Netinfo Security ›› 2026, Vol. 26 ›› Issue (2): 189-210.doi: 10.3969/j.issn.1671-1122.2026.02.002
Previous Articles Next Articles
CCASim: Research on Performance Simulator for Arm Confidential Compute Architecture
LIN Tiantian1,2, WANG Yitian1,2, WANG Xiaohang1,2( ), ZHU Ting1,2, REN Kui1,2
), ZHU Ting1,2, REN Kui1,2
1. The State Key Laboratory of Blockchain and Data Security ,Zhejiang University Hangzhou 310027, China 2. Institute of Blockchain and Data Security ,Hangzhou High-Tech Zone (Binjiang) Hangzhou 310052, China
-
Received:2025-08-27Online:2026-02-10Published:2026-02-23
CLC Number:
Cite this article
LIN Tiantian, WANG Yitian, WANG Xiaohang, ZHU Ting, REN Kui. CCASim: Research on Performance Simulator for Arm Confidential Compute Architecture[J]. Netinfo Security, 2026, 26(2): 189-210.
share this article
Add to citation manager EndNote|Ris|BibTeX
URL: http://netinfo-security.org/EN/10.3969/j.issn.1671-1122.2026.02.002
| 基准测试 | 内容 |
|---|---|
| 多世界互相访问 | 在4个世界中分别进行105次4 GB物理地址范围内的随机地址访问,测试GPT的跨域内存隔离功能 |
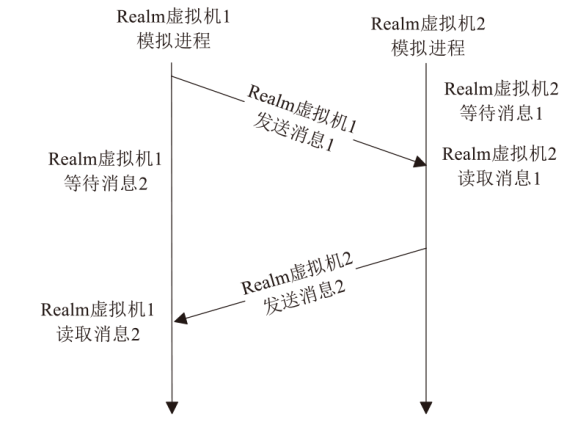
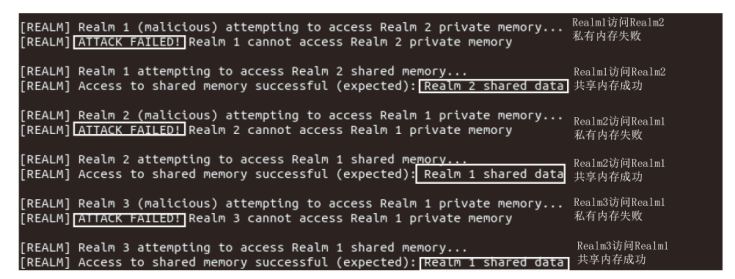
| 多Realm虚拟机通信与私有内存攻击 | 使用前后端分离式仿真器仿真2台Realm虚拟机的共享内存通信与私有内存访问;在全系统模式仿真中,仿真10台恶意Realm虚拟机互相访问私有内存,测试私有内存加密 |
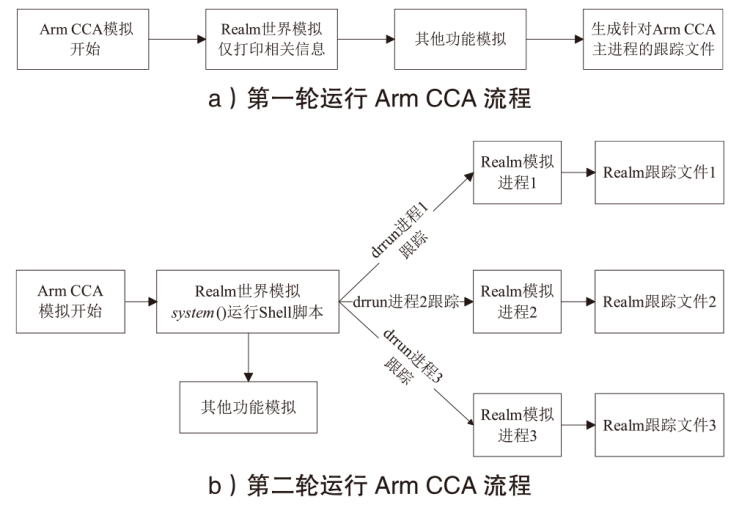
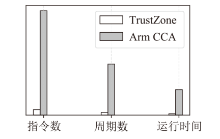
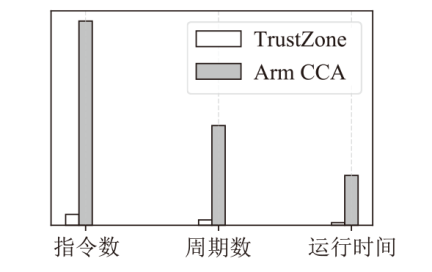
| Arm CCA运行 | 运行完整的Arm CCA仿真程序,获取其运行开销 |
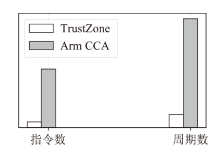
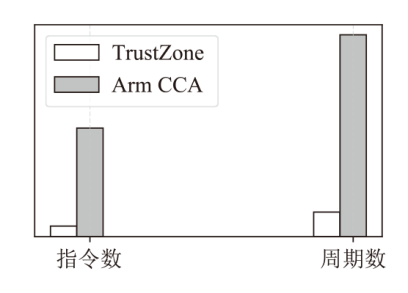
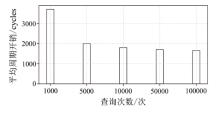
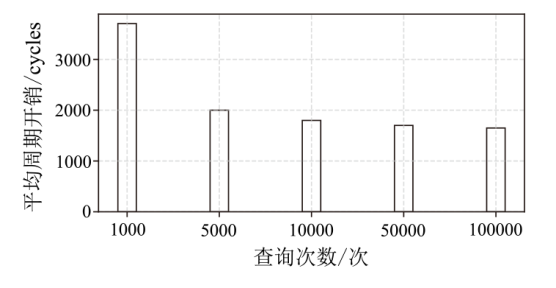
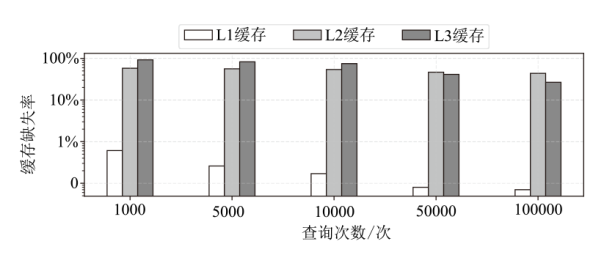
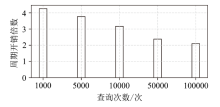
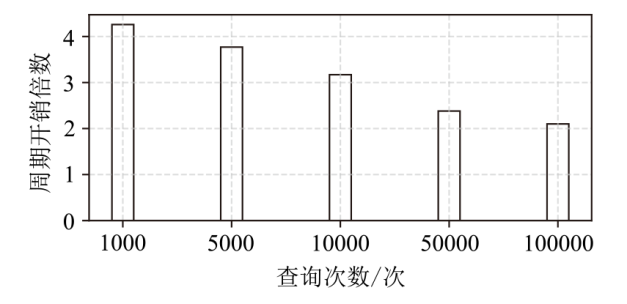
| GPT查询 | 进行103~105次随机内存访问,测试查询次数对GPT查询性能的影响;针对4 GB~128 GB物理地址空间构建的GPT进行105次随机查询,测试GPT大小对查询性能的影响 |
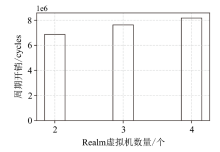
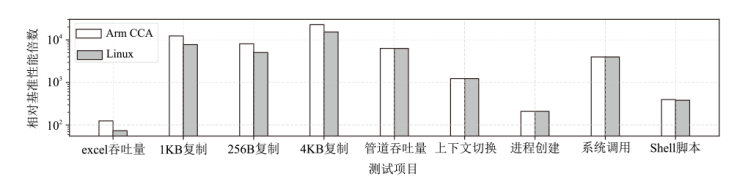
| 多Realm虚拟机 并行运行 | 以UnixBench作为Realm应用,测试虚拟机 性能开销 |
| [1] | XU Xiangyi, WANG Wenhao, WU Yongzheng, et al. virtCCA: Virtualized Arm Confidential Compute Architecture with TrustZone[EB/OL]. (2024-02-18)[2025-06-11]. https://doi.org/10.48550/arXiv.2306.1101. |
