信息网络安全 ›› 2026, Vol. 26 ›› Issue (2): 224-235.doi: 10.3969/j.issn.1671-1122.2026.02.004
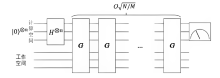
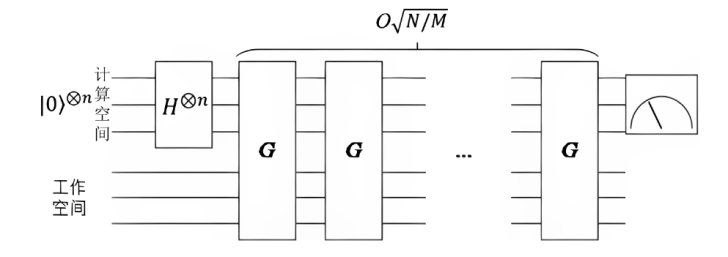
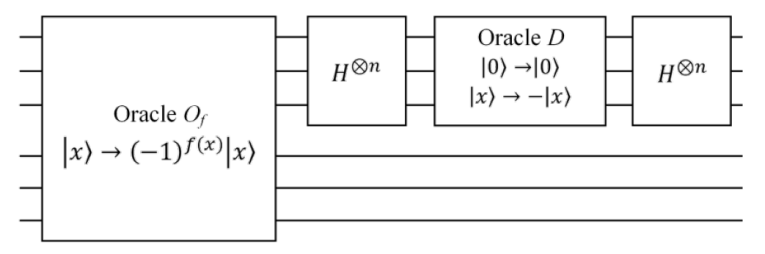
基于Grover算法的高斯筛法量子线路设计方法
1.中国科学技术大学网络空间安全学院 合肥 230027 2.中国科学院电磁空间信息重点实验室 合肥 230027
-
收稿日期:2025-10-18出版日期:2026-02-10发布日期:2026-02-23 -
通讯作者:胡红钢 hghu2005@ustc.edu.cn -
作者简介:曹仁龙(2000—),男,安徽,硕士研究生,主要研究方向为格密码及应用|胡红钢(1978—),男,四川,教授,博士,主要研究方向为密码学理论及应用 -
基金资助:国家自然科学基金(62472397)
Gauss Sieve Quantum Circuit Design Method Based on Grover’s Algorithm
CAO Renlong1, HU Honggang1,2( )
)
1. School of Cyber Science and Technology ,University of Science and Technology of China Hefei 230027, China 2. Key Laboratory of Electromagnetic Space Information ,Chinese Academy of Science Hefei 230027, China
-
Received:2025-10-18Online:2026-02-10Published:2026-02-23
摘要:
筛法是求解格中最短向量问题的最快方法。在实际应用中,启发式筛法因其较低的时间复杂度和卓越的攻击效率,成为针对格密码算法的新型攻击手段。随着量子计算技术迅猛发展,量子算法的引入使量子筛法在理论上能够达到最优的渐近时间复杂度,但目前针对量子筛法的电路设计研究仍处于初级阶段。因此,文章提出一种基于Grover量子搜索算法的高斯筛法量子线路设计方案,深入探讨高斯筛法中两个核心搜索过程的量子电路设计及其关键操作,并成功构建相应Oracle黑盒的量子线路。通过玩具示例验证该方案不仅能够在量子计算模型下正确执行,而且能有效降低高斯筛法的时间复杂度。
中图分类号:
引用本文
曹仁龙, 胡红钢. 基于Grover算法的高斯筛法量子线路设计方法[J]. 信息网络安全, 2026, 26(2): 224-235.
CAO Renlong, HU Honggang. Gauss Sieve Quantum Circuit Design Method Based on Grover’s Algorithm[J]. Netinfo Security, 2026, 26(2): 224-235.
