Netinfo Security ›› 2024, Vol. 24 ›› Issue (6): 948-958.doi: 10.3969/j.issn.1671-1122.2024.06.012
Previous Articles Next Articles
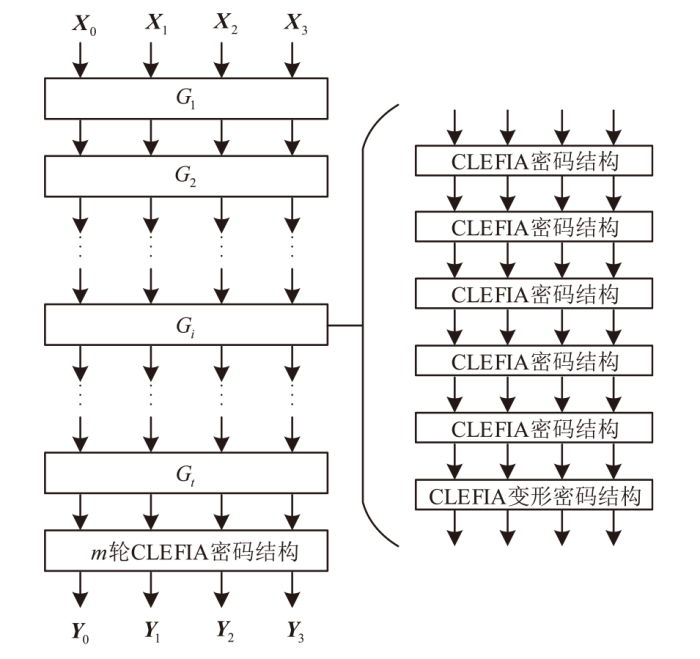
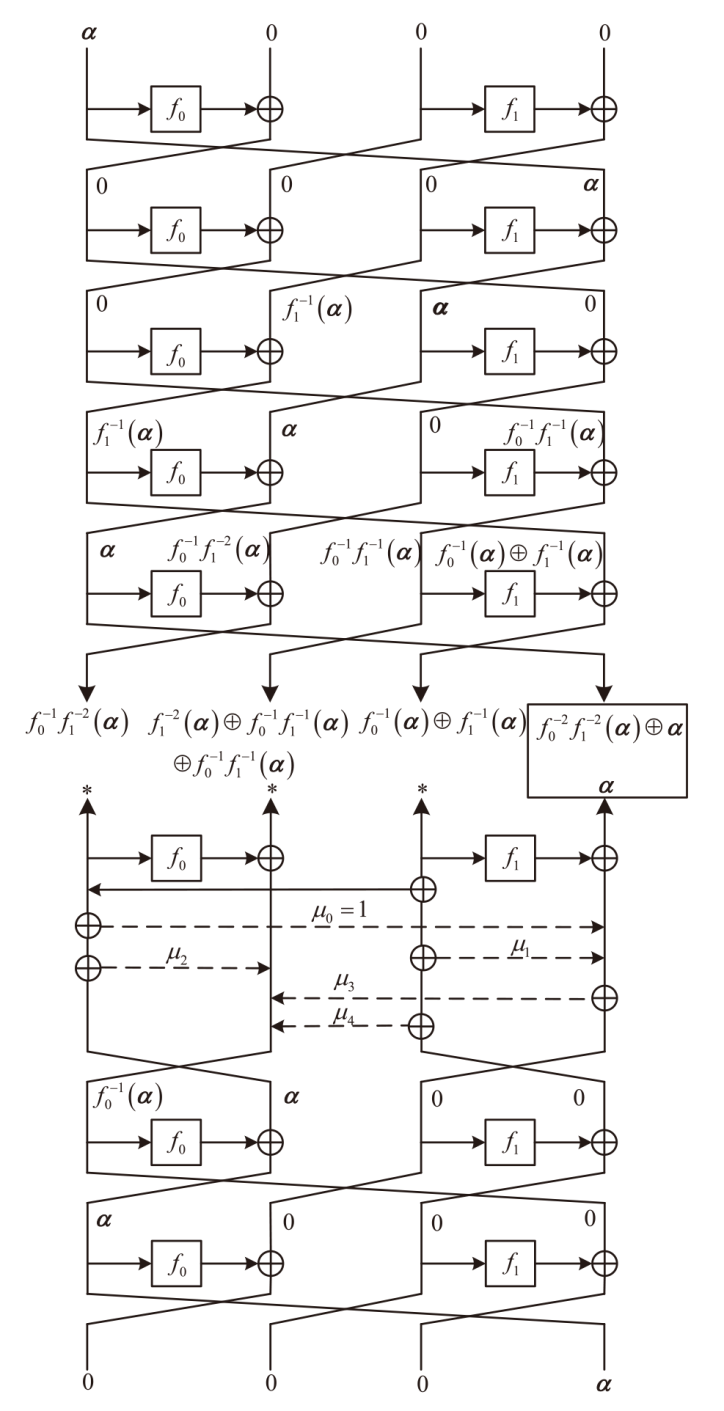
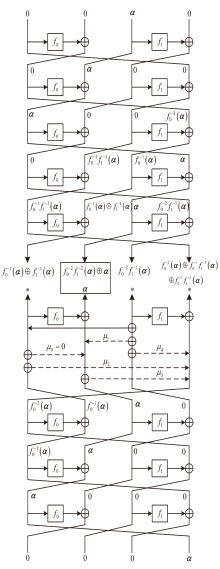
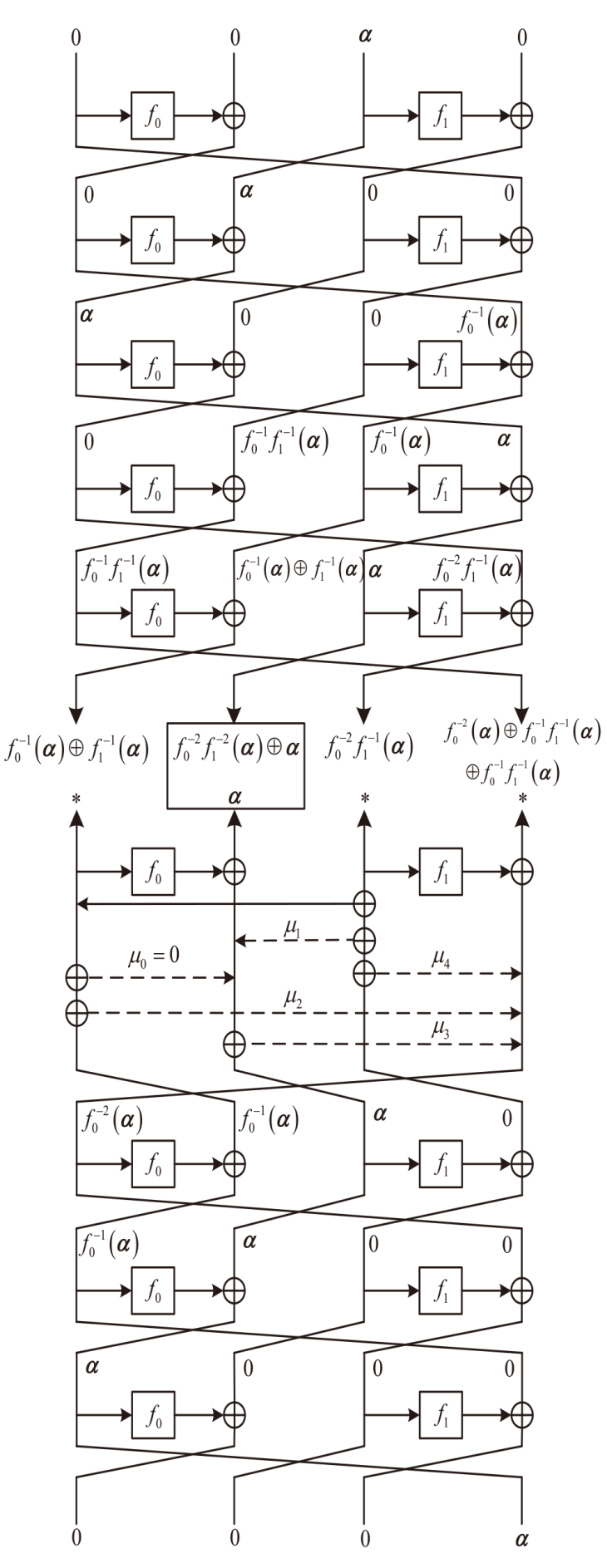
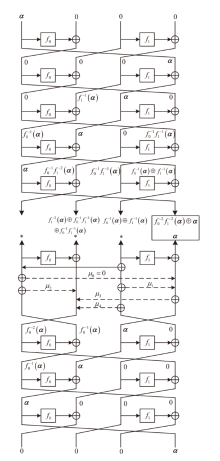
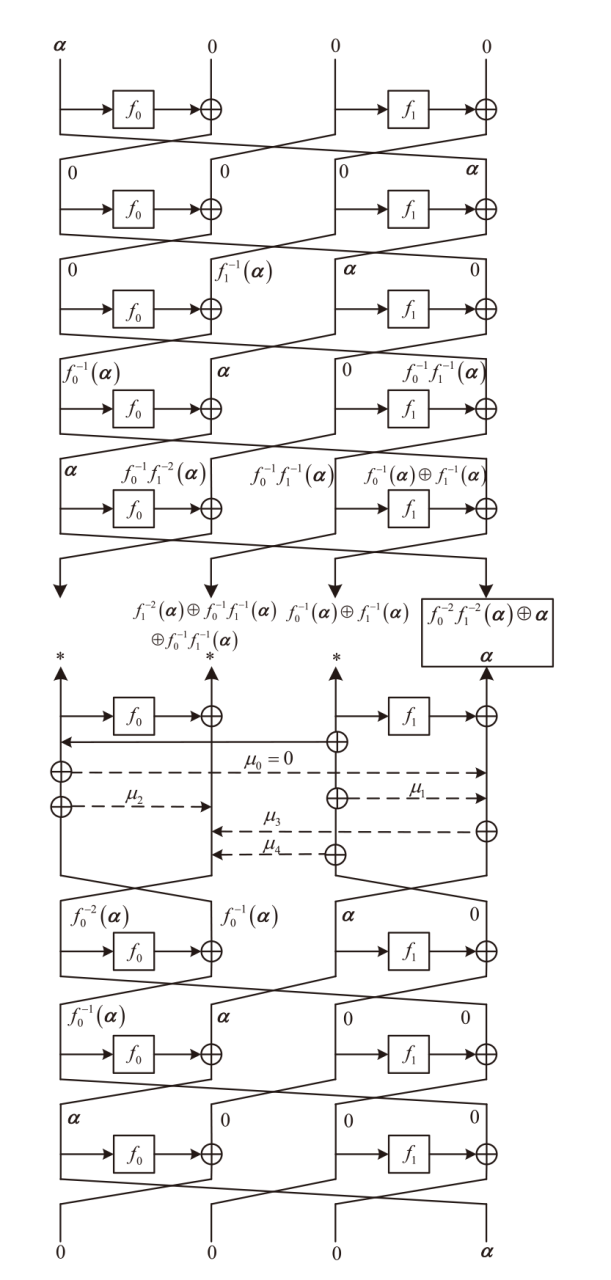
Research on the Construction of Zero-Correlation Linear Discriminator for CLEFIA Dynamic Cipher Structure
SHEN Xiamin, XIONG Tao( ), LI Hua, SHEN Xuan
), LI Hua, SHEN Xuan
- College of Information and Communication, National University of Defense Technology, Wuhan 430010, China
-
Received:2024-03-05Online:2024-06-10Published:2024-07-05
CLC Number:
Cite this article
SHEN Xiamin, XIONG Tao, LI Hua, SHEN Xuan. Research on the Construction of Zero-Correlation Linear Discriminator for CLEFIA Dynamic Cipher Structure[J]. Netinfo Security, 2024, 24(6): 948-958.
share this article
| [1] | WU Wenling, FENG Dengguo, ZHANG Wentao. Design and Analysis of Block Cipher(The Second Edition)[M]. Beijing: Tsinghua University Press, 2009. |
| 吴文玲, 冯登国, 张文涛. 分组密码的设计与分析(第二版)[M]. 北京: 清华大学出版社, 2009. | |
| [2] | ZHENG Jianhua, REN Sheng, JING Qing, et al. Z Cipher Scheme[J]. Journal of Cryptologic Research, 2018, 5(6): 579-590. |
|
郑建华, 任盛, 靖青, 等. Z密码算法设计方案[J]. 密码学报, 2018, 5(6): 579-590.
