Netinfo Security ›› 2026, Vol. 26 ›› Issue (3): 389-398.doi: 10.3969/j.issn.1671-1122.2026.03.005
Previous Articles Next Articles
Research on Collaborative Defense against Cryptojacking Malware Based on Multi-Source Detection and AI Behavior Analysis
KANG Wenjie, LIU Yiguo, LIU Xuchong( ), ZHAO Wei, OUYANG Tianjian, LI Jiaxin
), ZHAO Wei, OUYANG Tianjian, LI Jiaxin
- Department of Information Technology (Network Supervision), Hunan Police Academy, Changsha 410138, China
-
Received:2025-08-11Online:2026-03-10Published:2026-03-30
CLC Number:
Cite this article
KANG Wenjie, LIU Yiguo, LIU Xuchong, ZHAO Wei, OUYANG Tianjian, LI Jiaxin. Research on Collaborative Defense against Cryptojacking Malware Based on Multi-Source Detection and AI Behavior Analysis[J]. Netinfo Security, 2026, 26(3): 389-398.
share this article
Add to citation manager EndNote|Ris|BibTeX
URL: http://netinfo-security.org/EN/10.3969/j.issn.1671-1122.2026.03.005
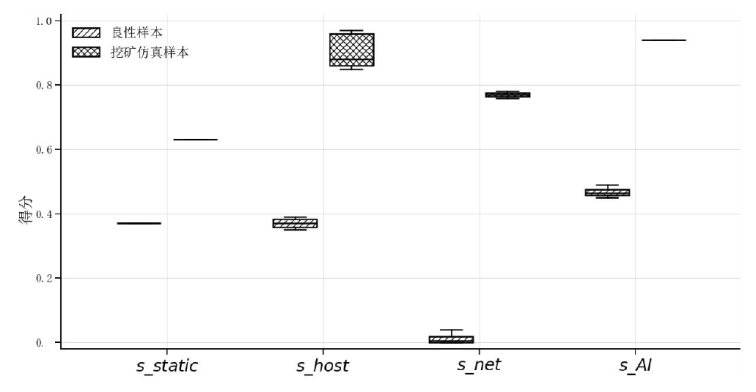
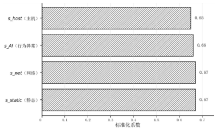
| 得分/特征 | 原始观测信号 | 评分/归一化方法 | 范围 | 用途说明 |
|---|---|---|---|---|
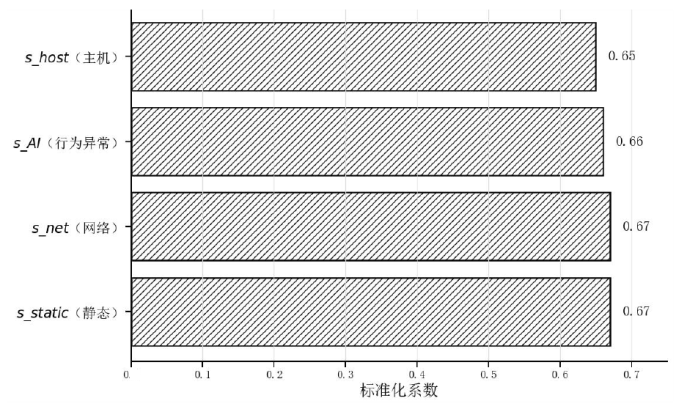
| s_static | 不可变文件标记、异常落地路径/关键目录写入、可疑文件 属性 | 规则命中项加权求和后归一化(min-max/分段映射) | [0,1] | 静态持久化/落地异常 强度 |
| s_host | CPU占用率、持续时间、进程树异常度(父子关系/命令行特征) | 时间窗统计量→异常分,归一化后输出 | [0,1] | 主机侧行为异常强度 |
| s_net | 外联频率、目的地址画像、Stratum特征命中度 | 命中/相似度→风险分,归一化后输出 | [0,1] | 网络侧挖矿通信可疑度 |
| s_AI | AI异常检测模块输出(概率/异常分) | 模型输出直接作为异常分(必要时做校准) | [0,1] | 补足弱信号与伪装场景检出 |
| [1] | HOU Jian, LU Hui, LIU Fang’ai, et al. Detection and Countermeasure of Encrypted Malicious Traffic: A Survey[J]. Journal of Software, 2024, 35(1): 333-355. |
| 侯剑, 鲁辉, 刘方爱, 等. 加密恶意流量检测及对抗综述[J]. 软件学报, 2024, 35(1): 333-355. | |
| [2] |
NI Xueli, MA Zhuo, WANG Qun. Overview of Blockchain Mining Pool Networks and Typical Attack Modes[J]. Computer Engineering, 2024, 50(1): 17-29.
