Netinfo Security ›› 2020, Vol. 20 ›› Issue (4): 73-80.doi: 10.3969/j.issn.1671-1122.2020.04.009
Previous Articles Next Articles
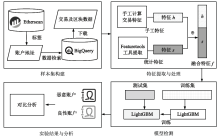
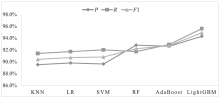
Ethereum Malicious Account Detection Method Based on LightGBM
BIAN Lingyu1,2, ZHANG Linlin1,2( ), ZHAO Kai1,2, SHI Fei1,2
), ZHAO Kai1,2, SHI Fei1,2
- 1. College of Information Science and Engineering, Xinjiang University, Urumqi 830046, China
2. College of Cyber Science and Engineering, Xinjiang University, Urumqi 830046, China
-
Received:2020-01-03Online:2020-04-10Published:2020-05-11 -
Contact:Linlin ZHANG E-mail:zllnadasha@xju.edu.cn
CLC Number:
Cite this article
BIAN Lingyu, ZHANG Linlin, ZHAO Kai, SHI Fei. Ethereum Malicious Account Detection Method Based on LightGBM[J]. Netinfo Security, 2020, 20(4): 73-80.
share this article
Add to citation manager EndNote|Ris|BibTeX
URL: http://netinfo-security.org/EN/10.3969/j.issn.1671-1122.2020.04.009
| [1] | SHAO Qifeng, JIN Cheqing, ZHANG Zhao, et al.Blockchain: Architecture and Research Progress[J]. Chinese Journal of Computers, 2018, 41(5): 969-988. |
| 邵奇峰,金澈清,张召,等.区块链技术:架构及进展[J].计算机学报,2018,41(5):969-988. | |
| [2] | GUO Dongchao, DONG Jiaqing, WANG Kai.Graph Structure and Statistical Properties of Ethereum Transaction Relationships[J]. Information Sciences, 2019, 492(2019): 58-71. |
| [3] | DEEPAK P, NISHA M, MOHANTY S P, et al.Everything You Wanted to Know About the Blockchain: Its Promise, Components, Processes, and Problems[J]. IEEE Consumer Electronics Magazine, 2018, 7(4): 6-14. |
| [4] | ZHU Liehuang, GAO Feng, SHEN Meng, et al.Survey on Privacy Preserving Techniques for Blockchain Technology[J]. Journal of Computer Research and Development, 2017, 54(10): 2170-2186. |
| 祝烈煌,高峰,沈蒙,等.区块链隐私保护研究综述[J].计算机研究与发展,2017,54(10):2170-2186. | |
| [5] | ETHERSCAN. Ethereum Block Explorer[EB/OL]. , 2019-9-27. |
| [6] | YUAN Yong, WANG Feiyue.Blockchain: The State of the Art and Future Trends[J]. Acta Automatica Sinica, 2016, 42(4): 481-494. |
| 袁勇,王飞跃.区块链技术发展现状与展望[J].自动化学报,2016,42(4):481-494. | |
| [7] | LIU Han, YANG Zhiqiang, JIANG Yu, et al.Enabling Clone Detection for Ethereum via Smart Contract Birthmarks[C]//IEEE/ACM. 27th International Conference on Program Comprehension(ICPC), May 25-31, 2019, Montreal, QC, Canada. New York: ACM, 2019: 105-115. |
| [8] | SUN Guozi, WANG Jitao, GU Yu.Security Threat Analysis of Blockchain Technology[J]. Journal of Nanjing University of Posts and Telecommunications(Natural Science Edition), 2019, 39(5): 48-62. |
| 孙国梓,王纪涛,谷宇.区块链技术安全威胁分析[J].南京邮电大学学报(自然科学版),2019,39(5):48-62. | |
| [9] | HUANG Butian, LIU Zhenguang, CHEN Jianhai, et al.Behavior Pattern Clustering in Blockchain Networks[J]. Multimedia Tools and Applications, 2017, 76(19): 20099-20110. |
| [10] | FEATURE LABS. Featuretools[EB/OL]. , 2019-9-27. |
| [11] | ZHAO Chen.Graph-Based Forensic Investigation of Bitcoin Transactions[D]. Ames, Jowa: Jowa State University, 2014. |
