Netinfo Security ›› 2021, Vol. 21 ›› Issue (1): 88-96.doi: 10.3969/j.issn.1671-1122.2021.01.011
Research on Authentication and Key Agreement Method of IMS-based Mobile Communication Private Network
DONG Qiang1, LUO Guoming1, SHI Hongkui2, ZHANG Yongyue3( )
)
- 1. Institute of Communication Engineering, Army Engineering University of PLA, Nanjing 210042, China
2. Nanjing University of Posts and Telecommunications, Nanjing 210023, China
3. Tianjin Municipal Big Data Administration Center, Tianjin 300221, China
-
Received:2020-11-20Online:2021-01-10Published:2021-02-23 -
Contact:ZHANG Yongyue E-mail:zyy_xp@126.com
CLC Number:
Cite this article
DONG Qiang, LUO Guoming, SHI Hongkui, ZHANG Yongyue. Research on Authentication and Key Agreement Method of IMS-based Mobile Communication Private Network[J]. Netinfo Security, 2021, 21(1): 88-96.
share this article
Add to citation manager EndNote|Ris|BibTeX
URL: http://netinfo-security.org/EN/10.3969/j.issn.1671-1122.2021.01.011
| 端到端类 文献方案 | 数学 基础 | RTT | 主叫端开销 | 被叫端开销 | 主叫端 估时 | 被叫端 估时 |
|---|---|---|---|---|---|---|
| [7] | DLP | 2.5 | 2RNG+2EXPO+ 2ENCB+3DNCB | 2RNG+2EXPO+ 3ENCB+2DNCB | 8.801 | 8.801 |
| [22] | RSA | 4 | SIGN+SEVR | SIGN+SEVR | 4.0425 | 4.0425 |
| [10] | 双线 性对 | 2 | RNG+2PAIRING+EXPO+ HMAC+H1+2PM | RNG+2PAIRING+ EXPO+HMAC+H1+2PM | 21.4146 | 21.4146 |
| [11](使用SAS) | DLP/ECDLP | 5 | RNG+2EXPO+ 4H+MAAU | RNG+2EXPO+ 4H+MAAU | >104 | >104 |
| [11](使用rs) | HASH | 3 | H+3HMAC | H+3HMAC | 0.0161 | 0.0161 |
| [15] | DLP | 3 | 2RNG+2EXPO+5HMAC+ SIGN+SVER | 2RNG+2EXPO+5HMAC+ SIGN+SVER | 12.8435 | 12.8435 |
| 端到服务器类文献方案 | 数学 基础 | RTT | 用户端开销 | 服务器端开销 | 用户端估时 | 服务器端估时 |
|---|---|---|---|---|---|---|
| [18] | ECDLP | 2 | 2H+2PM+RNG+PA | 2H+2PM+ RNG+PA | 5.0244 | 5.0244 |
| [19] | DLP | 1.5 | RNG+2PM+ENCB+4H | RNG+2PM+ DNCB+5H | 5.0048 | 5.0071 |
| [20] | HASH | 1.5 | RNG+3CHEV+5H | RNG+3CHEV+5H | 2.7765 | 2.7765 |
| [21] | DLP | 2 | 2RNG+EXPO+4H | 2RNG+2EXPO+4H | 16.4872 | 8.7872 |
| [23] | HASH | Y | 6H+RNG | HA开销:10H FA开销:RNG+10H | 0.5528 | 0.585 |
| [1] | LIANG Xuemei, FANG Xiaonong, YANG Shuo, et al. IMS Technology in Industry Private Network[M]. Beijing: Posts & Telecom Press Co.,LTD, 2016. |
| 梁雪梅, 方晓农, 杨硕, 等. IMS技术行业专网应用[M]. 北京: 人民邮电出版社, 2016. | |
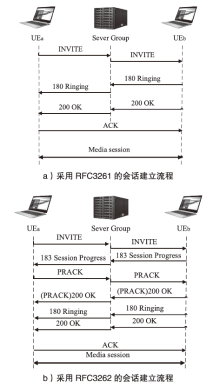
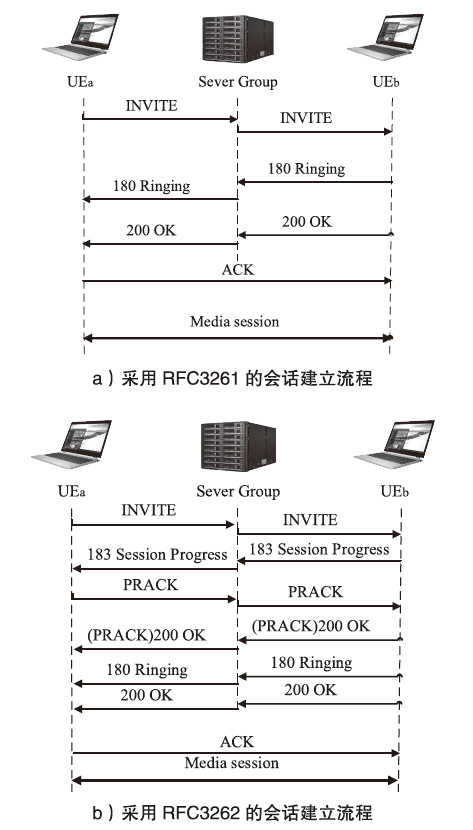
| [2] | ROSENBERG J, SCHULZRINNE H. IETF RFC3261 SIP: Session Initiation Protocol[EB/OL]. https://tools.ietf.org/pdf/rfc3261.pdf, 2020-10-08. |