| [2] | Huawei. Huawei CCA QEMU[EB/OL]. [2025-06-11]. https://github.com/Huawei/Huawei_CCA_QEMU. |
| [3] | ZHANG Yiming, HU Yuxin, NING Zhenyu, et al. SHELTER: Extending Arm CCA with Isolation in User Space[C]// USENIX. The 32nd USENIX Security Symposium (USENIX Security 23). Berkely: USENIX, 2023: 6257-6274. |
| [4] | Gem5. Gem5: The Gem5 Simulator System[EB/OL]. [2025-06-11]. https://www.gem5.org/. |
| [5] | Sniper. The Sniper Multi-Core Simulator[EB/OL]. [2025-06-11]. https://snipersim.org//w/The_Sniper_Multi-Core_Simulator. |
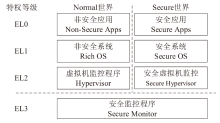
| [6] | ARM. TrustZone for Cortex-A[EB/OL]. [2025-06-11]. https://www.arm.com/technologies/trustzone-for-cortex-a. |
| [7] | ARM. Exception Levels[EB/OL]. [2025-06-11]. https://developer.arm.com/documentation/102412/0103/Privilege-and-Exception-levels. |
| [8] | DAVID C, NUNO S, PEDRO F, et al. SoK: Understanding the Prevailing Security Vulnerabilities in TrustZone-Assisted TEE Systems[C]// IEEE. 2020 IEEE Symposium on Security and Privacy (SP). New York: IEEE, 2020: 1416-1432. |
| [9] | DAVID C, JOSÉ M, NUNO S, et al. ReZone: Disarming TrustZone with TEE Privilege Reduction[C]// USENIX. The 31st USENIX Security Symposium (USENIX Security 22). Berkely: USENIX, 2022: 2261-2279. |
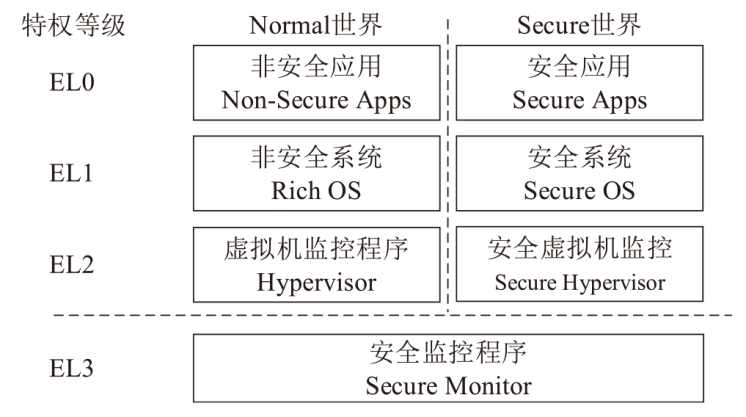
| [10] | DAVID S. Arm Introduces Its Confidential Compute Architecture[EB/OL]. (2021-06-23)[2025-06-11]. https://fuse.wikichip.org/news/5699/arm-introduces-its-confidential-compute-architecture/. |
| [11] | LI Xupeng, LI Xuheng, CHRISTOFFER D, et al. Enabling Realms with the Arm Confidential Compute Architecture[EB/OL]. (2023-07-13)[2025-06-11]. https://www.usenix.org/publications/loginonline/enabling-realms-arm-confidential-compute-architecture. |
| [12] | Trusted Firmware-A. Realm Management Extension (RME)[EB/OL]. [2025-06-11]. https://trustedfirmware-a.readthedocs.io/en/latest/components/realm-management-extension.html. |
