| [1] |
PAKKI A, LU Kangjie. Exaggerated Error Handling Hurts! An In-Depth Study and Contextaware Detection[C]// ACM. The 2020 ACM SIGSAC Conference on Computer and Communications Security. New York: ACM, 2020: 1203-1218.
|
| [2] |
LU Kangjie, PAKKI A, WU Qiushi. Automatically Identifying Security Checks for Detecting Kernel Semantic Bugs[C]// Springer. The 24th European Symposium on Research in Computer Security, Luxembourg (Computer Security-ESORICS 2019). Heidelberg: Springer, 2019: 3-25.
|
| [3] |
LU Kangjie, PAKKI A, WU Qiushi. Detecting Missing-Check Bugs via Semantic-and Context-Aware Criticalness and Constraints Inferences[C]// USENIX. The 28th USENIX Security Symposium (USENIX Security 19). Berkely: USENIX, 2019: 1769-1786.
|
| [4] |
MITRE. CWE-754:Improper Check for Unusual or Exceptional Conditions[EB/OL]. [2025-06-10]. https://cwe.mitre.org/data/definitions/754.html.
|
| [5] |
ZHAN Dongyang, YU Xiangzhan, ZHANG Hongli, et al. ErrHunter: Detecting Error-Handling Bugs in the Linux Kernel through Systematic Static Analysis[J]. IEEE Transactions on Software Engineering, 2023, 49(2): 684-698.
doi: 10.1109/TSE.2022.3160155
URL
|
| [6] |
QASEM A, SHIRANI P, DEBBABI M, et al. Automatic Vulnerability Detection in Embedded Devices and Firmware: Survey and Layered Taxonomies[J]. ACM Computing Surveys, 2021, 54(2): 1-42.
|
| [7] |
LU Shenming, ZUO Zhiqiang, WANG Linzhang. Progress in Parallelization of Static Program Analysis[J]. Journal of Software, 2020, 31(5): 1243-1254.
|
|
陆申明, 左志强, 王林章. 静态程序分析并行化研究进展[J]. 软件学报, 2020, 31(5):1243-1254.
|
| [8] |
SONNEKALB T, HEINZE T S, MÄDER P. Deep Security Analysis of Program Code: A Systematic Literature Review[EB/OL]. (2022-01-01)[2025-06-10]. https://doi.org/10.1007/s10664-021-1002.
|
| [9] |
LIN Guanjun, WEN Sheng, HAN Qinglong, et al. Software Vulnerability Detection Using Deep Neural Networks: A Survey[J]. Proceedings of the IEEE, 2020, 108(10): 1825-1848.
doi: 10.1109/PROC.5
URL
|
| [10] |
BODDEN E. Inter-Procedural Data-Flow Analysis with IFDS/IDE and Soot[C]// ACM. The ACM SIGPLAN International Workshop on State of the Art in Java Program Analysis. New York: ACM, 2012: 3-8.
|
| [11] |
MARJAMÄKI D. Cppcheck: A Tool for Static C/C++ Code Analysis[EB/OL]. [2025-06-10]. https://cppcheck.sourceforge.io.
|
| [12] |
Checkmarx. Checkmarx[EB/OL]. [2025-06-10]. https://checkmarx.com/.
|
| [13] |
LI Zhen, ZOU Deqing, XU Shouhuai, et al. VulDeePecker: A Deep Learning-Based System for Vulnerability Detection[EB/OL]. (2018-01-05)[2025-06-10]. https://arxiv.org/abs/1801.01681.
|
| [14] |
VENKATESH G A. The Semantic Approach to Program Slicing[C]// ACM. The ACM SIGPLAN 1991 Conference on Programming Language Design and Implementation. New York: ACM, 1991: 107-119.
|
| [15] |
LI Zhen, ZOU Deqing, XU Shouhuai, et al. SySeVR: A Framework for Using Deep Learning to Detect Software Vulnerabilities[J]. IEEE Transactions on Dependable and Secure Computing, 2022, 19(4): 2244-2258.
