信息网络安全 ›› 2026, Vol. 26 ›› Issue (3): 355-366.doi: 10.3969/j.issn.1671-1122.2026.03.002
网络靶场研究进展
- 江苏警官学院计算机信息与网络安全系,南京 210031
-
收稿日期:2025-08-06出版日期:2026-03-10发布日期:2026-03-30 -
通讯作者:王群 E-mail:wangqun@jspi.edu.cn -
作者简介:李馥娟(1974—),女,陕西,教授,硕士,主要研究方向为网络空间安全|王群(1971—),男,甘肃,教授,博士,CCF杰出会员,主要研究方向为网络空间安全 -
基金资助:国家自然科学基金(61802155);国家自然科学基金(62272209)
Research Progress of Cyber Ranges
- Department of Computer Information and Cyber Security, Jiangsu Police Institute, Nanjing 210031, China
-
Received:2025-08-06Online:2026-03-10Published:2026-03-30
摘要:
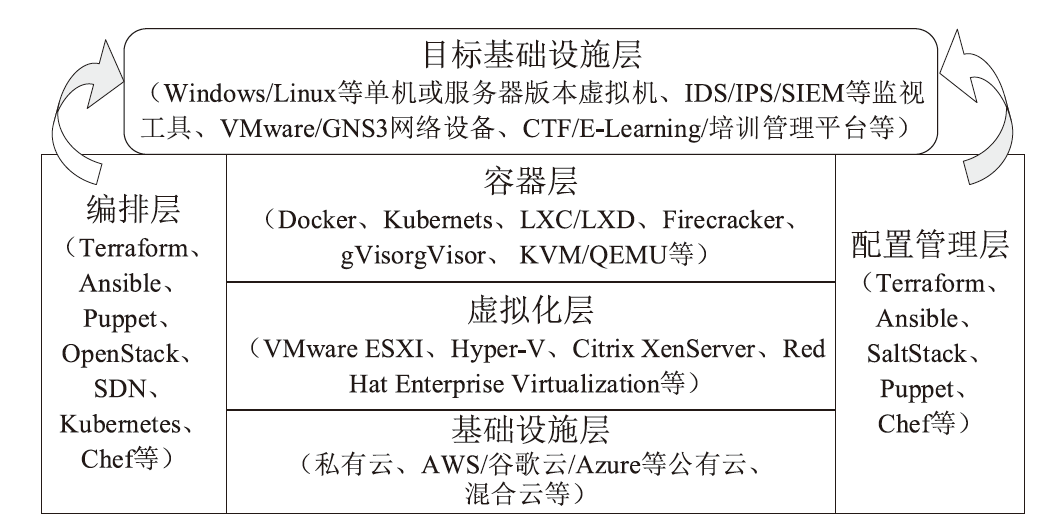
网络靶场作为网络空间安全研究的核心实验平台,通过构建可控、可复现的虚拟化攻防环境,为安全技术验证、人才培养及攻防演练提供了关键支撑。文章系统梳理了网络靶场的发展脉络,从美国NCR、欧洲CRF到日本StarBED,展现了从单一功能平台向联邦协同架构的演进历程,同时阐述了国内网络靶场从技术验证到协同创新的跨越式发展路径。在技术架构方面,网络靶场呈现多层级体系特征,涵盖基础设施层、虚拟化层、容器层等核心组件,通过虚拟化与仿真技术实现高保真环境构建。关键技术聚焦于场景生成与对抗、跨域协同及自动化评估3大方向,形成了完整的技术支撑体系。研究表明,网络靶场已从静态仿真容器升级为动态能力生成平台,应用场景拓展至联邦态势感知、供应链安全溯源等领域。
中图分类号:
引用本文
李馥娟, 王群. 网络靶场研究进展[J]. 信息网络安全, 2026, 26(3): 355-366.
LI Fujuan, WANG Qun. Research Progress of Cyber Ranges[J]. Netinfo Security, 2026, 26(3): 355-366.
