts. Heidelberg: Springer, 2021: 205-215. |
| [15] | ZHANG Xiaoqi, LI Guangsong, WANG Yongjuan. GAN-Based Abnormal Transaction Detection in Bitcoin[C]// IEEE. 2022 IEEE 7th International Conference on Smart Cloud(SmartCloud). New York: IEEE, 2022: 157-162. |
| [16] | JIANG Wenlong, YIN Pei, ZHU Wangwei. Cryptocurrency Transaction Fraud Detection Based on Imbalanced Classification with Interpretable Analysis[C]// Springer. New Challenges and Opportunities for Digital-Enabled Intelligent Future. Heidelberg: Springer, 2024: 386-398. |
| [17] | WANG Chundong, YANG Weijie. Semi-Supervised Blockchain Anomaly Transaction Detection Based on Deep AutoEncoder and Multi-Layer Perceptron[C]// IEEE. 2024 4th International Conference on Digital Society and Intelligent Systems(DSInS). New York: IEEE, 2024: 115-119. |
| [18] | ALOTIBI J, ALMUTANNI B, ALSUBAIT T, et al. Money Laundering Detection Using Machine Learning and Deep Learning[J]. International Journal of Advanced Computer Science and Applications, 2022, 13(10): 732-738. |
| [19] | AIRLANGGA G. Deep Learning for Anomaly Detection and Fraud Analysis in Blockchain Transactions of the Open Metaverse[J]. Jurnal Informatika Ekonomi Bisnis, 2024, 6(2): 324-329. |
| [20] |
UMER Q, LI Jianwei, ASHRAF M R, et al. Ensemble Deep Learning-Based Prediction of Fraudulent Cryptocurrency Transactions[J]. IEEE Access, 2023, 11: 95213-95224.
doi: 10.1109/ACCESS.2023.3310576 URL |
| [21] | YUE Yuyu, ZHANG Jixin, ZHANG Mingwu, et al. An Abnormal Account Identification Method by Topology Feature Analysis for Blockchain-Based Transaction Network[EB/OL]. (2024-04-09)[2025-04-28]. https://doi.org/10.3390/electronics13081416. |
| [22] |
LIAO Qian, GU Yijun. Anomaly Transaction Detection in Bitcoin Network Based on LSCP Algorithm[J]. Computer Engineering and Applications, 2022, 58(15): 117-123.
doi: 10.3778/j.issn.1002-8331.2105-0028 |
|
廖茜, 顾益军. 基于LSCP算法的比特币网络异常交易检测[J]. 计算机工程与应用, 2022, 58(15):117-123.
doi: 10.3778/j.issn.1002-8331.2105-0028 |
|
| [23] |
NERURKAR P. Illegal Activity Detection on Bitcoin Transaction Using Deep Learning[J]. Soft Computing, 2023, 27(9): 5503-5520.
doi: 10.1007/s00500-022-07779-1 |
| [24] | POCHER N, ZICHICHI M, MERIZZI F, et al. Detecting Anomalous Cryptocurrency Transactions: An AML/CFT Application of Machine Learning-Based Forensics[EB/OL]. (2023-03-18)[2025-04-28]. https://doi.org/10.48550/arXiv.2206.04803. |
| [25] | JIAO Feipeng, YUE Ruiqing. BN-GCN: Detecting Abnormal Bitcoin Transactions Using Graph Neural Networks[C]// IEEE. 2024 IEEE 6th International Conference on Power, Intelligent Computing and Systems(ICPICS). New York: IEEE, 2024: 1412-1416. |
| [26] | ZHENG Yang. GRU-GAT Model for Blockchain Bitcoin Abnormal Transaction Detection[C]// IEEE. 2022 IEEE Conference on Telecommunications, Optics and Computer Science(TOCS). New York: IEEE, 2022: 666-674. |
| [27] | ZHAO Kewei, DONG Guixin, BIAN Dong. Detection of Illegal Transactions of Cryptocurrency Based on Mutual Information[EB/OL]. (2023-02-27)[2025-04-28]. https://doi.org/10.3390/electronics12071542. |