| [3] | GU Xiaohui, SHI Jiajia, GUO Fang. Security Mechanism of SIP and Improvement of HTTP Digest Authentication[J]. Journal of Donghua University(Natural Science), 2010,36(2):165-169. |
| 顾晓辉, 施佳佳, 郭放. SIP的安全机制及其HTTP摘要认证的改进[J]. 东华大学学报(自然科学版), 2010,36(002):165-169. | |
| [4] | QIANG Lei, RAO Shaoyang, CHEN Hui, et al. IMS Core Principle and Application[M]. Beijing: Posts & Telecom Press Co., LTD, 2008. |
| 强磊, 饶少阳, 陈卉, 等. IMS核心原理与应用[M]. 北京: 人民邮电出版社, 2008. | |
| [5] | ROSENBERG J, SCHULZRINNE H. IETF RFC3262 Reliability of Provisional Responses in the Session Initiation Protocol (SIP)[EB/OL]. https://tools.ietf.org/pdf/rfc3262.pdf, 2020-10-08. |
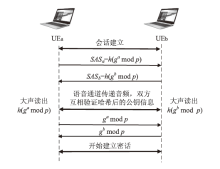
| [6] | DONG Qiang, LUO Guoming, ZHU Lei, et al. Research on SIP Based Key Distribution Method of Private Mobile Communication System[J]. Command Control & Simulation, 2020,42(4):111-116. |
| 董锵, 罗国明, 朱磊, 等. 基于SIP的专用移动通信系统密钥分发方法[J]. 指挥控制与仿真, 2020,42(4):111-116. | |
| [7] | BELLOVIN S M. Encrypted Key Exchange: Password-based Protocols Secure Against Dictionary Attacks[C] // IEEE. Proc IEEE Symposium on Security & Privacy, May 4-6, 1992, Oakland, CA, USA. USA: IEEE Computer Society, 1992: 72-84. |
| [8] | ZUO Liming, CHEN Lanlan. Special Digital Signature Scheme Based on Identity Identification and It’s Application[J]. Computer Science, 2020,47(1):309-314. |
| 左黎明, 陈兰兰. 基于身份标识的特殊数字签名方案及其应用[J]. 计算机科学, 2020,47(1):309-314. | |
| [9] | Al-Riyami S S, PATERSON K G. Certificateless Public Key Cryptography[C] // Springer. Proceedings of International Conference on the Theory and Application of Cryptology and Information Security, January 1-4, 2003,Berlin, Germany: Springer, 2003: 452-473. |
| [10] | XU Ping, ZHANG Fangzhou, ZHANG Xiaoyu, et al. End to End Key Agreement Protocol Based on Mobile Network[J]. Journal of Northeast Petroleum University, 2012,36(4):74-78. |
| 徐平, 张方舟, 张晓宇, 等. 基于移动网络的端到端密钥协商协议[J]. 东北石油大学学报, 2012,36(4):74-78. | |
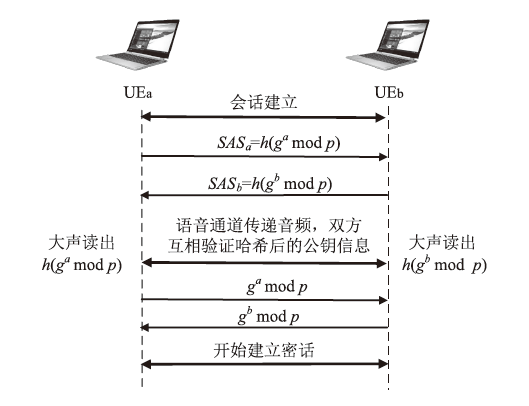
| [11] | ZIMMERMANN P, JOHNSTON A, CALLAS J. IETF RFC 6189 ZRTP: Media Path Key Agreement for Unicast Secure RTP[EB/OL]. https://tools.ietf.org/pdf/rfc6189.pdf, 2020-10-08. |
| [12] | BAUGHER M, MCGREW D, NASLUND M. IETF RFC 3711 The Secure Real-time Transport Protocol (SRTP)[EB/OL]. https://tools.ietf.org/pdf/rfc3711.pdf, 2020-10-08. |
