信息网络安全 ›› 2026, Vol. 26 ›› Issue (4): 642-653.doi: 10.3969/j.issn.1671-1122.2026.04.011
基于多特征感知和注意力机制的深度伪造图像检测研究
甘肃政法大学网络空间安全学院 兰州 730070
-
收稿日期:2026-01-07出版日期:2026-04-10发布日期:2026-04-29 -
通讯作者:袁小刚 E-mail:yxg7349@gsupl.edu.cn -
作者简介:袁小刚(1980—),男,江苏,教授,博士,CCF会员,主要研究方向为网络安全、信息内容安全和密码技术|裴桓(2001—),女,甘肃,硕士研究生,主要研究方向为计算机视觉|安德智(1973—),男,浙江,教授,本科,CCF会员,主要研究方向为网络安全和信息内容安全|万建鑫(2001—),男,河南,硕士研究生,主要研究方向为网络安全 -
基金资助:国家自然科学基金(62562005);甘肃省高校教师创新基金(2025A-124);兰州市科技计划(2023-1-53)
Research on Deepfake Image Detection Based on Multi-Feature Perception and Attention Mechanism
YUAN Xiaogang( ), PEI Huan, AN Dezhi, WAN Jianxin
), PEI Huan, AN Dezhi, WAN Jianxin
School of Cyberspace Security ,Gansu University of Political Science and Law Lanzhou 730070, China
-
Received:2026-01-07Online:2026-04-10Published:2026-04-29
摘要:
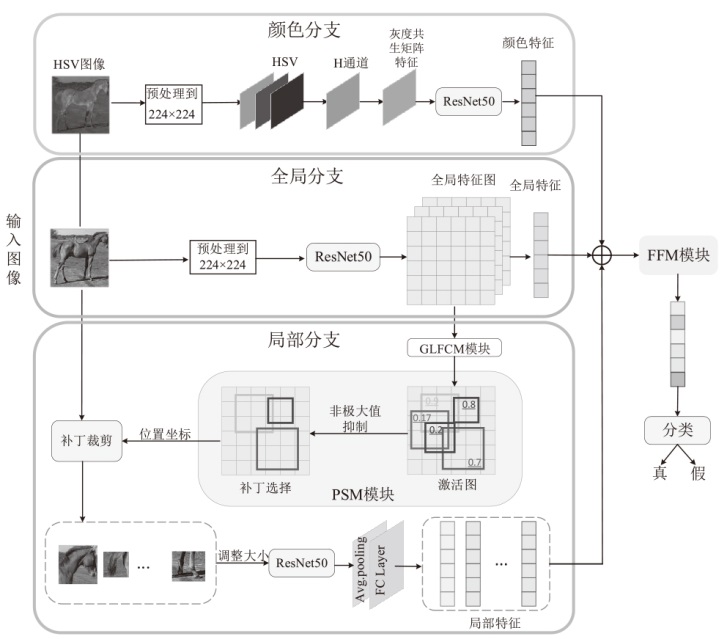
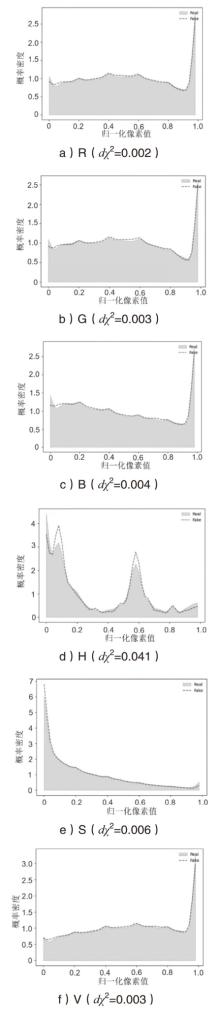
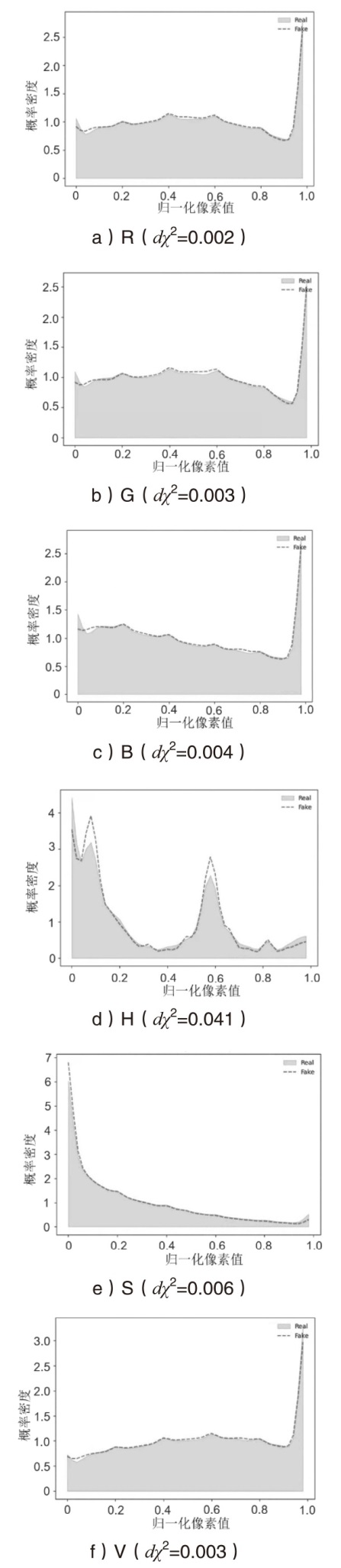
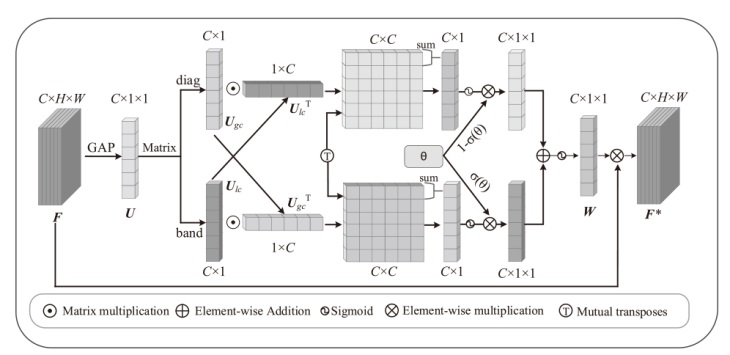
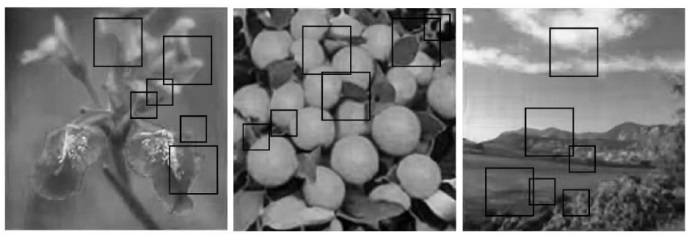
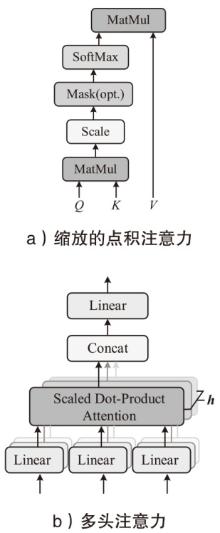
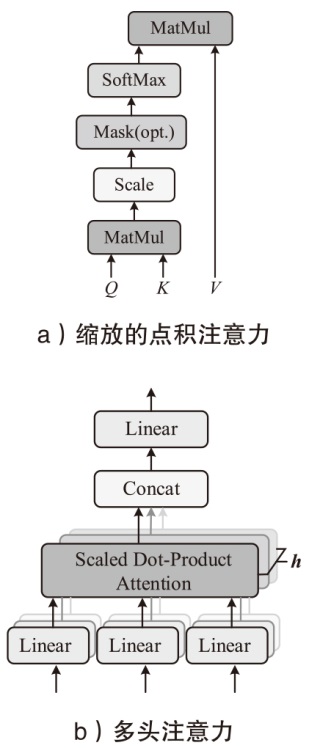
随着生成对抗网络(GAN)和扩散技术的不断进步,生成的图像在视觉质量上已经达到一个较高水平,与真实图像几乎难以分辨,这对个人隐私和社会安全均构成潜在威胁。为应对这一挑战,文章提出一种多特征融合的深度伪造图像检测模型,该模型结合全局、局部和颜色特征,以全面捕捉生成图像中的伪造痕迹,进而准确识别图像真伪。全局分支聚焦提取整个图像的全局空间信息,局部分支通过细粒度选择模块关注关键区域的局部特征,而颜色分支则增强了对不同颜色空间中伪造特征的适应性。将这些特征通过注意力机制进行融合,全面提升对深度伪造图像伪造痕迹的捕捉能力。通过在14个GAN和5个扩散模型数据集上的实验,验证了该方法对不同生成模型均具有较高的检测准确性和泛化能力,为深度伪造图像的检测提供了一种高效且可靠的解决方案。
中图分类号:
引用本文
袁小刚, 裴桓, 安德智, 万建鑫. 基于多特征感知和注意力机制的深度伪造图像检测研究[J]. 信息网络安全, 2026, 26(4): 642-653.
YUAN Xiaogang, PEI Huan, AN Dezhi, WAN Jianxin. Research on Deepfake Image Detection Based on Multi-Feature Perception and Attention Mechanism[J]. Netinfo Security, 2026, 26(4): 642-653.
