| [1] |
China Internet Network Information Center. The 49th China Statistical Report on Internet Development[EB/OL]. (2022-02-25)[2025-08-03]. https://www.cnnic.net.cn/n4/2022/0401/c88-1131.html.
|
|
中国互联网络信息中心. 第49次中国互联网络发展状况统计报告[EB/OL]. (2022-02-25)[2025-08-03]. https://www.cnnic.net.cn/n4/2022/0401/c88-1131.html.
|
| [2] |
YIN Jie, JIANG Yuxiang, NIU Bowei, et al. Remote Detection of Web Page Tampering Based on Deep Learning[J]. Journal of Nanjing University of Science and Technology, 2020, 44(1): 49-54.
|
|
印杰, 蒋宇翔, 牛博威, 等. 基于深度学习的网页篡改远程检测研究[J]. 南京理工大学学报, 2020, 44(1): 49-54.
|
| [3] |
BARTOLI A, DAVANZO G, MEDVET E. A Framework for Large-Scale Detection of Web Site Defacements[J]. ACM Transactions on Internet Technology, 2010, 10(3): 1-37.
|
| [4] |
ZHOU Wenyi, GU Xubo, SHI Yong, et al. Detection Method for Hidden Hyperlink Based on Machine Learning[J]. Computer Engineering, 2018, 44(10): 22-27.
doi: 10.19678/j.issn.1000-3428. 0051189
|
|
周文怡, 顾徐波, 施勇, 等. 基于机器学习的网页暗链检测方法[J]. 计算机工程, 2018, 44(10): 22-27.
|
| [5] |
DAVANZO G, MEDVET E, BARTOLI A. Anomaly Detection Techniques for a Web Defacement Monitoring Service[J]. Expert Systems with Applications, 2011, 38(10): 12521-12530.
doi: 10.1016/j.eswa.2011.04.038
URL
|
| [6] |
MENG Chijie, WANG Wei, GENG Guanggang. Internet Hidden Hyperlinks Detection Based on Statistical Machine Learning[J]. Application Research of Computers, 2015, 32(9): 2779-2783.
|
|
孟池洁, 王伟, 耿光刚. 基于统计机器学习的互联网暗链检测方法[J]. 计算机应用研究, 2015, 32(9): 2779-2783.
|
| [7] |
LIM M, ABDULLAH A, JHANJHI N, et al. Hidden Link Prediction in Criminal Networks Using the Deep Reinforcement Learning Technique[EB/OL]. (2019-01-11)[2025-08-03]. https://doi.org/10.3390/computers8010008.
|
| [8] |
SARAVANOU A, KATAKIS I, VALKANAS G, et al. Revealing the Hidden Links in Content Networks: An Application to Event Discovery[C]// ACM. The 2017 ACM on Conference on Information and Knowledge Management. New York: ACM, 2017: 2283-2286.
|
| [9] |
LIM M, ABDULLAH A, JHANJHI N Z. Performance Optimization of Criminal Network Hidden Link Prediction Model with Deep Reinforcement Learning[J]. Journal of King Saud University-Computer and Information Sciences, 2021, 33(10): 1202-1210.
doi: 10.1016/j.jksuci.2019.07.010
URL
|
| [10] |
PANCHAL B Y, CHAUHAN G, PANCHAL S R, et al. An Investigation on Feature and Text Extraction from Images Using Image Recognition in Android[J]. Materials Today: Proceedings, 2022, 51: 798-802.
doi: 10.1016/j.matpr.2021.06.237
URL
|
| [11] |
HE Xiaomin, WANG Jin, HE Yueying, et al. A Deep Learning Approach for Website Fingerprinting Attack[C]// IEEE. 2018 IEEE 4th International Conference on Computer and Communications (ICCC). New York: IEEE, 2019: 1419-1423.
|
| [12] |
BHAT S, LU D, KWON A, et al. Var-CNN: A Data-Efficient Website Fingerprinting Attack Based on Deep Learning[J]. Proceedings on Privacy Enhancing Technologies, 2019(4): 292-310.