| [13] | KRAWCZYK H. SIGMA: The 'SIGn-and-MAc' Approach to Authenticated Diffie-Hellman and Its Use in the IKE Protocols[J]. Proc of Crypto, 2003,2729(2):400-425. |
| [14] |
NIKANDER P, GURTOV A, HENDERSON T R. Host Identity Protocol (HIP): Connectivity, Mobility, Multi-Homing, Security, and Privacy over IPv4 and IPv6 Networks[J]. IEEE Communications Surveys & Tutorials, 2010,12(2):186-204.
doi: 10.1109/SURV.2010.021110.00070 URL |
| [15] |
PECORI R, VELTRI L. 3AKEP: Triple-authenticated Key Exchange Protocol for Peer-to-peer VoIP Applications[J]. Computer Communications, 2016,85(1):28-40.
doi: 10.1016/j.comcom.2016.04.005 URL |
| [16] | ARKKO J, CARRARA E, LINDHOLM F. IETF RFC 3830 MIKEY: Multimedia Internet KEYing [EB/OL]. https://tools.ietf.org/pdf/rfc3830.pdf, 2020-10-08. |
| [17] |
KILINC H H, YANIK T. A Survey of SIP Authentication and Key Agreement Schemes[J]. IEEE Communications Surveys & Tutorials, 2014,16(2):1005-1023.
doi: 10.1109/SURV.2013.091513.00050 URL |
| [18] | YOON E J, YOO KY. A New Authentication Scheme for Session Initiation Protocol[C] //IEEE. 2009 International Conference on Complex, Intelligent and Software Intensive Systems, March 16-19, 2009, Fukuoka, Japan. Japan: IEEE, 2009: 549-554. |
| [19] |
ISLAM S H, VIJAYAKUMAR P, BHUIYAN M Z A, et al. A Provably Secure Three-factor Session Initiation Protocol for Multimedia Big Data Communications[J]. IEEE Internet of Things Journal, 2018,5(5):3408-3418.
doi: 10.1109/JIoT.6488907 URL |
| [20] | GUO Xiangyu, SUN Dazhi, YANG Ying. An Improved Three-factor Session Initiation Protocol Using Chebyshev Chaotic Map [EB/OL]. https://ieeexplore.ieee.org/stamp/stamp.jsp?tp=&arnumber=9117092, 2020-06-26. |
| [21] | CAI Dazhuang. Research and Design of a Security Mechanism for IMS Access Layer[D]. Shenyang: Shenyang Institute of Computing Technology of Chinese Academy of Sciences, 2015. |
| 才大壮. IMS接入侧安全机制的研究与设计[D]. 沈阳:中国科学院研究生院(沈阳计算技术研究所), 2015. | |
| [22] | KONG L, BALASUBRAMANIYAN V B, AHAMAD M. A Lightweight Scheme for Securely and Reliably Locating SIP Users[C] // IEEE. IEEE Workshop on VoIP Management & Security. April 3-7, 2006, Vancouver, BC, Canada. Canada: IEEE, 2006: 8-16. |
| [23] |
GOPE P, HWANG T. Lightweight and Energy-efficient Mutual Authentication and Key Agreement Scheme With User Anonymity for Secure Communication in Global Mobility Networks[J]. IEEE Systems Journal, 2016,10(4):1-10.
