Netinfo Security ›› 2026, Vol. 26 ›› Issue (2): 325-337.doi: 10.3969/j.issn.1671-1122.2026.02.012
Previous Articles Next Articles
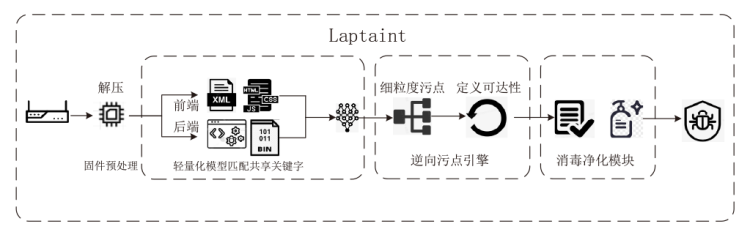
High-Confidence Vulnerability Detection in IoT Firmware Based on Taint Flow Analysis
ZHANG Guanghua1, LI Guoyu1, WANG He2, LI Heng3, WU Shaoguang1( )
)
1. School of Information Science and Engineering ,Hebei University of Science and Technology Shijiazhuang 050018, China 2. School of Cyber Engineering ,Xidian University Xi’an 710071, China 3. Hebei Cybersecurity Perception and Defense Technology Innovation Center Shijiazhuang 052161, China
-
Received:2025-06-20Online:2026-02-10Published:2026-02-23
CLC Number:
Cite this article
ZHANG Guanghua, LI Guoyu, WANG He, LI Heng, WU Shaoguang. High-Confidence Vulnerability Detection in IoT Firmware Based on Taint Flow Analysis[J]. Netinfo Security, 2026, 26(2): 325-337.
share this article
Add to citation manager EndNote|Ris|BibTeX
URL: http://netinfo-security.org/EN/10.3969/j.issn.1671-1122.2026.02.012
| 固件品牌及数量 | SaTc | Mango | Laptaint | |||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 警告 | 漏洞 | 警告 | 漏洞 | 警告 | 漏洞 | |||||||
| cmdi | bof | cmdi | bof | cmdi | bof | cmdi | bof | cmdi | bof | cmdi | bof | |
| TP-Link(8) | 0 | 2 | 0 | 1 | 11 | 55 | 5 | 35 | 7 | 40 | 5 | 32 |
| D-Link(8) | 0 | 27 | 0 | 11 | 7 | 32 | 3 | 19 | 5 | 24 | 3 | 18 |
| NetGear(7) | 12 | 144 | 8 | 45 | 73 | 694 | 36 | 348 | 47 | 394 | 35 | 327 |
| Tenda(7) | 6 | 117 | 5 | 71 | 78 | 56 | 50 | 25 | 52 | 32 | 48 | 25 |
| 总计 | 18 | 290 | 13 | 128 | 169 | 837 | 94 | 427 | 111 | 490 | 91 | 402 |
| 固件品牌及数量 | SaTc | Mango | Laptaint | |||
|---|---|---|---|---|---|---|
| 时间 | 时间 | 时间 | ||||
| cmdi | bof | cmdi | bof | cmdi | bof | |
| TP-Link(8) | 12h28min | 16h49min | 19h40min | 21h12min | 24h10min | 22h31min |
| D-Link(8) | 67h14min | 71h32min | 12h7min | 29h40min | 11h57min | 31h49min |
| NetGear(7) | 58h28min | 84h9min | 27h19min | 35h6min | 27h49min | 32h22min |
| Tenda(7) | 37h30min | 61h38min | 18h12min | 24h23min | 15h30min | 25h22min |
| 总计 | 175h40min | 234h8min | 77h18min | 110h21min | 79h26min | 112h4min |
| 固件 | |||||
|---|---|---|---|---|---|
| DIR-842.fw.revA.1-02.eu.multi.0151008 | 231 | 342 | 423 | 83.12% | 23.68% |
| DIR-868L.w.evA.1-12.eu.multi.20170316 | 254 | 412 | 464 | 82.68% | 12.62% |
| DIR-880L.A1.FW107WWb08 | 179 | 263 | 321 | 79.33% | 22.05% |
| XR500-V2.1.0.4 | 456 | 542 | 545 | 19.52% | 0.55% |
| R6400v2-V1.0.4.84.10.0.58 | 573 | 453 | 625 | 9.08% | 37.97% |
| R7000-V1.0.11.100.10.2.100 | 542 | 582 | 591 | 9.04% | 1.55% |
| US.AC6V1.0BR.V15.03.05.16.multi.TD01 | 274 | 321 | 519 | 89.42% | 61.68% |
| US.AC9V1.0B.V15.03.05.14.multi.TD01 | 312 | 521 | 642 | 105.77% | 23.22% |
| US.AC15V1.0BR.V15.03.05.19.multi.TD01 | 317 | 475 | 719 | 126.81% | 51.37% |
| wa830nv2.en.3.14.8.up.boot | 211 | 264 | 428 | 102.84% | 62.12% |
| wr1043ndv3.en.3.16.9.up.boot | 97 | 153 | 188 | 93.81% | 22.88% |
| TD-W9970v1.0.9.1.2.5.up.boot.2015-08-31.17.13.22 | 102 | 243 | 256 | 150.98% | 5.34% |
| 平均 | 296 | 381 | 477 | 61.25% | 25.16% |
| 路由器品牌及数量 | 正向分析 | 逆向分析 | 提升效率 | ||
|---|---|---|---|---|---|
| 时间 | 时间 | ||||