doi: 10.19678/j.issn.1000-3428.0068203 |
|
倪雪莉, 马卓, 王群. 区块链矿池网络及典型攻击方式综述[J]. 计算机工程, 2024, 50(1): 17-29.
doi: 10.19678/j.issn.1000-3428.0068203 |
|
| [3] | HE Shijie. Research on DNS Covert Tunnels in APT Attacks[D]. Chengdu: Southwest Jiaotong University, 2019. |
| 贺诗洁. APT攻击中的DNS隐蔽隧道技术研究[D]. 成都: 西南交通大学, 2019. | |
| [4] | GU Guomin, CHEN Wenhao, HUANG Weida. A Covert Tunnel and Encrypted Malicious Traffic Detection Method Based on Multi-Model Fusion[J]. Netinfo Security, 2024, 24(5): 694-708. |
| 顾国民, 陈文浩, 黄伟达. 一种基于多模型融合的隐蔽隧道和加密恶意流量检测方法[J]. 信息网络安全, 2024, 24(5): 694-708. | |
| [5] |
MANI G, KIM M, BHARGAVA B, et al. Malware Speaks! Deep Learning Based Assembly Code Processing for Detecting Evasive Cryptojacking[J]. IEEE Transactions on Dependable and Secure Computing, 2024, 21(4): 2461-2477.
doi: 10.1109/TDSC.2023.3307445 URL |
| [6] |
DONG Fanghe, SHI Qiong, SHI Zhibin. Adversarial Traffic Detection Method Based on Ensemble Learning and Anomaly Detection[J]. Computer Engineering, 2026, 52(2): 275-286.
doi: 10.19678/j.issn.1000-3428.0069846 |
|
董方和, 石琼, 师智斌. 基于集成学习与异常检测的对抗流量检测方法[J]. 计算机工程, 2026, 52(2): 275-286.
doi: 10.19678/j.issn.1000-3428.0069846 |
|
| [7] | SUN Haoran. Research and Implementation of Mining Traffic Detection System for Campus Network[D]. Beijing: Beijing University of Posts and Telecommunications, 2024. |
| 孙浩然. 面向校园网的挖矿流量检测系统的研究与实现[D]. 北京: 北京邮电大学, 2024. | |
| [8] | LIANG Fei, FANG Ruobing, WANG Kai. Detection of Illegal Bitcoin Transactions Based on Variational Bayesian Network[EB/OL]. [2025-07-08]. https://www.doc88.com/p-39999494179531.html. |
| 梁飞, 方若冰, 王凯. 基于变分贝叶斯图神经网络检测比特币非法交易的技术[EB/OL]. [2025-07-08]. https://www.doc88.com/p-39999494179531.html. | |
| [9] | WANG Gang, GAO Yunpeng, YANG Songru, et al. A Survey on Deep Learning-Based Encrypted Malicious Traffic Detection Methods[J]. Netinfo Security, 2025, 25(8): 1276-1301. |
| 王钢, 高雲鹏, 杨松儒, 等. 基于深度学习的加密恶意流量检测方法研究综述[J]. 信息网络安全, 2025, 25(8): 1276-1301. | |
| [10] |
SANDA O, PAVLIDIS M, POLATIDIS N. A Deep Learning Approach for Host-Based Cryptojacking Malware Detection[J]. Evolving Systems, 2024, 15(1): 41-56.
