Netinfo Security ›› 2026, Vol. 26 ›› Issue (3): 491-499.doi: 10.3969/j.issn.1671-1122.2026.03.015
Previous Articles Next Articles
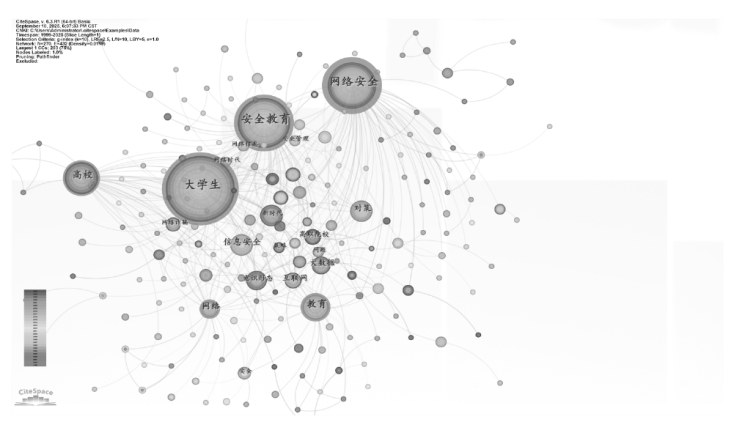
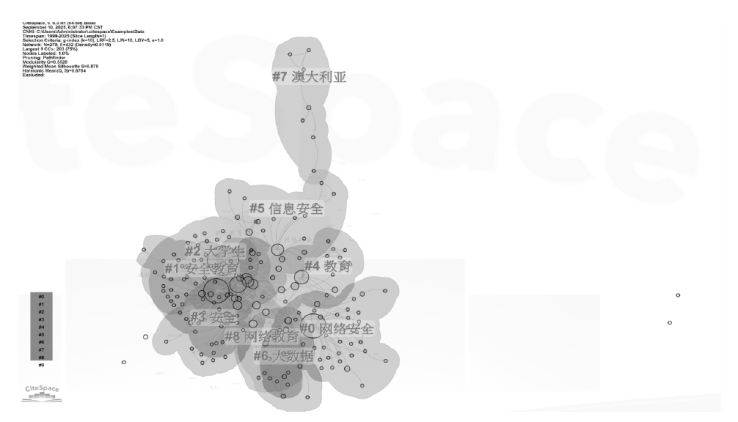
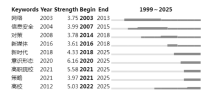
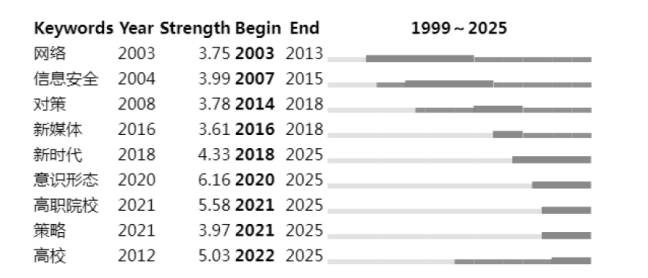
Analysis of Hotspots and Trends in Cybersecurity Education - A Graph-Based Quantitative Analysis Using CiteSpace
- 1. School of Criminology, People’s Public Security University of China, Beijing 100038, China
2. Graduate School, People’s Public Security University of China, Beijing 100038, China
-
Received:2025-10-17Online:2026-03-10Published:2026-03-30
CLC Number:
Cite this article
HUANG Dong, CHEN Zhijun. Analysis of Hotspots and Trends in Cybersecurity Education - A Graph-Based Quantitative Analysis Using CiteSpace[J]. Netinfo Security, 2026, 26(3): 491-499.
