| [1] |
HELLMAN M. New Directions in Cryptography[J]. IEEE Transactions on Information Theory, 1976, 22(6): 644-654.
doi: 10.1109/TIT.1976.1055638
URL
|
| [2] |
RIVEST R L, SHAMIR A, ADLEMAN L. A Method for Obtaining Digital Signatures and Public-Key Cryptosystems[J]. Communications of the ACM, 1978, 21(2): 120-126.
doi: 10.1145/359340.359342
URL
|
| [3] |
ELGAMAL T. A Public Key Cryptosystem and a Signature Scheme Based on Discrete Logarithms[J]. IEEE Transactions on Information Theory, 1985, 31(4): 469-472.
doi: 10.1109/TIT.1985.1057074
URL
|
| [4] |
MERKLE R, HELLMAN M. Hiding Information and Signatures in Trapdoor Knapsacks[J]. IEEE Transactions on Information Theory, 1978, 24(5): 525-530.
|
| [5] |
SHOR P W. Algorithms for Quantum Computation: Discrete Logarithms and Factoring[C]// IEEE. The 35th Annual Symposium on Foundations of Computer Science. New York: IEEE, 1994: 124-134.
|
| [6] |
LAGARIAS J C, ODLYZKO A M. Solving Low-Density Subset Sum Problems[J]. Journal of the ACM (JACM), 1985, 32(1): 229-246.
doi: 10.1145/2455.2461
URL
|
| [7] |
COSTER M J, LAMACCHIA B A, ODLYZKO A M, et al. An Improved Low-Density Subset Sum Algorithm[C]// Springer. Workshop on the Theory and Application of Cryptographic Techniques. Heidelberg: Springer, 1991: 54-67.
|
| [8] |
COPPERSMITH D. Finding a Small Root of a Univariate Modular Equation[C]// Springer. International Conference on the Theory and Applications of Cryptographic Techniques. Heidelberg: Springer, 1996: 155-165.
|
| [9] |
COPPERSMITH D. Finding a Small Root of a Bivariate Integer Equation; Factoring with High Bits Known[C]// Springer. International Conference on the Theory and Applications of Cryptographic Techniques. Heidelberg: Springer, 1996: 178-189.
|
| [10] |
VAN EMDE BOAS P. Another NP-Complete Problem and the Complexity of Computing Short Vectors in a Lattice[D]. Amsterdam: University of Amsterdam, 1981.
|
| [11] |
AJTAI M. The Shortest Vector Problem in L2 is NP-Hard for Randomized Reductions[C]// ACM. The 30th Annual ACM Symposium on Theory of Computing. New York: ACM, 1998: 10-19.
|
| [12] |
AJTAI M, KUMAR R, SIVAKUMAR D. A Sieve Algorithm for the Shortest Lattice Vector Problem[C]// ACM. The 33rd Annual ACM Symposium on Theory of Computing. New York: ACM, 2001: 601-610.
|
| [13] |
NGUYEN P Q, VIDICK T. Sieve Algorithms for the Shortest Vector Problem Are Practical[J]. Journal of Mathematical Cryptology, 2008, 2(2): 181-207.
doi: 10.1515/JMC.2008.009
URL
|
| [14] |
MICCIANCIO D, VOULGARIS P. Faster Exponential Time Algorithms for the Shortest Vector Problem[C]// ACM. The 21st Annual ACM-SIAM Symposium on Discrete Algorithms. New York: ACM, 2010: 1468-1480.
|
| [15] |
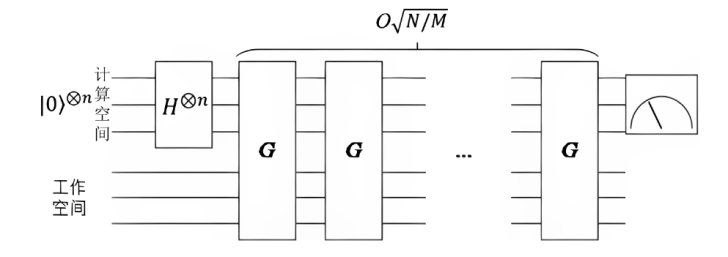
MERMIN N D. Quantum Computer Science: An Introduction[M]. Cambridge: Cambridge University Press, 2007.
|
| [16] |
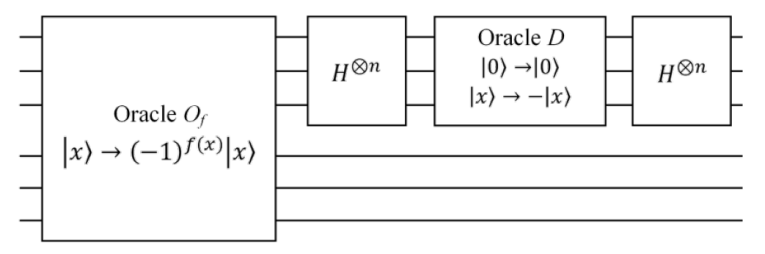
GROVER L K. Quantum Mechanics Helps in Searching for a Needle in a Haystack[J]. Physical Review Letters, 1997, 79(2): 325-328.
doi: 10.1103/PhysRevLett.79.325
URL
|
| [17] |
BRASSARD G, HOYER P, MOSCA M, et al. Quantum Amplitude Amplification and Estimation[J]. Contemporary Mathematics, 2002, 305: 53-74.
|
| [18] |
LAARHOVEN T, MOSCA M, VAN DE POL J. Solving the Shortest Vector Problem in Lattices Faster Using Quantum Search[C]// Springer. International Workshop on Post-Quantum Cryptography. Heidelberg: Springer, 2013: 83-101.
|
| [19] |
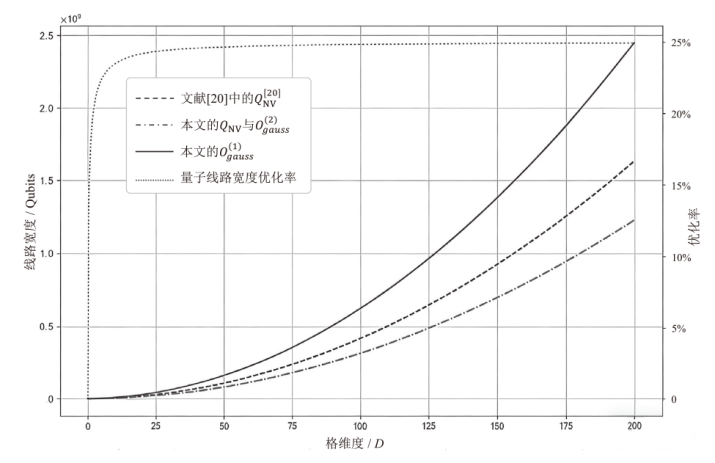
KIM H, JANG K, OH Y, et al. Finding Shortest Vector Using Quantum NV Sieve on Grover[C]// Springer. International Conference on Information Security and Cryptology. Heidelberg: Springer, 2023: 97-118.
|
| [20] |
KIM H, JANG K, KIM H, et al. Quantum NV Sieve on Grover for Solving Shortest Vector Problem[EB/OL]. (2024-05-29)[2025-02-01]. https://eprint.iacr.org/2024/712.
|
| [21] |
DORIGUELLO J F, GIAPITZAKIS G, LUONGO A, et al. On the Practicality of Quantum Sieving Algorithms for the Shortest Vector Problem[EB/OL]. (2024-10-17)[2025-02-01]. https://doi.org/10.48550/arXiv.2410.1375.
|
 )
)