Netinfo Security ›› 2026, Vol. 26 ›› Issue (2): 171-188.doi: 10.3969/j.issn.1671-1122.2026.02.001
Previous Articles Next Articles
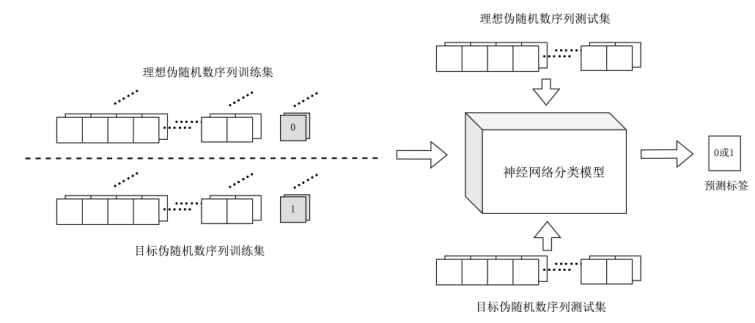
A Survey of Neural Network-Based Evaluation of Random Number Generators
HAN Yiliang( ), FENG Haokang, WU Xuguang, SUN Yuteng, WANG Yuanyuan
), FENG Haokang, WU Xuguang, SUN Yuteng, WANG Yuanyuan
College of Cryptography Engineering ,Engineering University of PAP Xi’an 710086, China
-
Received:2025-04-07Online:2026-02-10Published:2026-02-23
CLC Number:
Cite this article
HAN Yiliang, FENG Haokang, WU Xuguang, SUN Yuteng, WANG Yuanyuan. A Survey of Neural Network-Based Evaluation of Random Number Generators[J]. Netinfo Security, 2026, 26(2): 171-188.
share this article
Add to citation manager EndNote|Ris|BibTeX
URL: http://netinfo-security.org/EN/10.3969/j.issn.1671-1122.2026.02.001
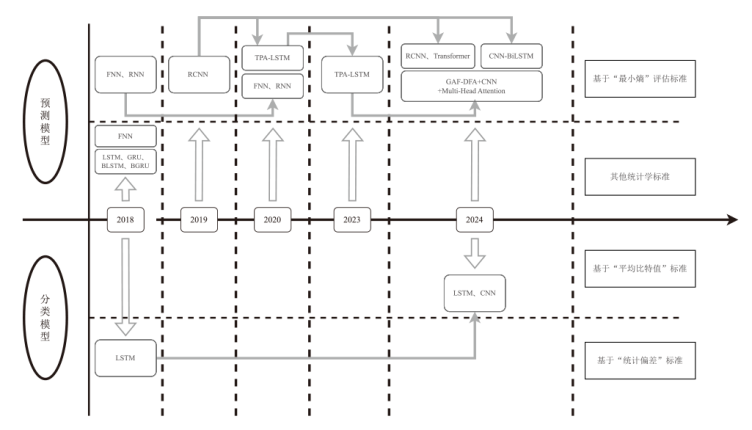
| 方案 | 模型 | 随机数 生成器 | 评估 标准 | 对比对象 |
|---|---|---|---|---|
| FAN[ | FNN | PRNG | 成功预测概率 | 无 |
| FISCHER[ | LSTM、GRU、BLSTM、BGRU | PRNG、CSPRNG | 统计学标准 | Diehard测试 |
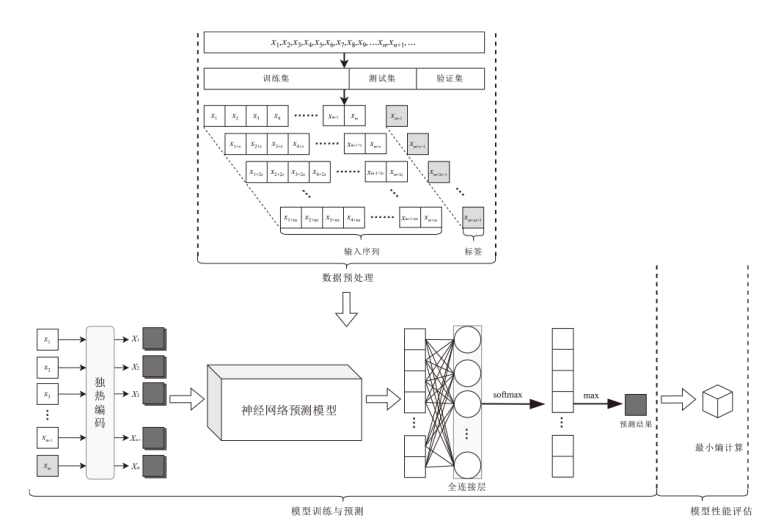
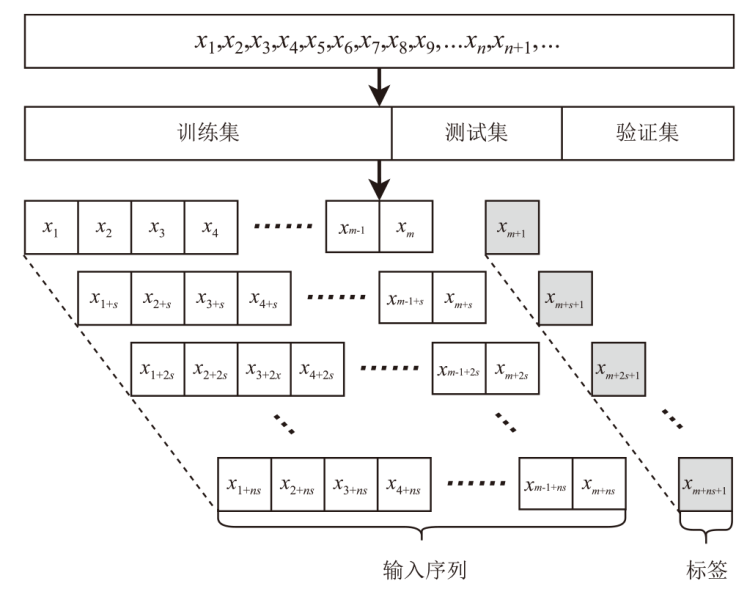
| YANG[ 等人方案 | FNN和RNN | PRNG | 最小熵 | NIST 800-90B |