| [28] | YAO Chenhao, FU Zhangjie, LIU Tianyi, et al. Attention-Driven Topology Adaptive Graph Convolutional Networks for Bitcoin Abnormal Transaction Detection[C]// IEEE. 2024 Twelfth International Conference on Advanced Cloud and Big Data(CBD). New York: IEEE, 2024: 25-30. |
| [29] | YU Lian, JING Qi, LI Ruomiao, et al. ParGCN: Abnormal Transaction Detection Based on Graph Neural Networks[C]// IEEE. 2022 IEEE 22nd International Conference on Software Quality, Reliability and Security(QRS). New York: IEEE, 2022: 797-808. |
| [30] | DING Zhihao, SHI Jieming, LI Qing, et al. Effective Illicit Account Detection on Large Cryptocurrency MultiGraphs[C]// ACM. The 33rd ACM International Conference on Information and Knowledge Management. New York: ACM, 2024: 457-466. |
| [31] | WEBER M, DOMENICONI G, CHEN Jie, et al. Anti-Money Laundering in Bitcoin: Experimenting with Graph Convolutional Networks for Financial Forensics[EB/OL]. (2019-07-31)[2025-05-20]. http://arxiv.org/abs/1908.02591. |
| [32] | ELMOUGY Y, LIU Ling. Demystifying Fraudulent Transactions and Illicit Nodes in the Bitcoin Network for Financial Forensics[C]// ACM. The 29th ACM SIGKDD Conference on Knowledge Discovery and Data Mining. New York: ACM, 2023: 3979-3990. |
| [1] | SHE Wei, MA Tianxiang, FENG Haige, LIU Wei. Tracing-Free Blockchain Covert Communication Method Based on RBF Mechanism [J]. Netinfo Security, 2025, 25(8): 1302-1312. |
| [2] | ZHAO Wei, REN Xiaoning, XUE Yinxing. Membership Inference Attacks Method Based on Ensemble Learning [J]. Netinfo Security, 2024, 24(8): 1252-1264. |
| [3] | XIANG Hui, XUE Yunhao, HAO Lingxin. Large Language Model-Generated Text Detection Based on Linguistic Feature Ensemble Learning [J]. Netinfo Security, 2024, 24(7): 1098-1109. |
| [4] | TU Xiaohan, ZHANG Chuanhao, LIU Mengran. Design and Implementation of Malicious Traffic Detection Model [J]. Netinfo Security, 2024, 24(4): 520-533. |
| [5] | JIANG Rong, LIU Haitian, LIU Cong. Unsupervised Network Intrusion Detection Method Based on Ensemble Learning [J]. Netinfo Security, 2024, 24(3): 411-426. |
| [6] | XING Lingkai, ZHANG Jian. Research and Implementation on Abnormal Behavior Detection Technology of Virtualization Platform Based on HPC [J]. Netinfo Security, 2023, 23(10): 64-69. |
| [7] | WANG Haoyang, LI Wei, PENG Siwei, QIN Yuanqing. An Intrusion Detection Method of Train Control System Based on Ensemble Learning [J]. Netinfo Security, 2022, 22(5): 46-53. |
| [8] | ZHENG Haixiao, WEN Bin. Bitcoin Illegal Transaction Identification Method Based on Graph Convolutional Network [J]. Netinfo Security, 2021, 21(9): 74-79. |
| [9] | Zewen MA, Yang LIU, Hongping XU, Hang YI. DoS Traffic Identification Technology Based on Integrated Learning [J]. Netinfo Security, 2019, 19(9): 115-119. |
| [10] | Chunguang MA, Jing AN, Wei BI, Qi YUAN. Smart Contract in Blockchain [J]. Netinfo Security, 2018, 18(11): 8-17. |
| [11] | Hao WANG, Xiangfu SONG, Junming KE, Qiuliang XU. Blockchain and Privacy Preserving Mechanisms in Cryptocurrency [J]. Netinfo Security, 2017, 17(7): 32-39. |
| [12] | TANG Jian, SUN Chun-lai, LI Dong. Discussion about the Industrial Control Network Intrusion Prevention Technology based on On-line Ensemble Learning [J]. 信息网络安全, 2014, 14(9): 86-91. |
| Viewed | ||||||
|
Full text |
|
|||||
|
Abstract |
|
|||||