doi: 10.1007/s12530-023-09534-9 |
| [11] | KADHUM L M, FIRDAUS A, HISHAM S I, et al. Features, Analysis Techniques, and Detection Methods of Cryptojacking Malware: A Survey[J]. International Journal on Informatics Visualization, 2024, 8(2): 891-896. |
| [12] | CHAHOKI A Z, SHAHRIARI H R, ROVERI M. Demo-Unmasking the Unseen: CryptojackingTrap, the Most Resilient Evasion-Proof Cryptojacking Malware Detection Algorithm[C]// IEEE. 2024 IEEE International Workshop on Information Forensics and Security (WIFS). New York: IEEE, 2024: 1-4. |
| [13] | LIU Renting, ZHENG Yahong, ZHANG Yingmin, et al. Detection and Practice of Cryptomining Behavior Based on Deep Packet Inspection[J]. Experiment Science and Technology, 2024, 22(3): 15-21. |
| 刘仁婷, 郑雅洪, 张映敏, 等. 基于深度流量分析的挖矿行为检测与实践[J]. 实验科学与技术, 2024, 22(3): 15-21. | |
| [14] | WEI Jinxia, HUANG Xizhang, FU Yuhao, et al. Mining Traffic Detection Method Based on Global Feature Learning[J]. Netinfo Security, 2024, 24(10): 1506-1514. |
| 魏金侠, 黄玺章, 付豫豪, 等. 基于全局特征学习的挖矿流量检测方法[J]. 信息网络安全, 2024, 24(10): 1506-1514. | |
| [15] | LIU Fengchun, WANG Zihe, YANG Aimin, et al. Research on the Detection Method of Network Malicious Traffic Based on CPO-BiLSTM-KAN[J]. Electronic Measurement Technology, 2026, 49(1): 70-79. |
| 刘凤春, 王子贺, 杨爱民, 等. 基于CPO-BiLSTM-KAN的网络恶意流量检测方法研究[J]. 电子测量技术, 2026, 49(1): 70-79. | |
| [16] |
ZAREH C A, SHAHRIARI H R, ROVERI M. CryptojackingTrap: An Evasion Resilient Nature-Inspired Algorithm to Detect Cryptojacking Malware[J]. IEEE Transactions on Information Forensics and Security, 2024, 19: 7465-7477.
doi: 10.1109/TIFS.2024.3353072 URL |
| [17] | QIAN Kexiang. Research on Intelligent Analysis Methods for Multi-Layer Anomalous Behavior in Botnets[D]. Beijing: Beijing University of Posts and Telecommunications, 2025. |
| 钱珂翔. 多层僵尸网络异常行为智能分析方法研究[D]. 北京: 北京邮电大学, 2025. | |
| [18] | ZHAO Bo, PENG Junru, WANG Yixuan. Network Security Situation Assessment Method Based on Threat Propagation[J]. Netinfo Security, 2025, 25(6): 843-858. |
| 赵波, 彭君茹, 王一琁. 基于威胁传播的网络安全态势评估方法[J]. 信息网络安全, 2025, 25(6): 843-858. | |
| [19] | LUO Heng, WAN Liang. A Network Traffic Intrusion Detection Method Based on Dynamic Spatio-Temporal Graph Neural Network[EB/OL]. (2025-03-06)[2025-07-08]. https://www.ecice06.com/CN/10.19678/j.issn.1000-3428.0070520. |
| 罗恒, 万良. 基于动态时空图神经网络的网络流量入侵检测方法[EB/OL]. (2025-03-06)[2025-07-08]. https://www.ecice06.com/CN/10.19678/j.issn.1000-3428.0070520. | |
| [20] | SUN Jianwen, ZHANG Bin, SI Nianwen, et al. Lightweight Malicious Traffic Detection Method Based on Knowledge Distillation[J]. Netinfo Security, 2025, 25(6): 859-871. |
| 孙剑文, 张斌, 司念文, 等. 基于知识蒸馏的轻量化恶意流量检测方法[J]. 信息网络安全, 2025, 25(6): 859-871. | |
| [21] | BAI Wuxia. Research on Malicious Traffic Detection Method Based on Generative Adversarial Network[D]. Wuhan: Huazhong University of Science and Technology, 2024. |
| 白无瑕. 基于生成对抗网络的网络恶意流量检测方法研究[D]. 武汉: 华中科技大学, 2024. | |
| [22] | VASUDEVAN A R, STEPHAN J, MOHAMED A E, et al. MinerJAB: CLI-Based Tool for Detection and Mitigation of Host-Based Cryptojacking Malware[C]// IEEE. 2025 6th International Conference on Control, Communication and Computing (ICCC). New York: IEEE, 2025: 1-6. |
