信息网络安全 ›› 2023, Vol. 23 ›› Issue (2): 19-25.doi: 10.3969/j.issn.1671-1122.2023.02.003
基于改进贝叶斯网络的高维数据本地差分隐私方法
- 1.北京交通大学智能交通数据安全与隐私保护北京市重点实验室,北京 100044
2.北京交通大学计算机与信息技术学院,北京 100044
3.山东省计算中心,济南 250014
4.山东正中信息技术股份有限公司,济南 250014
-
收稿日期:2022-04-24出版日期:2023-02-10发布日期:2023-02-28 -
通讯作者:赵佳 E-mail:zhaojia@bjtu.edu.cn -
作者简介:赵佳(1980—),女,内蒙古,副教授,博士,主要研究方向为网络空间安全、可信计算、隐私保护|高塔(1996—),女,河北,硕士研究生,主要研究方向为网络空间安全|张建成(1973—),男,河南,副研究员,硕士,主要研究方向为密码技术、物联网安全、信息系统咨询与信息标准化 -
基金资助:国家自然科学基金青年科学基金(61502030);中央高校基本科研业务费(2018JBM016);山东省重大科技创新工程项目(2019JZZY020128)
Method of Local Differential Privacy Method for High-Dimensional Data Based on Improved Bayesian Network
ZHAO Jia1,2( ), GAO Ta1,2, ZHANG Jiancheng3,4
), GAO Ta1,2, ZHANG Jiancheng3,4
- 1. Beijing Key Laboratory of Security and Privacy in Intelligent Transportation, Beijing Jiaotong University, Beijing 100044, China
2. School of Computer and Information Technology, Beijing Jiaotong University, Beijing 100044, China
3. Shandong Computer Science Center, Jinan 250014, China
4. Shandong Zhengzhong Information Technology Co., Ltd., Jinan 250014, China
-
Received:2022-04-24Online:2023-02-10Published:2023-02-28 -
Contact:ZHAO Jia E-mail:zhaojia@bjtu.edu.cn
摘要:
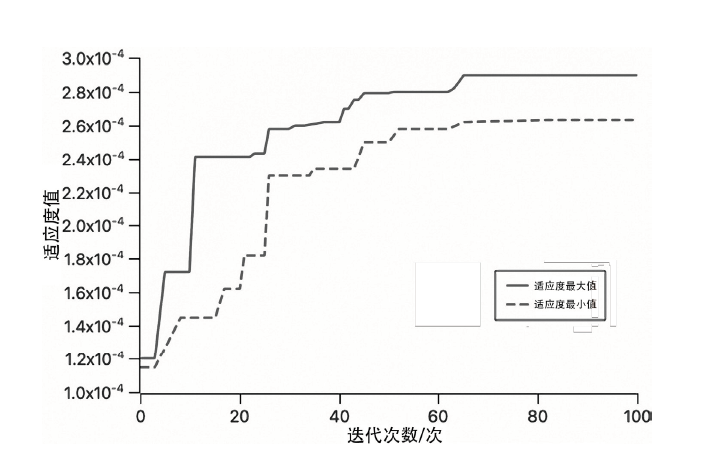
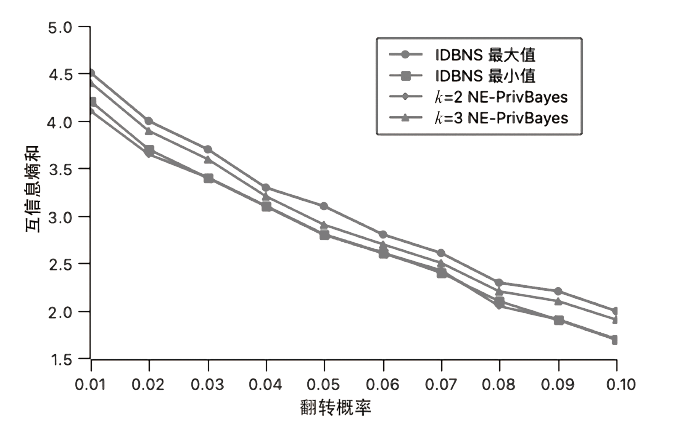
文章提出一种基于改进贝叶斯网络的高维数据本地差分隐私方法,首先通过数据源差分隐私保护算法对用户端数据集进行扰动,生成扰动数据集,保护本地原始数据集隐私;然后通过改进的贝叶斯网络将高维数据集降维为多个低维属性集合;最后合成新数据集,使用人工蜂群算法对贝叶斯网络结构进一步改进。实验结果表明,该方法在数据实用性方面具有优势,且得到的贝叶斯网络收敛性更好。
中图分类号:
引用本文
赵佳, 高塔, 张建成. 基于改进贝叶斯网络的高维数据本地差分隐私方法[J]. 信息网络安全, 2023, 23(2): 19-25.