| TRUONG[ | RCNN(LSTM+CNN) | TRNG、CSRNG | 最小熵 | NIST STS |
| LI[ 方案 | TPA-LSTM | TRNG、PRNG | 最小熵 | NIST SP 800-22 |
| LYU[ | FNN和RNN | PRNG | 最小熵 | NIST 800-90B |
| LI[ 方案 | TPA-LSTM | PRNG | 最小熵 | NIST 800-90B、FNN、RNN |
| BLANCO-ROMERO[ | RCNN、Transformer | PRNG | 平均最小熵 | NIST 800-90B |
| CAO[ | CNN-BiLSTM | TRNG | 最小熵 | NIST SP 800-22、RCNN |
| HUANG[ | GAF-DFA+二维CNN+ 多头自注意力机制 | PRNG | 最小熵 | NIST 800-90B、FNN、RNN、RCNN、TPA-LSTM |
| [1] |
CHEN Dongyu, CHEN Hua, FAN Limin, et al. Research on Test Strategy for Randomness Based on Deep Learning[J]. Journal on Communications, 2023, 44(6): 23-33.
doi: 10.11959/j.issn.1000-436x.2023111 |
|
陈东昱, 陈华, 范丽敏, 等. 基于深度学习的随机性检验策略研究[J]. 通信学报, 2023, 44(6): 23-33.
doi: 10.11959/j.issn.1000-436x.2023111 |
|
| [2] |
YOSHIYA K, TERASHIMA Y, KANNO K, et al. Entropy Evaluation of White Chaos Generated by Optical Heterodyne for Certifying Physical Random Number Generators[J]. Optics Express, 2020, 28(3): 3686-3698.
doi: 10.1364/OE.382234 pmid: 32122032 |
| [3] |
WANG Anbang, WANG Yuncai, WANG Bingjie, et al. Physical White Chaos Generation[J]. IEEE Journal of Selected Topics in Quantum Electronics, 2015, 21(6): 531-540.
