Netinfo Security ›› 2025, Vol. 25 ›› Issue (3): 494-503.doi: 10.3969/j.issn.1671-1122.2025.03.011
Previous Articles Next Articles
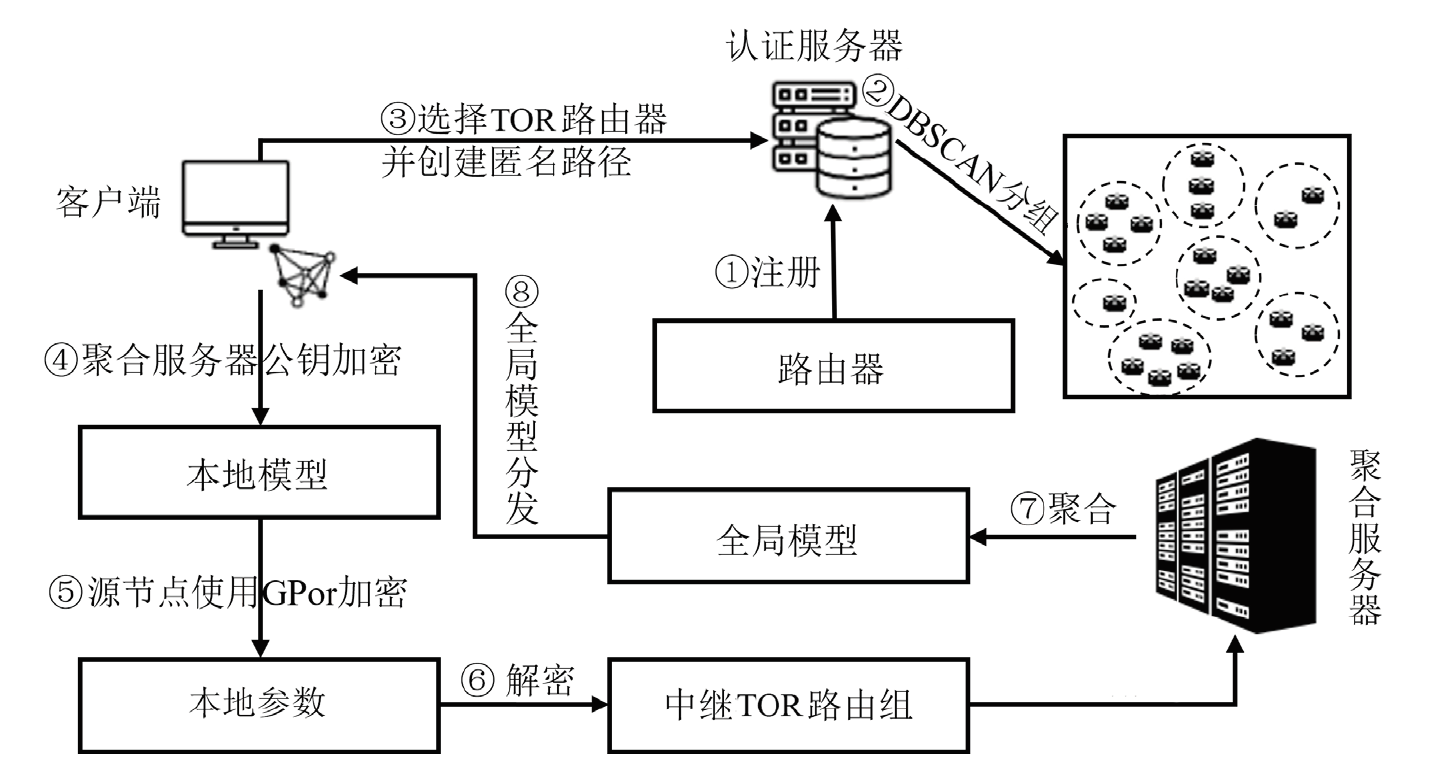
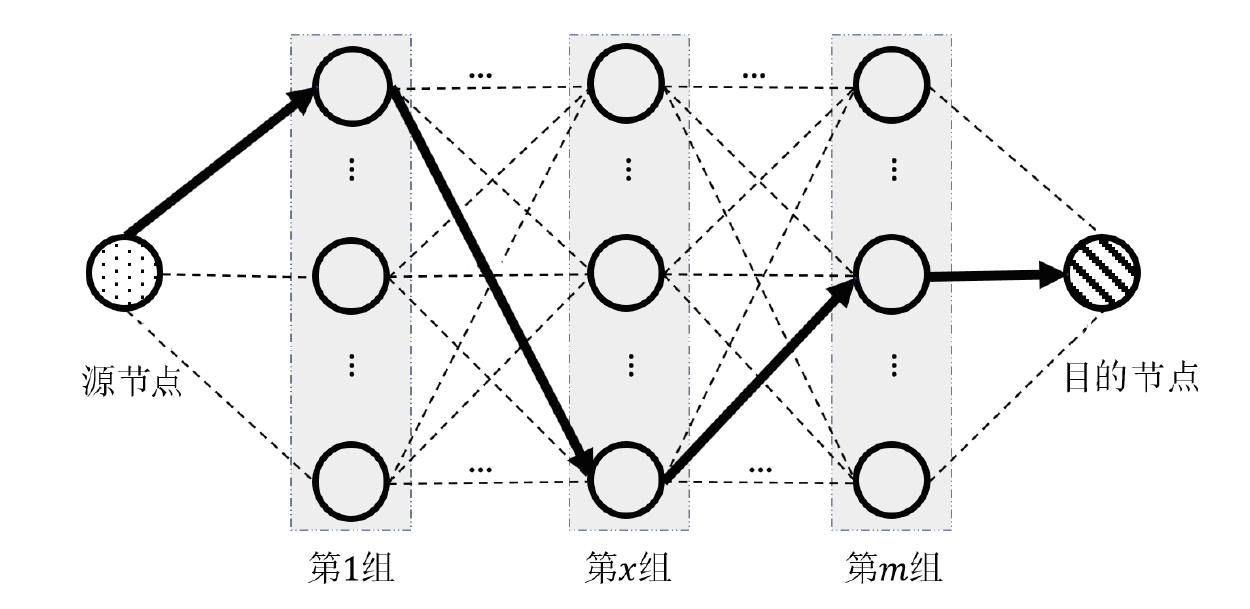
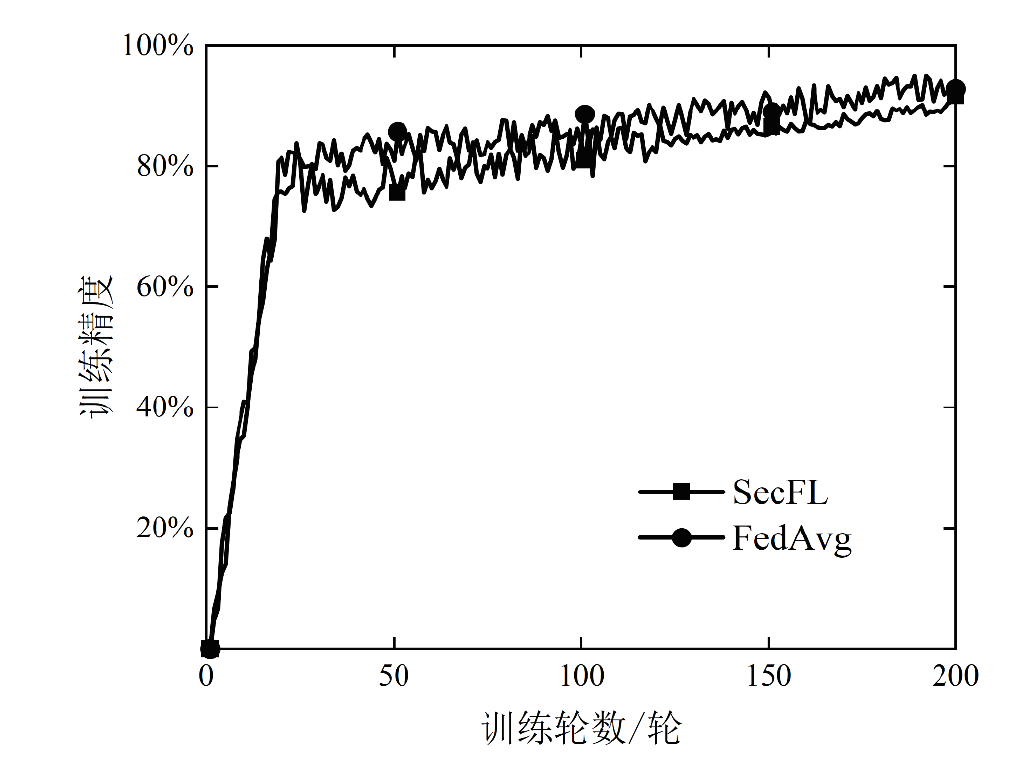
An Anonymous Routing Federated Learning Framework for Data Privacy Protection
LI Jiadong, ZENG Haitao, PENG Li, WANG Xiaoding( )
)
- College of Computer and Cyber Security, Fujian Normal University, Fuzhou 350117, China
-
Received:2024-06-11Online:2025-03-10Published:2025-03-26 -
Contact:WANG Xiaoding E-mail:wangdin1982@fjnu.edu.cn
CLC Number:
Cite this article
LI Jiadong, ZENG Haitao, PENG Li, WANG Xiaoding. An Anonymous Routing Federated Learning Framework for Data Privacy Protection[J]. Netinfo Security, 2025, 25(3): 494-503.