表1
4类典型网络靶场对比分析
| 名称 | 启用 时间 | 主导模式 | 核心技术 | 关键能力 | 规模指标 | 创新 特点 |
|---|---|---|---|---|---|---|
| 美国NCR | 2008年 | 政府主导、军民融合 | 联邦学习、数字孪生 | 网络武器测试、作战训练 | 多节点互联综合体 | 自动化评估 体系 |
| 欧洲CRF | 2013年(CD TEXP) | 多国协同、区域合作 | 联邦学习、动态蜜网 | 跨国防务演练、关基防护 | 万级虚拟节点 | CRF成熟度 模型 |
| 日本StarBED | 2002年 | 研发机构主导、产学研结合 | 时序精确仿真、SDN/NFV | 协议验证、设备测试 | 大规模拓扑模拟 | 量子安全测试 |
| 中国鹏城靶场 | 2009年 | 国家队引领、生态共建 | 联邦学习、快速组网 | 实战演练、人才培养 | 百万节点级仿真 | 联邦靶场生态 |
表1
表2
典型网络靶场主要功能描述
| 功能 | 描述 |
|---|---|
| 网络安全人才培养 | 通过场景化实战训练,提升岗位匹配度,弥补技能短板,缓解人才缺口 |
| 赋能技能迭代 | 依托动态训练模块,支持安全人员持续学习前沿防御策略与新型攻防技术 |
| 构建隔离的实验环境 | 基于虚拟化与网络隔离技术,提供可复用、安全可控的实验空间,避免影响真实系统 |
| 事件响应能力建设 | 模拟多种网络安全事件场景,强化预案执行与标准化操作,提升实战响应能力 |
| 紧跟威胁演化态势 | 实时同步新兴威胁情报与技术,帮助安全人员动态更新知识体系,做好前瞻准备 |
| 支撑精准化绩效评估 | 通过量化指标与多维度反馈,科学评估安全能力,定位薄弱环节,优化培训效果 |
| 模拟实战化技能训练 | 在隔离环境中复现真实攻击场景,积累实战经验,提升应对真实威胁的能力 |
| 专业技能培养 | 围绕威胁检测、防御部署、应急处置等环节,打磨专项技能与动态防御能力 |
| 培养团队协作能力 | 在复杂攻击场景中提供跨角色协同演练平台,提升团队信息共享与整体响应效率 |
| 赋能技术研发与验证 | 提供测试环境,支持安全工具与防护方案的研发、评估与持续优化 |
表2
表3
不同类型网络靶场的对比
| 类型 | 关键技术 | 主要功能 | 典型应用 |
|---|---|---|---|
| 教育训练型靶场 | 动态场景构建:基于模块化与漏洞库,支持从基础漏洞到APT攻击的灵活编排;能力量化评估:通过行为与图推理算法,实现多阶能力的自动化评测 | 构建基础、进阶、高阶三级培养体系,集成微课、虚拟演练、CTF等模块,支持教学管理与智能纠错 | 高校实验平台、企业认证体系,用于实操能力考核 |
| 竞赛竞技型靶场 | 零信任隔离:通过覆盖网络与微分段实现多租户攻击域隔离;动态评分引擎:基于ATT&CK框架与防御效能量化,支持多模式切换 | 可信保障:区块链存证与反作弊引擎;动态对抗:攻击流量自适应生成 | 国际/国家级赛事、新兴威胁演练平台 |
| 科研实验型靶场 | 数字孪生:多模态网络仿真架构;威胁演化引擎:支持APT攻击链的动态建模 | 高精度控制:可编程网络损伤;深度可观测:全栈流量捕获与检测接口 | 军事仿真推演、攻击机理研究、新型威胁复现 |
| 行业应用型靶场 | 行业协议仿真:专用协议仿真引擎;业务影响模型:量化业务中断的经济损失与时间 | 业务逻辑集成:深度复现行业系统;高保真场景:模拟特有攻击向量 | 工控安全靶场(如电网)、金融核心系统验证平台 |
表3
表4
虚拟化与仿真涉及的3类关键技术对比分析
| 名称 | 技术定位 | 主要功能 | 主要角色 | 主要优势 | 面临挑战 |
|---|---|---|---|---|---|
| 边缘计算与5G网络 集成 | 提供低时延、高带宽的网络与分布式算力 | 数据本地处理、网络切片、实时响应 | 为高实时性靶场提供通信与算力 基础 | 延迟低、减轻核心网压力、提升场景真实感 | 初始成本高、技术集成复杂 |
| 数字 孪生 | 构建物理实体的虚拟镜像,支持数据驱动的仿真与决策 | 高保真建模、攻防策略验证、过程可视化与评估 | 作为靶场核心仿真引擎,支撑场景复现与 推演 | 全面的数字映射、支持复杂推演预测、可量化评估 | 建模精度与实时性难兼顾、多源数据融合难、对算力数据要求高 |
| 混合虚拟化 架构 | 融合多种虚拟化技术,实现资源高效隔离与 调度 | 动态算力卸载、多层次安全隔离、异构设备 仿真 | 作为靶场资源管理基石,支撑异构环境灵活构建 | 性能与灵活性兼备、资源利用率高、弹性 伸缩 | 跨层调度管理复杂、安全隔离策略设计难度大 |
表4
| [1] | LI Qiuxiang, HAO Wenjiang, LI Cuicui, et al. Present Situation and Enlightenment of the Foreign Network Range Technology[J]. Netinfo Security, 2014, 14(9): 63-68. |
| 李秋香, 郝文江, 李翠翠, 等. 国外网络靶场技术现状及启示[J]. 信息网络安全, 2014, 14(9): 63-68. | |
| [2] |
LI Fujuan, WANG Qun. Research on Cyber Ranges and Its Key Technologies[J]. Computer Engineering and Applications, 2022, 58(5): 12-22.
