信息网络安全 ›› 2022, Vol. 22 ›› Issue (1): 55-63.doi: 10.3969/j.issn.1671-1122.2022.01.007
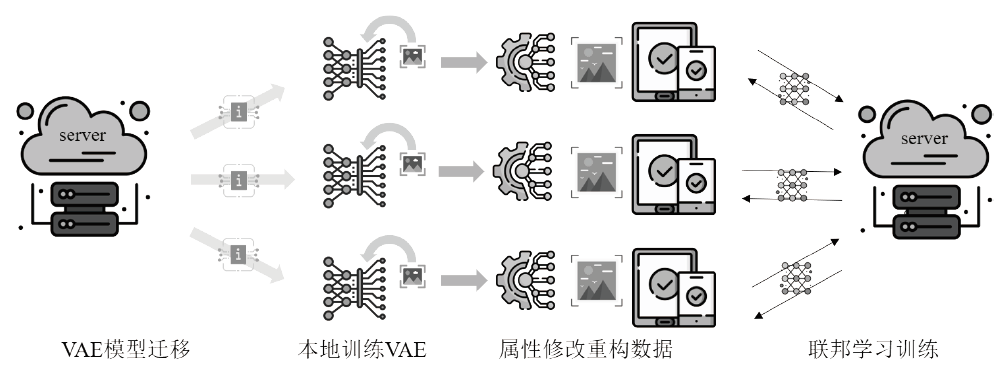
基于数据属性修改的联邦学习隐私保护策略
- 中国海洋大学信息科学与工程学部计算机科学与技术学院,青岛 266100
-
收稿日期:2021-10-08出版日期:2022-01-10发布日期:2022-02-16 -
通讯作者:夏辉 E-mail:xiahui@ouc.edu.cn -
作者简介:徐硕(1998—),男,山东,博士研究生,主要研究方向为隐私保护、联邦学习和人工智能安全|张睿(1995—),女,山东,博士研究生,主要研究方向为物联网安全、人工智能安全和网络防御|夏辉(1986—),男,山东,教授,博士,主要研究方向为无线自组织网络、物联网安全、人工智能安全、隐私保护、边缘计算和联邦学习 -
基金资助:国家自然科学基金面上项目(62172377);国家自然科学基金面上项目(61872205);山东省自然科学基金面上项目(ZR2019MF018)
Privacy-preserving Strategies for Federated Learning Based on Data Attribute Modification
- College of Computer Science and Technology, Faculty of Information Science and Engineering, Ocean University of China, Qingdao 266100, China
-
Received:2021-10-08Online:2022-01-10Published:2022-02-16 -
Contact:XIA Hui E-mail:xiahui@ouc.edu.cn
摘要:
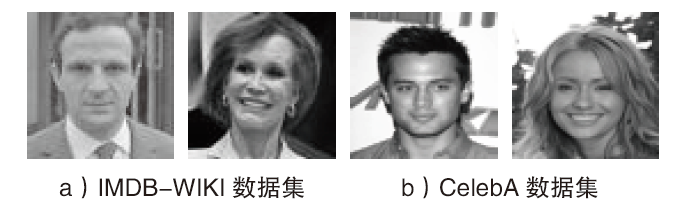
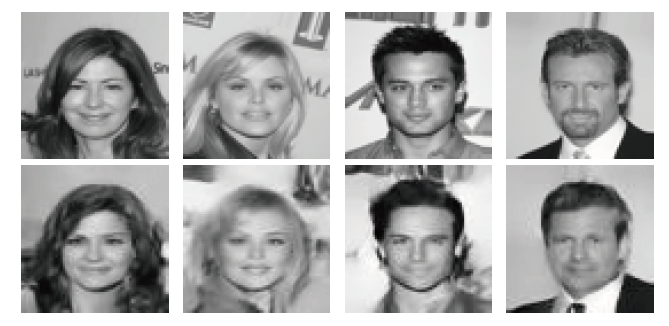
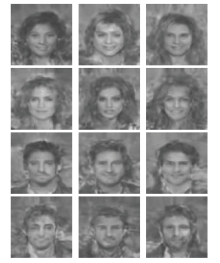
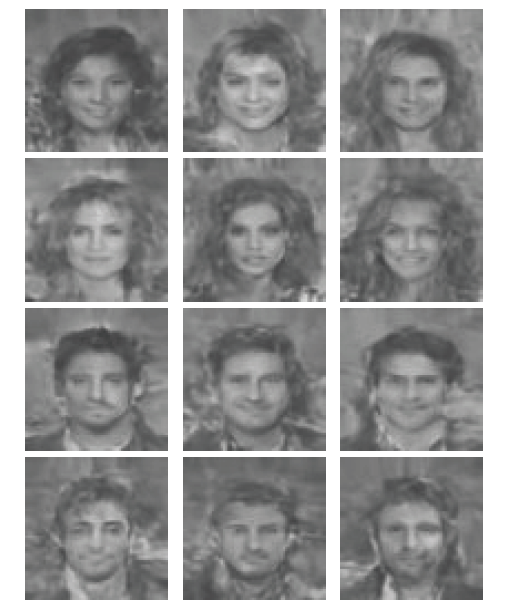
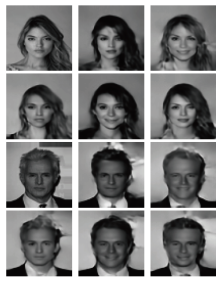
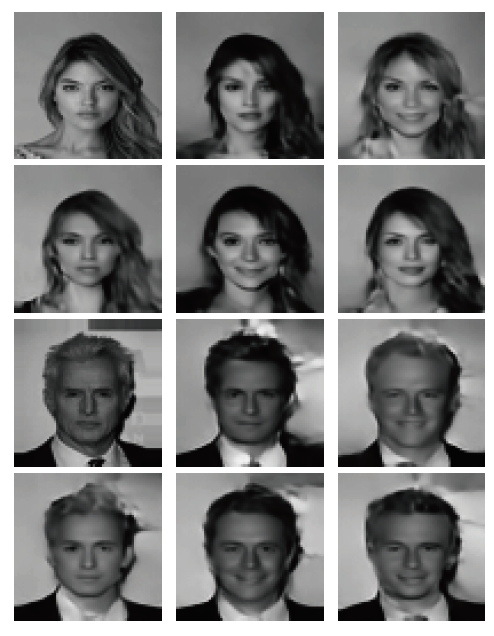
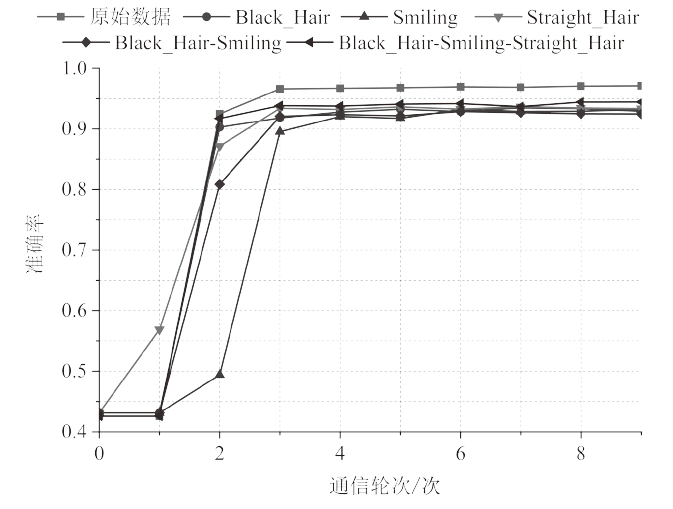
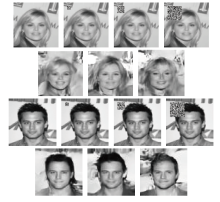
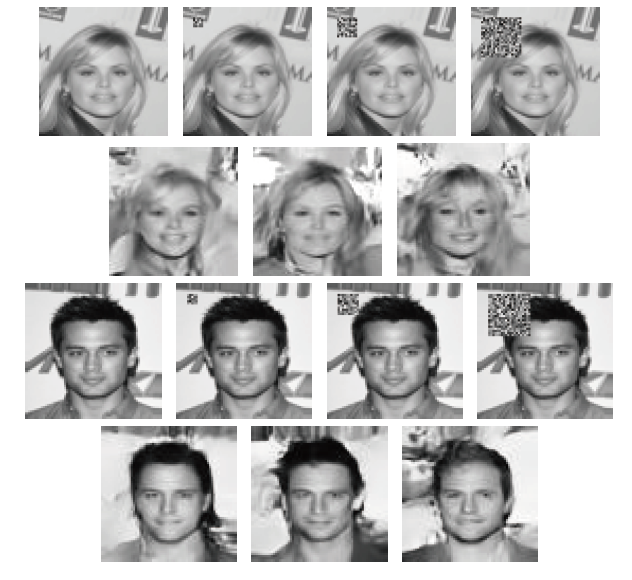
针对大部分联邦学习防御方法存在降低联邦学习实用性、计算效率低和防御攻击种类单一等问题,文章提出一种基于变分自编码器的属性修改框架,在客户端对数据预处理以达到保护联邦学习的目的。首先,为了提高算法计算效率,文章提出一种基于迁移学习的变分自编码器训练方案来减少客户端训练周期;其次,利用变分自编码器具有连续性的潜变量,设计了一种基于属性分布约束规则的属性修改方案来实现客户端训练数据的重构。实验结果表明,属性修改方案可以成功分离和控制图像的属性向量,通过将原始图像改变为带有相应属性的重构图像,保护了客户端数据隐私。将修改后的图像用于训练联邦学习分类任务,其准确率可达94.44%,体现了方案的可用性,并且该方案可以成功防御非主属性隐私泄露和基于数据中毒的后门攻击。