share this article
| [1] | MCMAHAN H B, MOORE E, RAMAGE D, et al. Communication-Efficient Learning of Deep Networks from Decentralized Data[EB/OL]. (2016-02-17)[2024-05-16]. https://arxiv.org/abs/1602.05629v4. |
| [2] | BONAWITZ K, EICHNER H, GRIESKAMP W, et al. Towards Federated Learning at Scale: System Design[J]. (2019-03-22)[2024-05-16]. https://doi.org/10.48550/arXiv.1902.01046. |
| [3] |
LI Tian, SAHU A K, TALWALKAR A, et al. Federated Learning: Challenges, Methods, and Future Directions[J]. IEEE Signal Processing Magazine, 2020, 37(3): 50-60.
doi: 10.1109/MSP.2020.2975749 |
| [4] |
WANG Teng, HUO Zheng, HUANG Yaxin, et al. Review on Privacy-Preserving Technologies in Federated Learning[J]. Journal of Computer Applications, 2023, 43(2): 437-449.
doi: 10.11772/j.issn.1001-9081.2021122072 |
|
王腾, 霍峥, 黄亚鑫, 等. 联邦学习中的隐私保护技术研究综述[J]. 计算机应用, 2023, 43(2): 437-449.
doi: 10.11772/j.issn.1001-9081.2021122072 |
|
| [5] | MELIS L, SONG Congzheng, DE C E, et al. Exploiting Unintended Feature Leakage in Collaborative Learning[C]// IEEE. 2019 IEEE Symposium on Security and Privacy (SP). New York: IEEE, 2019: 691-706. |
| [6] | LAI Chengzhe, ZHAO Yining, ZHENG Dong. A Privacy Preserving and Verifiable Federated Learning Scheme Based on Homomorphic Encryption[J]. Netinfo Security, 2024, 24(1): 93-105. |
| 赖成喆, 赵益宁, 郑东. 基于同态加密的隐私保护与可验证联邦学习方案[J]. 信息网络安全, 2024, 24(1): 93-105. | |
| [7] | SINGH P, SINGH M K, SINGH R, et al. Federated Learning:Challenges, Methods, and Future Directions[M]. Heidelberg: Springer, 2022. |
| [8] | ZHU Ligeng, LIU Zhijian, HAN Song. Deep Leakage from Gradients[J]. Neural Information Processing Systems, 2019(1323): 14774-14784. |
| [9] | WAINAKH A, VENTOLA F, MÜßIG T, et al. User-Level Label Leakage from Gradients in Federated Learning[EB/OL]. (2021-05-19)[2024-05-16]. https://doi.org/10.48550/arXiv.2105.09369. |
| [10] | ZHANG Xinwei, CHEN Xiangyi, HONG Mingyi, et al. Understanding Clipping for Federated Learning: Convergence and Client-Level Differential Privacy[EB/OL]. (2021-06-25)[2024-05-16]. https://doi.org/10.48550/arXiv.2106.13673. |
| [11] | BONAWITZ K, IVANOV V, KREUTER B, et al. Practical Secure Aggregation for Privacy-Preserving Machine Learning[C]// ACM. Proceedings of the 2017 ACM SIGSAC Conference on Computer and Communications Security. New York: ACM, 2017: 1175-1191. |
| [12] | SAV S, PYRGELIS A, TRONCOSO-PASTORIZA J R, et al. POSEIDON: Privacy-Preserving Federated Neural Network Learning[EB/OL]. (2021-01-08)[2024-05-16]. https://arxiv.org/abs/2009.00349v3. |
| [13] | DINGLEDINE R, MATHEWSON N, SYVERSON P F. Tor: The Second-Generation Onion Router[EB/OL]. (2004-08-09)[2024-05-16]. https://www.usenix.org/conference/13th-usenix-security-symposium/tor-second-generation-onion-router. |
| [14] | LAI R W F, CHEUNG H K F, CHOW S S M, et al. Another Look at Anonymous Communication[J]. IEEE Transactions on Dependable and Secure Computing, 2017, 16(5): 731-742. |