doi: 10.1109/TDSC.2021.3051525
URL
|
| [16] |
CAO Sicong, SUN Xiaobing, BO Lili, et al. MVD: Memory-Related Vulnerability Detection Based on Flow-Sensitive Graph Neural Networks[C]// IEEE. 2022 IEEE/ACM 44th International Conference on Software Engineering(ICSE). New York: IEEE, 2022: 1456-1468.
|
| [17] |
AHMADI M, FARKHANI R M, WILLIAMS R, et al. Finding Bugs Using Your Own Code: Detecting Functionally-Similar Yet Inconsistent Code[C]// USENIX. The 30th USENIX Security Symposium (USENIX Security 21). Berkely: USENIX, 2021: 2025-2040.
|
| [18] |
ZHU Xiaogang, WEN Sheng, CAMTEPE S, et al. Fuzzing: A Survey for Roadmap[J]. ACM Computing Surveys, 2022, 54: 1-36.
|
| [19] |
LIU Peiyu, JI Shouling, ZHANG Xuhong, et al. IFIZZ: Deep-State and Efficient Fault-Scenario Generation to Test Iot Firmware[C]// IEEE. 2021 36th IEEE/ACM International Conference on Automated Software Engineering (ASE). New York: IEEE, 2021: 805-816.
|
| [20] |
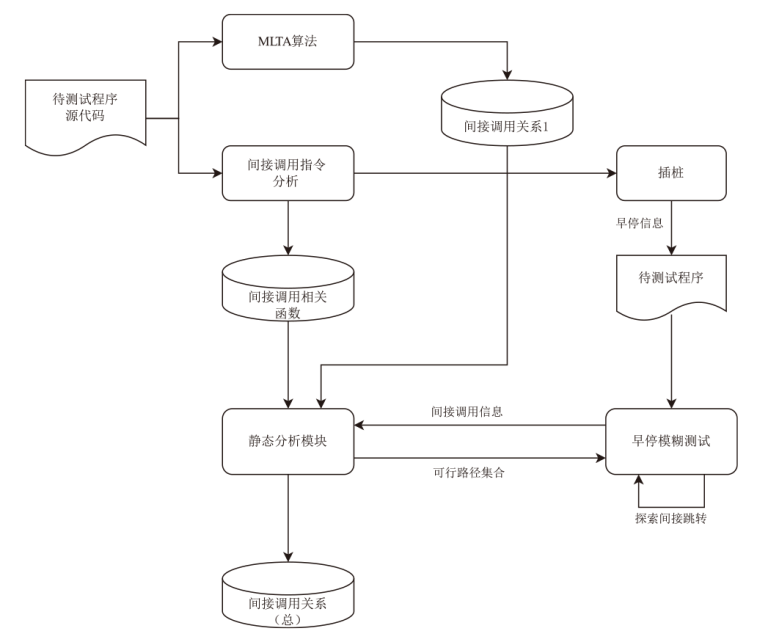
LU Kang jie, HU Hong. Where Does It Go? Refining Indirect-Call Targets with Multi-Layer Type Analysis[C]// ACM. The 2019 ACM SIGSAC Conference on Computer and Communications Security. New York: ACM, 2019: 1867-1881.
|
| [21] |
SRIVASTAVA P, NAGY S, HICKS M, et al. One Fuzz Doesn’t Fit All: Optimizing Directed Fuzzing via Target-Tailored Program State Restriction[C]// ACM. The 38th Annual Computer Security Applications Conference. New York: ACM, 2022: 388-399.
|
| [22] |
JIA Zhouyang, LI Shanshan, YU Tingting, et al. Detecting Error-Handling Bugs without Error Specification Input[C]// IEEE. 2019 34th IEEE/ACM International Conference on Automated Software Engineering (ASE). New York: IEEE, 2019: 213-225.
|
| [23] |
LI Yuwei, JI Shouling, CHEN Yuan, et al. UNIFUZZ: A Holistic and Pragmatic Metrics-Driven Platform for Evaluating Fuzzers[C]// USENIX. The 30th USENIX Security Symposium (USENIX Security 21). Berkely: USENIX, 2021: 2777-2794.
|
 )
)