中图分类号:
引用本文
徐硕, 张睿, 夏辉. 基于数据属性修改的联邦学习隐私保护策略[J]. 信息网络安全, 2022, 22(1): 55-63.
XU Shuo, ZHANG Rui, XIA Hui. Privacy-preserving Strategies for Federated Learning Based on Data Attribute Modification[J]. Netinfo Security, 2022, 22(1): 55-63.
表2
防御非主属性隐私泄露效果
| 属性 | $\beta $ | 0 | 1 | 2 | 3 | 4 | 5 | 6 | 7 | 8 | 9 |
|---|---|---|---|---|---|---|---|---|---|---|---|
| Black_Hair | 1.0 | 65% | 63% | 66% | 66% | 65% | 64% | 66% | 65% | 67% | 61% |
| 0.5 | 79% | 77% | 79% | 79% | 79% | 79% | 80% | 78% | 81% | 75% | |
| 0.1 | 86% | 84% | 85% | 84% | 86% | 86% | 85% | 83% | 85% | 83% | |
| Smiling | 1.0 | 56% | 56% | 56% | 57% | 56% | 56% | 56% | 56% | 56% | 54% |
| 0.5 | 74% | 74% | 75% | 76% | 75% | 74% | 74% | 73% | 73% | 71% | |
| 0.1 | 86% | 86% | 86% | 86% | 87% | 85% | 85% | 85% | 85% | 85% | |
| Straight_Hair | 1.0 | 72% | 71% | 72% | 70% | 72% | 71% | 72% | 72% | 72% | 73% |
| 0.5 | 76% | 75% | 75% | 74% | 76% | 74% | 76% | 74% | 75% | 76% | |
| 0.1 | 75% | 74% | 74% | 73% | 74% | 73% | 75% | 73% | 74% | 74% |
表2
| [1] | DENG Jia, DONG Wei, SOCHER R, et al. Imagenet: A Large-scale Hierarchical Image Database[C]//IEEE. IEEE-computer-society Conference on Computer Vision and Pattern Recognition Workshops, June 20-25, 2009, Miami, FL, USA. New York: IEEE, 2009: 248-255. |