| [15] | VAKDE G, BIBIKAR R, LE Zhengyi, et al. EnPassant: Anonymous Routing for Disruption-Tolerant Networks with Applications in Assistive Environments[J]. Security and Communication Networks, 2011, 4(11): 1243-1256. |
| [16] | SHI Cong, LUO Xiapu, TRAYNOR P, et al. ARDEN: Anonymous Networking in Delay Tolerant Networks[J]. Ad Hoc Networks, 2012, 10(6): 918-930. |
| [17] | CAMENISCH J, HOHENBERGER S, KOHLWEISS M, et al. How to Win the Clonewars: Efficient Periodic N-Times Anonymous Authentication[C]// ACM. Proceedings of the 13th ACM Conference on Computer and Communications Security. New York: ACM, 2006: 201-210. |
| [18] |
LI Yijing, TAO Xiaofeng, ZHANG Xuefei, et al. Privacy-Preserved Federated Learning for Autonomous Driving[J]. IEEE Transactions on Intelligent Transportation Systems, 2022, 23(7): 8423-8434.
doi: 10.1109/TITS.2021.3081560 |
| [19] | DOMINGO-FERRER J, BLANCO-JUSTICIA A, MANJÓN J, et al. Secure and Privacy-Preserving Federated Learning via Co-Utility[J]. IEEE Internet of Things Journal, 2022, 9(5): 3988-4000. |
| [20] | CATALANO D, FIORE D, GENNARO R. A Certificateless Approach to Onion Routing[J]. International Journal of Information Security, 2017, 16(3): 327-343. |
| [21] | GIRGIS A M, DATA D, DIGGAVI S, et al. Shuffled Model of Federated Learning: Privacy, Accuracy and Communication Trade-Offs[J]. IEEE Journal on Selected Areas in Information Theory, 2021, 2(1): 464-478. |
| [22] | LYU Lingjuan, YU Jiangshan, NANDAKUMAR K, et al. Towards Fair and Privacy-Preserving Federated Deep Models[J]. IEEE Transactions on Parallel and Distributed Systems, 2020, 31(11): 2524-2541. |
| [23] | CHEN Yijin, SU Ye, ZHANG Mingyue, et al. FedTor: An Anonymous Framework of Federated Learning in Internet of Things[J]. IEEE Internet of Things Journal, 2022, 9(19): 18620-18631. |
| [24] | KOTZANIKOLAOU P, CHATZISOFRONIOU G, BURMESTER M. Broadcast Anonymous Routing (BAR): Scalable Real-Time Anonymous Communication[J]. International Journal of Information Security, 2017, 16(3): 313-326. |
| [25] | HAN Guangjie, ZHOU Lina, WANG Hao, et al. A Source Location Protection Protocol Based on Dynamic Routing in WSNS for the Social Internet of Things[J]. Future Generation Computer Systems, 2018, 82: 689-697. |
| [26] | KIM S, HAN J, HA J, et al. SGX-Tor: A Secure and Practical Tor Anonymity Network with SGX Enclaves[J]. IEEE/ACM Transactions on Networking, 2018, 26(5): 2174-2187. |
| [27] | WOLINSKY D I, CORRIGAN-GIBBS H, FORD B, et al. Dissent in Numbers: Making Strong Anonymity Scale[C]// USENIX. The 10th USENIX Symposium on Operating Systems Design and Implementation (OSDI’12). Berlin:USENIX, 2012: 179-182. |
| [28] | HASIRCIOGLU B, GUNDUZ D. Private Wireless Federated Learning with Anonymous Over-the-Air Computation[C]// IEEE. ICASSP 2021 IEEE International Conference on Acoustics, Speech and Signal Processing (ICASSP). New York: IEEE, 2021: 5195-5199. |
