Netinfo Security ›› 2025, Vol. 25 ›› Issue (3): 451-466.doi: 10.3969/j.issn.1671-1122.2025.03.008
Previous Articles Next Articles
Construction Method of Cybersecurity Knowledge Graph Based on Ontology
XU Zhishuang1, ZHANG Kun2, FAN Junchao1, CHANG Xiaolin1( )
)
- 1. School of Cyberspace Science and Technology, Beijing Jiaotong University, Beijing 100044, China
2. State Information Center, Beijing 100045, China
-
Received:2024-12-30Online:2025-03-10Published:2025-03-26 -
Contact:CHANG Xiaolin E-mail:xlchang@bjtu.edu.cn
CLC Number:
Cite this article
XU Zhishuang, ZHANG Kun, FAN Junchao, CHANG Xiaolin. Construction Method of Cybersecurity Knowledge Graph Based on Ontology[J]. Netinfo Security, 2025, 25(3): 451-466.
share this article
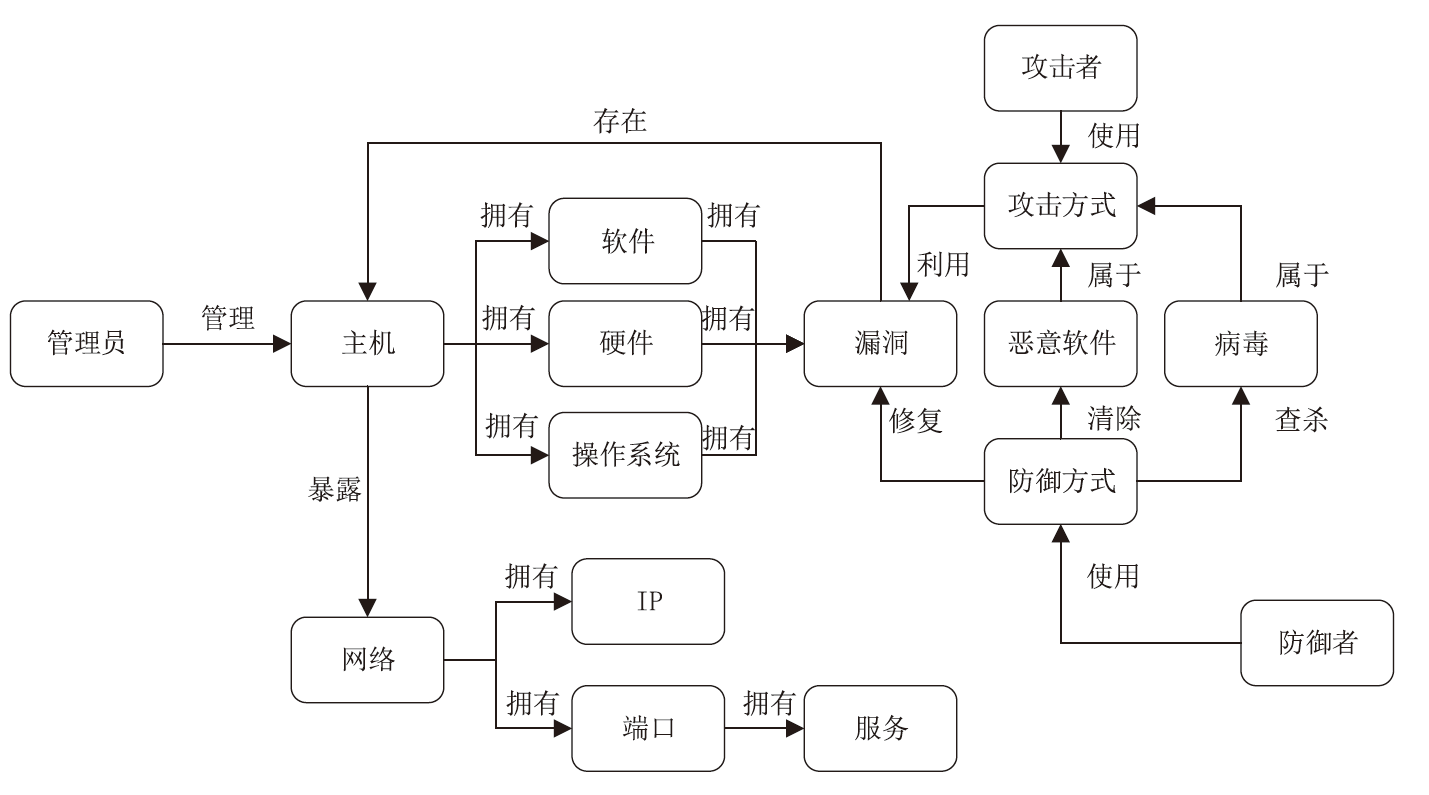
| 符号 | 含义 | 符号 | 含义 |
|---|---|---|---|
| B-administrator | 管理员实体的开始部分 | I-network | 网络实体的其余部分 |
| I-administrator | 管理员实体的其余部分 | B-attacker | 攻击者实体的开始部分 |
| B-host | 主机实体的开始 部分 | I-attacker | 攻击者实体的其余部分 |
| I-host | 主机实体的其余 部分 | B-attack_mode | 攻击方式实体的开始 部分 |
| B-system | 操作系统实体的 开始部分 | I-attack_mode | 攻击方式实体的其余 部分 |
| I-system | 操作系统实体的 其余部分 | B-loophole | 漏洞实体的开始部分 |
| B-hardware | 硬件实体的开始 部分 | I-loophole | 漏洞实体的其余部分 |
| I-hardware | 硬件实体的其余 部分 | B-malware | 恶意软件实体的开始 部分 |
| B-software | 软件实体的开始 部分 | I-malware | 恶意软件实体的其余 部分 |
| I-software | 软件实体的其余 部分 | B-virus | 病毒实体的开始部分 |
| B-ip | IP实体的开始部分 | I-virus | 病毒实体的其余部分 |
| I-ip | IP实体的其余部分 | B-defender | 防御者实体的开始部分 |
| B-port | 端口实体的开始 部分 | I-defender | 防御者实体的其余部分 |
| I-port | 端口实体的其余 部分 | B-defense_mode | 防御方式实体的开始 部分 |
| B-service | 服务实体的开始 部分 | I-defense_mode | 防御方式实体的其余 部分 |
| I-service | 服务实体的其余 部分 | O | 非实体 |
| B-network | 网络实体的开始 部分 | — | — |
| [1] | REN Yitong, XIAO Yanjun, ZHOU Yinghai, et al. CSKG4APT: A Cybersecurity Knowledge Graph for Advanced Persistent Threat Organization Attribution[J]. IEEE Transactions on Knowledge and Data Engineering, 2022, 35(6): 5695-5709. |
| [2] | JIANG Yuning, JEUSFELD M A, DING Jianguo, et al. Model-Based Cybersecurity Analysis: Extending Enterprise Modeling to Critical Infrastructure Cybersecurity[J]. Business & Information Systems Engineering, 2023, 65(6): 643-676. |
| [3] | SIKOS L F. Cybersecurity Knowledge Graphs[J]. Knowledge and Information Systems, 2023, 65(9): 3511-3531. |
| [4] | LIU Kai, WANG Fei, DING Zhaoyun, et al. Recent Progress of Using Knowledge Graph for Cybersecurity[J]. Electronics, 2022, 11(15): 2287-2314. |
| [5] | WANG Gaosheng, LIU Peipei, HUANG Jintao, et al. KnowCTI: Knowledge-Based Cyber Threat Intelligence Entity and Relation Extraction[J]. Computers & Security, 2024, 141(6): 1-12. |
| [6] | WANG Xiaodi, HUANG Cheng, LIU Jiayong. Research Overview on Knowledge Graphs for Open Source Intelligence in Cybersecurity[J]. Netinfo Security, 2023, 23(6): 11-21. |