doi: 10.3778/j.issn.1002-8331.2109-0137 |
|
李馥娟, 王群. 网络靶场及其关键技术研究[J]. 计算机工程与应用, 2022, 58(5): 12-22.
doi: 10.3778/j.issn.1002-8331.2109-0137 |
|
| [3] | FERGUSON B, TALL A, OLSEN D. National Cyber Range Overview[C]// IEEE. 2014 IEEE Military Communications Conference. New York: IEEE, 2014: 123-128. |
| [4] | FANG Binxing. Improving Cyberspace Security Situation from Perspective of “Talent, Finance and Infrastructure”[J]. Bulletin of Chinese Academy of Sciences, 2022, 37(1): 53-59. |
| 方滨兴. 从“人、财、物”视角出发,提升网络空间的安全态势[J]. 中国科学院院刊, 2022, 37(1): 53-59. | |
| [5] | ZHANG Jiawei, LI Zongzhe, CHEN Rui, et al. A Survey of Cyber Range: Current Status, Analysis, and Future Trends[C]// Springer. Network Simulation and Evaluation. Heidelberg: Springer, 2024: 88-101. |
| [6] | YAMIN M M, KATT B, GKIOULOS V. Cyber Ranges and Security Testbeds: Scenarios, Functions, Tools and Architecture[EB/OL]. (2019-10-07)[2025-07-09]. https://doi.org/10.1016/j.cose.2019.101636. |
| [7] | LINARDOS V. Development of a Cyber Range Platform[D]. Piraeus: University of Piraeus, 2021. |
| [8] | STAMATOPOULOS D, KATSANTONIS M, FOULIRAS P, et al. Exploring the Architectural Composition of Cyber Ranges: A Systematic Review[EB/OL]. (2024-06-28)[2025-07-09]. https://doi.org/10.3390/fi16070231. |
| [9] | NIST. Cyber Ranges[EB/OL]. (2018-02-13)[2025-07-09]. https://www.nist.gov/system/files/documents/2018/02/13/cyber_ranges.pdf. |
| [10] | ECSO. Understanding Cyber Ranges: From Hype to Reality[EB/OL]. (2020-03-01)[2025-07-09]. https://ecs-org.eu/ecso-uploads/2023/05/2020_SWG-5.1_paper_UnderstandingCyberRanges_final_v1.0-update.pdf. |
| [11] | LILLEMETS P, BASHIR J N, KASHI J, et al. A Systematic Review of Cyber Range Taxonomies: Trends, Gaps, and a Proposed Taxonomy[EB/OL]. (2025-05-05)[2025-07-09]. https://doi.org/10.3390/fi17060259. |
| [12] | CHOULIARAS N, KITTES G, KANTZAVELOU I, et al. Cyber Ranges and TestBeds for Education, Training, and Research[EB/OL]. (2021-02-18)[2025-07-09]. https://doi.org/10.3390/app11041809. |
| [13] |
KATSANTONIS M N, MANIKAS A, MAVRIDIS I, et al. Cyber Range Design Framework for Cyber Security Education and Training[J]. International Journal of Information Security, 2023, 22(4): 1005-1027.