表1
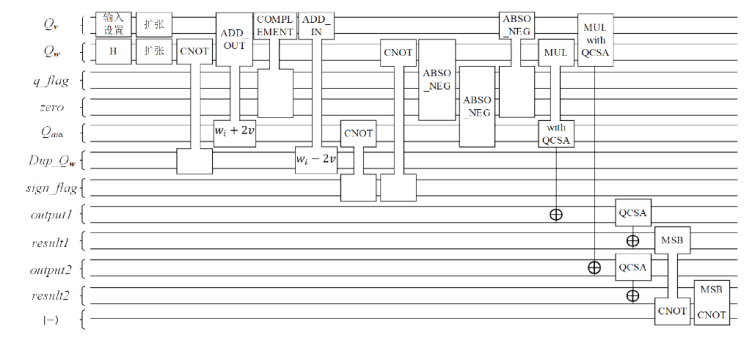
预言机$O_{\text{gauss}}^{\left( 1 \right)}$的逐步执行结果
| 算法步骤 | 经典/量子寄存器变量 | 值 |
|---|---|---|
| STEP 1 | {2,-8, 6,-4, 10} | |
| {2,-3, 1,-3, 6} | ||
| STEP 2 | {2,-8, 6,-4, 10} | |
| {2,-3, 1,-3, 6} | ||
| STEP 3 | {2,-3, 1,-3, 6} | |
| STEP 4.1 | {4,-11, 7,-7, 16} | |
| STEP 4.2 | {-2, 8,-6, 4,-10} | |
| STEP 4.3 | {0, 5,-5, 1,-4} | |
| STEP 5.1 | sign_flag [0: rank-1] | {0, 0, 0, 0, 0} |
| STEP 5.2 | sign_flag [rank: 2rank-1] | {0, 1, 1, 1, 1} |
| STEP 5.3 | {0, 5, 5, 1, 4} | |
| {2, 3, 1, 3, 6} | ||
| {4, 11, 7, 7, 16} | ||
| STEP 5.4 | output1 | {8, 33, 7, 21, 96} |
| STEP 5.5 | output2 | {0,-15,-5,-3,-24} |
| STEP 6 | result1 | |
| result2 | ||
| STEP 7 | MSB | 0 |
| MSB | 1 |
表2
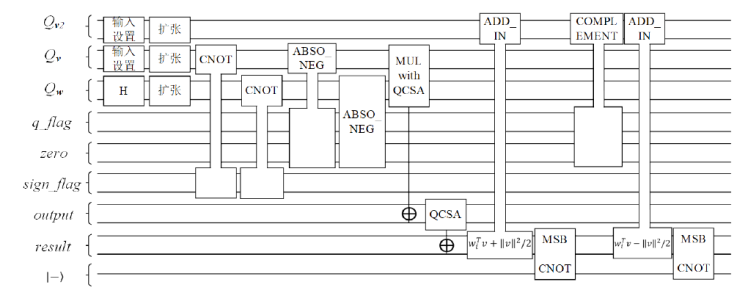
预言机$O_{\text{gauss}}^{\left( 2 \right)}$的逐步执行结果
| 算法步骤 | 经典/量子寄存器变量 | 值 |
|---|---|---|
| STEP 1 | {1,-4, 3,-2, 5} | |
| {-2, 3,-1, 3, 6} | ||
| STEP 2 | {1,-4, 3,-2, 5} | |
| {-2, 3,-1, 3, 6} | ||
| STEP 3.1 | sign_flag[0: rank-1] | {1, 1, 1, 1, 0} |
| {1, 4, 3, 2, 5} | ||
| {2, 3, 1, 3, 6} | ||
| STEP 3.2 | output | {-2,-12,-3,-6, 30} |
| STEP 4 | result | |
| STEP 5.1 | result | |
| STEP 5.2 | MSB | 0 |
| STEP 6.1 | ||
| STEP 6.2 | result | |
| STEP 6.3 | MSB | 1 |
| [1] |
HELLMAN M. New Directions in Cryptography[J]. IEEE Transactions on Information Theory, 1976, 22(6): 644-654.
doi: 10.1109/TIT.1976.1055638 URL |
| [2] |
RIVEST R L, SHAMIR A, ADLEMAN L. A Method for Obtaining Digital Signatures and Public-Key Cryptosystems[J]. Communications of the ACM, 1978, 21(2): 120-126.
doi: 10.1145/359340.359342 URL |
| [3] |
ELGAMAL T. A Public Key Cryptosystem and a Signature Scheme Based on Discrete Logarithms[J]. IEEE Transactions on Information Theory, 1985, 31(4): 469-472.
doi: 10.1109/TIT.1985.1057074 URL |
| [4] | MERKLE R, HELLMAN M. Hiding Information and Signatures in Trapdoor Knapsacks[J]. IEEE Transactions on Information Theory, 1978, 24(5): 525-530. |
| [5] | SHOR P W. Algorithms for Quantum Computation: Discrete Logarithms and Factoring[C]// IEEE. The 35th Annual Symposium on Foundations of Computer Science. New York: IEEE, 1994: 124-134. |
| [6] |
LAGARIAS J C, ODLYZKO A M. Solving Low-Density Subset Sum Problems[J]. Journal of the ACM (JACM), 1985, 32(1): 229-246.