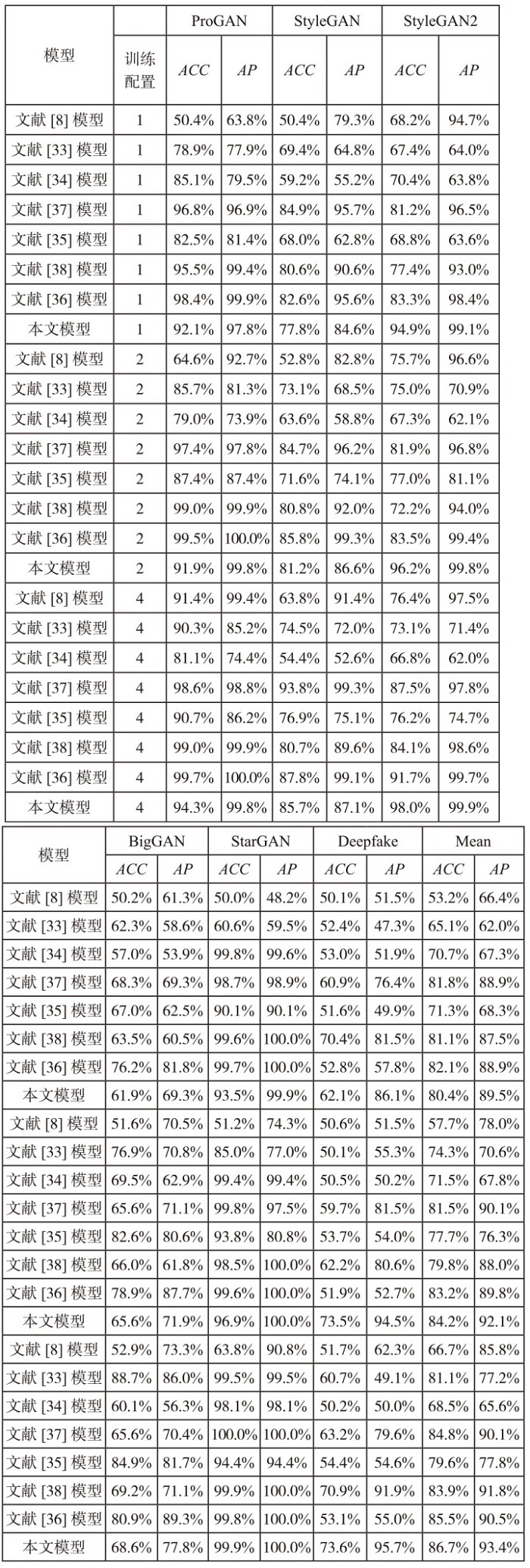
表1
跨类别测试
| 模型 | 分类器 | 同类测试 | 跨类测试 | 全类测试 | |||
|---|---|---|---|---|---|---|---|
| ACC | AP | ACC | AP | ACC | AP | ||
| 基于像素方法 | ResNet-50 | 72.4% | 68.7% | 61.9% | 58.6% | 64.5% | 61.1% |
| 文献[ | ResNet-50 | 50.5% | 66.6% | 50.0% | 58.3% | 50.2% | 60.4% |
| 文献[ | ResNet-50 | 93.3% | 89.7% | 73.5% | 68.1% | 78.4% | 73.5% |
| 文献[ | SVM(rbf) | 88.3% | 83.0% | 62.0% | 59.2% | 68.5% | 65.1% |
| 文献[ | SVM(poly) | 88.8% | 83.9% | 62.0% | 59.1% | 68.7% | 65.3% |
| 文献[ | SVM(linear) | 81.1% | 74.1% | 60.2% | 57.0% | 65.4% | 61.3% |
| 文献[ | Linear Reg. | 79.9% | 73.2% | 60.5% | 57.0% | 65.3% | 61.1% |
| 文献[ | ResNet-50 | 94.8% | 93.5% | 73.4% | 69.0% | 78.7% | 75.2% |
| 文献[ | Attention | 95.0% | 94.1% | 77.0% | 68.3% | 80.0% | 79.0% |
| 本文模型 | Attention | 98.5% | 99.1% | 81.9% | 98.6% | 92.6% | 98.7% |
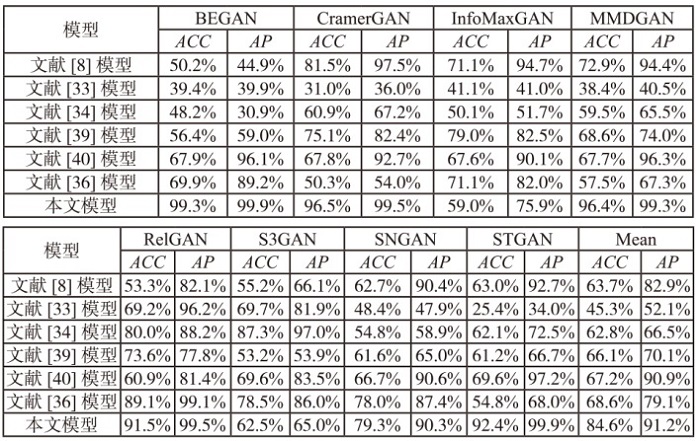
表4
TAN数据集上的跨模型性能
| 模型 | IDDPM | ADM | DDPM | Midjourney | DALLE | Mean | ||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|
| ACC | AP | ACC | AP | ACC | AP | ACC | AP | ACC | AP | ACC | AP | |
| 文献[ | 48.3% | 52.6% | 53.4% | 64.4% | 50.0% | 63.3% | 48.6% | 38.5% | 49.3% | 44.7% | 49.9% | 52.7% |
| 文献[ | 70.5% | 85.7% | 67.3% | 72.2% | 47.6% | 43.1% | 39.7% | 40.8% | 68.7% | 65.2% | 58.8% | 61.4% |
| 文献[ | 63.2% | 71.7% | 39.1% | 40.8% | 54.1% | 53.6% | 45.7% | 47.2% | 53.9% | 52.2% | 51.2% | 53.1% |
| 文献[ | 63.5% | 62.5% | 57.1% | 60.1% | 55.3% | 57.7% | 54.3% | 56.4% | 48.8% | 47.4% | 55.8% | 56.8% |
| 文献[ | 47.9% | 57.0% | 51.0% | 56.1% | 47.3% | 45.5% | 50.0% | 44.7% | 49.8% | 49.7% | 49.2% | 50.6% |