doi: 10.1007/s10207-023-00680-4 |
| [14] | CIUPERCA E, STANCIU A, CÎRNU C. Postmodern Education and Technological Development. Cyber Range as a Tool for Developing Cyber Security Skills[J]. INTED 2021 Proceedings, 2021, 1: 8241-8246. |
| [15] | PARK M, LEE H, KIM Y, et al. Design and Implementation of Multi-Cyber Range for Cyber Training and Testing[EB/OL]. (2022-12-07)[2025-07-09]. https://doi.org/10.3390/app122412546. |
| [16] | YAMIN M M, KATT B. Use of Cyber Attack and Defense Agents in Cyber Ranges: A Case Study[EB/OL]. (2022-08-27)[2025-07-09]. https://doi.org/10.1016/j.cose.2022.102892. |
| [17] |
SISODIYA D S, TIWARI R, JAIN P, et al. An AI-Based Cyber Ranges to Strengthen the Cybersecurity of Cyber Physical Systems[J]. Journal of Applied Security Research, 2025, 20(4): 473-505.
doi: 10.1080/19361610.2025.2518383 URL |
| [18] | HANNAY J E, STOLPE A, YAMIN M M. Toward AI-Based Scenario Management for Cyber Range Training[EB/OL]. (2021-11-11)[2025-07-09]. https://link.springer.com/chapter/10.1007/978-3-030-90963-5_32. |
| [19] | STROM B E, APPLEBAUM A, MILLER D P, et al. Mitre ATT&CK:Design and Philosophy[EB/OL]. (2020-03-01)[2025-07-09]. https://www.mitre.org/sites/default/files/2021-11/prs-19-01075-28-mitre-attack-design-and-philosophy.pdf. |
| [20] |
LU Chao, LYU Jiafei, ZHANG Liming, et al. Nuclear Power Plants with Artificial Intelligence in Industry 4.0 Era: Top-Level Design and Current Applications—A Systemic Review[J]. IEEE Access, 2020, 8: 194315-194332.
doi: 10.1109/ACCESS.2020.3032529 URL |
| [21] | ZHOU Haifeng, LI Mohan, SUN Yanbin, et al. Digital Twin-Based Cyber Range for Industrial Internet of Things[J]. IEEE Consumer Electronics Magazine, 2023, 12(6): 66-77. |
| [22] | EDA. Cyber Ranges Federation Project Reaches New Milestone[EB/OL]. (2018-09-13)[2025-07-09]. https://eda.europa.eu/news-and-events/news/2018/09/13/cyber-ranges-federation-project-reaches-new-milestone. |
| [23] | DIAKOUMAKOS J, CHASKOS E, KOLOKOTRONIS N, et al. Cyber-Range Federation and Cyber-Security Games: A Gamification Scoring Model[C]// IEEE. 2021 IEEE International Conference on Cyber Security and Resilience (CSR). New York: IEEE, 2021: 186-191. |
| [24] | NICT. StarBED Equipment[EB/OL]. [2025-07-09]. https://starbed.nict.go.jp/en/equipment/index.html. |
| [25] | LATEȘ I, BOJA C. Cyber Range Technology Stack Review[EB/OL]. (2023-01-01)[2025-07-09]. https://doi.org/10.1007/978-981-19-6755-9_3. |
| [26] | LEITNER M, FRANK M, HOTWAGNER W, et al. AIT Cyber Range: Flexible Cyber Security Environment for Exercises, Training and Research[C]// ACM. The European Interdisciplinary Cybersecurity Conference. New York: ACM, 2020: 1-6. |
| [27] | BICA I, UNC R L, ȚURCANU Ș. Virtualization and Automation for Cybersecurity Training and Experimentation[EB/OL]. (2021-02-04)[2025-07-09]. https://doi.org/10.1007/978-3-030-69255-1_15. |
| [28] | BALTO K E, YAMIN M M, SHALAGINOV A, et al. Hybrid IoT Cyber Range[EB/OL]. (2023-03-13)[2025-07-09]. https://doi.org/10.3390/s23063071. |
| [29] | BLAGOEV I, SHALAMANOV V. Development of Cyber Ranges as a Reference Environment for Digital Transformation[C]// IEEE. 2023 4th International Conference on Communications, Information, Electronic and Energy Systems (CIEES). New York: IEEE, 2023: 1-5. |
| [30] |
FU Yongquan, HAN Weihong, YUAN Dong. Disentangled Orchestration on Cyber Ranges[J]. IEEE Transactions on Dependable and Secure Computing, 2024, 21(4): 2344-2360.