| [13] | ARM. Realm Management Monitor[EB/OL]. [2025-06-11]. https://developer.arm.com/documentation/den0127/0200/Software-components/Realm-Management-Monitor. |
| [14] | WANG Chenxu, ZHANG Fengwei, DENG Yunjie, et al. CAGE: Complementing Arm CCA with GPU Extensions[C]// NDSS. The Network and Distributed System Security Symposium (NDSS Symposium 2024). Reston: Internet Society, 2024: 1-16. |
| [15] | ARM. Granule Protection Checks[EB/OL]. [2025-06-11]. https://developer.arm.com/documentation/den0126/0101/Granule-Protection-Checks. |
| [16] | DynamoRIO. DynamoRIO Home Page[EB/OL]. [2025-06-11]. https://dynamorio.org/. |
| [17] | Capstone Engine. Capstone[EB/OL]. [2025-06-11]. https://github.com/capstone-engine/capstone. |
| [18] | ARM. Arm CCA Hardware Architecture-Memory Management for Arm CCA[EB/OL]. [2025-06-11]. https://developer.arm.com/documentation/den0125/0300/Arm-CCA-Hardware-ArchitectureArm. |
| [19] | ANDREW F, ANDREW B, CHRIS H, et al. Using Verification to Disentangle Secure-Enclave Hardware from Software[C]// ACM. The 26th Symposium on Operating Systems Principles(SOSP ’17). New York: ACM, 2017: 287-305. |
| [20] | HIMANSHU R, STEFAN S, ALEC W, et al. fTPM: A Software-Only Implementation of a TPM Chip[C]// USENIX. The 25th USENIX Conference on Security Symposium(SEC’16). Berkely: USENIX, 2016: 841-856. |
| [1] | ZHAO Jia, WANG Yanchun, MA Hongliang, LI Qi. Hierarchical Role-Based Encryption Scheme Based on Trusted Execution Environment [J]. Netinfo Security, 2026, 26(2): 315-324. |
| [2] | SHI Yijuan, ZHOU Danping, FAN Lei, LIU Yin. Secure Multi-Party Computation Protocol Based on Trusted Execution Environment [J]. Netinfo Security, 2025, 25(9): 1439-1446. |
| [3] | ZHU Hui, FANG Yunyi, WANG Fengwei, XU Wei. Research Progress on Data Security Processing Integrating Confidential Computing [J]. Netinfo Security, 2025, 25(11): 1643-1657. |
| [4] | HAO Meng, LI Jiayong, YANG Hongwei, ZHANG Weizhe. Heterogeneous CPU-GPU System Confidential Computing Survey [J]. Netinfo Security, 2025, 25(11): 1658-1672. |