ZHAO Jia, GAO Ta, ZHANG Jiancheng. Method of Local Differential Privacy Method for High-Dimensional Data Based on Improved Bayesian Network[J]. Netinfo Security, 2023, 23(2): 19-25.
| [1] | DWORK C. Differential Privacy[M]. Heidelberg: Springer, 2006. |
| [2] | DWORK C, ROTH A. The Algorithmic Foundations of Differential Privacy[EB/OL]. [2020-12-10]. https://www.microsoft.com/en-us/research/publication/algorithmic-foundations-differential-privacy/. |
| [3] |
SWEENEY L. k-Anonymity: a Model for Protecting Privacy[J]. International Journal of Uncertainty Fuzziness and Knowledge-Based Systems, 2002, 10(5): 557-570.
doi: 10.1142/S0218488502001648 URL |
| [4] | MACHANVAJJHALA A, KIFER D, GEHRKE J. L-Diversity: Privacy beyond k-Anonymity[J]. ACM Trans on Knowledge Discovery and from Data, 2007, 1(1): 1-52. |
| [5] |
SWEENEY L. Achieving k-Anonynity Privacy Protection Using Generalization and Suppression[J]. Fuzziness and Knowledge-Based Systems, 2002, 10(5): 571-588.
doi: 10.1142/S021848850200165X URL |
| [6] | LI Ninghui, LI Tiancheng, VENKATASUBRAMANIAN S. t-Closeness: Privacy beyond k-Anonymity and l-Diversity[C]// IEEE. 23rd IEEE International Conference on Data Engineering. New York: IEEE, 2007: 106-115. |
| [7] | WONG R C W, LI Jiuyong, FU A W C, et al. (a,k)-Anonymity: An Enhanced k-Anonymity Model for Privacy Preserving Data Publishing[C]// ACM. 12th ACMSIGKDD International Conference on Knowledge Discovery and Data Mining(KDD). New York:ACM, 2006: 754-759. |
| [8] | DWORK C, MCSHERRY F, NISSIM K, et al. Calibrating Noise to Sensitivity in Private Data Analysis[C]// IACR. 3rd Theory of Cryptography. Heidelberg: Springer, 2006: 265-284. |
| [9] | ROTH A, ROUGHGARDEN T. Interactine Privacy via the Median Mechanism[C]// ACM. 42nd ACM Symposium on Theory of Computing. New York: ACM, 2010: 765-774. |
| [10] | HAY M, RASTOGI V, MIKLAU G, et al. Boosting the Accuracy of Differentially Private Histograms through Consistency[J]. VLDB Endowment, 2010, 3(1): 1021-1032. |
| [11] |
XU Jia, ZHANG Zhenjie, XIAO Xiaokui. Differentially Private Histogram Publication[J]. The VLDB Journal, 2013, 22(6): 797-822.