| [12] | MONACO J V.Identifying Bitcoin Users by Transaction Behavior[C]//SPIE. 2015 International Society for Optics and Photonics Defense Security and Sensing, April 20-24, 2015, Baltimore, MD, USA. Washington: SPIE, 2015: 33-47. |
| [13] | ANDROULAKI E, KARAME G O, ROESCHLIN M, et al.Evaluating User Privacy in Bitcoin[C]//Springer. 17th International Conference on Financial Cryptography and Data Security, April 1-5, 2013, Okinawa, Japan. Berlin: Springer, 2013: 34-51. |
| [14] | REID F, HARRIGAN M.An Analysis of Anonymity in the Bitcoin System[C]//IEEE. 3rd IEEE International Conference on Privacy, Security, Risk and Trust and 3rd IEEE International Conference on Social Computing, October 9-11, 2011, Boston, MA, USA. NJ: IEEE, 2011: 1318-1326. |
| [15] | YIN H S, LANGENHELDT K, HARLEV M, et al.Regulating Cryptocurrencies: A Supervised Machine Learning Approach to De-anonymizing the Bitcoin Blockchain[J]. Journal of Management Information Systems, 2019, 36(1): 37-73. |
| [16] | LIN Yujing, WU Powei, HSU Chenghan, et al.An Evaluation of Bitcoin Address Classification Based on Transaction History Summarization[C]//IEEE. International Conference on Blockchain and Cryptocurrency(ICBC), May 14-17, 2019, Seoul, Korea(South). NJ: IEEE, 2019: 302-310. |
| [17] | TOYODA K, OHTSUKI T, MATHIOPOULOS P T.Multi-Class Bitcoin-Enabled Service Identification Based on Transaction History Summarization[C]//IEEE. 11th IEEE International Conference on Internet of Things(iThings) and 14th IEEE Green Computing and Communications(GreenCom) and 11th IEEE Cyber, Physical and Social Computing(CPSCom) and 4th IEEE Smart Data(SmartData), July 30-August 3, 2018, Halifax, NS, Canada. NJ: IEEE, 2018: 1153-1160. |
| [18] | TOYODA K, OHTSUKI T, MATHIOPOULOS P T.Identification of High Yielding Investment Programs in Bitcoin via Transactions Pattern Analysis[C]//IEEE. 60th IEEE Global Communications Conference, June 12-14, 2017, Singapore. NJ: IEEE, 2017: 1-6. |
| [19] | KANEMURA K, TOYODA K, OHTSUKI T.Identification of Darknet Markets’ Bitcoin Addresses by Voting Per-address Classification Results[C]//IEEE. International Conference on Blockchain and Cryptocurrency(ICBC), May 14-17, 2019, Seoul, Korea(South). NJ: IEEE, 2019: 154-158. |
| [20] | CHEN Weili, ZHENG Zibin, NGAI E C, et al.Exploiting Blockchain Data to Detect Smart Ponzi Schemes on Ethereum[J]. IEEE Access, 2019, 7(2019): 37575-37586. |
| [21] | LIAO K, ZHAO Ziming, DOUPE A, et al.Behind Closed Doors: Measurement and Analysis of CryptoLocker Ransoms in Bitcoin[C]//IEEE. 11th APWG Symposium on Electronic Crime Research(eCrime), June 1-3, 2016, Toronto, Canada. NJ: IEEE, 2016: 1-13. |
| [22] | KE Guolin, MENG Qi, THOMAS F, et al.LightGBM: A Highly Efficient Gradient Boosting Decision Tree[C]//NIPS. 31st Conference on Neural Information Processing Systems, December 4-9, 2017, Long Beach, CA, USA. New York: Curran Associates, 2017: 3146-3154. |
| [23] | YUN Ju, SUN Guangyu, CHEN Quanhe, et al.A Model Combining Convolutional Neural Network and LightGBM Algorithm for Ultra-Short-Term Wind Power Forecasting[J]. IEEE Access, 2019, 7(2019): 28309-28318. |
