| [1] |
CHASE M, MIAO Peihan. Private Set Intersection in the Internet Setting from Lightweight Oblivious PRF[C]// IACR. Advances in Cryptology-CRYPTO 2020: The 40th Annual International Cryptology Conference. Heidelberg: Springer, 2020: 34-63.
|
| [2] |
PINKAS B, ROSULEK M, TRIEU N, et al. PSI from PaXoS:Fast, Malicious Private Set Intersection[C]// IACR. Annual International Conference on the Theory and Applications of Cryptographic Techniques. Heidelberg: Springer, 2020: 739-767.
|
| [3] |
RINDAL P, SCHOPPMANN P. VOLE-PSI: Fast OPRF and Circuit-PSI from Vector-OLE[C]// IACR. Annual International Conference on the Theory and Applications of Cryptographic Techniques. Heidelberg: Springer, 2021: 901-930.
|
| [4] |
ELKORDY A R, EZZELDIN Y H, AVESTIMEHR S. Federated K-Private Set Intersection[C]// ACM. The 31st ACM International Conference on Information & Knowledge Management. New York: ACM, 2022: 436-445.
|
| [5] |
LU Linpeng, DING Ning. Multi-Party Private Set Intersection in Vertical Federated Learning[C]// IEEE. 2020 IEEE 19th International Conference on Trust, Security and Privacy in Computing and Communications. New York: IEEE, 2020: 707-714.
|
| [6] |
GHOSH S, NILGES T. An Algebraic Approach to Maliciously Secure Private Set Intersection[C]// IACR. Annual International Conference on the Theory and Applications of Cryptographic Techniques. Heidelberg: Springer, 2019: 154-185.
|
| [7] |
NGUYEN D T, TRIEU N. MPCCache: Privacy-Preserving Multi-Party Cooperative Cache Sharing at the Edge[C]// IFCA. International Conference on Financial Cryptography and Data Security. Heidelberg: Springer, 2022: 80-99.
|
| [8] |
MIYAJI A, NISHIDA S. A Scalable Multiparty Private Set Intersection[C]// Springer. International Conference on Network and System Security. Heidelberg: Springer, 2015: 376-385.
|
| [9] |
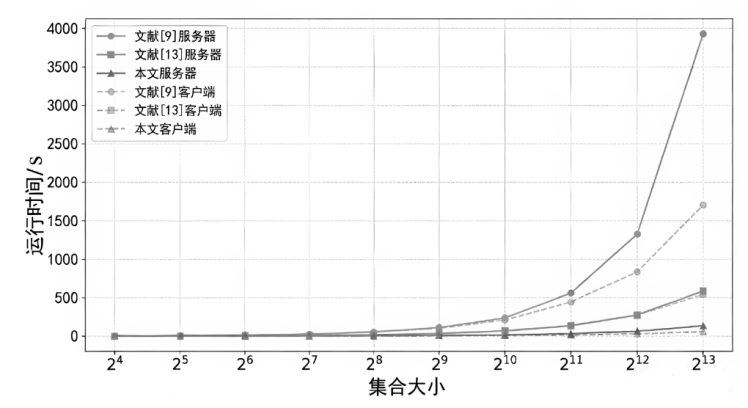
BAY A, ERKIN Z, HOEPMAN J H, et al. Practical Multi-Party Private Set Intersection Protocols[J]. IEEE Transactions on Information Forensics and Security, 2021, 17: 1-15.
doi: 10.1109/TIFS.2021.3118879
URL
|
| [10] |
DAVIDSON A, CID C. An Efficient Toolkit for Computing Private Set Operations[C]// Springer. Information Security and Privacy:The 22nd Australasian Conference. Heidelberg: Springer, 2017: 261-278.
|
| [11] |
VOS J, CONTI M, ERKIN Z. Fast Multi-Party Private Set Operations in the Star Topology from Secure ANDs and ORs[EB/OL]. (2022-07-21)[2025-02-17]. https://eprint.iacr.org/2022/721.pdf.
|
| [12] |
RUAN Ou, AI Chaohao. An Efficient Multi-Party Private Set Intersection Protocols Based on Bloom Filter[C]// Karpagam College of Engineering. The Second International Conference on Algorithms, Microchips, and Network Applications. Bellingham: SPIE, 2023: 282-287.