doi: 10.1007/s00778-013-0309-y URL |
| [12] | ZHANG Xiaojian, SHAO Chao, MENG Xiaofeng. Accurate Histogram Release under Differential Privacy[J]. Journal of Computer Research and Development, 2016, 53(5): 1106-1117. |
| 张啸剑, 邵超, 孟小峰. 差分隐私下一种精确直方图发布方法[J]. 计算机研究与发展, 2016, 53(5):1106-1117. | |
| [13] | YANG Geng, XIA Chunting, BAI Yunlu. Algorithm for Differential Privacy Histogram for Real-Time Data Flow[J]. Journal of Nanjing University of Posts and Telecommunications(Natural Science Edition), 2018, 38(2): 69-77. |
| 杨庚, 夏春婷, 白云璐. 面向实时数据流的差分隐私直方图发布技术[J]. 南京邮电大学学报:自然科学版, 2018, 38(2):69-77. | |
| [14] | XU Chugui, REN Jun, ZHANG Yaoxue, et al. DPPro: Differentially Private High-Dimensional Data Release via Random Projection[J]. IEEE Transactions on Information Forensics & Security, 2017, 12(12): 3081-3093. |
| [15] | CHEN Rui, MOHAMMED N, FUNG B, et al. Publishing SetValued Data via Differential Privacy[J]. VLDB Endowment, 2011, 4(11): 1087-1098. |
| [16] | QARDAJI W, YANGWeining, LINinghui. Priview: Practical Differentially Private Release of Marginal Contingency Tables[C]// ACM. 2014 ACM SIGMOD International Conference on Management of Data. New York: ACM, 2014, 1435-1446. |
| [17] |
REN Xuebin, YU C M, YU Weiren, et al. LoPub: High-Dimensional Crowdsourced Data Publication with Local Differential Privacy[J]. IEEE Transactions on Information Forensics and Security, 2018, 13(9): 2151-2166.
doi: 10.1109/TIFS.2018.2812146 URL |
| [18] | DWORK C, KENTHAPADI K, MCSHERRY F, et al. Ourdata, Ourselves: Privacy via Distributed Noise Generation[C]// IACR. 24th Annual International Conference on the Theory and Applications of Cryptographic Techniques. Heidelberg: Springer, 2006: 486-503. |
| [19] | XIAO Biao, YAN Hongqiang, LUO Haining, et al. Research on Improvement of Bayesian Network Privacy Protection Algorithm Based on Differential Privacy[J]. Netinfo Security, 2020, 20(11): 75-86. |
| 肖彪, 闫宏强, 罗海宁, 等. 基于差分隐私的贝叶斯网络隐私保护算法的改进研究[J]. 信息网络安全, 2020, 20(11):75-86. | |
| [20] | XU Chugui, REN Ju, ZHANG Deyu. Distilling at the Edge: A Local Differential Privacy Obfuscation Framework for IoT Data Analytics[J]. IEEE Communications Magazine, 2018, 56(8): 20-25. |
| [21] | ZHANG Jiacheng, PENG Jia, WANG Lei. A Graph Information Collection Method Based on Local Differential Privacy in Big Data Environment[J]. Netinfo Security, 2020, 20(6): 44-56. |
| 张佳程, 彭佳, 王雷. 大数据环境下的本地差分隐私图信息收集方法[J]. 信息网络安全, 2020, 20(6):44-56. | |
| [22] | LARRANNAGA P, POZA M, YURRAMENDI Y. Structure Learning of Bayesian Networks by Genetic Algorithms: A Performance Analysis of Control Parameters[J]. IEEE Transactions on Pattern Analysis and Machine Intelligence, 1996, 18(9): 921-926. |
| [23] | ZHENG Zehao. Research on State Evaluation Method of Intelligent Electric EnergyMeter Based on Bayesian Network and Emseble Learning[D]. Changchun: Jilin University, 2020. |
| 郑泽豪. 基于贝叶斯网和集成学习的智能电能表状态评价方法研究[D]. 长春: 吉林大学, 2020. |
| [1] | 顾兆军, 杨睿, 隋翯. 面向网络架构的系统攻击面建模方法[J]. 信息网络安全, 2022, 22(3): 29-38. |
| [2] | 罗文华, 张耀文. 基于贝叶斯网络的电信网络诈骗受害人特征分析[J]. 信息网络安全, 2021, 21(12): 25-30. |
| [3] | 朱容辰, 李欣, 林小暖. 基于贝叶斯网络的视频专网安全风险分析方法[J]. 信息网络安全, 2021, 21(12): 91-101. |
| [4] | 张佳程, 彭佳, 王雷. 大数据环境下的本地差分隐私图信息收集方法[J]. 信息网络安全, 2020, 20(6): 44-56. |
| [5] | 肖彪, 闫宏强, 罗海宁, 李炬成. 基于差分隐私的贝叶斯网络隐私保护算法的改进研究[J]. 信息网络安全, 2020, 20(11): 75-86. |
| [6] | 何一青. 一种基于有向二分图模型和贝叶斯网络的入侵检测方法[J]. , 2012, 12(8): 0-0. |
| 阅读次数 | ||||||
|
全文 |
|
|||||
|
摘要 |
|
|||||