| cmdi | bof | cmdi | bof | ||
| TP-Link(8) | 31h26min | 30h42min | 24h10min | 22h31min | 33.15% |
| D-Link(8) | 12h53min | 32h34min | 11h57min | 31h49min | 3.65% |
| NetGear(7) | 42h19min | 53h21min | 27h49min | 32h22min | 58.95% |
| Tenda(7) | 19h49min | 34h14min | 15h30min | 25h22min | 32.25% |
| 总计 | 106h27min | 150h51min | 79h26min | 112h4min | 34.36% |
| [1] | LIU Lingxiang, PAN Zulie, LI Yang, et al. A Static Localization Method for Firmware Vulnerabilities Based on Front-End and Back-End Correlation Analysis[J]. Netinfo Security, 2022, 22(8): 44-54. |
| 刘翎翔, 潘祖烈, 李阳, 等. 基于前后端关联性分析的固件漏洞静态定位方法[J]. 信息网络安全, 2022, 22(8):44-54. | |
| [2] | VAILSHERY L S. Topic: Internet of Things (IoT)[EB/OL]. (2024-06-11)[2025-05-13]. https://www.statista.com/topics/2637/internet-of-things/. |
| [3] |
ZHANG Guanghua, CHEN Fang, CHANG Jiyou, et al. Accelerating Firmware Vulnerability Discovery via Precise Intermediate Taint Source and Dangerous Function Localization[J]. Computer Science, 2025, 52(7): 1-12.
doi: 10.1063/1.31803 URL |
| 张光华, 陈放, 常继友, 等. 利用精确中间污点源和危险函数定位加速固件漏洞挖掘[J]. 计算机科学, 2025, 52(7):1-12. | |
| [4] | THREAT I T. 150000 Verkada Security Cameras Hacked—to Make a Point[EB/OL]. (2021-03-12)[2025-05-14]. https://www.threatdown.com/blog/150000-verkada-security-cameras-hacked-to-make-a-point/. |
| [5] | ANTONAKAKIS M, APRIL T, BAILEY M, et al. Understanding the Mirai Botnet[C]// USENIX. The 26th USENIX Conference on Security Symposium. Berkeley: USENIX, 2017: 1093-1110. |
| [6] | LANGNER R. Stuxnet: Dissecting a Cyberwarfare Weapon[J]. IEEE Security & Privacy, 2011, 9(3): 49-51. |
| [7] | WANG Ningchao, CHEN Zuoning, GAN Shuitao, et al. Research on the Technologies of Security Analysis Technologies on the Embedded Device Firmware[EB/OL]. (2023-02-22)[2025-05-14]. https://jglobal.jst.go.jp/en/detail?JGLOBAL_ID=202102221104018110. |
| [8] | CHEN Libo, WANG Yanhao, CAI Quanpu, et al. Sharing More and Checking Less: Leveraging Common Input Keywords to Detect Bugs in Embedded Systems[C]// USENIX. The 30th USENIX Security Symposium. Berkeley: USENIX, 2021: 303-319. |
| [9] | SRIVASTAVA P, PENG Hui, LI Jiahao, et al. FirmFuzz: Automated IoT Firmware Introspection and Analysis[C]// ACM. The 2nd International ACM Workshop on Security and Privacy for the Internet-of-Things. New York: ACM, 2019: 15-21. |
| [10] | GUO Jundong. Research on Automated Vulnerability Discovery Technology for Routers Based on Static Analysis[D]. Beijing: Beijing Jiaotong University, 2024. |
| 郭俊东. 基于静态分析的路由器自动化漏洞挖掘技术研究[D]. 北京: 北京交通大学, 2024. | |
| [11] | ZHANG Guanghua, CHANG Jiyou, CHEN Fang, et al. Firmware Simulation Scheme of IoT Devices Based on Dynamic Substitution of Library Functions[J]. Netinfo Security, 2025, 25(7): 1053-1062. |
| 张光华, 常继友, 陈放, 等. 基于库函数动态替换的物联网设备固件仿真方案[J]. 信息网络安全, 2025, 25(7):1053-1062. | |
| [12] | SHOSHITAISHVILI Y, WANG Ruoyu, SALLS C, et al. (State of ) The Art of War: Offensive Techniques in Binary Analysis[C]// IEEE. 2016 IEEE Symposium on Security and Privacy. New York: IEEE, 2016: 138-157. |
| [13] | ZADDACH J, BRUNO L, BALZAROTTI D, et al. Avatar: A Framework to Support Dynamic Security Analysis of Embedded Systems’ Firmwares[C]// NDSS. Network and Distributed System Security (NDSS) Symposium. San Diego: NDSS, 2014: 157-173. |