| 文献[ | 45.2% | 46.9% | 72.7% | 79.3% | 59.8% | 88.5% | 68.3% | 76.0% | 75.1% | 80.9% | 64.2% | 74.3% |
| 本文模型 | 68.6% | 74.6% | 70.8% | 82.7% | 58.2% | 81.0% | 74.5% | 69.0% | 68.9% | 77.2% | 68.2% | 76.9% |
| [1] | HO J, JAIN A, ABBEEL P. Denoising Diffusion Probabilistic Models[J]. Advances in Neural Information Processing Systems, 2020, 33: 6840-6851. |
| [2] | RAMESH A, PAVLOV M, GOH G, et al. Zero-Shot Text-to-Image Generation[C]// PMLR. International Conference on Machine Learning. New York: PMLR, 2021: 8821-8831. |
| [3] | THOMSON T, ANGUS D, DOOTSON P, et al. Visual Mis/Disinformation in Journalism and Public Communications: Current Verification Practices, Challenges and Future Opportunities[J]. Journalism Practice, 2022, 16(5): 938-962. |
| [4] | BRUNDAGE M, AVIN S, CLARK J, et al. The Malicious Use of Artificial Intelligence: Forecasting, Prevention and Mitigation[EB/OL].(2018-02)[2026-01-02]. https://arxiv.org/pdf/1802.07228. |
| [5] | BAI Weiming, ZHANG Zhipeng, LI Bing, et al. Robust Texture-Aware Computer-Generated Image Forensic: Benchmark and Algorithm[J]. IEEE Trans Image Process, 2021, 30: 8439-8453. |
| [6] | YANG Ke, LI Yongliang, HE Jindong, et al. Deepfake Face Detection Based on Masked Image Modeling[J]. Computer Applications, 2025, 45: 72-77. |
| 杨珂, 李永亮, 何金栋, 等. 基于掩码图像建模的深度伪造人脸检测[J]. 计算机应用, 2025, 45: 72-77. | |
| [7] | LI Jialin, SHEN Zhe. Channel-Adaptive Deepfake Image Detection Enhanced by Spatial Domain Features[J]. Journal of Computer-Aided Design and Graphics, 2025, 37(2): 313-320. |
| 李佳林, 沈哲. 空间域增强的通道自适应深度伪造图像检测方法[J]. 计算机辅助设计与图形学学报, 2025, 37(2): 313-320. | |