|
| [13] |
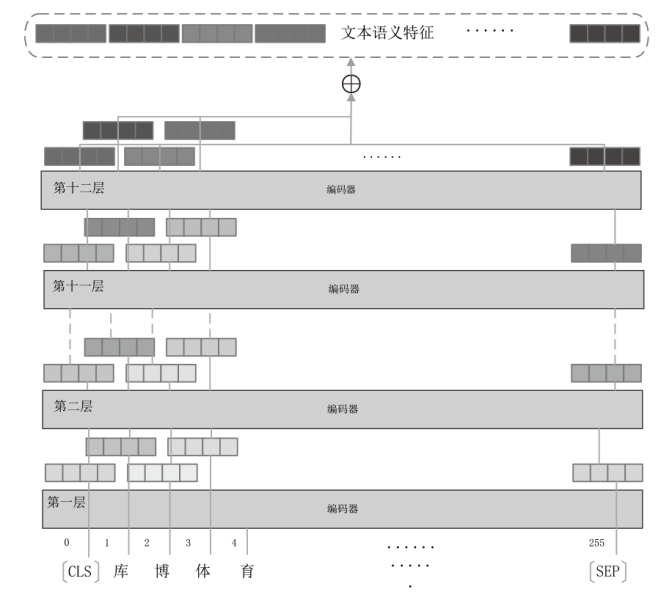
DEVLIN J, CHANG Mingwei, LEE K, et al. BERT: Pre-Training of Deep Bidirectional Transformers for Language Understanding[C]//ACL. The 2019 Conference of the North American Chapter of the Association for Computational Linguistics:Human Language Technologies. New York: ACL, 2019: 4171-4186.
|
| [14] |
HE Kaiming, ZHANG Xiangyu, REN Shaoqing, et al. Deep Residual Learning for Image Recognition[C]// IEEE. 2016 IEEE Conference on Computer Vision and Pattern Recognition (CVPR). New York: IEEE, 2016: 770-778.
|
| [15] |
LEI Chengmin, MU Shaomin, SUN Wenjie, et al. Image Recognition of Peach Pests Based on Multi-Scale Attention Residual Network[J]. Journal of Shandong Agricultural University (Natural Science Edition), 2022, 53(2): 253-258.
|
|
类成敏, 牟少敏, 孙文杰, 等. 基于多尺度注意力残差网络的桃树害虫图像识别[J]. 山东农业大学学报(自然科学版), 2022, 53(2): 253-258.
|
| [16] |
CAI Yuhan. Image Classification Algorithm Based on Convolutional Self-Coding and Residual Network[J]. Information Technology and Informatization, 2022(7): 73-76.
|
|
蔡雨涵. 基于卷积自编码和残差网络的图像分类算法[J]. 信息技术与信息化, 2022(7): 73-76.
|
| [17] |
VASWANI A, SHAZEER N, PARMAR N, et al. Attention is All You Need[C]// ACM. The 31st International Conference on Neural Information Processing Systems. New York: ACM, 2017: 6000-6010.
|
| [18] |
NATHANI D, CHAUHAN J, SHARMA C, et al. Learning Attention-Based Embeddings for Relation Prediction in Knowledge Graphs[C]// ACL. The 57th Annual Meeting of the Association for Computational Linguistics. New York: ACL, 2019: 4710-4723.
|
| [19] |
REDMON J, FARHADI A. YOLOv3:An Incremental Improvemen[EB/OL]. (2018-04-08)[2025-08-03]. https://doi.org/10.48550/arXiv.1804.02767.
|
| [20] |
KIM W, LEE J, PARK E, et al. Advanced Mechanism for Reducing False Alarm Rate in Web Page Defacement Detection[EB/OL]. (2006-01-01)[2025-08-03]. https://www.researchgate.net/publication/228953432_Advanced_Mechanism_for_Reducing_False_Alarm_Rate_in_Web_Page_Defacement_Detection.
|
 ), XIE Wenwei2
), XIE Wenwei2