| [14] | CHEN Jiongyi, DIAO Wenrui, ZHAO Qingchuan, et al. IoTFuzzer: Discovering Memory Corruptions in IoT Through App-Based Fuzzing[C]// NDSS. Network and Distributed System Security Symposium 2018. San Diego: NDSS, 2018: 187-202. |
| [15] | WEI Zhou, ZHANG Lan, LE Guan, et al. What Your Firmware Tells You is not How You Should Emulate It: A Specification-Guided Approach for Firmware Emulation[C]// ACM. The 2022 ACM SIGSAC Conference on Computer and Communications Security. New York: ACM, 2022: 3269-3283. |
| [16] | ZHENG Yaowen, DAVANIAN A, ZHU Hongsong, et al. FIRM-AFL: High-Throughput Greybox Fuzzing of IoT Firmware via Augmented Process Emulation[C]// USENIX. The 28th USENIX Conference on Security Symposium (SEC’19). Berkeley: USENIX, 2019: 1099-1114. |
| [17] | SHE Dongdong, CHEN Yizheng, ABHISHEK S, et al. Neutaint: Efficient Dynamic Taint Analysis with Neural Networks[C]// IEEE. The 41th IEEE Symposium on Security and Privacy. New York: IEEE, 2020: 1527-1543. |
| [18] | QIAN Sang, WANG Yanhao, LIU Yuwei, et al. AirTaint: Making Dynamic Taint Analysis Faster and Easier[C]// IEEE. 2024 IEEE Symposium on Security and Privacy (SP). New York: IEEE, 2024: 3998-4014. |
| [19] | ZHU Yuming, DONG Weiyu. nnTaint: An Optimized Dynamic Taint Analysis Method Based on Neural Network[C]// IEEE. 2022 IEEE 10th International Conference on Information, Communication and Networks (ICICN). New York: IEEE, 2022: 63-70. |
| [20] | KIM M, KIM D, KIM E, et al. FirmAE: Towards Large-Scale Emulation of IoT Firmware for Dynamic Analysis[C]// ACM. The 36th Annual Computer Security Applications Conference. New York: ACM, 2020: 733-745. |
| [21] | GAO Zicong, ZHANG Chao, LIU Hangtian, et al. Faster and Better: Detecting Vulnerabilities in Linux-Based IoT Firmware with Optimized Reaching Definition Analysis[C]// NDSS. Network and Distributed System Security Symposium 2024. San Diego: NDSS, 2024: 564-571. |
| [22] | REDINI N, MACHIRY A, WANG Ruoyu, et al. Karonte: Detecting Insecure Multi-Binary Interactions in Embedded Firmware[C]// IEEE. 2020 IEEE Symposium on Security and Privacy (SP). New York: IEEE, 2020: 1544-1561. |
| [23] | GIBBS W, RAJ A S, VADAYATH J M, et al. Operation Mango: Scalable Discovery of Taint-Style Vulnerabilities in Binary Firmware Services[C]// USENIX. The 33rd USENIX Conference on Security Symposium. Berkeley: USENIX, 2024: 7123-7139. |
| [24] | CHENG Kai, ZHENG Yangwen, LIU Tao, et al. Detecting Vulnerabilities in Linux-Based Embedded Firmware with SSE-Based on-Demand Alias Analysis[C]// ACM. The 32nd ACM SIGSOFT International Symposium on Software Testing and Analysis. New York: ACM, 2023: 360-372. |
| [25] | LIU Puzhuo, ZHENG Yaowen, SUN Chengnian, et al. FITS: Inferring Intermediate Taint Sources for Effective Vulnerability Analysis of IoT Device Firmware[C]// ACM. The 28th ACM International Conference on Architectural Support for Programming Languages and Operating Systems. New York: ACM, 2024: 138-152. |