| [8] | WANG S, WANG O, ZHANG R, et al. CNN-Generated Images Are Surprisingly Easy to Spot. for Now[C]// IEEE. The IEEE/CVF Conference on Computer Vision and Pattern Recognition. New York: IEEE, 2020: 8695-8704. |
| [9] | LI Weichuang, HE Peisong, LI Haoliang, et al. Detection of GAN-Generated Images by Estimating Artifact Similarity[J]. IEEE Signal Processing Letters, 2021, 29: 862-866. |
| [10] | CHEN Beijing, LIU Xin, ZHENG Yuhui, et al. A Robust GAN-Generated Face Detection Method Based on Dual-Color Spaces and An Improved Xception[J]. IEEE Transactions on Circuits and Systems for Video Technology, 2021, 32(6): 3527-3538. |
| [11] | LIU Yun, WAN Zuliang, YIN Xiaohua, et al. Detection of GAN Generated Image Using Color Gradient Representation[J]. Journal of Visual Communication and Image Representation, 2023, 95: 1-9. |
| [12] | LIU Honggu, LI Xiaodan, ZHOU Wenbo, et al. Spatial-Phase Shallow Learning: Rethinking Face Forgery Detection in Frequency Domain[C]// IEEE. The IEEE/CVF Conference on Computer Vision and Pattern Recognition. New York: IEEE, 2021: 772-781. |
| [13] | GAO Yuan, ZHANG Yu, ZENG Ping, et al. Refining Localized Attention Features with Multi-Scale Relationships for Enhanced Deepfake Detection in Spatial-Frequency Domain[J]. Electronics, 2024, 13(9): 1749. |
| [14] | CHAI L, BAU D, LIM S, et al. What Makes Fake Images Detectable? Understanding Properties That Generalize[C]// Springer. European Conference on Computer Vision. Heidelberg: Springer, 2020: 103-120. |
| [15] | CHEN Beijing, JU Xingwang, XIAO Bin, et al. Locally GAN-Generated Face Detection Based on An Improved Xception[J]. Information Sciences, 2021, 572: 16-28. |
| [16] | SONG Jiajun, LIU Guixiong, HUANG Jiaxi, et al. HiFi-Net Deepfake Image Detection Based on U-HRNet and SoftTripleLoss[J]. China Testing, 2023, 49(9): 37-45. |