| [5] | GUAN Zhi, HU Jianbin, LI Yue, CHEN Zhong. A Comprehensive Survey of Blockchain Technologies and Applications Based on Trusted Execution Environments [J]. Netinfo Security, 2025, 25(11): 1673-1690. |
| [6] | REN Fengyuan, ZHANG Xinyue, LEI Zhuoyi, LIU Xin. Research on Key-Value Data Storage and Operation Optimization Method Based on Confidential Computing [J]. Netinfo Security, 2025, 25(11): 1707-1717. |
| [7] | XUE Kaiping, ZHANG Chunyi, LIU Feng, WANG Feng. Security-Enhanced Index Scheme in Encrypted Database Based on Trusted Execution Environment [J]. Netinfo Security, 2025, 25(11): 1718-1731. |
| [8] | ZHAO Bo, LYU Jiamin, WANG Yixuan. A Multidimensional Security Measurement Architecture for the Container Lifecycle [J]. Netinfo Security, 2025, 25(11): 1745-1761. |
| [9] | WANG Yajie, LU Jinbiao, LI Yuhang, FAN Qing, ZHANG Zijian, ZHU Liehuang. Hierarchical Dynamic Protection Algorithm for Federated Learning Based on Trusted Execution Environment [J]. Netinfo Security, 2025, 25(11): 1762-1773. |
| [10] | LU Di, LIU Yujia, LYU Chaoyue, SUN Mengna, ZHANG Qingwen, YANG Li. Cloud-Native TEE Service Sharing Mechanism for Secure Edge Computing [J]. Netinfo Security, 2025, 25(11): 1774-1791. |
| [11] | HU Yuyi, CAI Wei, CHEN Jingfan, LIU Mohan, WANG Juan, HE Yun. Research on Unified Remote Attestation Mechanism for Confidential Containers Devices [J]. Netinfo Security, 2025, 25(11): 1811-1823. |
| [12] | YU Fajiang, WANG Chaozhou. Implementation Mechanism for TrustZone Paravirtualization and Containerization [J]. Netinfo Security, 2025, 25(10): 1523-1536. |
| [13] | SUN Yu, XIONG Gaojian, LIU Xiao, LI Yan. A Survey on Trusted Execution Environment Based Secure Inference [J]. Netinfo Security, 2024, 24(12): 1799-1818. |
| [14] | TANG Yu, ZHANG Chi. A Privacy Protection Scheme for Information-Centric Networking Based on Intel SGX [J]. Netinfo Security, 2023, 23(6): 55-65. |
| [15] | LIU Xin, LI Yunyi, WANG Miao. A Lightweight Authentication Protocol Based on Confidential Computing for Federated Learning Nodes [J]. Netinfo Security, 2022, 22(7): 37-45. |
| Viewed | ||||||
|
Full text |
|
|||||
|
Abstract |
|
|||||