| [26] | CHENG Kai, LI Qiang, WANG Lei, et al. DTaint: Detecting the Taint-Style Vulnerability in Embedded Device Firmware[C]// IEEE. 2018 48th Annual IEEE/IFIP International Conference on Dependable Systems and Networks (DSN). New York: IEEE, 2018: 430-441. |
| [27] | EACMEN P. ReFirmLabs/Binwalk: Firmware Analysis Tool[EB/OL]. [2025-05-17]. https://github.com/ReFirmLabs/binwalk. |
| [1] | TAO Ci, CHEN Haoran, CHEN Ping. A Directed Fuzz Testing Method for C Language Exception Handling Paths in Industrial Control Systems [J]. Netinfo Security, 2026, 26(2): 211-223. |
| [2] | XU Pu, SUN Xinyi, ZHU Yonggen. A Method for Detecting Java Injection Vulnerabilities Based on Interprocedure Constant String Analysis [J]. Netinfo Security, 2026, 26(2): 304-314. |
| [3] | WANG Lei, CHEN Jiongyi, WANG Jian, FENG Yuan. Intelligent Reverse Analysis Method of Firmware Program Interaction Relationships Based on Taint Analysis and Textual Semantics [J]. Netinfo Security, 2025, 25(9): 1385-1396. |
| [4] | ZHANG Xuewang, LU Hui, XIE Haofei. A Data Augmentation Method Based on Graph Node Centrality and Large Model for Vulnerability Detection [J]. Netinfo Security, 2025, 25(4): 550-563. |
| [5] | CHANG Zhenxuan, ZHENG Zhihan, MEI Aohan, TAN Yu’an. An Efficient Gray-Box Fuzzing Approach for Firmware Network Applications [J]. Netinfo Security, 2025, 25(4): 654-663. |
| [6] | ZHANG Yuxuan, HUANG Cheng, LIU Rong, LENG Tao. Smart Contract Vulnerability Detection Method Combining Prompt Tuning [J]. Netinfo Security, 2025, 25(4): 664-673. |
| [7] | MENG Hui, MAO Linlin, PENG Juzhi. Sanitize Processing and Recognition Method Driven by Large Language Model [J]. Netinfo Security, 2025, 25(12): 1990-1998. |
| [8] | WANG Juan, ZHANG Boxian, ZHANG Zhijie, XIE Haining, FU Jintao, WANG Yang. Java Deserialization Vulnerability Mining Based on Fuzzing [J]. Netinfo Security, 2025, 25(1): 1-12. |
| [9] | LI Pengchao, ZHANG Quantao, HU Yuan. Smart Contract Vulnerability Detection Method Based on Graph Convolutional Network with Dual Attention Mechanism [J]. Netinfo Security, 2024, 24(11): 1624-1631. |
| [10] | ZHANG Guanghua, LIU Yongsheng, WANG He, YU Naiwen. Smart Contract Vulnerability Detection Scheme Based on BiLSTM and Attention Mechanism [J]. Netinfo Security, 2022, 22(9): 46-54. |
| [11] | ZHAO Zhiyan, JI Xiaomo. Research on the Intelligent Fusion Model of Network Security Situation Awareness [J]. Netinfo Security, 2020, 20(4): 87-93. |
| [12] | Weiping WEN, Jingwei LI, Yingnan JIAO, Hailin LI. A Vulnerability Detection Method Based on Random Detection Algorithm and Information Aggregation [J]. Netinfo Security, 2019, 19(1): 1-7. |
| [13] | Jian ZHAO, Rui WANG, Siqi LI. Research on Smart Home Vulnerability Mining Technology Based on Taint Analysis [J]. Netinfo Security, 2018, 18(6): 36-44. |
| [14] | Xiaowen DA, Limin MAO, Mingjie WU, Min GUO. Research on a Vulnerability Location Technology Based on Patch Matching and Static Taint Analysis [J]. Netinfo Security, 2017, 17(9): 5-5. |
| [15] | Xiajing WANG, Changzhen HU, Rui MA, Xinzhu GAO. A Survey of the Key Technology of Binary Program Vulnerability Discovery [J]. Netinfo Security, 2017, 17(8): 1-13. |
| Viewed | ||||||
|
Full text |
|
|||||
|
Abstract |
|
|||||