share this article
Add to citation manager EndNote|Ris|BibTeX
URL: http://netinfo-security.org/EN/10.3969/j.issn.1671-1122.2026.03.015
| [1] | YAN Na, CONG Peibing. Cybersecurity Education for College Students in the Context of Xi Jinping’s Comprehensive National Security Outlook[J]. Journal of Jilin Provincial Education Institute, 2019, 35(1): 30-33. |
| 闫娜, 丛培兵. 习近平总体国家安全观视域下的大学生网络安全教育[J]. 吉林省教育学院学报, 2019, 35(1):30-33. | |
| [2] | XU Chang, GAO Jinhu. Research on Cultivating Cybersecurity Awareness Among U. S. Citizens[J]. Journal of Intelligence, 2018, 37(12): 135-139, 146. |
| 许畅, 高金虎. 美国公民国家网络安全意识培养问题研究[J]. 情报杂志, 2018, 37(12):135-139,146. | |
| [3] | ZHAO Dongchen. Cybersecurity Education in Primary and Secondary Schools of EU Countries: Current Status and Implications[J]. Foreign Primary and Secondary Education, 2010(9): 12-15. |
| 赵冬臣. 欧盟国家的中小学网络安全教育:现状与启示[J]. 外国中小学教育, 2010(9):12-15. | |
| [4] | ZHANG Benqing, LI Hongge. Effective Pathways for Integrating Cyberspace Ideological Security Education into College Ideological and Political Theory Courses[J]. Guide to Ideological and Theoretical Education, 2019(7): 97-100. |
| 张本青, 李红革. 网络意识形态安全教育融入高校思想政治理论课的有效路径[J]. 思想理论教育导刊, 2019(7):97-100. | |
| [5] | WANG Juan, CHEN Shichao, WANG Linli, et al. Analysis of Research Hotspots and Trends in Education Big Data Based on CiteSpace[J]. Modern Educational Technology, 2016, 26(2): 5-13. |
| 王娟, 陈世超, 王林丽, 等. 基于CiteSpace的教育大数据研究热点与趋势分析[J]. 现代教育技术, 2016, 26(2):5-13. | |
| [6] | HOU Jianhua, HU Zhigang. Review and Prospects of CiteSpace Software Application Research[J]. Modern Intelligence, 2013, 33(4): 99-103. |
|
侯剑华, 胡志刚. CiteSpace软件应用研究的回顾与展望[J]. 现代情报, 2013, 33(4):99-103.
doi: 10.3969/j.issn.1008-0821.2013.04.022 |
|
| [7] | HUANG Rong, ZHAO Xiqun. Pathways for Online Ideological Security Education among College Students[J]. Contemporary Education Theory and Practice, 2015, 7(4): 133-136. |
| 黄蓉, 赵惜群. 大学生网络意识形态安全教育路径探析[J]. 当代教育理论与实践, 2015, 7(4):133-136. | |
| [8] | JIANG Yanling. Enhancing Online Ideological Security Education in Higher Education Institutions[J]. Chinese Higher Education, 2021(6): 34-36. |
| 蒋燕玲. 强化高校网络意识形态安全教育论析[J]. 中国高等教育, 2021(6):34-36. | |
| [9] | DIAO Yigang. Analysis of Research Hotspots and Trends in Personal Information Protection Based on CiteSpace[J]. Information Network Security, 2024, 24(12): 1948-1954. |
| 刁毅刚. 基于CiteSpace的个人信息保护领域研究热点及趋势分析[J]. 信息网络安全, 2024, 24(12):1948-1954. | |
| [10] | LAI Yuping, WEI Yanni. Integrated Progression of Cybersecurity Education in the New Era[J]. Teaching of Ideological and Political Courses, 2025(7): 4-7. |
| 赖裕平, 魏燕妮. 新时代网络安全教育的一体化进阶[J]. 思想政治课教学, 2025(7):4-7. | |
| [11] | CHEN Yue, CHEN Chaomei, LIU Zeyuan, et al. Methodological Functions of CiteSpace Knowledge Graphs[J]. Studies in Science of Science, 2015, 33(2): 242-253. |
| 陈悦, 陈超美, 刘则渊, 等. CiteSpace知识图谱的方法论功能[J]. 科学学研究, 2015, 33(2):242-253. | |
| [12] | DONG Xinliang, GUO Junmin, GUO Xiting. An Analysis of Cybersecurity Curriculum Development for Australian Youth[J]. Comparative Education Research, 2020, 42(1): 26-32. |
| 董新良, 郭俊敏, 郭熙婷. 澳大利亚青少年网络安全课程建设探析[J]. 比较教育研究, 2020, 42(1):26-32. | |
| [13] | WANG Ting. Challenges and Countermeasures for Enhancing Cybersecurity Awareness among Primary and Secondary School Teachers and Students in the Context of Educational Digitalization[J]. Education Theory and Practice, 2024, 44(35): 17-20. |