| 宋家骏, 刘桂雄, 黄家曦, 等. 应用U-HRNet+SoftTripleLoss的HiFi-Net伪造图像检测技术研究[J]. 中国测试, 2023, 49(9): 37-45. | |
| [17] | RAJ S, MATHEW J, MONDAL A. Generalized and Robust Model for GAN-Generated Image Detection[J]. Pattern Recognition Letters, 2024, 182: 104-110. |
| [18] | XI Ziyi, LIN Hao, LUO Weiqi. Dual Stream Computer-Generated Image Detection Network Based on Channel Joint and Softpool[EB/OL].(2022-07-07)[2026-01-02]. https://arxiv.org/pdf/2207.03205. |
| [19] | ZHAO Lei, ZHANG Mingcheng, DING Hongwei, et al. MFF-Net: Deepfake Detection Network Based on Multi-Feature Fusion[J]. Entropy, 2021, 23(12): 1692-1706. |
| [20] | CORVI R, COZZOLINO D, ZINGARINI G, et al. On the Detection of Synthetic Images Generated by Diffusion Models[C]// IEEE. ICASSP 2023-2023 IEEE International Conference on Acoustics, Speech and Signal Processing (ICASSP). New York: IEEE, 2023: 1-5. |
| [21] | CAZENAVETTE G, SUD A, LEUNG T, et al. Fakeinversion: Learning to Detect Images from Unseen Text-to-Image Models by Inverting Stable Diffusion[C]// IEEE. The IEEE/CVF Conference on Computer Vision and Pattern Recognition. New York: IEEE, 2024: 10759-10769. |
| [22] | LORENZ P, DURALL R L, KEUPER J. Detecting Images Generated by Deep Diffusion Models Using Their Local Intrinsic Dimensionality[C]// IEEE. The IEEE/CVF International Conference on Computer Vision. New York: IEEE, 2023: 448-459. |
| [23] | SANTOSH L L, AMERINI I, WANG Xin, et al. Robust CLIP-Based Detector for Exposing Diffusion Model-Generated Images[EB/OL].(2024-09-08)[2026-01-02]. https://arxiv.org/pdf/2404.12908. |