| [23] | PAN Xue, YANG Yingkui, LIU Chunxue. Discussion on Virus Analysis and Treatment of no File Mining[J]. Heilongjiang Meteorology, 2022, 39(4): 41-42. |
| 潘雪, 杨英奎, 刘春雪. 浅谈无文件挖矿病毒分析与处理[J]. 黑龙江气象, 2022, 39(4): 41-42. | |
| [24] | GU Huanhuan, LI Qianmu, LIU Zhen, et al. Research on Hidden Backdoor Prompt Attack Methods Based on False Demonstrations[J]. Netinfo Security, 2025, 25(4): 619-629. |
| 顾欢欢, 李千目, 刘臻, 等. 基于虚假演示的隐藏后门提示攻击方法研究[J]. 信息网络安全, 2025, 25(4): 619-629. |
| [1] | HU Wentao, DING Weijie. DiffGuard: Network Traffic Anomaly Detection Based on Diffusion Models and Adaptive Sequence Learning [J]. Netinfo Security, 2026, 26(3): 378-388. |
| [2] | HU Yucui, GAO Haotian, ZHANG Jie, YU Hang, YANG Bin, FAN Xuejian. Automated Exploitation of Vulnerabilities in Vehicle Network Security [J]. Netinfo Security, 2025, 25(9): 1348-1356. |
| [3] | YANG Judong, CHEN Xingshu, ZHU Yi. Research on Covert Transformation Method for Malicious Communication Behavior Based on Packet Length Sequence [J]. Netinfo Security, 2025, 25(5): 794-805. |
| [4] | LI Hailong, CUI Zhian, SHEN Xieyang. Overview of Anomaly Analysis and Detection Methods for Network Traffic [J]. Netinfo Security, 2025, 25(2): 194-214. |
| [5] | ZHANG Xinyou, GAO Zhichao, FENG Li, XING Huanlai. FFT-iTransformer-Based Cybersecurity Situation Awareness Feature Imputation and Prediction [J]. Netinfo Security, 2025, 25(2): 228-239. |
| [6] | YANG Zhipeng, LIU Daidong, YUAN Junyi, WEI Songjie. Research on Network Local Security Situation Fusion Method Based on Self-Attention Mechanism [J]. Netinfo Security, 2024, 24(3): 398-410. |
| [7] | HE Kaiyu, WANG Bin, YU Zhe, CHEN Fang. Research on ARP Spoofing Attack and Hardware Defense [J]. Netinfo Security, 2024, 24(10): 1604-1610. |
| [8] | FU Jing. Exploration and Practice of Security Protection of Critical Information Infrastructure of Water Conservancy [J]. Netinfo Security, 2023, 23(8): 121-127. |
| [9] | SUN Chengcheng. Research on Countermeasures for Network Security Governance [J]. Netinfo Security, 2023, 23(6): 104-110. |
| [10] | LI Dong, YU Junqing, WEN Ruibin, XIE Yiding. Endogenous Security Methods for Container Cloud Based on IPv6 [J]. Netinfo Security, 2023, 23(12): 21-28. |
| [11] | SUN Pengyu, TAN Jinglei, LI Chenwei, ZHANG Hengwei. Network Security Defense Decision-Making Method Based on Time Differential Game [J]. Netinfo Security, 2022, 22(5): 64-74. |
| [12] | JIN Bo, TANG Qianjin, TANG Qianlin. Interpretation of the Top 10 Development Trends of Network Security in 2022 by CCF Computer Security Professional Committee [J]. Netinfo Security, 2022, 22(4): 1-6. |
| [13] | CHEN Yan, WEI Xiang, LU Zhen. Research on Testing Approaches for Network Security Products in Cloud Computing Environment [J]. Netinfo Security, 2022, 22(12): 1-6. |
| [14] | BAI Hongpeng, DENG Dongxu, XU Guangquan, ZHOU Dexiang. Research on Intrusion Detection Mechanism Based on Federated Learning [J]. Netinfo Security, 2022, 22(1): 46-54. |
| [15] | GU Zhaojun, YAO Feng, DING Lei, SUI He. Network Security Test of Airport Fuel Supply Automatic Control System Based on Semi-physical Object [J]. Netinfo Security, 2021, 21(9): 16-24. |
| Viewed | ||||||
|
Full text |
|
|||||
|
Abstract |
|
|||||