doi: 10.1109/JSTQE.2015.2427253 URL |
| [4] | MARSAGLIA G. Random Number CDROM Including the Diehard Battery of Tests of Randomness[EB/OL]. (1995-12-09).[2025-02-03]. https://cir.nii.ac.jp/crid/1571698600607540352. |
| [5] | L’ECUYER P, SIMARD R. TestU01: A C Library for Empirical Testing of Random Number Generators[J]. ACM Transactions on Mathematical Software, 2007, 33(4): 1-40. |
| [6] | TURAN M S, BARKER E, KELSEY J, et al. Recommendation for the Entropy Sources Used for Random Bit Generation: NIST SP 800-90b[EB/OL]. (2025-01-27)[2025-03-27]. https://nvlpubs.nist.gov/nistpubs/SpecialPublications/NIST.SP.800-90B.pdf. |
| [7] |
GISIN N, RIBORDY G, TITTEL W, et al. Quantum Cryptography[J]. Reviews of Modern Physics, 2002, 74(1): 145-195.
doi: 10.1103/RevModPhys.74.145 URL |
| [8] | FENG Yulong, HAO Lingyi. Testing Randomness Using Artificial Neural Network[J]. IEEE Access, 2020, 8: 163685-163693. |
| [9] | VOLOVICH I V. Randomness in Classical Mechanics and Quantum Mechanics[J]. Foundations of Physics, 2011, 41(3): 516-528. |
| [10] |
OZKAYNAK F. Cryptographically Secure Random Number Generator with Chaotic Additional Input[J]. Nonlinear Dynamics, 2014, 78(3): 2015-2020.
doi: 10.1007/s11071-014-1591-y URL |
| [11] | PRENEEL B, DODUNEKOV S, RIJMEN V. Enhancing Cryptographic Primitives with Techniques from Error Correcting Codes[M]. Amsterdam: IOS Press, 2000. |
| [12] | HAAHR M. Introduction to Randomness and Random Numbers[J]. Statistics, 1999(8): 1-4. |
| [13] | LEE J S, CLEAVER G B. The Cosmic Microwave Background Radiation Power Spectrum as a Random Bit Generator for Symmetric and Asymmetric-Key Cryptography[J]. Heliyon, 2017, 3(10): 1-11. |
| [14] | ZHUN Huang, CHENHongyi. A Truly Random Number Generator Based on Thermal Noise[C]// IEEE. The 4th International Conference on ASIC. New York: IEEE, 2001: 62-86. |
| [15] | HAMBURG M, KOCHER P, MARSON M E. Analysis of Intel’s Ivy Bridge Digital Random Number Generator[R]. San Francisco, CA: Cryptography Research, Inc., Intel_TRNG_Report_20120312, 2012. |
| [16] |
STOJANOVSKI T, PIHL J, KOCAREV L. Chaos-Based Random Number Generators[J]. IEEE Transactions on Circuits and Systems I: Fundamental Theory and Applications, 2001, 48(3): 382-385.
doi: 10.1109/81.915396 URL |
| [17] | ANANTHASWAMY A. How to Ttrn a Quantum Computer into the Ultimate Randomness Generator[EB/OL]. (2019-06-19)[2025-03-27]. https://www.quantamagazine.org/how-to-turn-a-quantum-computer-into-the-ultimate-randomness-generator-20190619/. |
| [18] |
ELMAN J L. Finding Structure in Time[J]. Cognitive Science, 1990, 14(2): 179-211.
doi: 10.1207/s15516709cog1402_1 URL |
| [19] |
LECUN Y, BOTTOU L, BENGIO Y, et al. Gradient-Based Learning Applied to Document Recognition[J]. Proceedings of the IEEE, 1998, 86(11): 2278-2324.
doi: 10.1109/5.726791 URL |
| [20] | VASWANI A, SHAZEER N, PARMAR N, et al. Attention Is All You Need[EB/OL]. (2017-11-07)[2025-03-27]. https://arxiv.org/abs/1706.03762.. |
| [21] |
HOCHREITER S, SCHMIDHUBER J. Long Short-Term Memory[J]. Neural Computation, 1997, 9(8): 1735-1780.