doi: 10.13868/j.cnki.jcr.000267 |
|
| [3] | YANG Hongzhi, HAN Wenbao, SI Xueming. New Design Method for Cipher Algorithms for Block Cipher[J]. Computer Science, 2010, 37(7): 102-104. |
| 杨宏志, 韩文报, 斯雪明. 一种新的密码算法设计方法[J]. 计算机科学, 2010, 37(7): 102-104. | |
| [4] | HU Xiangyi, LIU Tong. Research and Discussion on Dynamic Symmetric Cryptography Algorithm[J]. Network Security Technology and Application, 2006, 6(3): 69-71. |
| 胡祥义, 刘彤. 动态对称密码算法的研究与探讨[J]. 网络安全技术与应用, 2006, 6(3): 69-71. | |
| [5] | CHEN Like, ZHANG Runtong. Novel Software Block Cipher Using Dynamic S-Box and P-Box[J]. Computer Science, 2009, 36(2): 78-81. |
| 陈利科, 张润彤. 一种基于动态S-盒P-盒的快速分组密码算法—DSP[J]. 计算机科学, 2009, 36(2): 78-81. | |
| [6] |
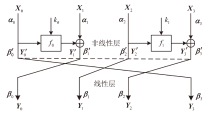
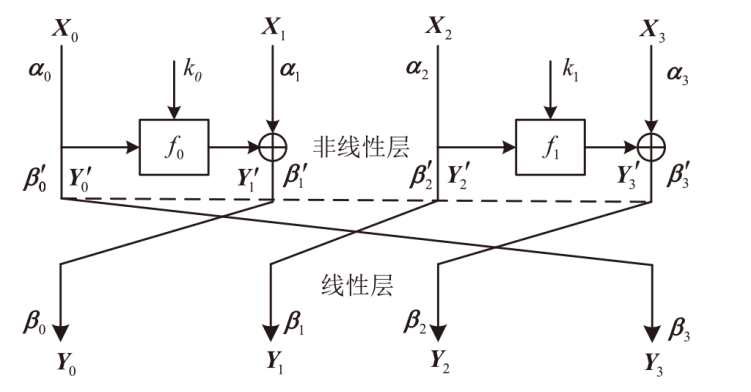
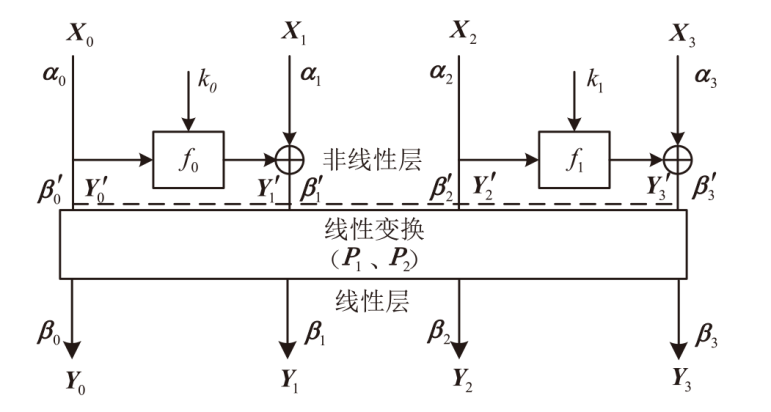
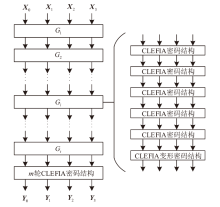
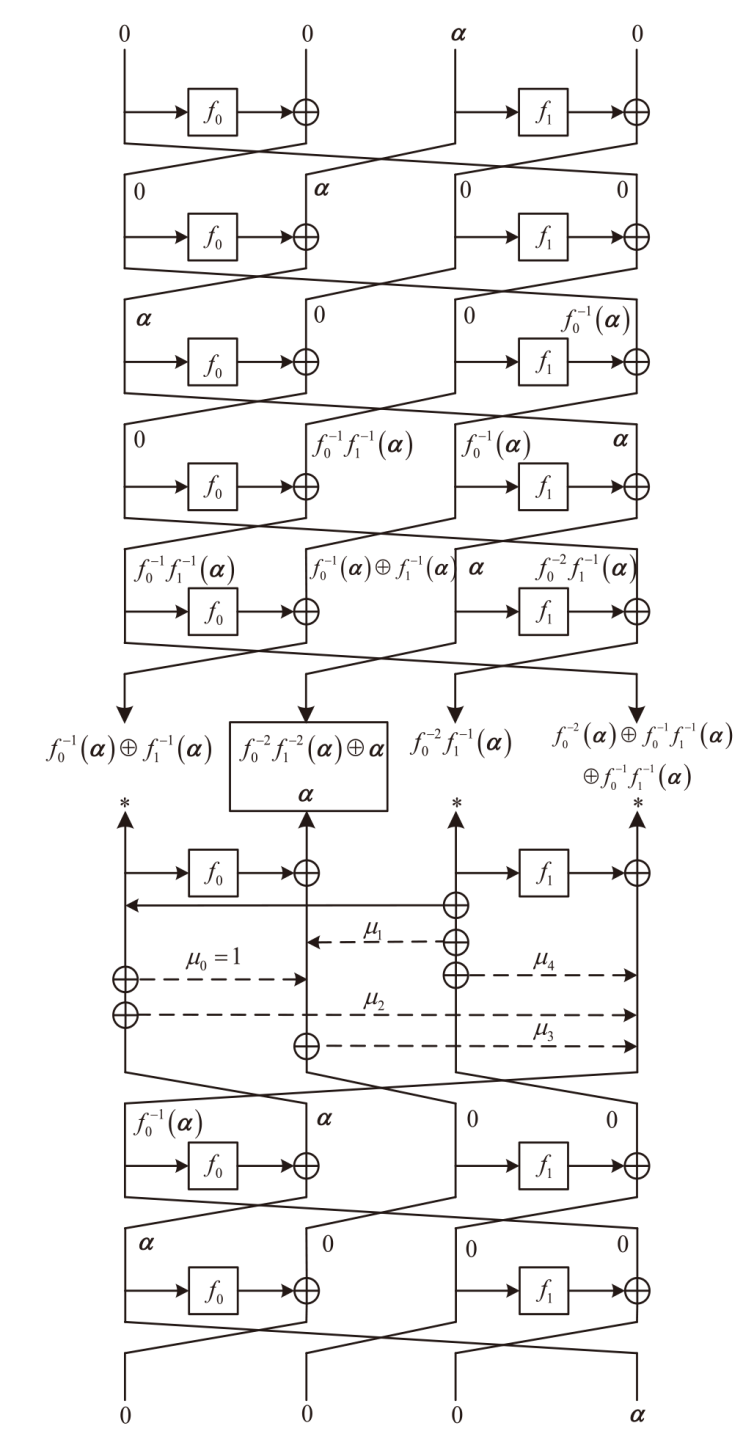
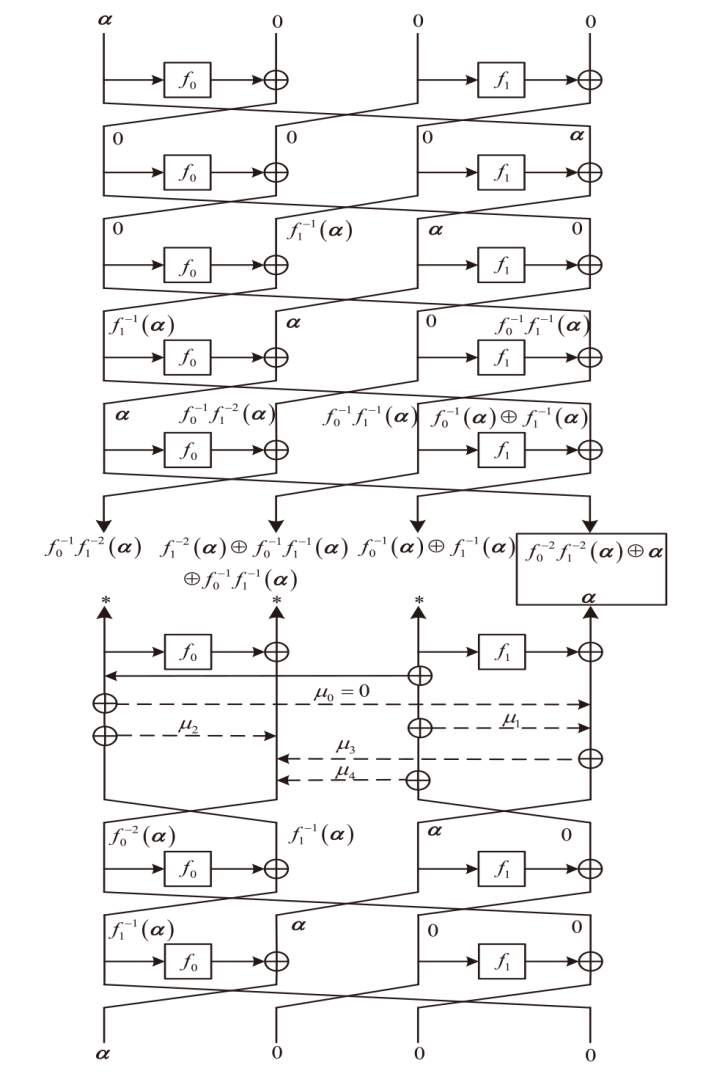
YANG Jilin, WANG Nianping. Security Evaluation Against Differential Cryptanalysis for CLEFIA-Like Dynamic Cryptographic Structure[J]. Acta Electronica Sinica, 2021, 49(11): 2279-2283.