| [2] | MCMAHAN B, MOORE E, RAMAGE D, et al. Communication-efficient Learning of Deep Networks from Decentralized Data[C]//PMLR. 20th International Conference on Artificial Intelligence and Statistics, April 20-22, 2017, Fort Lauderdale, FL, USA. Brookline: Microtome Publishing, 2017: 1273-1282. |
| [3] | MELIS L, SONG Congzheng, CRISTOFARO E D, et al. Exploiting Unintended Feature Leakage in Collaborative Learning[C]//IEEE. 40th IEEE Symposium on Security and Privacy (SP), May 19-23, 2019, San Francisco, CA, USA. New York: IEEE, 2019: 691-706. |
| [4] | WANG Hongyi, SREENIVASAN K, RAJPUT S, et al. Attack of the Tails: Yes, You Really Can Backdoor Federated Learning[J]. NIPS, 2020, 33(5):16070-16084. |
| [5] | RIVEST R L, ADLEMAN L, DERTOUZOS M L. On Data Banks and Privacy Homomorphisms[J]. Foundations of Secure Computation, 1978, 4(11):169-180. |
| [6] |
LIU Yang, KANG Yan, XING Chaoping, et al. A Secure Federated Transfer Learning Framework[J]. IEEE Intelligent Systems, 2020, 35(4):70-82.
doi: 10.1109/MIS.9670 URL |
| [7] | DWORK C, MCSHERRY F, NISSIM K, et al. Calibrating Noise to Sensitivity in Private Data Analysis[C]//Springer. 3rd Theory of Cryptography Conference, March 4-7, 2006, New York, NY, USA. Berlin: Springer-Verlag, 2006: 265-284. |
| [8] | JAYARAMAN B, EVANS D. When Relaxations Go Bad: “Differentially- private”Machine Learning[EB/OL]. https://arxiv.org/abs/1902.08874v2, 2019-08-12. |
| [9] | BLANCHARD P, EL MHAMDI E M, GUERRAOUI R, et al. Machine Learning with Adversaries: Byzantine Tolerant Gradient Descent[C]//NIPS. 31st Annual Conference on Neural Information Processing Systems, December 4-9, 2017, Long Beach, CA, USA. California: NIPS, 2017: 118-128. |