doi: 10.1162/neco.1997.9.8.1735 pmid: 9377276 |
| [22] | CHO K, MERRIENBOER B, GULCEHRE C, et al. Learning Phrase Representations Using RNN Encoder-Decoder for Statistical Machine Translation[EB/OL]. (2014-09-03)[2025-03-29]. http://arxiv.org/abs/1406.1078. |
| [23] | RUKHIN A, SOTO J, NECHVATAL J, et al. A Statistical Test Suite for Random and Pseudo Random Number Generators for Cryptographic Applications[M]. Gaithersburg: NIST, 2001. |
| [24] | GM/T 0005-2021 Randomness Testing Specification[S]. Beijing: State Cryptography Administration, 2021. |
| GM/T 0005-2021 随机性检测规范[S]. 北京: 国家密码管理局, 2021. | |
| [25] |
HURLEY-SMITH D, HERNANDEZ-CASTRO J. Certifiably Biased: An In-Depth Analysis of a Common Criteria EAL4+ Certified TRNG[J]. IEEE Transactions on Information Forensics and Security, 2018, 13(4): 1031-1041.
doi: 10.1109/TIFS.2017.2777342 URL |
| [26] | MANTIN I, SHAMIR A. A Practical Attack on Broadcast RC4[C]// Springer. Fast Software Encryption Conference. Heidelberg: Springer, 2002: 152-164. |
| [27] | CRYPTREC. Investigation Reports on Cryptographic Techniques[EB/OL]. (2023-02-12)[2025-03-29]. https://www.cryptrec.go.jp/en/tech_reports.html. |
| [28] |
SHANNON C E. Prediction and Entropy of Printed English[J]. Bell System Technical Journal, 1951, 30(1): 50-64.
doi: 10.1002/bltj.1951.30.issue-1 URL |
| [29] | HAGERTY P, DRAPER T. Entropy Bounds and Statistical Tests[C]// NIST. The NIST Random Bit Generation Workshop. Gaithersburg: NIST, 2012: 5-6. |
| [30] | GOLIC J D. New Methods for Digital Generation and Postprocessing of Random Data[J]. IEEE Transactions on Computers, 2006, 55(10): 1217-1229. |
| [31] | WIECZOREK P Z, GOŁOFIT K. Dual-Metastability Time-Competitive True Random Number Generator[J]. IEEE Transactions on Circuits and Systems I: Regular Papers, 2014, 61(1): 134-145. |
| [32] | TURAN M S, BARKER E, KELSEY J, et al. Recommendation for the Entropy Sources Used for Random Bit Generation[R]. Gaithersburg: National Institute of Standards and Technology, NIST SP 800-90b, 2018. |
| [33] | KELSEY J, MCKAY K, TURAN M. Predictive Models for Min-Entropy Estimation[C]// Springer. Cryptographic Hardware and Embedded Systems Conference. Heidelberg: Springer, 2015: 373-392. |
| [34] | ZHU Shuangyi, MA Yuan, CHEN Tianyu, et al. Analysis and Improvement of Entropy Estimators in NIST SP 800-90B for Non-IID Entropy Sources[J]. IACR Transactions on Symmetric Cryptology, 2017(6): 151-168. |
| [35] | MENEZES A J, OORSCHOT P C, VANSTONE S A. Handbook of Applied Cryptography[M]. Boca Raton: CRC Press, 2018. |
| [36] | SAVIR J, MCANNEY W H. A Multiple Seed Linear Feedback Shift Register[C]// IEEE. International Test Conference. New York: IEEE, 1990: 657-659. |
| [37] | LI Youru, ZHU Zhenfeng, KONG Deqiang, et al. EA-LSTM: Evolutionary Attention-Based LSTM for Time Series Prediction[J]. Knowledge-Based Systems, 2019, 181: 85-96. |
| [38] | NIU Zhenwen, YU Zeyuan, TANG Wenhu, et al. Wind Power Forecasting Using Attention-Based Gated Recurrent Unit Network[J]. Energy, 2020, 196: 70-81. |
| [39] |
YUAN Ye, JIA Kebin, MA Fenglong, et al. A Hybrid Self-Attention Deep Learning Framework for Multivariate Sleep Stage Classification[J]. BMC Bioinformatics, 2019, 20(16): 586-595.