| [24] | WANG Zhendong, BAO Jianmin, ZHOU Wengang, et al. Dire for Diffusion-Generated Image Detection[C]// IEEE. The IEEE/CVF International Conference on Computer Vision. New York: IEEE, 2023: 22445-22455. |
| [25] | CHEN Baoying, ZENG Jishen, YANG Jianquan, et al. Drct: Diffusion Reconstruction Contrastive Training towards Universal Detection of Diffusion Generated Images[C]// PMLR. Forty-First International Conference on Machine Learning. New York: PLMR, 2024: 7621-7639. |
| [26] | HE Kaiming, ZHANG Xiangyu, REN Shaoqing, et al. Deep Residual Learning for Image Recognition[C]// IEEE. The IEEE Conference on Computer Vision and Pattern Recognition. New York: IEEE, 2016: 770-778. |
| [27] | KARRAS T, AILA T, LAINE S, et al. Progressive Growing of GANs for Improved Quality, Stability and Variation[EB/OL].(2018-02-26)[2026-01-02]. https://arxiv.org/pdf/1710.10196. |
| [28] | TAN Chuangchuang, TAO Renshuai, LIU Huan, et al. Gangen-Detection: A Dataset Generated by Gans for Generalizable Deepfake Detection[EB/OL].( 2024)[2026-01-02]. https://github.com/chuangchuangtan/GANGen-Detection. |
| [29] | TAN Chuangchuang, ZHAO Yao, WEI Shikui, et al. Rethinking the Up-Sampling Operations in CNN-Based Generative Network for Generalizable Deepfake Detection[C]// IEEE. The IEEE/CVF Conference on Computer Vision and Pattern Recognition. New York: IEEE, 2024: 28130-28139. |
| [30] | YU F, SEFF A, ZHANG Yinda, et al. Lsun: Construction of a Large-Scale Image Dataset Using Deep Learning with Humans in the Loop[EB/OL].(2016-06-04)[2026-01-02]. https://arxiv.org/pdf/1506.03365. |
| [31] | PASZKE A, GROSS S, MASSA F, et al. Pytorch: An Imperative Style, High-Performance Deep Learning Library[J]. Advances in Neural Information Processing Systems, 2019, 32: 8026-8037. |