| [1] | XU Ruzhi, TONG Yumeng, DAI Lipeng. Research on Federated Learning Adaptive Differential Privacy Method Based on Heterogeneous Data [J]. Netinfo Security, 2025, 25(1): 63-77. |
| [2] | WEN Jinming, LIU Qing, CHEN Jie, WU Yongdong. Research Current Status and Challenges of Fully Homomorphic Cryptography Based on Learning with Errors [J]. Netinfo Security, 2024, 24(9): 1328-1351. |
| [3] | LIN Zhanhang, XIANG Guangli, LI Zhenpeng, XU Ziyi. Privacy Protection Scheme of Feedforward Neural Network Based on Homomorphic Encryption [J]. Netinfo Security, 2024, 24(9): 1375-1385. |
| [4] | GUO Qian, ZHAO Jin, GUO Yi. Hierarchical Clustering Federated Learning Framework for Personalized Privacy-Preserving [J]. Netinfo Security, 2024, 24(8): 1196-1209. |
| [5] | CAI Manchun, XI Rongkang, ZHU Yi, ZHAO Zhongbin. A Fingerprint Identification Method of Multi-Page and Multi-Tag Targeting Tor Website [J]. Netinfo Security, 2024, 24(7): 1088-1097. |
| [6] | FU Yanming, LU Shenglin, CHEN Jiayuan, QIN Hua. Dynamic Task Allocation for Crowd Sensing Based on Deep Reinforcement Learning and Privacy Protection [J]. Netinfo Security, 2024, 24(3): 449-461. |
| [7] | XUE Mingzhu, HU Liang, WANG Ming, WANG Feng. TAP Rule Processing System Based on Federated Learning and Blockchain Technology [J]. Netinfo Security, 2024, 24(3): 473-485. |
| [8] | LIN Yihang, ZHOU Pengyuan, WU Zhiqian, LIAO Yong. Federated Learning Backdoor Defense Method Based on Trigger Inversion [J]. Netinfo Security, 2024, 24(2): 262-271. |
| [9] | JIN Zhigang, DING Yu, WU Xiaodong. Federated Intrusion Detection Algorithm with Bilateral Correction Merging Gradient Difference [J]. Netinfo Security, 2024, 24(2): 293-302. |
| [10] | HE Zeping, XU Jian, DAI Hua, YANG Geng. A Review of Federated Learning Application Technologies [J]. Netinfo Security, 2024, 24(12): 1831-1844. |
| [11] | XU Jianfeng, ZHANG Wei, TU Min, WEI Qingting, LAI Zhanqing, WANG Qianqian. A k-Anonymity Completion Method Generated Based on Semantic Fusion Trajectories [J]. Netinfo Security, 2024, 24(12): 1911-1921. |
| [12] | LAN Haoliang, WANG Qun, XU Jie, XUE Yishi, ZHANG Bo. Review of Research on Blockchain-Based Federated Learning [J]. Netinfo Security, 2024, 24(11): 1643-1654. |
| [13] | GU Haiyan, LIU Qi, MA Zhuo, ZHU Tao, QIAN Hanwei. Research on Data Noise Addition Method Based on Availability [J]. Netinfo Security, 2024, 24(11): 1731-1738. |
| [14] | SA Qirui, YOU Weijing, ZHANG Yifei, QIU Weiyang, MA Cunqing. A Survey of Ownership Protection Schemes for Federated Learning Models [J]. Netinfo Security, 2024, 24(10): 1553-1561. |
| [15] | CHEN Jing, ZHANG Jian. A Data-Free Personalized Federated Learning Algorithm Based on Knowledge Distillation [J]. Netinfo Security, 2024, 24(10): 1562-1569. |
| Viewed | ||||||
|
Full text |
|
|||||
|
Abstract |
|
|||||