| [1] |
ASOKAN N, EKBERG J E, KOSTIAINEN K, et al. Mobile Trusted Computing[J]. Proceedings of the IEEE, 2014, 102(8): 1189-1206.
doi: 10.1109/JPROC.2014.2332007
URL
|
| [2] |
CHANG C C, LIN I C, TSAI H M, et al. A Key Assignment Scheme for Controlling Access in Partially Ordered User Hierarchies[C]// IEEE. The 18th International Conference on Advanced Information Networking and Applications. New York: IEEE, 2004: 376-379.
|
| [3] |
AKL S G, TAYLOR P D. Cryptographic Solution to a Problem of Access Control in a Hierarchy[J]. ACM Transactions on Computer Systems, 1983, 1(3): 239-248.
doi: 10.1145/357369.357372
URL
|
| [4] |
ATALLAH M J, BLANTON M, FAZIO N, et al. Dynamic and Efficient Key Management for Access Hierarchies[J]. ACM Transactions on Information and System Security, 2009, 12(3): 1-43.
|
| [5] |
LIN Yuli, HSU C L. Secure Key Management Scheme for Dynamic Hierarchical Access Control Based on ECC[J]. Journal of Systems and Software, 2011, 84(4): 679-685.
doi: 10.1016/j.jss.2010.11.926
URL
|
| [6] |
TANG Shaohua, LI Xiaoyu, HUANG Xinyi, et al. Achieving Simple, Secure and Efficient Hierarchical Access Control in Cloud Computing[J]. IEEE Transactions on Computers, 2016, 65(7): 2325-2331.
doi: 10.1109/TC.2015.2479609
URL
|
| [7] |
CHEN Y R, TZENG W G. Hierarchical Key Assignment with Dynamic Read-Write Privilege Enforcement and Extended KI-Security[C]// Springer. International Conference on Applied Cryptography and Network Security. Heidelberg: Springer, 2017: 165-183.
|
| [8] |
PAREEK G, PURUSHOTHAMA B R. Efficient Strong Key Indistinguishable Access Control in Dynamic Hierarchies with Constant Decryption Cost[C]// ACM. The 11th International Conference on Security of Information and Networks. New York: ACM, 2018: 1-7.
|
| [9] |
ZHOU Lan, VARADHARAJAN V, HITCHENS M. Enforcing Role-Based Access Control for Secure Data Storage in the Cloud[J]. The Computer Journal, 2011, 54(10): 1675-1687.
doi: 10.1093/comjnl/bxr080
URL
|
| [10] |
ZHU Yan, AHN G J, HU Hongxin, et al. Role-Based Cryptosystem: A New Cryptographic RBAC System Based on Role-Key Hierarchy[J]. IEEE Transactions on Information Forensics and Security, 2013, 8(12): 2138-2153.
doi: 10.1109/TIFS.2013.2287858
URL
|
| [11] |
MARIN-PERE J M, PEREZ G M, SKARMETA-GOMEZ A F. SecRBAC: Secure Data in the Clouds[J]. IEEE Transactions on Services Computing, 2017, 10(5): 726-740.
doi: 10.1109/TSC.2016.2553668
URL
|
| [12] |
SCHWARZ M, WEISER S, GRUSS D. Practical Enclave Malware with Intel SGX[C]// Springer. International Conference on Detection of Intrusions and Malware, and Vulnerability Assessment. Heidelberg: Springer, 2019: 177-196.
|
| [13] |
RAN Jinhao, CAI Dongliang. Attribute Signature Identity Authentication Scheme Based on Blockchain and Trusted Execution Environment[J]. Journal of Computer Research and Development, 2023, 60(11): 2555-2566.
|
|
冉津豪, 蔡栋梁. 基于区块链和可信执行环境的属性签名身份认证方案[J]. 计算机研究与发展, 2023, 60(11):2555-2566.
|
| [14] |
YE Jiajun. Research on Federated Learning Algorithms Based on Trusted Execution Environment[D]. Hangzhou: Zhejiang University, 2024.
|
|
叶家俊. 基于可信执行环境的联邦学习算法研究[D]. 杭州: 浙江大学, 2024.
|
| [15] |
HE Jiahao. Research and Implementation of Data Privacy Protection Method for Fabric Consortium Chain Based on Trusted Execution Environment[D]. Nanjing: Southeast University, 2023.
|
|
何嘉昊. 基于可信执行环境的Fabric联盟链数据隐私保护方法研究与实现[D]. 南京: 东南大学, 2023.
|
| [16] |
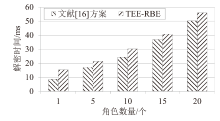
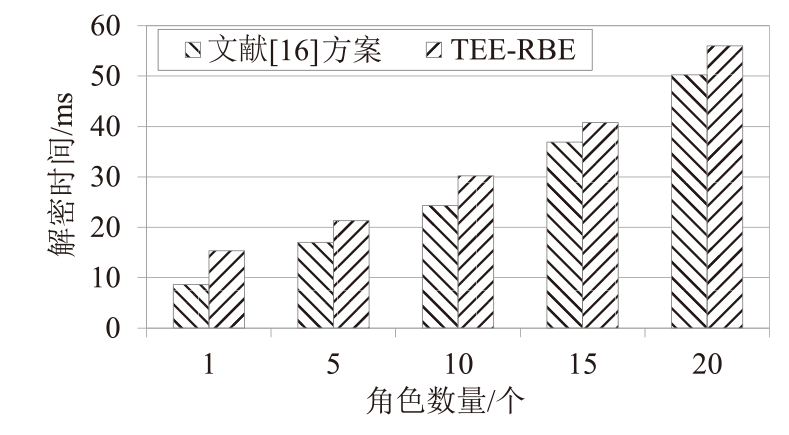
SULTAN N H, VARADHARAJAN V, ZHOU Lan, et al. A Role-Based Encryption(RBE) Scheme for Securing Outsourced Cloud Data in a Multi-Organization Context[J]. IEEE Transactions on Services Computing, 2022, 16(3): 1647-1661.
doi: 10.1109/TSC.2022.3194252
URL
|
 ), WANG Yanchun1, MA Hongliang2, LI Qi3
), WANG Yanchun1, MA Hongliang2, LI Qi3