doi: 10.1109/JSYST.2016.2528398 URL |
| [1] | YU Guo, WANG Chonghua, CHEN Xuehong, LI Jun. Industrial Internet Identifier Resolution Security from the Perspective of Authentication [J]. Netinfo Security, 2020, 20(9): 77-81. |
| [2] | WANG Li, LI Erxia, JI Yuchen, LI Xiaoyong. PUF-based Anti-physical Cloning RFID Security Authentication Protocol [J]. Netinfo Security, 2020, 20(8): 89-97. |
| [3] | ZHANG Xiao, LIU Jiqiang. Multi-factor Authentication Protocol Based on Hardware Fingerprint and Biometrics [J]. Netinfo Security, 2020, 20(8): 9-15. |
| [4] | SUN Ziwen, ZHANG Xiangyang. Large-scale Mobile RFID System Shamir’s Key Sharing PUF Security Authentication Protocol [J]. Netinfo Security, 2020, 20(6): 26-35. |
| [5] | LIU Xiaofen, CHEN Xiaofeng, LIAN Guiren, LIN Song. Authenticated Multiparty Quantum Secret Sharing Protocol with d-level Single Particle [J]. Netinfo Security, 2020, 20(3): 51-55. |
| [6] | HOU Lin, FENG Da, XUAN Pengkai, ZHOU Fucai. Outsourcing Database Join Query Verification Scheme Based on Authentication Tree [J]. Netinfo Security, 2020, 20(2): 91-97. |
| [7] | ZHAO Guofeng, ZHOU Wentao, XU Chuan, XU Lei. A Secure Identity Authentication Scheme for Space-ground Integrated Network Based on Bilinear Pairing [J]. Netinfo Security, 2020, 20(12): 33-39. |
| [8] | YU Beiyuan, LIU Jianwei, ZHOU Ziyu. Research on Node Authentication Mechanism in Self-organizing Network Environment [J]. Netinfo Security, 2020, 20(12): 9-18. |
| [9] | ZHANG Zheng, ZHA Daren, LIU Yanan, FANG Xuming. PUF-based Kerberos Extension Protocol with Formal Analysis [J]. Netinfo Security, 2020, 20(12): 91-97. |
| [10] | LIU Lijuan, LI Zhihui, ZHI Danli. A Multi-party Quantum Key Distribution Protocol with Quantum Identity Authentication [J]. Netinfo Security, 2020, 20(11): 59-66. |
| [11] | CHENG Yang, LEI Min, LUO Qun. Access Authentication Method for IoT Terminal Devices Based on Deep Learning [J]. Netinfo Security, 2020, 20(11): 67-74. |
| [12] | HU Die, MA Dongtang, GONG Ming, MA Zhao. A Physical Layer Security Authentication Method Based on PUF [J]. Netinfo Security, 2020, 20(1): 61-66. |
| [13] | Fuyou ZHANG, Qiongxiao WANG, Li SONG. Research on Unified Identity Authentication System Based on Biometrics [J]. Netinfo Security, 2019, 19(9): 86-90. |
| [14] | Baoyuan KANG, Mingming XIE, Lin SI. Research on a Biometrics-based Multi-cloud Server Authentication Scheme [J]. Netinfo Security, 2019, 19(6): 45-52. |
| [15] | Ruiying CHEN, Zemao CHEN, Hao WANG. Design and Optimization of Security Monitoring and Controlling Protocol in Industrial Control Systems [J]. Netinfo Security, 2019, 19(2): 60-69. |
| Viewed | ||||||
|
Full text |
|
|||||
|
Abstract |
|
|||||