Netinfo Security ›› 2015, Vol. 15 ›› Issue (9): 124-128.doi: 10.3969/j.issn.1671-1122.2015.09.029
• Orginal Article • Previous Articles Next Articles
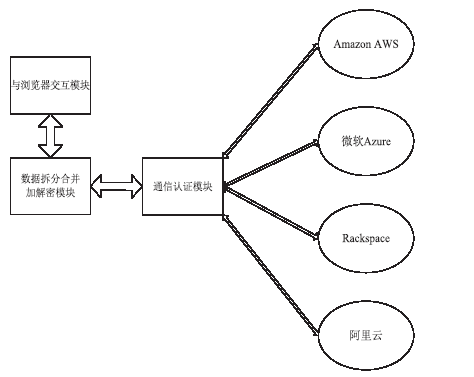
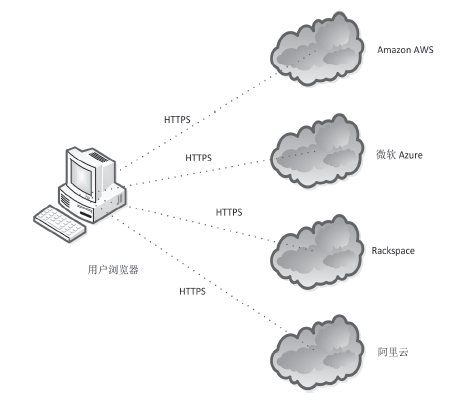
Design and Implementation of a Multi-cloud Based Browser Password Manager
Ding-bo LI1,2,3( ), Lu-ning XIA1,3, Zhan WANG1,3
), Lu-ning XIA1,3, Zhan WANG1,3
- 1. State Key Laboratory of Information Security, Institute of Information Engineering, Chinese Academy of Sciences, Beijing 100093, China
2.University of Chinese Academy of Sciences, Beijing 100049, China
3.Data Assurance and Communication Security Research Center, Beijing 100093, China
-
Received:2015-07-15Online:2015-09-30Published:2015-11-13
CLC Number:
Cite this article
Ding-bo LI, Lu-ning XIA, Zhan WANG. Design and Implementation of a Multi-cloud Based Browser Password Manager[J]. Netinfo Security, 2015, 15(9): 124-128.
share this article
Add to citation manager EndNote|Ris|BibTeX
URL: http://netinfo-security.org/EN/10.3969/j.issn.1671-1122.2015.09.029
| [1] | J. Bonneau, C. Herley, P. C. van Oorschot, and F. Stajano. The quest to replace passwords: A framework for comparative evaluation of web authentication schemes[C]// proc. of IEEE Symposium on Security and Privacy, 2012. |
| [2] | 武传坤. 身份证件的安全要求和可使用的密码学技术[J]. 信息网络安全,2015,(5):21-27. |
| [3] | Kelley, Patrick Gage, et al.Guess again (and again and again): Measuring password strength by simulating password-cracking algorithms[C]// proc. IEEE Symposium on Security and Privacy (S&P'12),2012. |
| [4] | S. Komanduri, R. Shay, P. G. Kelley, M. L. Mazurek,L. Bauer, N. Christin, L. F. Cranor,S. Egelman.Of passwords and people: Measuring the effect of password-composition policies[C]//Proc. of CHI, 2011. |
| [5] | J. Yan, A. Blackwell, R. Anderson,A. Grant.Password memorability and security: Empirical results[J]. IEEE Security and Privacy, 2004, 2(5):25-31. |
| [6] | 段娟,辛阳,马宇威. 基于Web应用的安全日志审计系统研究与设计[J]. 信息网络安全,2014,(10):70-76. |
| [7] | Zhao R, Yue C.All your browser-saved passwords could belong to us: a security analysis and a cloud-based new design[C] //Proceedings of the third ACM conference on Data and application security and privacy. ACM, 2013: 333-340. |
| [8] | 袁艳祥,游林. 基于身份加密的可认证密钥协商协议[J]. 信息网络安全,2014,(3):1-6. |
| [9] | Zhao, Rui,Chuan Yue. Toward a secure and usable cloud-based password manager for web browsers[J] .Computers & Security 2014: 32-47. |
| [10] | Li, Zhiwei, et al.The emperor? s new password manager: Security analysis of web-based password managers[C]//23rd USENIX Security Symposium (USENIX Security 14). 2014. |
| [11] | Zhao R, Yue C, Sun K.Vulnerability and risk analysis of two commercial browser and cloud based password managers[J]. SCIENCE, 2013, 2(4):183-197. |
| [12] | 吕从东,韩臻,马威. 云存储服务端数据存储加密机制的设计和实现[J]. 信息网络安全,2014,(6):1-5. |