| 王婷. 教育数字化背景下提高中小学师生网络安全意识面临的问题及应对策略[J]. 教育理论与实践, 2024, 44(35):17-20. | |
| [14] | LI Menglin, SONG Ping. Visual Analysis of Current Research in Cybersecurity Education[J]. Open University Journal of Science and Technology, 2024(4): 13-20. |
| 李孟林, 宋平. 网络安全教育研究现状的可视化分析[J]. 电大理工, 2024(4):13-20. | |
| [15] | LI Nuo, SHEN Zhijuan, ZHANG Jing. Building Cybersecurity Management Systems in Higher Education Institutions in the Big Data Era: Review of “Research on Cybersecurity Education and Management in Higher Education Institutions”[J]. Applied Chemistry, 2023, 52(10): 2995. |
| 李诺, 申志娟, 张静. 大数据时代高校网络安全管理体系建设—评《高校网络安全教育与管理研究》[J]. 应用化工, 2023, 52(10):2995. |
| [1] | YUAN Ming, ZOU Qilin, YUAN Wenqi, WANG Qun. A Survey on Prompt Injection Attacks and Defenses in Large Language Models [J]. Netinfo Security, 2026, 26(3): 341-354. |
| [2] | LI Fujuan, WANG Qun. Research Progress of Cyber Ranges [J]. Netinfo Security, 2026, 26(3): 355-366. |
| [3] | XU Yanwei, TU Min, ZHANG Liang. A Review on the Authenticity Verification of Deepfake Speech [J]. Netinfo Security, 2026, 26(3): 367-377. |
| [4] | HU Wentao, DING Weijie. DiffGuard: Network Traffic Anomaly Detection Based on Diffusion Models and Adaptive Sequence Learning [J]. Netinfo Security, 2026, 26(3): 378-388. |
| [5] | KANG Wenjie, LIU Yiguo, LIU Xuchong, ZHAO Wei, OUYANG Tianjian, LI Jiaxin. Research on Collaborative Defense against Cryptojacking Malware Based on Multi-Source Detection and AI Behavior Analysis [J]. Netinfo Security, 2026, 26(3): 389-398. |
| [6] | LIU Yanfei, LIU Dezhi, FENG Chuanlin, LI A, MAO Bowen. An AI-Generated Speech Detection Method Integrating Self-Supervised Representations and Multi-Scale Modeling [J]. Netinfo Security, 2026, 26(3): 399-411. |
| [7] | XU Wei, LUO Juan. Research on Network Information Security Gateway Technology Based on Polymorphic Load Balancing Algorithm [J]. Netinfo Security, 2026, 26(3): 412-419. |
| [8] | QIN Zhenkai, LUO Qining, NONG Xunyi, YU Xiaochuan, CAO Xiaochun. Multi-Level Speech Emotion Recognition Model Integrating Gender and Emotional Intensity Cue Features [J]. Netinfo Security, 2026, 26(3): 420-431. |
| [9] | CHEN Yuqi, QIAN Hanwei, XIA Lingling, WANG Qun. FEViT: A Frequency Domain Enhanced ViT for Deepfake Detection [J]. Netinfo Security, 2026, 26(3): 432-441. |
| [10] | LUO Wenhua, XU Shilong, LYU Tao, ZHANG Ning. Blockchain Data Provenance Mechanism Integrating Cuckoo Filters and Temporal B+ Tree [J]. Netinfo Security, 2026, 26(3): 442-451. |
| [11] | CHEN Chao, WANG Nuoxuan, ZHOU Shengli. Anomaly Detection Method for Bitcoin Transactions Based on ADASYN, Lasso Regression, and Ensemble Learning [J]. Netinfo Security, 2026, 26(3): 452-461. |
| [12] | YIN Jie, LIU Jiayin, HUANG Xiaoyu, LAN Haoliang, XIE Wenwei. Hidden Link Headline Detection Method Based on Multi-Modal Features [J]. Netinfo Security, 2026, 26(3): 462-470. |
| [13] | XIAO Wen, TU Min. Key Element Identification of Low-Resource Cases with Label Semantic Enhancement [J]. Netinfo Security, 2026, 26(3): 471-481. |
| [14] | LIANG Guangjun, QIU Yuchen, SI Hongtao, WANG Qun, MA Zhuo, CHEN Yuqi. Blockchain Virtual Currency Traceability and Analysis [J]. Netinfo Security, 2026, 26(3): 482-490. |
| [15] | HAN Yiliang, FENG Haokang, WU Xuguang, SUN Yuteng, WANG Yuanyuan. A Survey of Neural Network-Based Evaluation of Random Number Generators [J]. Netinfo Security, 2026, 26(2): 171-188. |
| Viewed | ||||||
|
Full text |
|
|||||
|
Abstract |
|
|||||