| [32] | KINGMA D P, BA J L. Adam: A Method for Stochastic Optimization[EB/OL].(2017-01-30)[2026-01-02]. https://arxiv.org/pdf/1412.6980. |
| [33] | FRANK J, EISENHOFER T, SCHÖNHERR L, et al. Leveraging Frequency Analysis for Deep Fake Image Recognition[C]// PMLR. International Conference on Machine Learning. New York: PMLR, 2020: 3247-3258. |
| [34] | DURALL R, KEUPER M, KEUPER J. Watch Your Up-Convolution: CNN Based Generative Deep Neural Networks Are Failing to Reproduce Spectral Distributions[C]// IEEE. The IEEE/CVF Conference on Computer Vision and Pattern Recognition. New York: IEEE, 2020: 7890-7899. |
| [35] | JEONG Y, KIM D, MIN S, et al. Bihpf: Bilateral High-Pass Filters for Robust Deepfake Detection[C]// IEEE. The IEEE/CVF Winter Conference on Applications of Computer Vision. New York: IEEE, 2022: 48-57. |
| [36] | TAN Chuangchuang, ZHAO Yao, WEI Shuikui, et al. Learning on Gradients: Generalized Artifacts Representation for GAN-Generated Images Detection[C]// IEEE. The IEEE/CVF Conference on Computer Vision and Pattern Recognition. New York: IEEE, 2023: 12105-12114. |
| [37] | QIAN Yuyang, YIN Guojun, SHENG Lu, et al. Thinking in frequency: Face Forgery Detection by Mining Frequency-Aware Clues[C]// Springer. European Conference on Computer Vision. Heidelberg: Springer, 2020: 86-103. |
| [38] | JEONG Y, KIM D, RO Y, et al. Frepgan: Robust Deepfake Detection Using Frequency-Level Perturbations[C]// AAAI. The AAAI Conference on Artificial Intelligence. Menlo Park: AAAI, 2022: 1060-1068. |
| [39] | SHIOHARA K, YAMASAKI T. Detecting Deepfakes with Self-Blended Images[C]// IEEE. The IEEE/CVF Conference on Computer Vision and Pattern Recognition. New York: IEEE, 2022: 18720-18729. |
