信息网络安全 ›› 2022, Vol. 22 ›› Issue (7): 46-54.doi: 10.3969/j.issn.1671-1122.2022.07.006
宋词自动生成的信息隐藏算法
- 1.甘肃农业大学机电工程学院,兰州 730070
2.清华大学天津电子信息研究院,天津 300467
3.公安部网络安全保卫局,北京100006
4.清华大学电子工程系,北京 100084
5.公安部第一研究所,北京 100044
-
收稿日期:2022-02-26出版日期:2022-07-10发布日期:2022-08-17 -
通讯作者:杨婉霞 E-mail:yangwanxia@163.com -
作者简介:杨婉霞(1979—),女,甘肃,副教授,博士,主要研究方向为信息隐藏、自然语言处理|陈帅(1989—),男,河南,工程师,硕士,主要研究方向为网络安全、大数据应用技术|管磊(1988—),男,河北,博士研究生,主要研究方向为云计算、数据安全|杨忠良(1993—),男,湖北,博士后,主要研究方向为信息安全、自然语言处理 -
基金资助:国家自然科学基金(61862002)
Information Steganography Algorithm for Automatic Generation of Song Ci
YANG Wanxia1,2( ), CHEN Shuai3, GUAN Lei4,5, YANG Zhongliang2,4
), CHEN Shuai3, GUAN Lei4,5, YANG Zhongliang2,4
- 1. College of Mechanical and Electrical Engineering, Gansu Agricultural University, Lanzhou 730070, China
2. Institute for Electronics and Information Technology in Tianjin, Tsinghua University, Tianjin 300467, China
3. Network Security Bureau of the Ministry of Public Security, Beijing 100006, China
4. Department of Electronic Engineering, Tsinghua University, Beijing 100084, China
5. The First Research Institute of the Ministry of Public Security, Beijing 100044, China
-
Received:2022-02-26Online:2022-07-10Published:2022-08-17 -
Contact:YANG Wanxia E-mail:yangwanxia@163.com
摘要:
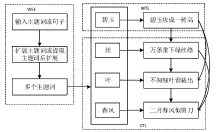
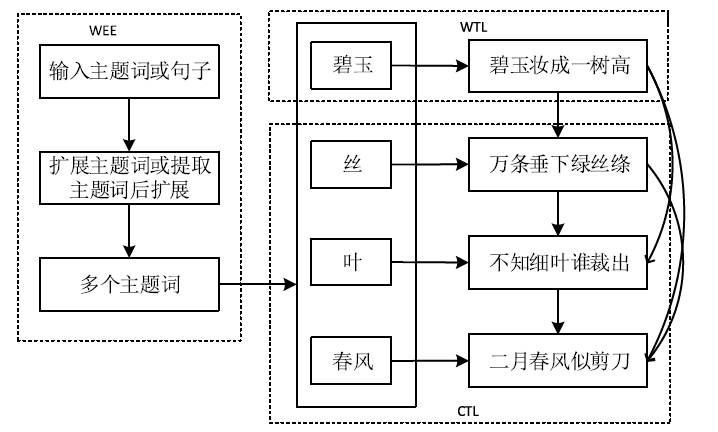
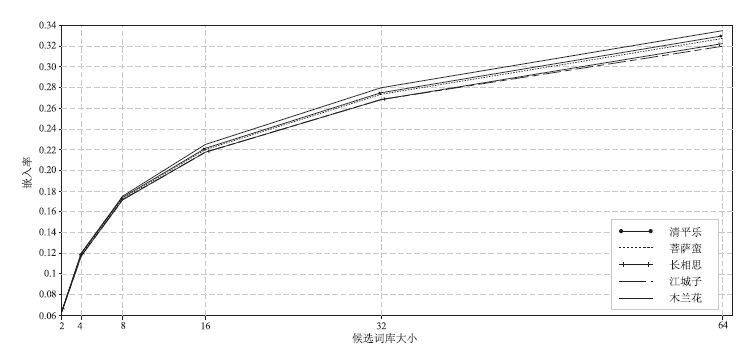
传统的文本隐写方案很难均衡隐藏容量和隐蔽性之间的矛盾。利用宋词载体语义丰富、句法灵活的特点,文章提出BERT(Bidirectional Encoder Representations from Transformers)词嵌入结合Attention机制的Seq2Seq模型生成隐写宋词的算法。该算法采用BERT词嵌入作为生成模型的语义向量转换部分,其丰富的词向量空间保证了生成句子间语义的连贯性,提高了生成宋词的质量。另外,该算法采用格律模板和互信息选词方法约束隐写语句的生成,增强了隐藏算法的安全性。通过与现有文本隐藏算法在嵌入率方面的对比实验和分析表明,文章所提算法的嵌入率相比Ci-stega提高了7%以上,且在安全性和鲁棒性方面均有良好的表现。
中图分类号:
引用本文
杨婉霞, 陈帅, 管磊, 杨忠良. 宋词自动生成的信息隐藏算法[J]. 信息网络安全, 2022, 22(7): 46-54.