doi: 10.1109/TDSC.2023.3303888 URL |
| [31] | ZOU Xing, HU Ning. Cyber-Range: The Scientific Infrastructure for Cyberspace Security Research[C]// IEEE. 2024 IEEE 9th International Conference on Data Science in Cyberspace (DSC). New York: IEEE, 2024: 188-195. |
| [32] | UKWANDU E, BEN FARAH M A, HINDY H, et al. A Review of Cyber-Ranges and Test-Beds: Current and Future Trends[EB/OL]. (2020-12-13)[2025-07-09]. https://doi.org/10.3390/s20247148. |
| [33] | KIM I, PARK M, LEE H J, et al. A Study on the Multi-Cyber Range Application of Mission-Based Cybersecurity Testing and Evaluation in Association with the Risk Management Framework[EB/OL]. (2023-12-28)[2025-07-09]. https://www.mdpi.com/2078-2489/15/1/18. |
| [34] | ZHANG Jiawei, LI Zongzhe, CHEN Rui, et al. A Survey of Cyber Range: Current Status, Analysis, and Future Trends[EB/OL]. (2024-08-02)[2025-07-09]. https://doi.org/10.1007/978-981-97-4522-7_6. |
| [35] | REBECCHI F, PASTOR A, MOZO A, et al. A Digital Twin for the 5G Era: The SPIDER Cyber Range[C]// IEEE. 2022 IEEE 23rd International Symposium on a World of Wireless, Mobile and Multimedia Networks (WoWMoM). New York: IEEE, 2022: 567-572. |
| [36] | ANGELOGIANNI A, POLITIS I, POLVANESI P L, et al. Unveiling the User Requirements of a Cyber Range for 5G Security Testing and Training[C]// IEEE. 2021 IEEE 26th International Workshop on Computer Aided Modeling and Design of Communication Links and Networks (CAMAD). New York: IEEE, 2021: 1-6. |
| [37] | TIWARI P, VITTAL S, ANTONY A. Sharding the Datastore Network Functions of 5G Core for Scalable and Resilient Slice Service[C]// IEEE. 2024 IEEE 10th International Conference on Network Softwarization (NetSoft). New York: IEEE, 2024: 331-335. |
| [38] | BU Youjun, CHEN Ruilong, ZHOU Kun, et al. Design and Implementation of Endogenous Security Cyber Range Based on Digital Twin Technology[C]// IEEE. 2024 Asia-Pacific Conference on Image Processing, Electronics and Computers (IPEC). New York: IEEE, 2024: 587-593. |
| [39] | GROSHEV M, GUIMARÃES C, MARTÍN-PÉREZ J, et al. Toward Intelligent Cyber-Physical Systems: Digital Twin Meets Artificial Intelligence[J]. IEEE Communications Magazine, 2021, 59(8): 14-20. |
| [40] | NAKAJIMA J, LIN Qian, YANG Sheng, et al. Optimizing Virtual Machines Using Hybrid Virtualization[C]// ACM. The 2011 ACM Symposium on Applied Computing. New York: ACM, 2011: 573-578. |
| [41] | DAUGHETY N, PENDLETON M, XU Shouhuai, et al. VCDS: A Virtualized Cross Domain Solution Architecture[C]// IEEE. 2021 IEEE Military Communications Conference (MILCOM). New York: IEEE, 2021: 61-68. |
| [42] | EL-MAGHRABY R T, ABD E N M, BAHAA-ELDIN A M. A Survey on Deep Packet Inspection[C]// IEEE. 2017 12th International Conference on Computer Engineering and Systems (ICCES). New York: IEEE, 2017: 188-197. |
| [43] | NAIR S S, SANTHA T. High Availability of Kernel-Based Virtual Machine Using Nested Virtualization[EB/OL]. (2023-02-15)[2025-07-09]. https://doi.org/10.1016/j.measen.2023.100712. |
| [44] |
GOODFELLOW I, POUGET-ABADIE J, MIRZA M, et al. Generative Adversarial Networks[J]. Communications of the ACM, 2020, 63(11): 139-144.