| [40] | MANDELLI S, BONETTINI N, BESTAGINI P, et al. Detecting GAN-Generated Images by Orthogonal Training of Multiple CNNs[C]// IEEE. 2022 IEEE International Conference on Image Processing. New York: IEEE, 2022: 3091-3095. |
| [1] | 胡文涛, 丁伟杰. DiffGuard:基于扩散模型与自适应序列学习的网络流量异常检测框架[J]. 信息网络安全, 2026, 26(3): 378-388. |
| [2] | 李思聪, 王飞, 魏子令, 陈曙晖. 面向恶意代码检测的深度注意力网络架构[J]. 信息网络安全, 2025, 25(8): 1208-1222. |
| [3] | 熊翱, 刘雨潇, 钱旭盛, 张楠. 基于扩散模型和生成对抗网络的生成式隐写方法[J]. 信息网络安全, 2025, 25(8): 1223-1230. |
| [4] | 李元诚, 孙鹤洋, 张桐, 张贺方, 杨立群. 基于DACDiff的分布式电源调度控制系统FDIAs防御方法[J]. 信息网络安全, 2025, 25(4): 578-586. |
| [5] | 梁凤梅, 潘正豪, 刘阿建. 基于共性伪造线索感知的物理和数字人脸攻击联合检测方法[J]. 信息网络安全, 2025, 25(10): 1604-1614. |
| [6] | 董云云, 朱玉玲, 姚绍文. 基于改进U-Net和混合注意力机制的高质量全尺寸图像隐写方法[J]. 信息网络安全, 2024, 24(7): 1050-1061. |
| [7] | 王健, 陈琳, 王凯崙, 刘吉强. 基于时空图神经网络的应用层DDoS攻击检测方法[J]. 信息网络安全, 2024, 24(4): 509-519. |
| [8] | 杨志鹏, 刘代东, 袁军翼, 魏松杰. 基于自注意力机制的网络局域安全态势融合方法研究[J]. 信息网络安全, 2024, 24(3): 398-410. |
| [9] | 江魁, 卢橹帆, 苏耀阳, 聂伟. 基于Attention-GRU的SHDoS攻击检测研究[J]. 信息网络安全, 2024, 24(3): 427-437. |
| [10] | 张新有, 孙峰, 冯力, 邢焕来. 基于多视图表征的虚假新闻检测[J]. 信息网络安全, 2024, 24(3): 438-448. |
| [11] | 冯光升, 蒋舜鹏, 胡先浪, 马明宇. 面向物联网的入侵检测技术研究新进展[J]. 信息网络安全, 2024, 24(2): 167-178. |
| [12] | 孙红哲, 王坚, 王鹏, 安雨龙. 基于Attention-BiTCN的网络入侵检测方法[J]. 信息网络安全, 2024, 24(2): 309-318. |
| [13] | 张国敏, 屠智鑫, 邢长友, 王梓澎, 张俊峰. 基于对抗样本的流量时序特征混淆方法[J]. 信息网络安全, 2024, 24(12): 1882-1895. |
| [14] | 李鹏超, 张全涛, 胡源. 基于双注意力机制图神经网络的智能合约漏洞检测方法[J]. 信息网络安全, 2024, 24(11): 1624-1631. |
| [15] | 刘刚, 杨雯莉, 王同礼, 李阳. 基于云联邦的差分隐私保护动态推荐模型[J]. 信息网络安全, 2023, 23(7): 31-43. |
| 阅读次数 | ||||||
|
全文 |
|
|||||
|
摘要 |
|
|||||