YANG Wanxia, CHEN Shuai, GUAN Lei, YANG Zhongliang. Information Steganography Algorithm for Automatic Generation of Song Ci[J]. Netinfo Security, 2022, 22(7): 46-54.
| [1] | ZHANG Zhenyu, LI Qianmu, QI Yong. Text Watermarking Design Based on Invisible Characters[J]. Journal of Nanjing University of Science and Technology, 2017, 41(4): 405-411. |
| 张震宇, 李千目, 戚湧. 基于不可见字符的文本水印设计[J]. 南京理工大学学报(自然科学版), 2017, 41(4): 405-411. | |
| [2] | WU Guohua, GONG Lichun, YUAN Lifeng, et al. Review of Information Hiding on Chinese Text[J]. Journal on Communications, 2019, 40(9): 145-156. |
| 吴国华, 龚礼春, 袁理锋, 等. 中文文本信息隐藏研究进展[J]. 通信学报, 2019, 40(9): 145-156. | |
| [3] | BEHROOZ K, BEHNAM K, BAHMAN K, et al. A New Method for pdf Steganography in Justified Texts[J]. Journal of Information Security and Applications, 2019(45): 61-70. |
| [4] | YU Zhenshan, HUANG Liusheng, CHEN Zhili, et al. High Embedding Ratio Text Steganography by Ci-Poetry of the Song Dynasty[J]. Journal of Chinese Information Processing, 2009, 23(4): 55-63. |
| 余振山, 黄刘生, 陈志立, 等. 用宋词实现高嵌入率文本信息隐藏[J]. 中文信息学报, 2009, 23(4): 55-63. | |
| [5] |
ALOTAIBI R A, ELREFAEI L A. Improved Capacity Arabic Text Watermarking Methods Based on Open Word Space[J]. Journal of King Saud University-Computer and Information Sciences, 2018, 30(2): 236-248.
doi: 10.1016/j.jksuci.2016.12.007 URL |
| [6] | ZHANG Wei, WANG Xiaomei, ZHANG Chenxu. Coverless Text Steganography Method Based on Tone Feature Mapping[J]. Journal of Information Engineering University, 2021, 22(1): 38-43. |
| 张维, 王晓梅, 张晨旭. 一种基于声调特征映射的无载体信息隐藏方法[J]. 信息工程大学学报, 2021, 22(1): 38-43. | |
| [7] | CHEN Xianyi, CHEN Sheng, WU Yulei. Coverless Information Hiding Method Based on the Chinese Character Encoding[J]. Journal of Internet Technology, 2017, 18(2): 313-320. |
| [8] | ZHANG Jianjun, WANG Lucai, LIN Haijun. Coverless Text Information Hiding Method Based on the Word Rank Map[J]. Journal of Internet Technology, 2017, 18(2): 427-434. |
| [9] |
YANG Zhongliang, GUO Xiaoqing, CHEN Ziming, et al. RNN-Stega: Linguistic Steganography Based on Recurrent Neural Networks[J]. IEEE Transactions on Information Forensics and Security, 2019, 14(5): 1280-1295.