| 王晓狄, 黄诚, 刘嘉勇. 面向网络安全开源情报的知识图谱研究综述[J]. 信息网络安全, 2023, 23(6):11-21. | |
| [7] | LI Hongyi, ZE Shi, PAN Chengwei, et al. Cybersecurity Knowledge Graphs Construction and Quality Assessment[J]. Complex & Intelligent Systems, 2024, 10(1): 5-16. |
| [8] | CHEN Jiarui, LU Yiqin, ZHANG Yang, et al. A Management Knowledge Graph Approach for Critical Infrastructure Protection: Ontology Design, Information Extraction and Relation Prediction[J]. International Journal of Critical Infrastructure Protection, 2023, 43(4): 3-7. |
| [9] | PREUVENEERS D, JOOSEN W. An Ontology-Based Cybersecurity Framework for AI-Enabled Systems and Applications[J]. Future Internet, 2024, 16(3): 4-18. |
| [10] | GRANDIN A. An Ontology of Cyberspace as a Basis for Decision-Making in Cyberoperations[C]// IEEE. International Conference on Cyber Warface and Security. New York: IEEE, 2024: 84-94. |
| [11] | BUGHIO K S, COOK D M, SHAH S A A. Developing a Novel Ontology for Cybersecurity in Internet of Medical Things-Enabled Remote Patient Monitoring[J]. Sensors, 2024, 24(9): 5-20. |
| [12] | BERNARDINI A, D’ALTERIO F, SAGRATELLA L, et al. “Work-in-Progress” Structuring the Complexity: an Ontological Approach to Analyze the Cybersecurity of a 5G Service[C]// IEEE. 2024 IEEE European Symposium on Security and Privacy Workshops (EuroS&PW). New York: IEEE, 2024: 691-700. |
| [13] | KOUGIOUMTZIDOU A, PAPOUTSIS A, KAVALLIEROS D, et al. An End-to-End Framework for Cybersecurity Taxonomy and Ontology Generation and Updating[C]// IEEE. 2024 IEEE International Conference on Cyber Security and Resilience (CSR). New York: IEEE, 2024: 247-254. |
| [14] | XU Derong, CHEN Wei, PENG Wenjun, et al. Large Language Models for Generative Information Extraction: A Survey[J]. Frontiers of Computer Science, 2024, 18(6): 2-14. |
| [15] | WANG Yaxin, ZHANG Jian. Electronic Medical Record Fingerprint Feature Extraction Based on Few-Shot Named Entity Recognition Technology[J]. Netinfo Security, 2024, 24(10): 1537-1543. |
| 王亚欣, 张健. 基于少样本命名实体识别技术的电子病历指纹特征提取[J]. 信息网络安全, 2024, 24(10):1537-1543. | |
| [16] | STUDIAWAN H, HASAN M F, PRATOMO B A. Rule-Based Entity Recognition for Forensic Timeline[C]// IEEE. 2023 Conference on Information Communications Technology and Society (ICTAS). New York: IEEE, 2023: 1-6. |
| [17] | HU Chenxi, WU Tao, LIU Chunsheng, et al. Joint Contrastive Learning and Belief Rule Base for Named Entity Recognition in Cybersecurity[J]. Cybersecurity, 2024, 7(1): 3-12. |
| [18] | SARHAN M, LAYEGHY S, MOUSTAFA N, et al. Feature Extraction for Machine Learning-Based Intrusion Detection in IoT Networks[J]. Digital Communications and Networks, 2024, 10(1): 205-216. |