doi: 10.1186/s12859-019-3075-z |
| [40] | FAN Fenglei, WANG Ge. Learning from Pseudo-Randomness with an Artificial Neural Network-Does God Play Pseudo-Dice?[J]. IEEE Access, 2018, 6: 22987-22992. |
| [41] | FISCHER T. Testing Cryptographically Secure Pseudo Random Number Generators with Artificial Neural Networks[C]// IEEE. The 17th IEEE International Conference on Trust, Security and Privacy in Computing and Communications. New York: IEEE, 2018: 1214-1223. |
| [42] | YANG Jing, ZHU Shuangyi, CHEN Tianyu, et al. Neural Network Based Min-Entropy Estimation for Random Number Generators[C]// Springer. Security and Privacy in Communication Networks. Heidelberg: Springer, 2018: 231-250. |
| [43] | TRUONG N D, HAW J Y, ASSAD S M, et al. Machine Learning Cryptanalysis of a Quantum Random Number Generator[J]. IEEE Transactions on Information Forensics and Security, 2019, 14(2): 403-414. |
| [44] | LI Cai, ZHANG Jianguo, SANG Luxiao, et al. Deep Learning-Based Security Verification for a Random Number Generator Using White Chaos[J]. Entropy, 2020, 22(10): 11-34. |
| [45] | LYU Na, CHEN Tianyu, ZHU Shuangyi, et al. High-Efficiency Min-Entropy Estimation Based on Neural Network for Random Number Generators[J]. Security and Communication Networks, 2020, 20: 1-18. |
| [46] | LI Haohao, ZHANG Jianguo, LI Zhihua, et al. Improvement of Min-Entropy Evaluation Based on Pruning and Quantized Deep Neural Network[J]. IEEE Transactions on Information Forensics and Security, 2023, 18: 1410-1420. |
| [47] | BLANCO-ROMERO J, LORENZO V, ALMENARES M F, et al. Machine Learning Predictors for Min-Entropy Estimation[J]. Entropy, 2025, 27(2): 156-165. |
| [48] | CAO Jian, ZHANG Minghui, LIU Weiqi, et al. Deep Learning-Based Security Analysis of Quantum Random Numbers Generated by Imperfect Devices[J]. IEEE Transactions on Information Forensics and Security, 2024, 19: 7841-7852. |
| [49] | HUANG Yilong, FAN Fan, HUANG Chaofeng, et al. MA-DG: Learning Features of Sequences in Different Dimensions for Min-Entropy Evaluation via 2D-CNN and Multi-Head Self-Attention[J]. IEEE Transactions on Information Forensics and Security, 2024, 19: 7879-7894. |
| [50] | ZHU Shuangyi, MA Yuan, LI Xusheng, et al. On the Analysis and Improvement of Min-Entropy Estimation on Time-Varying Data[J]. IEEE Transactions on Information Forensics and Security, 2020, 15: 1696-1708. |
| [51] | KIMURA H, ISOBE T, OHIGASHI T. Neural-Network-Based Pseudo-Random Number Generator Evaluation Tool for Stream Ciphers[C]// IEEE. 2019 Seventh International Symposium on Computing and Networking Workshops. New York: IEEE, 2019: 333-338. |
| [52] | CRESPO J, GONZALEZ-VILLA J, GUTIERREZ J, et al. Assessing the Quality of Random Number Generators through Neural Networks[J]. Machine Learning: Science and Technology, 2024, 5(2): 72-83. |
| [53] | SINHA S, ISLAM S H, OBAIDAT M S. A Comparative Study and Analysis of Some Pseudorandom Number Generator Algorithms[J]. Security and Privacy, 2018, 1(6): 46-52. |
| [54] | PIRANDOLA S, ANDERSEN U L, BANCHI L, et al. Advances in Quantum Cryptography[J]. Advances in Optics and Photonics, 2020, 12(4): 1012-1236. |
| [55] | KIM K, CHOI S, KWON H, et al. FACE-LIGHT: Fast AES-CTR Mode Encryption for Low-End Microcontrollers[C]// Springer. Information Security and Cryptology- ICISC 2019. Heidelberg: Springer, 2020: 102-114. |
| [56] | ZHOU Haoyi, ZHANG Shanghang, PENG Jiepeng, et al. Informer: Beyond Efficient Transformer for Long Sequence Time-Series Forecasting[C]// AAAI. The AAAI Conference on Artificial Intelligence. Cambridge: AAAI, 2021: 11106-11115. |