| [24] | JOURDAN M, BLANDIN S, WYNTER L, et al.Characterizing Entities in the Bitcoin Blockchain[C]//IEEE. 18th IEEE International Conference on Data Mining(ICDM), November 17-19, 2018, Singapore. NJ: IEEE, 2018: 55-62. |
| [25] | LEE D, KWON T.Automated Classification of Unknown Smart Contracts of Ethereum Using Machine Learning[J]. Journal of the Korea Institute of Information Security & Cryptology, 2018, 28(6): 1319-1328. |
| [1] | HAN Lei, CHEN Wuping, ZENG Zhiqiang, ZENG Yingming. Research on Hierarchical Network Structure and Application of Blockchain [J]. Netinfo Security, 2020, 20(9): 112-116. |
| [2] | WANG Jinmiao, XIE Yongheng, WANG Guowei, LI Yiting. A Method of Privacy Preserving and Access Control in Blockchain Based on Attribute-based Encryption [J]. Netinfo Security, 2020, 20(9): 47-51. |
| [3] | MAO Zhilai, LIU Yanan, SUN Huiping, CHEN Zhong. Research on Blockchain Performance Scalability and Security [J]. Netinfo Security, 2020, 20(3): 56-64. |
| [4] | LANG Weimin, ZHANG Han, ZHAO Yifeng, YAO Jinfang. A Blockchain-based Behavior Regulation and Activities Management Scheme for Internet of Things [J]. Netinfo Security, 2020, 20(2): 22-29. |
| [5] | Yihua ZHOU, Zhuqing LV, Yuguang YANG, Weimin SHI. Data Deposit Management System Based on Blockchain Technology [J]. Netinfo Security, 2019, 19(8): 8-14. |
| [6] | Aitong LU, Kuo ZHAO, Jingying YANG, Feng WANG. Research on Cross-chain Technology of Blockchain [J]. Netinfo Security, 2019, 19(8): 83-90. |
| [7] | Min ZHENG, Hong WANG, Hong LIU, Chong TAN. Survey on Consensus Algorithms of Blockchain [J]. Netinfo Security, 2019, 19(7): 8-24. |
| [8] | Yuanjian ZHOU, Dongmei QING, Yining LIU, Songzhan LV. Design of Electronic Warehouse Receipts System Based on Blockchain [J]. Netinfo Security, 2019, 19(6): 84-90. |
| [9] | Wenming WANG, Chongyang SHI, Yinghao WANG, Dejian WEI. Research on Transaction and Security Based on Blockchain Technology [J]. Netinfo Security, 2019, 19(5): 1-9. |
| [10] | Yiming HEI, Jianwei LIU, Zongyang ZHANG, Hui YU. Blockchain-based Distributed Cloud Storage System with Public Verification [J]. Netinfo Security, 2019, 19(3): 52-60. |
| [11] | Guofeng ZHAO, Mingcong ZHANG, Jihua ZHOU, Tao ZHAO. Research and Application of Block File Storage Model Based on Blockchain System of Erasure Code [J]. Netinfo Security, 2019, 19(2): 28-35. |
| [12] | Peili LI, Haixia XU, Tianjun MA, Yongheng MU. The Application of Blockchain Technology in Network Mutual Aid and User Privacy Protection [J]. Netinfo Security, 2018, 18(9): 60-65. |
| [13] | Qiongqiong DUAN, Dinghua XIANG, Hongzhou SHI. Design on the Blockchain-based Authentication for Smart Objects [J]. Netinfo Security, 2018, 18(9): 95-101. |
| [14] | Jinghao LIU, Jianchuan PING, Xiaomei FU. Research on A Distributed Public Key System Based on Blockchain [J]. Netinfo Security, 2018, 18(8): 25-33. |
| [15] | Wei HU, Qiuhan WU, Shengli LIU, Wei FU. Design of Secure eID and Identity Authentication Agreement in Mobile Terminal Based on Guomi Algorithm and Blockchain [J]. Netinfo Security, 2018, 18(7): 7-9. |
| Viewed | ||||||
|
Full text |
|
|||||
|
Abstract |
|
|||||