| [10] | FANG Minghong, CAO Xiaoyu, JIA Jinyuan, et al. Local Model Poisoning Attacks to Byzantine-robust Federated Learning[C]//USENIX. 29th USENIX Security Symposium, August 12-14, 2020, Boston, MA, USA. Berkeley: USENIX ASSOC, 2020: 1605-1622. |
| [11] |
KAIROUZ P, MCMAHAN H B, AVENT B, et al. Advances and Open Problems in Federated Learning[J]. Foundations and Trends in Machine Learning, 2021, 14(1-2):1-210.
doi: 10.1561/2200000083 URL |
| [12] | HE Chaoyang, LI Songze, SO J, et al. Fedml: A Research Library and Benchmark for Federated Machine Learning[EB/OL]. https://arxiv.org/abs/2007.13518, 2020-11-08. |
| [13] | KINGMA D P, WELLING M. Auto-encoding Variational Bayes[EB/OL]. https://arxiv.org/abs/1312.6114, 2014-05-01. |
| [14] | XIE Chulin, HUANG Keli, CHEN Pinyu, et al. Dba: Distributed Backdoor Attacks against Federated Learning[C]// ICLR. 7th International Conference on Learning Representations, May 6-9, 2019, New Orleans, LA, USA. New York: ICLR, 2019: 142-151. |
| [15] | LIU Ziwei, LUO Ping, WANG Xiaogang, et al. Large-scale Celebfaces Attributes (Celeba) Dataset[EB/OL]. http://mmlab.ie.cuhk.edu.hk/projects/CelebA.html, 2021-09-10. |
| [16] |
ROTHE R, TIMOFTE R, VAN GOOL L. Deep Expectation of Real and Apparent Age from a Single Image without Facial Landmarks[J]. International Journal of Computer Vision, 2018, 126(2):144-157.