doi: 10.12263/DZXB.20180973 |
|
杨继林, 王念平. 类CLEFIA动态密码结构抵抗差分密码分析能力评估[J]. 电子学报, 2021, 49(11): 2279-2283.
doi: 10.12263/DZXB.20180973 |
|
| [7] | ZHOU Shuyang, PENG Manman, XIAO Xiaohuan. An Improvement of SMS4 Algorithm Based on Dynamic[J]. Microelectronics & Computer, 2011, 28(9): 86-88. |
| 周术洋, 彭蔓蔓, 肖小欢. 一种基于动态思想的SMS4算法改进与实现[J]. 微电子学与计算机, 2011, 28(9): 86-88. | |
| [8] | LI Yanjun, WANG Qi, XIANG Yong, et al. Design and Implementation of Dynamic Cipher Component Involutory MDS Matrix[J]. Microelectronics & Computer, 2023, 37(12): 1-2. |
| 李艳俊, 王琦, 项勇, 等. 动态密码组件对合MDS矩阵的设计与实现[J]. 微电子学与计算机, 2023, 37(12): 1-2. | |
| [9] | SHIRAI T, SHIBUTANI K, AKISHITA T, et al. The 128-Bit Blockcipher CLEFIA (Extended Abstract)[C]// Springer. International Workshop on Fast Software Encryption. Heidelberg: Springer, 2007: 181-195. |
| [10] |
ZHONG Yue, GU Jieming, CAO Honglin. Survey of Lightweight Block Cipher[J]. Computer Science, 2023, 50(9): 3-15.
doi: 10.11896/jsjkx.230500190 |
|
钟悦, 谷杰铭, 曹洪林. 轻量级分组密码算法综述[J]. 计算机科学, 2023, 50(9): 3-15.
doi: 10.11896/jsjkx.230500190 |
|
| [11] |
WANG Nianping, GUO Zhicheng. Security Evaluation against Differential Cryptanalysis for Dynamic Cryptographic Structure[J]. Journal on Communications, 2021, 42(8): 70-79.
doi: 10.11959/j.issn.1000-436x.2021112 |
|
王念平, 郭祉成. 动态密码结构抵抗差分密码分析能力评估[J]. 通信学报, 2021, 42(8): 70-79.