|
| [13] |
RUAN Ou, YAN Changwang, ZHOU Jing, et al. A Practical Multiparty Private Set Intersection Protocol Based on Bloom Filters for Unbalanced Scenarios[EB/OL]. (2023-12-13)[2025-02-17]. https://www.mdpi.com/2076-3417/13/24/13215.
|
| [14] |
GAO Ying, LUO Yuanchao, WANG Longxin, et al. Efficient Scalable Multi-Party Private Set Intersection (-Variants) from Bicentric Zero-Sharing[C]// ACM. The 2024 on ACM SIGSAC Conference on Computer and Communications Security. New York: ACM, 2024: 4137-4151.
|
| [15] |
KOLESNIKOV V, MATANIA N, PINKAS B, et al. Practical Multi-Party Private Set Intersection from Symmetric-Key Techniques[C]// ACM. The 2017 ACM SIGSAC Conference on Computer and Communications Security. New York: ACM, 2017: 1257-1272.
|
| [16] |
INBAR R, OMRI E, PINKAS B. Efficient Scalable Multiparty Private Set-Intersection via Garbled Bloom Filters[C]// IACR. International Conference on Security and Cryptography for Networks. Heidelberg: Springer, 2018: 235-252.
|
| [17] |
DONG Changyu, CHEN Liqun, WEN Zikai. When Private Set Intersection Meets Big Data: An Efficient and Scalable Protocol[C]// ACM.The 2013 ACM SIGSAC Conference on Computer and Communications Security. New York: ACM, 2013: 789-800.
|
| [18] |
NEVO O, TRIEU N, YANAI A. Simple, Fast Malicious Multiparty Private Set Intersection[C]// ACM. The 2021 ACM SIGSAC Conference on Computer and Communications Security. New York: ACM, 2021: 1151-1165.
|
| [19] |
WU Mingli, YUEN T H, CHAN K Y. O-Ring and K-Star: Efficient Multi-Party Private Set Intersection[C]// USENIX. The 33rd USENIX Security Symposium. Berkeley: USENIX, 2024: 6489-6506.
|
| [20] |
BLOOM B H. Space/Time Trade-Offs in Hash Coding with Allowable Errors[J]. Communications of the ACM, 1970, 13(7): 422-426.
doi: 10.1145/362686.362692
URL
|
| [21] |
ELGAMAL T. A Public Key Cryptosystem and a Signature Scheme Based on Discrete Logarithms[J]. IEEE Transactions on Information Theory, 1985, 31(4): 469-472.
doi: 10.1109/TIT.1985.1057074
URL
|
| [22] |
KATZ J, LINDELL Y. Introduction to Modern Cryptography: Principles and Protocols[M]. New York: Chapman and Hall/CRC, 2007.
|
| [23] |
KOLESNIKOV V, KUMARESAN R, ROSULEK M, et al. Efficient Batched Oblivious PRF with Applications to Private Set Intersection[C]// ACM. The 2016 ACM SIGSAC Conference on Computer and Communications Security. New York: ACM, 2016: 818-829.
|
| [24] |
EVANS D, KOLESNIKOV V, ROSULEK M. A Pragmatic Introduction to Secure Multi-Party Computation[J]. Foundations and Trends in Privacy and Security, 2018, 2(2-3): 70-246.
doi: 10.1561/SEC
URL
|
| [25] |
CANETTI R. Security and Composition of Multiparty Cryptographic Protocols[J]. Journal of Cryptology, 2000, 13: 143-202.
doi: 10.1007/s001459910006
URL
|
| [26] |
KOLESNIKOV V, KUMARESAN R. Improved OT Extension for Transferring Short Secrets[C]// IACR. Advances in Cryptology-CRYPTO 2013-The 33rd Annual Cryptology Conference. Heidelberg: Springer, 2013: 54-70.
|
| [27] |
ASHAROV G, LINDELL Y, SCHNEIDER T, et al. More Efficient Oblivious Transfer and Extensions for Faster Secure Computation[C]// ACM. The 2013 ACM SIGSAC Conference on Computer and Communications Security. New York: ACM, 2013: 535-548.
|
 )
)