| [13] | J. K.Resch and J. S. Plank. AONT-RS: blending security and performance in dispersed storage systems[C]//FAST-2011: 9th Usenix Conference on File and Storage Technologies, February 2011. |
| [14] | 秦志光,包文意,赵洋,等. 云存储中一种模糊关键字搜索加密方案[J]. 信息网络安全,2015,(6):7-12. |
| [15] | Silver, David, et al.Password managers: Attacks and defenses[C]//Proceedings of the 23rd Usenix Security Symposium. 2014. |
| [1] | Zhiyan ZHAO, Xiaomo JI. Research on the Intelligent Fusion Model of Network Security Situation Awareness [J]. Netinfo Security, 2020, 20(4): 87-93. |
| [2] | Min LIU, Shuhui CHEN. Research on VoLTE Traffic Based on Association Fusion [J]. Netinfo Security, 2020, 20(4): 81-86. |
| [3] | Lingyu BIAN, Linlin ZHANG, Kai ZHAO, Fei SHI. Ethereum Malicious Account Detection Method Based on LightGBM [J]. Netinfo Security, 2020, 20(4): 73-80. |
| [4] | Yifeng DU, Yuanbo GUO. A Dynamic Access Control Method for Fog Computing Based on Trust Value [J]. Netinfo Security, 2020, 20(4): 65-72. |
| [5] | Zhizhou FU, Liming WANG, Ding TANG, Shuguang ZHANG. HBase Secondary Ciphertext Indexing Method Based on Homomorphic Encryption [J]. Netinfo Security, 2020, 20(4): 55-64. |
| [6] | Rong WANG, Chunguang MA, Peng WU. An Intrusion Detection Method Based on Federated Learning and Convolutional Neural Network [J]. Netinfo Security, 2020, 20(4): 47-54. |
| [7] | Xiaoli DONG, Shuai SHANG, Jie CHEN. Impossible Differential Attacks on 9-Round Block Cipher Rijndael-192 [J]. Netinfo Security, 2020, 20(4): 40-46. |
| [8] | Chun GUO, Changqing CHEN, Guowei SHEN, Chaohui JIANG. A Ransomware Classification Method Based on Visualization [J]. Netinfo Security, 2020, 20(4): 31-39. |
| [9] | Lu CHEN, Yajie SUN, Liqiang ZHANG, Yun CHEN. A Scheme of Measurement for Terminal Equipment Based on DICE in IoT [J]. Netinfo Security, 2020, 20(4): 21-30. |
| [10] | Jinfang JIANG, Guangjie HAN. Survey of Trust Management Mechanism in Wireless Sensor Network [J]. Netinfo Security, 2020, 20(4): 12-20. |
| [11] | Jianwei LIU, Yiran HAN, Bin LIU, Beiyuan YU. Research on 5G Network Slicing Security Model [J]. Netinfo Security, 2020, 20(4): 1-11. |
| [12] | Peng LIU, Qian HE, Wangyang LIU, Xu CHENG. CP-ABE Scheme Supporting Attribute Revocation and Outsourcing Decryption [J]. Netinfo Security, 2020, 20(3): 90-97. |
| [13] | Yubo SONG, Ming FAN, Junjie YANG, Aiqun HU. Multipath Solution and Blocking Method of Network Attack Traffic Based on Topology Analysis [J]. Netinfo Security, 2020, 20(3): 9-17. |
| [14] | Tengfei WANG, Manchun CAI, Tianliang LU, Ting YUE. IPv6 Network Attack Source Tracing Method Based on iTrace_v6 [J]. Netinfo Security, 2020, 20(3): 83-89. |
| [15] | Yi ZHANG, Hongyan LIU, Hequn XIAN, Chengliang TIAN. A Cloud Storage Encrypted Data Deduplication Method Based on Authorization Records [J]. Netinfo Security, 2020, 20(3): 75-82. |
| Viewed | ||||||
|
Full text |
|
|||||
|
Abstract |
|
|||||