doi: 10.11959/j.issn.1000-436x.2021112 |
|
| [12] | ZHANG Wenying, HAN Jing. Impossible Differential Analysis of Reduced Round CLEFIA[C]// Springer. Information Security & Cryptology. Heidelberg: Springer, 2009: 181-191. |
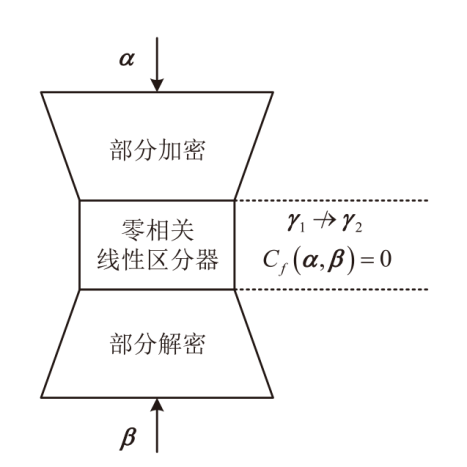
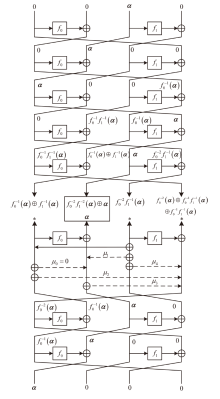
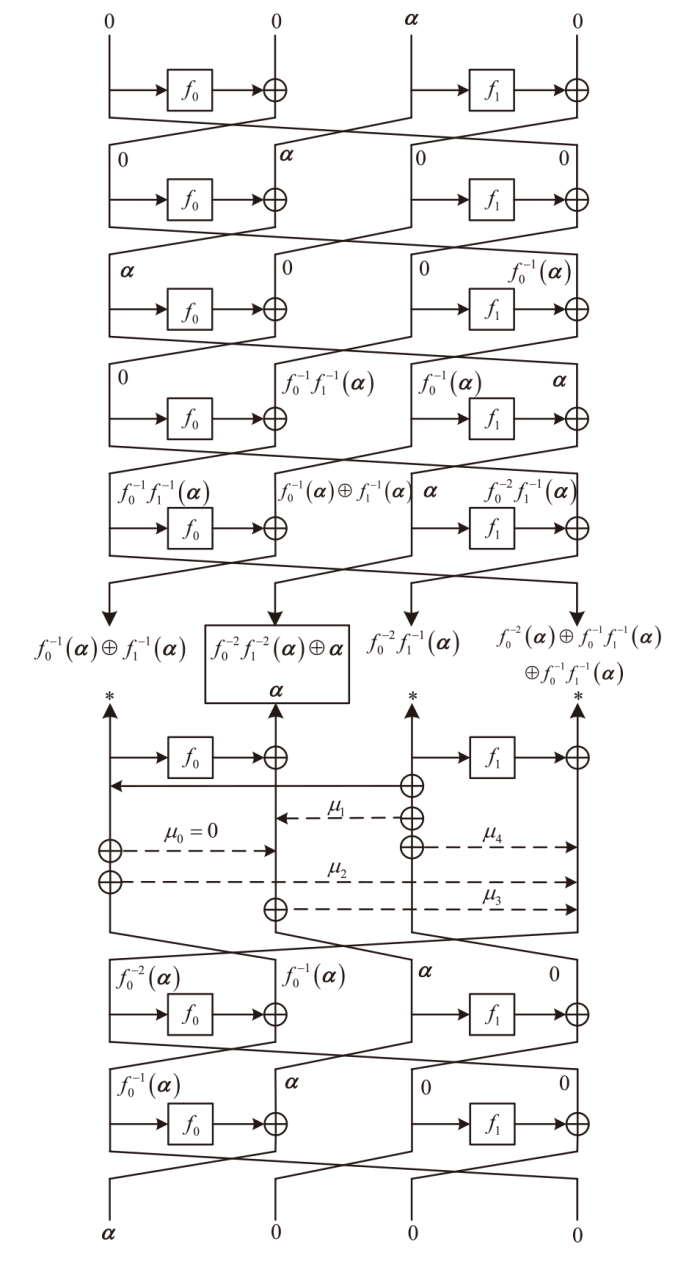
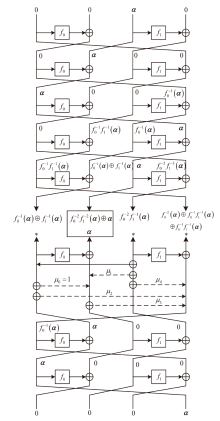
| [13] | CUI Ting, JIN Chenhui. Construction of Zero-Correlation Linear Hull for CLEFIA-Like Structure with SPN Round Functions[J]. Journal of Electronics&Information Technology, 2012, 34(1): 227-230. |
| 崔霆, 金晨辉. 嵌套代替-扩散网络的CLEFIA结构零相关线性逼近的构造[J]. 电子与信息学报, 2012, 34(1): 227-230. | |
| [14] | LI Yanjun, WU Wenling, ZHENG Xiulin. Integral Property Analysis on the Structure of SP-GFS[J]. Journal of Electronics & Information Technology, 2014, 36(8): 1798-1803. |
| 李艳俊, 吴文玲, 郑秀林. SP-GFS结构的积分性质研究[J]. 电子与信息学报, 2014, 36(8): 1798-1803. | |
| [15] | BOGDANOV A, RIJMEN V. Linear Hulls with Correlation Zero and Linear Cryptanalysis of Block Ciphers[J]. Designs, Codes and Cryptography, 2014, 70(3): 369-383. |
| [16] | BIHAM E, BIRYUKOV A, SHAMIR A. Cryptanalysis of Skipjack Reduced to 31 Rounds Using Impossible Differentials[J]. Journal of Cryptology, 1999, 18: 291-311. |
| [17] | SHEN Xuan, WANG Xinmei, HE Jun, et al. Revised Impossible Differential Crptanalysis of PFP Block Cipher[J]. Computer Science, 2020, 47(7): 263-267. |
| 沈璇, 王欣玫, 何俊, 等. PFP算法改进的不可能差分分析[J]. 计算机科学, 2020, 47(7): 263-267. | |
| [18] |
ZHAO Guangyao, SHEN Xuan, YU Bo, et al. Impossible Differential Cryptanalysis of Reduced-Round Ultra-Lightweight Block Cipher PFP[J]. Journal of Computer Applications, 2023, 43(9): 2784-2788.