doi: 10.1109/TIFS.2018.2871746 URL |
| [10] | KANG Huixian, WU Hanzhou, ZHANG Xinpeng. Generative Text Steganography Based on LSTM Network and Attention Mechanism with Keywords[J]. Electronic Imaging, 2020(4): 291-298. |
| [11] | LIU Yanchen, WANG Jian, WANG Zhibin, et al. A Technique of High Embedding Rate Text Steganography Based on Whole Poetry of Song Dynasty[C]// Springer. Proceedings of the Second International Conference on Cloud Computing and Security. Berlin: Springer, 2016: 178-189. |
| [12] | LUO Yubo, HUANG Yongfeng, LI Fufang, et al. Text Steganography Based on Ci-Poetry Generation Using Markov Chain Model[J]. KSII Transactions on Internet and Information Systems, 2016, 10(9): 4568-4584. |
| [13] | YI Xiaoyuan, LI Ruoyu, SUN Maosong. Generating Chinese Classical Poems with RNN Encode-Decoder[C]// IEEE. Proceedings of the 16th Chinese Computational Linguistics. New York: IEEE, 2017: 211-223. |
| [14] | YI Xiaoyuan, SUN Maosong, LI Ruoyu, et al. Chinese Poetry Generation with a Working Memory Mode[C]// ACM. Proceding of the 27th International Joint Conference on Artificial Intelligence. New York: ACM, 2018: 4553-4559. |
| [15] | LUO Yubo, HUANG Yongfeng. Text Steganography with High Embedding Rate: Using Recurrent Neural Networks to Generate Chinese Classic Poetry[C]// ACM. Proceedings of the Seventh ACM Workshop on Information Hiding & Multimedia Security. New York: ACM, 2017: 99-104. |
| [16] | QIN Chuan, WANG Meng, SI Guangwen, et al. Constructive Information Hiding with Chinese Quatrain Generation[J]. Chinese Journal of Computers, 2021, 44(4): 773-785. |
| 秦川, 王萌, 司广文, 等. 基于绝句生成的构造式信息隐藏算法[J]. 计算机学报, 2021, 44(4): 773-785. | |
| [17] |
ZHENG Haitao, WANG Wei, CHEN Wang, et al. Automatic Generation of News Comments Based on Gated Attention Neural Networks[J]. IEEE Access, 2018, 6: 702-710.
doi: 10.1109/ACCESS.2017.2774839 URL |
| [18] | MA Liang, WANG Zili, YANG Fan, et al. Robust State of Charge Estimation Based on a Sequence-to-Sequence Mapping Model with Process Information[J]. Journal of Power Sources, 2020(474): 30-35. |
| [19] | LI Xuehong, GUO Hui, ANG Chaoqun. Text Digital Watermarking Algorithm Based on Improve Line Shift Coding[J]. Computer & Digital Engineering, 2014, 42(9): 1687-1690, 1712. |
| 李雪红, 郭晖, 昂朝群. 改进行移编码的文本数字水印算法研究[J]. 计算机与数字工程, 2014, 42(9): 1687-1690,1712. | |
| [20] | KIM M Y, ZAIANE O R. Natural Lanuage Watermarking Based on Syntactic Displacement and Morphological Divsion[C]// IEEE. Computer Software and Applications Conference Workshops (COMPSACW). New York:IEEE, 2010: 164-169. |
| [21] | CHAPMAN M, DAVIDA G. Hiding the Hidden: A Software System for Concealing Ciphertext in Innocuous Text[C]// Springer. Proceedings of the International Conference on Information and Communications Security. Berlin: Springer, 1997: 335-345. |
| [1] | 陈帆;林和;石周;崔伟男. 基于互信息变化率的属性约简算法[J]. , 2012, 12(7): 0-0. |
| 阅读次数 | ||||||
|
全文 |
|
|||||
|
摘要 |
|
|||||