| [19] | MUMTAZ G, AKRAM S, IQBAL M W, et al. Classification and Prediction of Significant Cyber Incidents (SCI) Using Data Mining and Machine Learning (DM-ML)[J]. IEEE Access, 2023, 11: 94486-94496. |
| [20] | LI Jiao, ZHANG Yuqing, WU Yabiao. Large Language Model Data Augmentation Methods for Relationship Extraction in Cybersecurity[J]. Netinfo Security, 2024, 24(10): 1477-1483. |
| 李娇, 张玉清, 吴亚飚. 面向网络安全关系抽取的大语言模型数据增强方法[J]. 信息网络安全, 2024, 24(10):1477-1483. | |
| [21] | WANG Fei, DING Zhaoyun, LIU Kai, et al. Multi-Relation Extraction for Cybersecurity Based on Ontology Rule-Enhanced Prompt Learning[J]. Electronics, 2024, 13(12): 1-25. |
| [22] | AHMED K, KHURSHID S K, HINA S. CyberEntRel: Joint Extraction of Cyber Entities and Relations Using Deep Learning[J]. Computer & Security, 2024, 136(1): 1-11. |
| [23] | JI Bin, LI Shasha, XU Hao, et al. Span-Based Joint Entity and Relation Extraction Augmented with Sequence Tagging Mechanism[J]. Science China Information Sciences, 2024, 67(5): 1-15. |
| [24] | CHEN S S, HWANG R H, SUN C Y, et al. Enhancing Cyber Threat Intelligence with Named Entity Recognition Using BERT-CRF[C]// IEEE. IEEE Global Communiacations Conference 2023. New York: IEEE, 2023: 7532-7537. |
| [25] | LIU Yafei, WEI Siqi, HUANG Haijun, et al. Naming Entity Recognition of Citrus Pests and Diseases Based on the BERT-BiLSTM-CRF Model[J]. Expert Systems with Applications, 2023, 234(27): 1-10. |
| [26] | PAN Xuefeng, CAO Yuanyuan, HOU Xiaorui, et al. Named Entity Recognition of TCM Electronic Medical Records Based on the ALBERT-BiLSTM-CRF Model[C]// IEEE. 2022 12th International Conference on Information Technology in Medicine and Education (ITME 2022). New York: IEEE, 2022: 575-582. |
| [27] | KE Jia, WANG Weiji, CHEN Xiaojun, et al. Medical Entity Recognition and Knowledge Map Relationship Analysis of Chinese EMRs Based on Improved BiLSTM-CRF[J]. Computers and Electrical Engineering, 2023, 108(4): 1-18. |
| [28] | 360 Total Security. Security Report[EB/OL]. (2024-05-09) [2024-11-14]. https://cert.360.cn/report. |
| 360安全安全报告[EB/OL]. (2024-05-09) [2024-11-14]. https://cert.360.cn/report. | |
| [29] | National Computer Network Emergency Response Technical Team/Coordination Center of China. Security Report[EB/OL]. (2023-06-28) [2024-11-20]. https://www.cert.org.cn/publish/main/17/index.html. |
| 国家计算机网络应急技术处理协调中心. 安全报告[EB/OL]. (2023-06-28)[2024-11-20]. https://www.cert.org.cn/publish/main/17/index.html. | |
| [30] | KAUR K, KAUR P. BERT-CNN: Improving BERT for Requirements Classification Using CNN[J]. Procedia Computer Science, 2023, 218(3): 2604-2611. |
| [31] | BELLO A, NG S C, LEUNG M F. A BERT Framework to Sentiment Analysis of Tweets[J]. Sensors, 2023, 23(1): 1-14. |