doi: 10.11772/j.issn.1001-9081.2022091395 |
|
赵光耀, 沈璇, 余波, 等. 缩减轮的超轻量级分组密码算法PFP的不可能差分分析[J]. 计算机应用, 2023, 43(9): 2784-2788.
doi: 10.11772/j.issn.1001-9081.2022091395 |
|
| [19] | WANG Meiqin, WEN Long. Research on Zero-Correlation Linear Cryptanalysis[J]. Journal of Cryptologic Research, 2014, 1(3): 296-310. |
|
王美琴, 温隆. 零相关线性分析研究[J]. 密码学报, 2014, 1(3): 296-310.
doi: 10.13868/j.cnki.jcr.000028 |
|
| [20] | DIFFIE W, HELLMAN M E. Special Feature Exhaustive Cryptanalysis of the NBS Data Encryption Standard[J]. Computer, 2006, 10(6): 74-84. |
| [1] | ZHANG Xinglan, GUO Yankun, CHEN Fei, ZHANG Feng. Key Recovery Attacks on Block Cipher EM-Like Structures Based on Quantum Simon’s Algorithm [J]. Netinfo Security, 2024, 24(1): 106-112. |
| [2] | ZHANG Xiaolei, DAI Zibin, LIU Yanjiang, QU Tongzhou. Design of High Speed Reconfigurable Modulo Arithmetic Unit for Block Cipher [J]. Netinfo Security, 2023, 23(5): 76-84. |
| [3] | HU Yujia, DAI Zhengyi, SUN Bing. Differential-Linear Cryptanalysis of the SIMON Algorithm [J]. Netinfo Security, 2022, 22(9): 63-75. |
| [4] | TONG Xiaojun, SU Yuyue, ZHANG Miao, WANG Zhu. Lightweight Cipher Algorithm Based on Chaos and Improved Generalized Feistel Structure [J]. Netinfo Security, 2022, 22(8): 8-18. |
| [5] | YANG Yunxiao, SHEN Xuan, SUN Bing. Impossible Differential Cryptanalysis of Mysterion [J]. Netinfo Security, 2021, 21(8): 43-51. |
| [6] | WANG Jianxin, ZHOU Shiqiang, XIAO Chaoen, ZHANG Lei. High-speed Implementation of FESH Block Cipher Algorithm Based on FPGA [J]. Netinfo Security, 2021, 21(1): 57-64. |
| [7] | DONG Xiaoli, SHANG Shuai, CHEN Jie. Impossible Differential Attacks on 9-Round Block Cipher Rijndael-192 [J]. Netinfo Security, 2020, 20(4): 40-46. |
| [8] | Yong WANG. Study on New Mathematical Difficult Problem and Application in Block Cipher [J]. Netinfo Security, 2014, 15(11): 79-82. |
| [9] | Ping ZHANG, Chang-song CHEN, Hong-gang HU. Authenticated Encryption Modes Based on Block Ciphers [J]. Netinfo Security, 2014, 15(11): 8-10. |
| [10] | . Authenticated Encryption Modes Based on Block Ciphers [J]. , 2014, 14(11): 8-. |
| [11] | . Study on New Mathematical Difficult Problem and Application in Block Cipher [J]. , 2014, 14(11): 79-. |
| Viewed | ||||||
|
Full text |
|
|||||
|
Abstract |
|
|||||