doi: 10.1145/2455.2461 URL |
| [7] | COSTER M J, LAMACCHIA B A, ODLYZKO A M, et al. An Improved Low-Density Subset Sum Algorithm[C]// Springer. Workshop on the Theory and Application of Cryptographic Techniques. Heidelberg: Springer, 1991: 54-67. |
| [8] | COPPERSMITH D. Finding a Small Root of a Univariate Modular Equation[C]// Springer. International Conference on the Theory and Applications of Cryptographic Techniques. Heidelberg: Springer, 1996: 155-165. |
| [9] | COPPERSMITH D. Finding a Small Root of a Bivariate Integer Equation; Factoring with High Bits Known[C]// Springer. International Conference on the Theory and Applications of Cryptographic Techniques. Heidelberg: Springer, 1996: 178-189. |
| [10] | VAN EMDE BOAS P. Another NP-Complete Problem and the Complexity of Computing Short Vectors in a Lattice[D]. Amsterdam: University of Amsterdam, 1981. |
| [11] | AJTAI M. The Shortest Vector Problem in L2 is NP-Hard for Randomized Reductions[C]// ACM. The 30th Annual ACM Symposium on Theory of Computing. New York: ACM, 1998: 10-19. |
| [12] | AJTAI M, KUMAR R, SIVAKUMAR D. A Sieve Algorithm for the Shortest Lattice Vector Problem[C]// ACM. The 33rd Annual ACM Symposium on Theory of Computing. New York: ACM, 2001: 601-610. |
| [13] |
NGUYEN P Q, VIDICK T. Sieve Algorithms for the Shortest Vector Problem Are Practical[J]. Journal of Mathematical Cryptology, 2008, 2(2): 181-207.
doi: 10.1515/JMC.2008.009 URL |
| [14] | MICCIANCIO D, VOULGARIS P. Faster Exponential Time Algorithms for the Shortest Vector Problem[C]// ACM. The 21st Annual ACM-SIAM Symposium on Discrete Algorithms. New York: ACM, 2010: 1468-1480. |
| [15] | MERMIN N D. Quantum Computer Science: An Introduction[M]. Cambridge: Cambridge University Press, 2007. |
| [16] |
GROVER L K. Quantum Mechanics Helps in Searching for a Needle in a Haystack[J]. Physical Review Letters, 1997, 79(2): 325-328.
doi: 10.1103/PhysRevLett.79.325 URL |
| [17] | BRASSARD G, HOYER P, MOSCA M, et al. Quantum Amplitude Amplification and Estimation[J]. Contemporary Mathematics, 2002, 305: 53-74. |
| [18] | LAARHOVEN T, MOSCA M, VAN DE POL J. Solving the Shortest Vector Problem in Lattices Faster Using Quantum Search[C]// Springer. International Workshop on Post-Quantum Cryptography. Heidelberg: Springer, 2013: 83-101. |
| [19] | KIM H, JANG K, OH Y, et al. Finding Shortest Vector Using Quantum NV Sieve on Grover[C]// Springer. International Conference on Information Security and Cryptology. Heidelberg: Springer, 2023: 97-118. |
| [20] | KIM H, JANG K, KIM H, et al. Quantum NV Sieve on Grover for Solving Shortest Vector Problem[EB/OL]. (2024-05-29)[2025-02-01]. https://eprint.iacr.org/2024/712. |
| [21] | DORIGUELLO J F, GIAPITZAKIS G, LUONGO A, et al. On the Practicality of Quantum Sieving Algorithms for the Shortest Vector Problem[EB/OL]. (2024-10-17)[2025-02-01]. https://doi.org/10.48550/arXiv.2410.1375. |
| [1] | 张兴兰, 李登祥. 基于Grover量子搜索算法的MD5碰撞攻击模型[J]. 信息网络安全, 2024, 24(8): 1210-1219. |
| [2] | 戚晗, 王敬童, ABDULLAH Gani, 拱长青. 基于随机量子层的变分量子卷积神经网络鲁棒性研究[J]. 信息网络安全, 2024, 24(3): 363-373. |
| [3] | 郭伟, 谢淑翠, 张建中, 杜红珍. 基于GHZ态的三粒子纠缠态量子信息共享研究[J]. 信息网络安全, 2016, 16(1): 24-28. |
| 阅读次数 | ||||||
|
全文 |
|
|||||
|
摘要 |
|
|||||