| [1] | GAO Hancheng, HUANG Haiping. A Novel Distributed Large-Scale Traffic Cleaning Scheme against DDoS Attacks [J]. Netinfo Security, 2025, 25(1): 78-87. |
| [2] | ZHANG Changlin, TONG Xin, TONG Hui, YANG Ying. A Survey of Large Language Models in the Domain of Cybersecurity [J]. Netinfo Security, 2024, 24(5): 778-793. |
| [3] | QIN Zhenkai, XU Mingchao, JIANG Ping. Research on the Construction Method and Application of Case Knowledge Graph Based on Prompt Learning [J]. Netinfo Security, 2024, 24(11): 1773-1782. |
| [4] | PU Junyan, LI Yahui, ZHOU Chunjie. Cross-Domain Dynamic Security Risk Analysis Method of Industrial Control System Based on Probabilistic Attack Graph [J]. Netinfo Security, 2023, 23(9): 85-94. |
| [5] | SUN Chengcheng. Research on Countermeasures for Network Security Governance [J]. Netinfo Security, 2023, 23(6): 104-110. |
| [6] | WANG Xiaodi, HUANG Cheng, LIU Jiayong. A Survey of Cyber Security Open-Source Intelligence Knowledge Graph [J]. Netinfo Security, 2023, 23(6): 11-21. |
| [7] | JIN Shuting, HE Jingsha, ZHU Nafei, PAN Shijia. Research on Privacy Protection Access Control Mechanism Based on Ontology Reasoning [J]. Netinfo Security, 2021, 21(8): 52-61. |
| [8] | ZHU Chaoyang, ZHOU Liang, ZHU Yayun, LIN Qingwen. Malicious Code Visual Classification Algorithm Based on Behavior Knowledge Graph Sieve [J]. Netinfo Security, 2021, 21(10): 54-62. |
| [9] | BI Qinbo, ZHAO Chengdong. Research and Application of 5G Cybersecurity Threat Modeling Based on STRIDE-LM [J]. Netinfo Security, 2020, 20(9): 72-76. |
| [10] | LIU Hong, XIE Yongheng, WANG Guowei, JIANG Shuai. Ontology-based Cross-domain Security Analysis [J]. Netinfo Security, 2020, 20(9): 82-86. |
| [11] | LI Shuilin, ZHU Guobang, FAN Chunling, CHEN Guangyong. Research on a New Scoring Algorithm of Testing and Evaluation for Classified Cybersecurity Protection [J]. Netinfo Security, 2020, 20(2): 1-6. |
| [12] | FAN Bo, GONG Gangjun, SUN Shuxian. Research on Dynamic Security System of Distribution IoT Based on Classified Protection of Cybersecurity 2.0 [J]. Netinfo Security, 2020, 20(11): 10-14. |
| [13] | TAO Yuan, HUANG Tao, LI Moyan, HU Wei. Research on Log Audit Analysis Model of Cyberspace Security Classified Protection Driven by Knowledge Map [J]. Netinfo Security, 2020, 20(1): 46-51. |
| [14] | Mengru GAO, Fangjun XIE, Hongqin DONG, Xiang LIN. Research on Network Security Evaluation System Oriented to Critical Information Infrastructure [J]. Netinfo Security, 2019, 19(9): 111-114. |
| [15] | Zhenfeng ZHANG, Zhiwen ZHANG, Ruichao WANG. Model of Cloud Computing Security and Compliance Capability for Classified Protection of Cybersecurity 2.0 [J]. Netinfo Security, 2019, 19(11): 1-7. |
| Viewed | ||||||
|
Full text |
|
|||||
|
Abstract |
|
|||||