doi: 10.1145/3422622 URL |
| [45] | CHEN Daowei, YAN Hongsheng. Research on APT Groups Malware Classification Based on TCN-GAN[EB/OL]. (2025-06-10)[2025-07-09]. https://doi.org/10.1371/journal.pone.0323377. |
| [46] | ARIFIN M M, AHMED M S, GHOSH T K, et al. A Survey on the Application of Generative Adversarial Networks in Cybersecurity: Prospective, Direction and Open Research Scopes[EB/OL]. (2024-09-20)[2025-07-09]. https://doi.org/10.48550/arXiv.2407.08839. |
| [47] |
MOGHADDAM P S, VAZIRI A, KHATAMI S S, et al. Generative Adversarial and Transformer Network Synergy for Robust Intrusion Detection in IoT Environments[J]. Future Internet, 2025, 17(6): 1-36.
doi: 10.3390/fi17010001 URL |
| [48] | ZEESHAN M, MAASOOMA. Trans-GAN: A Deep Learning Paradigm for Multi-Type Anomaly Detection in Network Traffic[C]// IEEE. 2024 International Conference on Frontiers of Information Technology (FIT). New York: IEEE, 2024: 1-6. |
| [49] | SUTTON R S, MCALLESTER D, SINGH S, et al. Policy Gradient Methods for Reinforcement Learning with Function Approximation[C]// MIT. The 12th International Conference on Neural Information Processing Systems. Cambridge: MIT, 1999: 1057-1063. |
| [50] | SANTORSOLA A, MIGLIAU A, CAPOR U S. Reinforcement Learning Agents for Simulating Normal and Malicious Actions in Cyber Range Scenarios[EB/OL]. [2025-07-09]. https://www.cybersuite.it/wp-content/uploads/2024/03/paper1.pdf. |
| [51] | ARORA S, DOSHI P. A Survey of Inverse Reinforcement Learning: Challenges, Methods and Progress[EB/OL]. (2021-03-24)[2025-07-09]. https://doi.org/10.1016/j.artint.2021.103500. |
| [52] |
IBRAHIM M, ELHAFIZ R, AL-WADI A. Reinforcement Learning-Based Attack Graph Analysis for Wastewater Treatment Plant[J]. IEEE Transactions on Industry Applications, 2023, 59(6): 7858-7867.
doi: 10.1109/TIA.2023.3298289 URL |
| [53] |
LITTMAN M L. A Tutorial on Partially Observable Markov Decision Processes[J]. Journal of Mathematical Psychology, 2009, 53(3): 119-125.
doi: 10.1016/j.jmp.2009.01.005 URL |
| [54] | MODI A, SUN Zhibo, PANWAR A, et al. Towards Automated Threat Intelligence Fusion[C]// IEEE. 2016 IEEE 2nd International Conference on Collaboration and Internet Computing (CIC). New York: IEEE, 2016: 408-416. |
| [55] | DHABLIYA D, KHETANI V, GANDHI Y, et al. Threat Intelligence Fusion with AI and Machine Learning[EB/OL]. (2025-06-20)[2025-07-09]. https://doi.org/10.1007/9. |
| [56] |
BENZEKKI K, EL F A, ELBELRHITI E A. Software-Defined Networking (SDN): A Survey[J]. Security and Communication Networks, 2016, 9(18): 5803-5833.
doi: 10.1002/sec.v9.18 URL |
| [57] | MAHALINGAM M, DUTT D, DUDA K, et al. Virtual Extensible Local Area Network (VXLAN): A Framework for Overlaying Virtualized Layer 2 Networks over Layer 3 Networks[EB/OL]. (2014-08-01)[2025-07-09]. https://www.rfc-editor.org/rfc/rfc7348.html. |
| [58] | NGO BILONG J R, BA M, KACHALLAH A M, et al. Eco-Efficient SDN-VXLAN Architecture for Multi-Tenant Datacenters: Isolation, Automation and Resource Optimization[C]// IEEE. 2025 3rd International Conference on Sustainable Computing and Data Communication Systems (ICSCDS). New York: IEEE, 2025: 567-573. |
| [59] | Canadian Centre for Cyber Security. National Cyber Threat Assessment 2025-2026[EB/OL]. [2025-07-09]. https://www.cyber.gc.ca/sites/default/files/national-cyber-threat-assessment-2025-2026-e.pdf. |
| [60] | DESJARDINS R. Overview and Status of the ISO Reference Model of Open Systems Interconnection[J]. ACM SIGCOMM Computer Communication Review, 1981, 11(2): 10-14. |
| [61] | FUNK M, HOSEMANN S, JUNG J C, et al. Towards Ontology Construction with Language Models[EB/OL]. (2023-09-18)[2025-07-09]. https://doi.org/10.48550/arXiv.2309.09898. |
| [62] | KANAKOGI K, WASHIZAKI H, FUKAZAWA Y, et al. Tracing CVE Vulnerability Information to CAPEC Attack Patterns Using Natural Language Processing Techniques[EB/OL]. (2021-07-26)[2025-07-09]. https://doi.org/10.3390/info12080298. |
| [63] |
LAHAT D, ADALI T, JUTTEN C. Multimodal Data Fusion: An Overview of Methods, Challenges, and Prospects[J]. Proceedings of the IEEE, 2015, 103(9): 1449-1477.