doi: 10.1007/s11263-016-0940-3 URL |
| [17] | VAHDAT A, KAUTZ J. Nvae: A Deep Hierarchical Variational Autoencoder[EB/OL]. https://arxiv.org/abs/2007.03898, 2021-01-08. |
| [1] | 白宏鹏, 邓东旭, 许光全, 周德祥. 基于联邦学习的入侵检测机制研究[J]. 信息网络安全, 2022, 22(1): 46-54. |
| [2] | 路宏琳, 王利明, 杨婧. 一种新的参数掩盖联邦学习隐私保护方案[J]. 信息网络安全, 2021, 21(8): 26-34. |
| [3] | 靳姝婷, 何泾沙, 朱娜斐, 潘世佳. 基于本体推理的隐私保护访问控制机制研究[J]. 信息网络安全, 2021, 21(8): 52-61. |
| [4] | 任涛, 金若辰, 罗咏梅. 融合区块链与联邦学习的网络入侵检测算法[J]. 信息网络安全, 2021, 21(7): 27-34. |
| [5] | 刘子昂, 黄缘缘, 马佳利, 周睿. 基于区块链的医疗数据滥用监控平台设计与实现[J]. 信息网络安全, 2021, 21(5): 58-66. |
| [6] | 王健, 赵曼莉, 陈志浩, 石波. 基于假名的智能交通条件隐私保护认证协议[J]. 信息网络安全, 2021, 21(4): 49-61. |
| [7] | 任航, 程相国, 张睿, 夏辉. 基于议价贝叶斯博弈模型的防欺诈策略[J]. 信息网络安全, 2021, 21(4): 81-88. |
| [8] | 周由胜, 王明, 刘媛妮. 支持区间查询的基于位置服务外包数据隐私保护方案[J]. 信息网络安全, 2021, 21(3): 26-36. |
| [9] | 路宏琳, 王利明. 面向用户的支持用户掉线的联邦学习数据隐私保护方法[J]. 信息网络安全, 2021, 21(3): 64-71. |
| [10] | 夏喆, 罗宾, 徐桂彬, 肖新秀. 智能电网中支持细粒度访问控制的隐私保护数据聚合方案[J]. 信息网络安全, 2021, 21(11): 28-39. |
| [11] | 李桐, 周小明, 任帅, 徐剑. 轻量化移动边缘计算双向认证协议[J]. 信息网络安全, 2021, 21(11): 58-64. |
| [12] | 李坤昌, 石润华, 李恩. 智能电网中数据聚合与用户查询隐私保护研究[J]. 信息网络安全, 2021, 21(11): 65-74. |
| [13] | 刘峰, 杨杰, 齐佳音. 基于哈希证明系统的区块链两方椭圆曲线数字签名算法研究[J]. 信息网络安全, 2021, 21(1): 19-26. |
| [14] | 汪金苗, 谢永恒, 王国威, 李易庭. 基于属性基加密的区块链隐私保护与访问控制方法[J]. 信息网络安全, 2020, 20(9): 47-51. |
| [15] | 李宁波, 周昊楠, 车小亮, 杨晓元. 云环境下基于多密钥全同态加密的定向解密协议设计[J]. 信息网络安全, 2020, 20(6): 10-16. |
| 阅读次数 | ||||||
|
全文 |
|
|||||
|
摘要 |
|
|||||