| [57] | YU Han, GUO Peikun, SANO A. AdaWaveNet: Adaptive Wavelet Network for Time Series Analysis[EB/OL]. (2024-05-17)[2025-03-11]. http://arxiv.org/abs/2405.11124. |
| [58] | LI Yanan, WANG Zhimin, XING Ruipeng, et al. Quantum Gated Recurrent Neural Networks[J]. IEEE Transactions on Pattern Analysis and Machine Intelligence, 2025, 47(4): 2493-2504. |
| [59] | LIU Junhua, LIM K H, WOOD K L, et al. Hybrid Quantum-Classical Convolutional Neural Networks[J]. Science China Physics, Mechanics & Astronomy, 2021, 64(9): 290-311. |
| [60] | SCARANI V, BECHMANN-PASQUINUCCI H, CERF N J, et al. The Security of Practical Quantum Key Distribution[J]. Reviews of Modern Physics, 2009, 81(3): 1301-1350. |
| [1] | LENG Yongqing, AO Tianyong, QIU Xin, CUI Xingli, LI Shaoshi. Design and Implementation of Automatic Assessment System for Cryptographic Criteria of S-Box [J]. Netinfo Security, 2025, 25(7): 1103-1110. |
| [2] | YANG Yijia, LI Kangquan, SUN Bing. Research on Orthomorphic Permutations Based on Cryptographic Structure [J]. Netinfo Security, 2025, 25(5): 722-731. |
| [3] | ZHANG Xinglan, TAO Kejin. Universal Perturbations Generation Method Based on High-Level Features and Important Channels [J]. Netinfo Security, 2025, 25(5): 767-777. |
| [4] | LI Xiao, SONG Xiao, LI Yong. Research on Differential Privacy Methods for Medical Diagnosis Based on Knowledge Distillation [J]. Netinfo Security, 2025, 25(4): 524-535. |
| [5] | HAN Yiliang, PENG Yixuan, WU Xuguang, LI Yu. Multimodal Feature Fusion Encrypted Traffic Classification Model Based on Graph Variational Auto-Encoder [J]. Netinfo Security, 2025, 25(12): 1914-1926. |
| [6] | ZHANG Lu, JIA Peng, LIU Jiayong. Binary Code Similarity Detection Method Based on Multivariate Semantic Graph [J]. Netinfo Security, 2025, 25(10): 1589-1603. |
| [7] | GUO Xiangxin, LIN Jingqiang, JIA Shijie, LI Guangzheng. Security Analysis of Cryptographic Application Code Generated by Large Language Model [J]. Netinfo Security, 2024, 24(6): 917-925. |
| [8] | YAN Hailong, WANG Shulan. Design and Implementation of Integrated Service Platform for Real Estate Registration Based on Domestic Cryptographic Technology [J]. Netinfo Security, 2024, 24(2): 303-308. |
| [9] | ZHANG Xuan, WAN Liang, LUO Heng, YANG Yang. Automated Botnet Detection Method Based on Two-Stage Graph Learning [J]. Netinfo Security, 2024, 24(12): 1933-1947. |
| [10] | SA Qirui, YOU Weijing, ZHANG Yifei, QIU Weiyang, MA Cunqing. A Survey of Ownership Protection Schemes for Federated Learning Models [J]. Netinfo Security, 2024, 24(10): 1553-1561. |
| [11] | JIANG Zenghui, ZENG Weijun, CHEN Pu, WU Shitao. Review of Adversarial Samples for Modulation Recognition [J]. Netinfo Security, 2023, 23(6): 74-90. |
| [12] | ZHAO Xiaolin, WANG Qiyao, ZHAO Bin, XUE Jingfeng. Research on Anonymous Traffic Classification Method Based on Machine Learning [J]. Netinfo Security, 2023, 23(5): 1-10. |
| [13] | ZHAO Caidan, CHEN Jingqian, WU Zhiqiang. Automatic Modulation Recognition Algorithm Based on Multi-Channel Joint Learning [J]. Netinfo Security, 2023, 23(4): 20-29. |
| [14] | WANG Jingyu, MA Zhaofeng, XU Danheng, DUAN Pengfei. Blockchain Transaction Data Privacy-Preserving Scheme Supporting National Cryptographic Algorithm [J]. Netinfo Security, 2023, 23(3): 84-95. |
| [15] | XU Shengwei, DENG Ye, LIU Changhe, TAN Li. A Selective Encryption Scheme for Audio and Video Based on the National Cryptographic Algorithm [J]. Netinfo Security, 2023, 23(11): 48-57. |
| Viewed | ||||||
|
Full text |
|
|||||
|
Abstract |
|
|||||