doi: 10.1109/JPROC.2015.2460697 URL |
| [64] | ZHAO Dongmei, WU Yaxing, ZHANG Hongbin. A Situation Awareness Approach for Network Security Using the Fusion Model[EB/OL]. (2022-08-21)[2025-07-09]. https://doi.org/10.1155/2022/6214738. |
| [65] | CHENG Jie, ZHANG Ru, TIAN Siyuan, et al. Fusion of Traffic Data and Alert Log Based on Sensitive Information[EB/OL]. (2022-07-13)[2025-07-09]. https://link.springer.com/chapter/10.1007/978-981-19-2456-9_9. |
| [1] | 杨望, 马鸣宇, 卞郡菁. 基于ATT&CK的多维网络靶场属性刻画模型及其相似性算法[J]. 信息网络安全, 2025, 25(7): 1063-1073. |
| [2] | 赵新强, 范博, 张东举. 基于威胁发现的APT攻击防御体系研究[J]. 信息网络安全, 2024, 24(7): 1122-1128. |
| [3] | 刘红, 谢永恒, 王国威, 蒋帅. 基于跨领域本体的信息安全分析[J]. 信息网络安全, 2020, 20(9): 82-86. |
| [4] | 余奕, 吕良双, 李肖坚, 王天博. 面向移动云计算场景的动态网络拓扑描述语言[J]. 信息网络安全, 2019, 19(9): 120-124. |
| [5] | 刘延华, 高晓玲, 朱敏琛, 苏培煌. 基于数据特征学习的网络安全数据分类方法研究[J]. 信息网络安全, 2019, 19(10): 50-56. |
| [6] | 李剑锋, 刘渊, 张浩, 王晓锋. 面向IaaS云平台的路由转发优化研究与实现[J]. 信息网络安全, 2017, 17(9): 10-15. |
| [7] | 王绍节, 龙春, 万巍, 赵静. 基于网络空间安全实时数据的HDFS小文件问题研究[J]. 信息网络安全, 2017, 17(10): 81-85. |
| [8] | 赵艳玲. 美国改变网络空间安全游戏规则的新理念与新技术[J]. 信息网络安全, 2015, 15(9): 50-53. |
| [9] | 陈华山, 皮兰, 刘峰, 林东岱. 网络空间安全科学基础的研究前沿及发展趋势[J]. 信息网络安全, 2015, 15(3): 1-5. |
| [10] | 段晋珏, 赵旦峰, 梁明珅. 基于数字喷泉码相关链提取的水声传感器网络HARQ协议[J]. 信息网络安全, 2015, 15(3): 64-68. |
| [11] | 李秋香, 郝文江, 李翠翠, 徐丽萍. 国外网络靶场技术现状及启示[J]. 信息网络安全, 2014, 14(9): 63-68. |
| [12] | 李战宝, 张文贵. 网络抗压能力是网络空间安全发展的新理念[J]. 信息网络安全, 2014, 14(9): 76-79. |
| [13] | . 基于NS的机会网络路由协议仿真[J]. , 2014, 14(5): 52-. |
| [14] | 张海霞;连一峰. 基于测试床模拟的通用安全评估框架[J]. , 2013, 13(Z): 0-0. |
| [15] | 李亮. 路由器队列调度算法仿真研究[J]. , 2011, 11(7): 0-0. |
| 阅读次数 | ||||||
|
全文 |
|
|||||
|
摘要 |
|
|||||